当前位置:网站首页>[note] IPC traditional interprocess communication and binder interprocess communication principle
[note] IPC traditional interprocess communication and binder interprocess communication principle
2022-07-03 23:04:00 【Li Baoming】
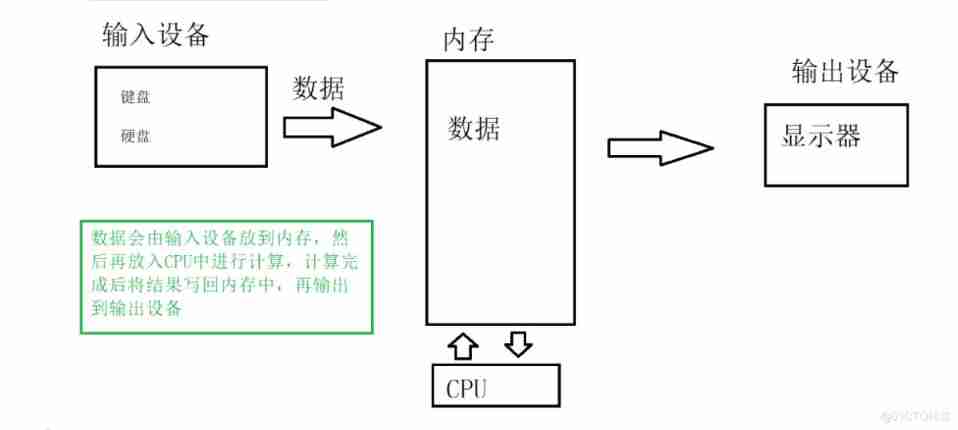
Tradition IPC
Two copy process :

1. The message sender stores the message data to be sent into the memory buffer , Enter kernel state through system call .
2. Then kernel program allocates memory in kernel space , And open up a memory cache , call copy_from_user() Copy data from the user space memory cache to the kernel cache in kernel space .
3. When receiving data, the receiver process creates a memory buffer in its own user space .
4. Then the kernel program calls copy_to_user() Copy the data from the kernel cache to the memory cache of the receiver process .
This completes a data transmission between processes .
This traditional IPC There are two problems with communication :
1. Poor performance , A data transfer needs to go through : Memory cache --> Kernel cache --> Memory cache , need 2 Secondary data copy ;
2. The buffer for receiving data is provided by the data receiving process , But the receiving process doesn't know how much space is needed to store the data to be transferred , So we can only open up as much memory space as possible or call first API Receive the message header to get the small of the message body , These two methods are either a waste of space or a waste of time .
Binder IPC

Binder IPC The memory mapping involved in the mechanism is through mmap() To achieve .
mmap(): Is a memory mapping method in the operating system .
Memory mapping is simply to map a block of memory area of user space to kernel space . After the mapping relationship is established , The user's modification of this memory area can directly reflect the kernel space ; On the other hand, the kernel space modification of this area can also directly reflect the user space .
Memory mapping can reduce the number of data copies , Achieve efficient interaction between user space and kernel space .
The changes of the two spaces can be directly reflected in the mapped memory area , So as to be perceived by each other's space in time
Once complete Binder IPC The communication process is usually like this :
1. First Binder The driver creates a data receiving buffer in kernel space ;
2. And then open a kernel cache in kernel space , Establish the mapping relationship between the kernel cache and the data receiving cache in the kernel , And the mapping relationship between the data receiving buffer and the user space address of the receiving process in the kernel ;
3. Sender process through system call copy from user() Put the data copy To the inside
Kernel cache in the kernel , Due to the memory mapping between the kernel cache and the user space of the receiving process , Therefore, it is equivalent to sending data to the user space of the receiving process , This completes a communication between processes .
边栏推荐
- Weekly leetcode - nc9/nc56/nc89/nc126/nc69/nc120
- [sg function] lightoj Partitioning Game
- 4 environment construction -standalone ha
- Bufferpool caching mechanism for executing SQL in MySQL
- QGIS grid processing DEM data reclassification
- SDNU_ ACM_ ICPC_ 2022_ Winter_ Practice_ 4th [individual]
- Mysql database - Advanced SQL statement (I)
- webAssembly
- 2022.02.14
- How can enterprises and developers take advantage of the explosion of cloud native landing?
猜你喜欢

Go Technology Daily (2022-02-13) - Summary of experience in database storage selection

Weekly leetcode - nc9/nc56/nc89/nc126/nc69/nc120
C deep anatomy - the concept of keywords and variables # dry inventory #
BUUCTF,Misc:LSB

Flutter internationalized Intl

Pointer concept & character pointer & pointer array yyds dry inventory
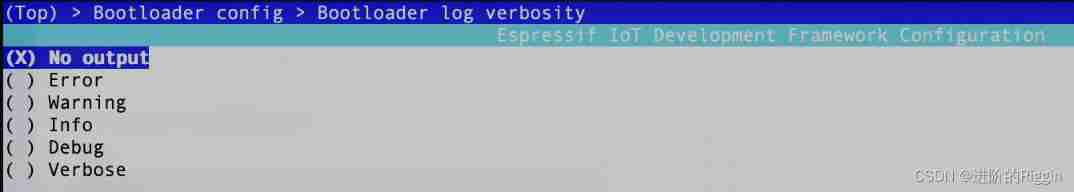
Esp-idf turns off serial port log output.
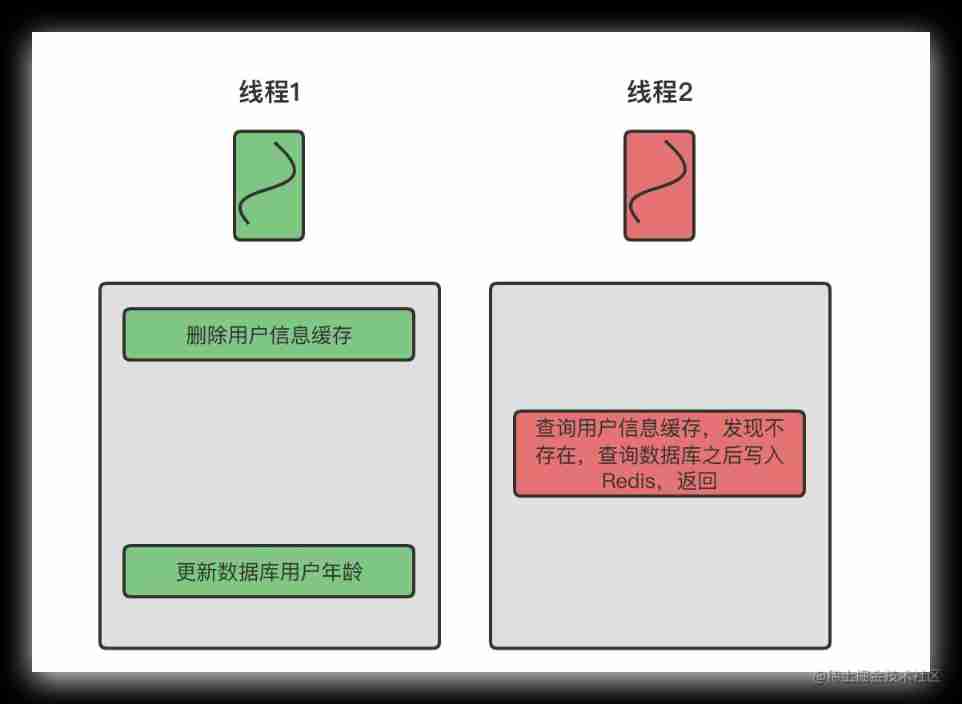
Data consistency between redis and database
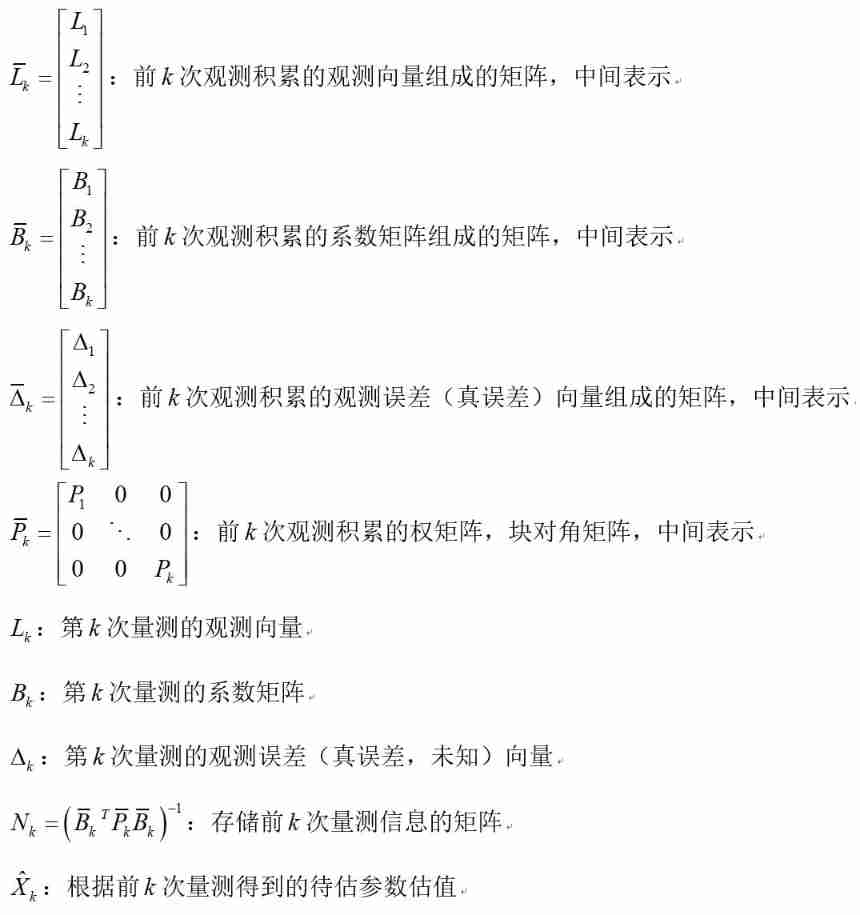
Recursive least square adjustment
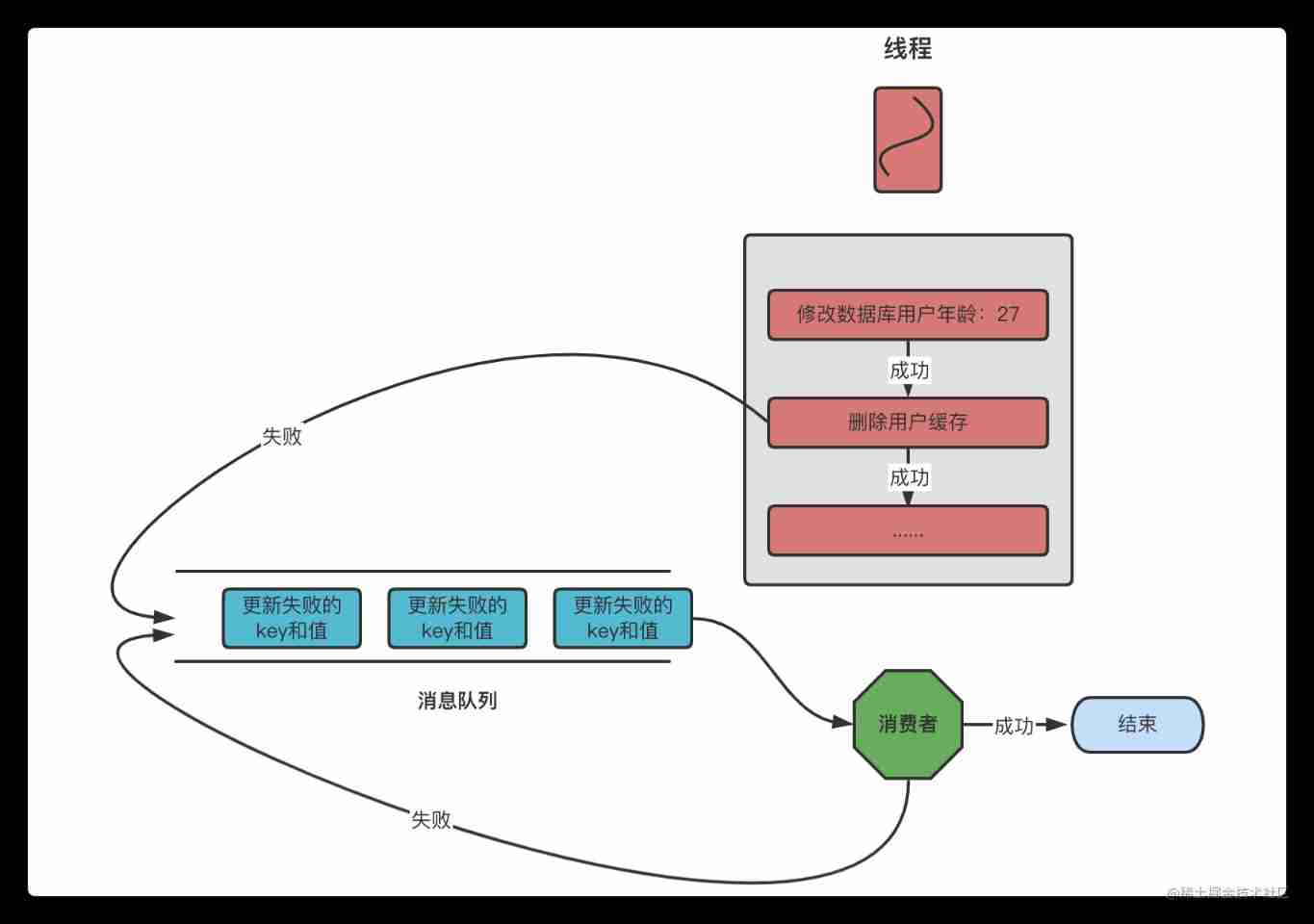
Data consistency between redis and database
随机推荐
LeetCode 540. A single element in an ordered array
[15th issue] Tencent PCG background development internship I, II and III (OC)
Creation of the template of the password management software keepassdx
BUUCTF,Misc:LSB
Firefox set up proxy server
[flax high frequency question] leetcode 426 Convert binary search tree to sorted double linked list
Mindmanager2022 serial number key decompression installer tutorial
1068. Consolidation of ring stones (ring, interval DP)
Teach you how to run two or more MySQL databases at the same time in one system
Ningde times and BYD have refuted rumors one after another. Why does someone always want to harm domestic brands?
Hcip day 15 notes
Hcip 13th day notes
Unique in China! Alibaba cloud container service enters the Forrester leader quadrant
Data consistency between redis and database
Qtoolbutton - menu and popup mode
Runtime. getRuntime(). totalMemory/maxMemory()
How about agricultural futures?
Shell script three swordsman awk
Qtoolbutton available signal
ADB related commands