当前位置:网站首页>A few words explain redis cache penetration, breakdown, avalanche, and redis sentinel
A few words explain redis cache penetration, breakdown, avalanche, and redis sentinel
2022-07-04 11:41:00 【Samsara】
A few words Redis Cache penetration 、 breakdown 、 An avalanche 、Redis sentry
This is an article that bloggers think is very easy to understand
Redis( Master slave copy , Sentinel mechanism , Cache penetration 、 Cache breakdown 、 Cache avalanche , Solve the problem of buffer penetration by using Bloom filter )
| type | Database state | Cache state |
|---|---|---|
| Cache penetration | There is no such data in the database | There is no such data in the cache |
| Cache breakdown | The database has this data | Cache single point expiration |
| Cache avalanche | The database has this data | A large number of caches have expired |
Solution
- Cache penetration :BloomFilter Intercept 、 The query results are stored in the cache and the life cycle is set ( Expiration time ) Shorter
- Cache breakdown : Due to the continuous operation of single point expired data , Therefore, you can set the hotspot data to never expire , Mutexes can also be added to restrict a large number of threads from accessing data at the same time
- Cache avalanche : Because a large number of data are expired , Therefore, it can be set randomly key The expiration time of , Cluster distribution can also query multiple key Put them in different libraries , You can also refresh the cache regularly
Redis sentry
yes Redis A process of , Monitor multiple by running independently Redis The situation of , Yes Master monitor , Also on the slave monitor , Keep it high redis The usability of . Sentinel cluster means that sentinels can also monitor each other's situation , More availability .
边栏推荐
- Heartbeat报错 attempted replay attack
- Experiment 7. IPv6
- LVS+Keepalived实现四层负载及高可用
- LxC shared directory addition and deletion
- C language memory layout
- QQ get group link, QR code
- Usage of case when then else end statement
- Global function Encyclopedia
- Is Sanli futures safe? How to open a futures account? How to reduce the handling charge of futures at present?
- Ternsort model integration summary
猜你喜欢
Elevator dispatching (pairing project) ③
![[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 14](/img/c5/dde92f887e8e73d7db869fcddc107f.jpg)
[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 14
Decrypt the advantages of low code and unlock efficient application development
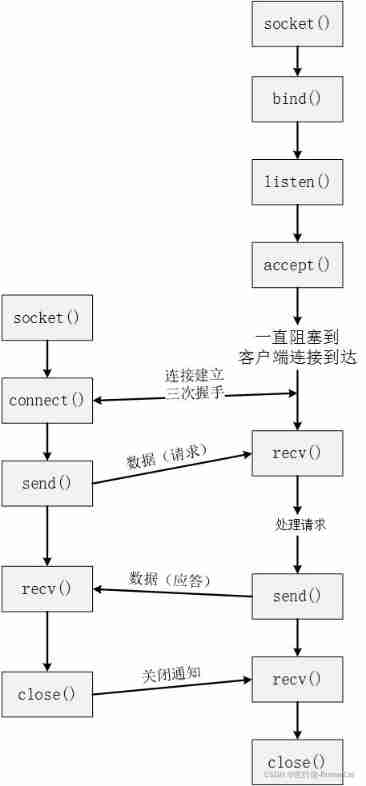
TCP slicing and PSH understanding
![[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 5](/img/68/4f92ca7cbdb90a919711b86d401302.jpg)
[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 5
![[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 15](/img/72/0fe9cb032339d5f1ccf6f6c24edc57.jpg)
[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 15

Take advantage of the world's sleeping gap to improve and surpass yourself -- get up early
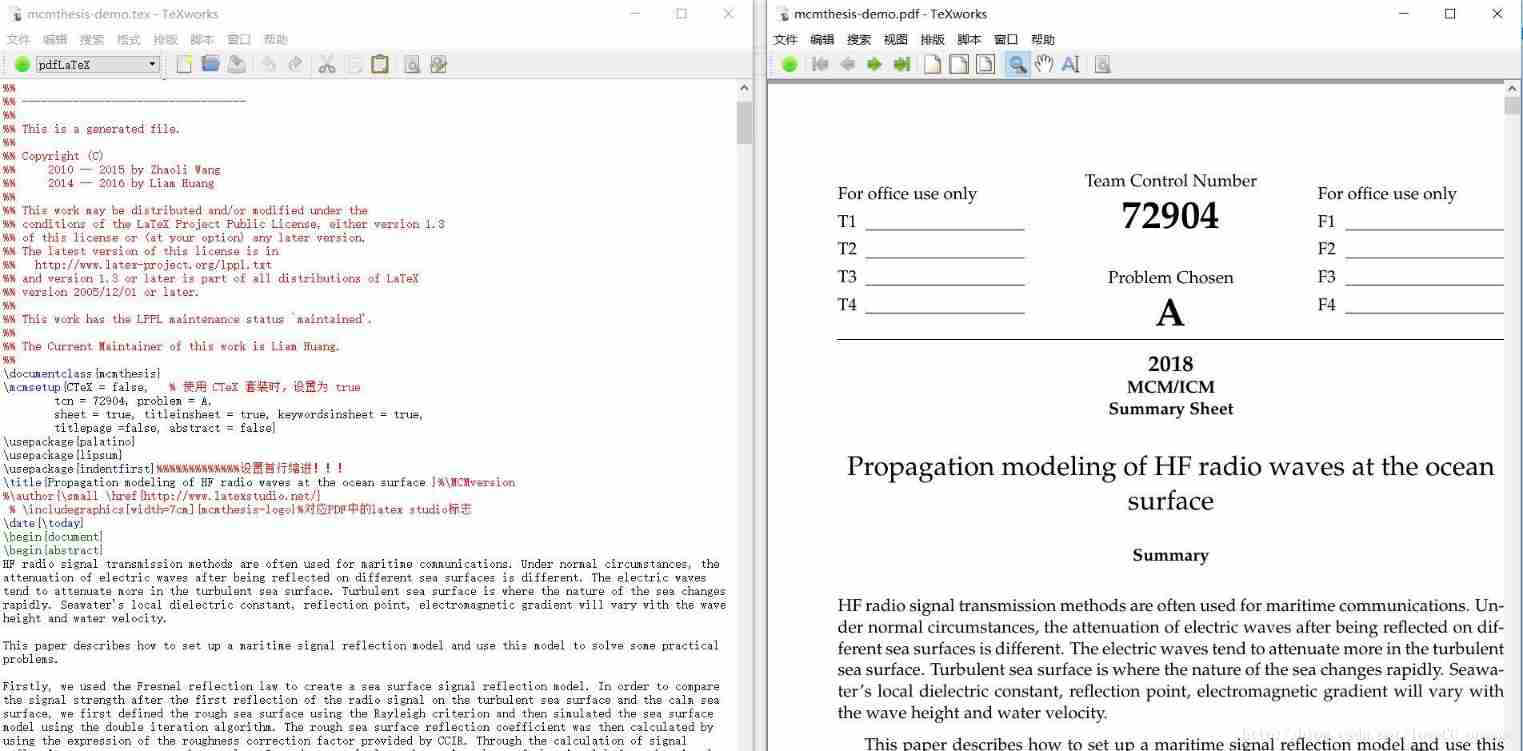
2018 meisai modeling summary +latex standard meisai template sharing
(August 10, 2021) web crawler learning - Chinese University ranking directed crawler
![Entitas learning [iv] other common knowledge points](/img/1c/f899f4600fef07ce39189e16afc44a.jpg)
Entitas learning [iv] other common knowledge points
随机推荐
Heartbeat报错 attempted replay attack
Configure SSH key to realize login free
Here, the DDS tutorial you want | first experience of fastdds - source code compilation & Installation & Testing
LVS+Keepalived实现四层负载及高可用
Reptile learning winter vacation series (2)
Login operation (for user name and password)
2020 Summary - Magic year, magic me
R built in data set
Failed to configure a DataSource: ‘url‘ attribute is not specified... Bug solution
Oracle11g | getting started with database. It's enough to read this 10000 word analysis
[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 21
Supercomputing simulation research has determined a safe and effective carbon capture and storage route
Lvs+kept realizes four layers of load and high availability
regular expression
Simple understanding of seesion, cookies, tokens
Usage of case when then else end statement
C language memory layout
20 kinds of hardware engineers must be aware of basic components | the latest update to 8.13
Definition and method of string
CSDN documentation specification