当前位置:网站首页>Cryptographic technology -- key and ssl/tls
Cryptographic technology -- key and ssl/tls
2022-07-02 23:08:00 【yiixiou】
Key definition
The key is a huge number . The key concept in cryptography is the size of the key space . The size of the key space is determined by the length of the key . common DES The key length is 7 byte ,DES-DES2 and DES-DES3 The key lengths are 14 Byte and 21 byte ,AES The key length is 128,192 or 256 The bit .
Here's the thing , The key and plaintext have the same value . If the plaintext is worth millions , Then the key that can crack the plaintext should have the same value .
Various keys
- Symmetric cryptographic key : Encryption and decryption use the same key . Also known as shared key password .
- Public key cryptographic key : Encryption and decryption use different keys . Encrypted is called public key , The decryption is called the private key . Public and private keys are also called key pairs .
- Message authentication code (MAC) The key of : The sender and receiver use the shared key for authentication .MAC It can only be calculated by the person who holds the legal key . take MAC Attached to the communication message , Identify whether the communication content has been tampered with or camouflaged . shortcoming :MAC There is a risk of tampering and camouflage in leakage .
- Key of digital signature : Different keys are used for signature generation and verification . The person who holds the private key generates a signature , The public key is used for authentication .
- session key : A key that can only be used once in communication . Such as : visit https:// The opening page ,Web Between the server and the browser SSL/TLS Encrypted communication , The key used in this communication is limited to this communication , Belongs to session key . advantage : Even if intercepted, it can only decipher the content of this communication , The confidentiality of other communications is not compromised .
- Master key : A key that has been reused .
- The key used to encrypt the content (Contents Encrypting Key, CEK): Content encryption key . Session keys are often used CEK.
- The key used to encrypt the key (Key Encrypting Key, KEK): Key encryption key . The master key often does KEK. somewhat : Reduce the number of keys that need to be declared .
Key management
- Key generation : Random number generation 、 Password generation (Password Based Encryption, PBE).
- Distribution key : Symmetric algorithm key faces the problem of key distribution , Because encryption and decryption use the same key . You can use a shared key in advance , Using a key distribution center , Use public key password, etc .
- Key update : A technology that improves the confidentiality of communications . This technology has backward security ( One way hash function is one-way , It's difficult to calculate backwards ), It can prevent decoding the contents of past communications .
- Key saving : When the key needs to be reused , We need to consider the problem of key preservation . Session keys are not considered .
- Void key .
SSL/TLS Definition
SSL/TLS It's a kind of Web Protocols widely used in servers .SSL The full name is Secure Socket Layer,TLS The full name is Transport Layer Security.
Client and server
Web The browser and Web Server follows HTTP Hypertext transfer protocol to communicate , Web Browsers are also called HTTP client ,Web Servers are also called HTTP The server . We can use SSL/TLS bearing HTTP, Through the superposition of the two protocols , It can be done to HTTP Communication for ( Requests and responses ) To encrypt , To prevent eavesdropping .SSL/TLS The job of
The working process needs to ensure three points :(1) The sending process cannot be bugged ;(2) The sending process cannot be tampered ;(3) Finally, the sender can be confirmed ;1,2,3 The points correspond to the confidentiality of the key 、 integrity 、 Certification issues .SSL and TLS The difference between
TLS yes SSL Subsequent versions , Added AES Symmetric cipher algorithm , Deleted DES, Added for CBC How to attack .
边栏推荐
- Typical case of data annotation: how does jinglianwen technology help enterprises build data solutions
- To myself who is about to work
- 编辑卡顿
- Stop slave is stuck -- the event of the transaction is not copied completely
- Addition, deletion, modification and query of handwritten ORM (object relationship mapping)
- Jerry's built-in shutdown current is 1.2ua, and then it can't be turned on by long pressing [chapter]
- 數據分析學習記錄--用EXCEL完成簡單的單因素方差分析
- 20220524_数据库过程_语句留档
- 設置單擊右鍵可以選擇用VS Code打開文件
- Generics and reflection, this is enough
猜你喜欢
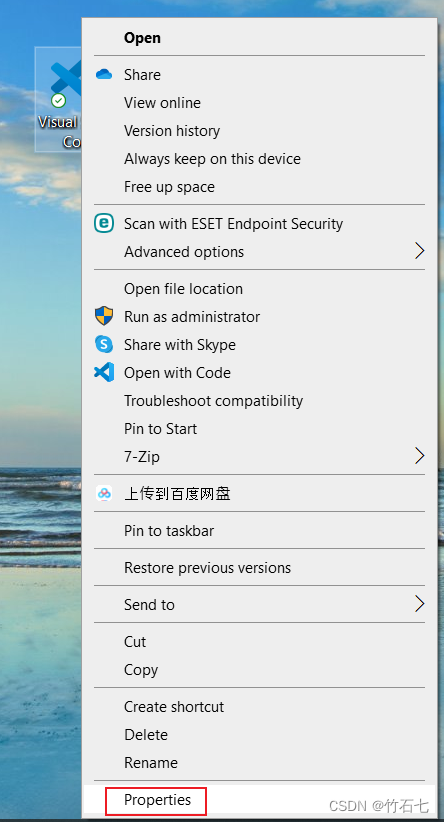
設置單擊右鍵可以選擇用VS Code打開文件

P1007 single log bridge

从2022年Q1财报看携程的韧性和远景

MySQL reset password, forget password, reset root password, reset MySQL password

阿里云有奖体验:如何使用 PolarDB-X
![[npuctf2020]ezlogin XPath injection](/img/6e/dac4dfa0970829775084bada740542.png)
[npuctf2020]ezlogin XPath injection

容器化技术在嵌入式领域的应用
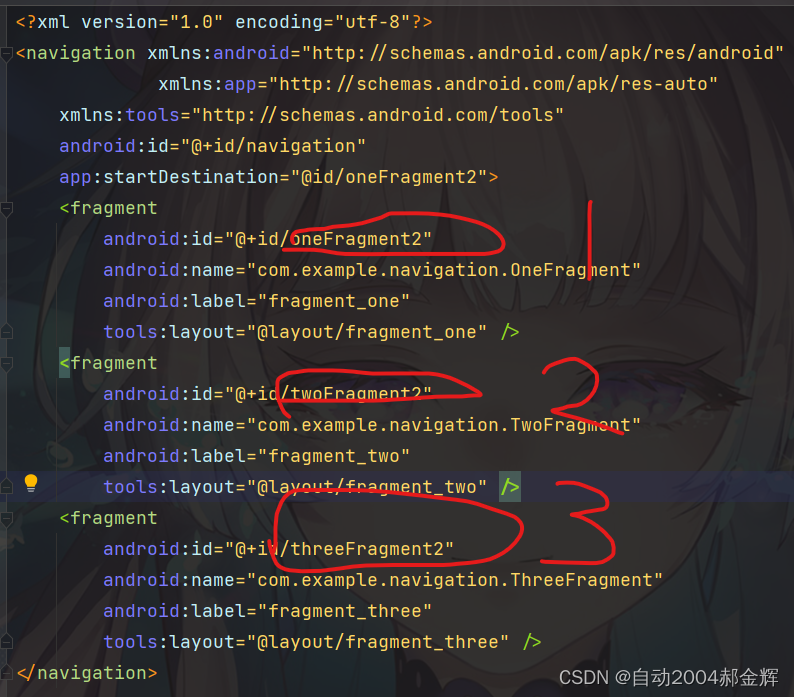
实现BottomNavigationView和Navigation联动
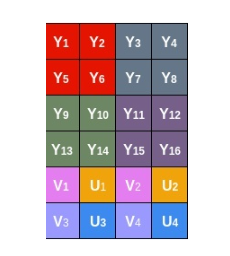
海思3559万能平台搭建:在截获的YUV图像上旋转操作

QT qpprogressbar details
随机推荐
easyclick,ec权朗网络验证源码
损失函数~
解决Chrome浏览器和Edeg浏览器主页被篡改的方法
电路设计者常用的学习网站
[hardware] origin of standard resistance value
归并排序详解及应用
[NPUCTF2020]ezlogin xPATH注入
The first batch of Tencent cloud completed the first cloud native security maturity assessment in China
1px pixel compatibility of mobile terminal, 1px border
Jatpack------LiveData
Odoo13 build a hospital HRP environment (detailed steps)
Jerry's prototype will trigger shutdown after multiple touches [chapter]
Analyse des données dossiers d'apprentissage - - analyse simple de la variance à facteur unique avec Excel
Higher order operation of bits
Golang's learning route
Jielizhi, production line assembly link [chapter]
Jerry's fast touch does not respond [chapter]
Lambda表达式:一篇文章带你通透
密码技术---分组密码的模式
[leetcode] reverse string [344]