当前位置:网站首页>Summit review | baowanda - an integrated data security protection system driven by compliance and security
Summit review | baowanda - an integrated data security protection system driven by compliance and security
2022-07-05 13:33:00 【Ink Sky Wheel】
2022 year 6 month 28、29 Japan , The China Academy of information and communications and the China Communications Standardization Association held a meeting in Beijing 2022 Big data industry summit . On the sub forum of data security , Liu Xianfeng, vice president of Jiangsu baowangda Software Technology Co., Ltd The theme is 《 Build an overall data security protection system driven by compliance and security 》 The share of .

Data security strategy rises to national security strategy
2021 The Political Bureau of the CPC Central Committee deliberated and approved 《 National security strategy (2021-2025 year )》, Juxtapose data security and network security , The strategic position of data security has been clarified from the top-level will of the country , The 14th five year plan also makes key requirements for data security , Data security has been written into the government work report for two consecutive years .
6 month 22 Japan , At the meeting on deepening reform, the general secretary also stressed the need to improve the data whole process compliance and regulatory rule system , Security should run through the whole process of data governance , Clarify the regulatory red line , Compaction enterprise data security responsibility . The data security industry has become highly valued by the state , Regulation is becoming increasingly strict , Has a good growth trend , Industries that also face many problems and challenges . As data security rises to the national strategic level , Data security related laws, regulations and regulatory policies have also been intensively introduced .
Main problems in data security management of enterprises :
With the continuous strengthening of national regulatory requirements and changes in external risks , The customer's original safety system has not fully adapted to the new requirements , Facing new problems , Specifically, :(1) How to unify the security system to meet the needs of multiple departments 、 Multiple laws , Compliance requirements of multiple standards (2) The original single point protection means can not guarantee safety , It can't meet the problem of compliance (3) How the original network security system and the new data security system are compatible and coordinated (4) Based on the basic characteristics of data flow , How to implement dynamic defense and dynamic operation (5) Too much data and too many systems , How to systematically carry out data security governance .
Baowangda “ Compliance and safety double drive ” Data security overall protection system
In view of the development trend of data security industry and the current problems faced by enterprises , Baowangda is based on more than ten years of practical experience in the data security industry , To build the “ Compliance and safety double drive ” Data security overall protection system .“ Dual drive system ” The starting point of is not only the growth of the enterprise itself , Pay more attention to the benign development of the overall data security environment .

At the same time, baowangda launched an innovative panorama of data security system driven by compliance and security - Ark platform . The ark platform contains three goals, five systems, eight scenes and fifteen data security products for data security , Products support cloud based architecture 、 Pooling and atomization , That is, it can be provided to customers as an overall platform , Some sub platform capabilities can also be provided according to the current situation and requirements of customers , And well adapt and integrate with the original platform of customers . Part of the concept of dual drive system is proposed for the first time in the data security industry , It has aroused enthusiastic response in the industry .

Construction of data security compliance system
The data security compliance system is based on PDCA The model is divided into eight steps : Follow up and interpretation of laws, regulations and regulatory policies - Compliance work planning and task decomposition - Compliance assessment - Compliance capacity building - Compliance check - Compliance analysis and continuous improvement - Report and complaint management - Regulatory data reporting . Among them, there are two things that need enterprises to focus on , One is : Report and complaint management , It is very easy to be ignored in the daily data security management of enterprises , Both internal and external departments need to establish publicity, reporting and complaint channels and maintain smooth channels . Two is : Regulatory data reporting , At present, in the process of enterprise operation , There are more and more requirements for long regulatory data , Centralized management of regulatory data is needed , And pay attention to the multi caliber verification of various data .
A case of the implementation of the integrated data security protection system driven by both compliance and security

Take an operator as an example , Through baowangda “ An overall data security protection system driven by compliance and security ” Implementation and landing of , Shared in the enterprise 70 Multiple business systems ,400 Multiple databases ,4 More than ten thousand tables , Sensitive table 1 More than ten thousand , Daily monitoring of main data flow 90 many G, Daily discovery risk 100 Bar or so .
After a preliminary assessment , Meet the requirements of national and industrial competent departments on control points and assessment points of data security supervision and compliance , It has achieved the double goals of data security compliance and risk protection , And can dynamically operate and continuously improve based on the overall system .
Baowangda has built a double driven data security overall protection system based on more than ten years of data security industry practice , While creating value for customers, it also gains the recognition of customers and peer experts .

Create a safer digital future

Baowangda will respond to the national call , Comply with regulatory guidelines , Focus on specialized and new research and development , Focus on Collaborative supporting capabilities , Build a financing innovation ecosystem with industry partners , Support the industrial upgrading of Suan , Together to create a safer digital future .
complete PPT download
link :
https://pan.baidu.com/s/1u070awW-Zs8I4edDbOlsyQ
Extraction code :2erp
边栏推荐
猜你喜欢
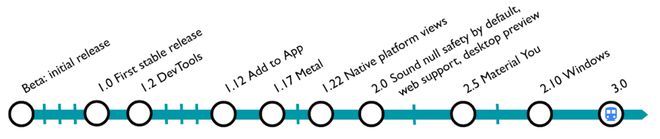
Flutter 3.0更新后如何应用到小程序开发中
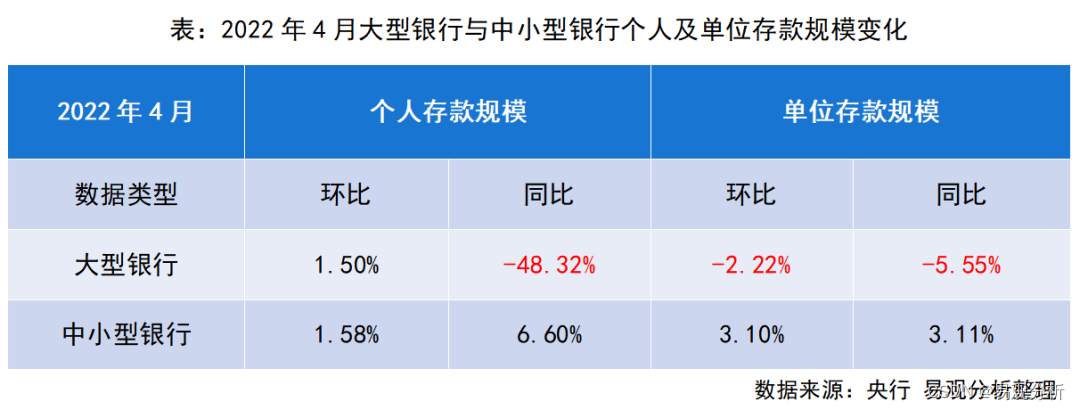
Although the volume and price fall, why are the structural deposits of commercial banks favored by listed companies?
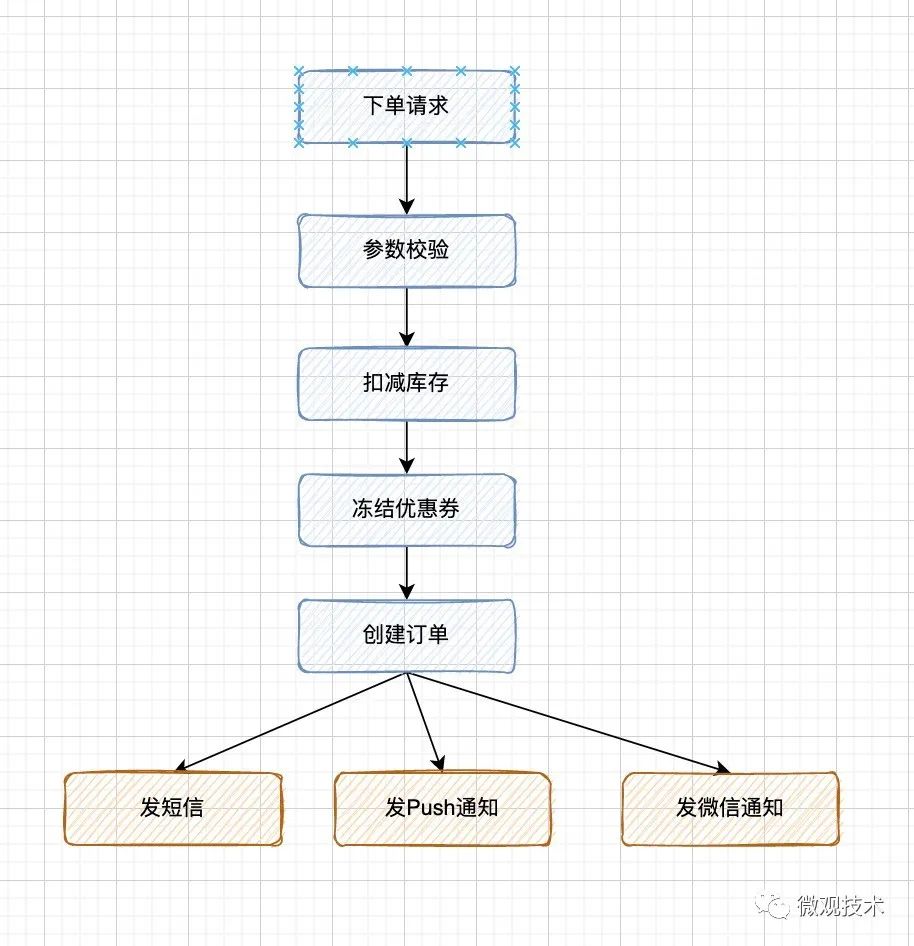
Talk about seven ways to realize asynchronous programming
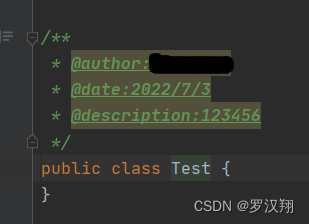
Idea set method annotation and class annotation

峰会回顾|保旺达-合规和安全双驱动的数据安全整体防护体系
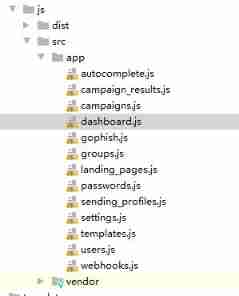
Changing JS code has no effect
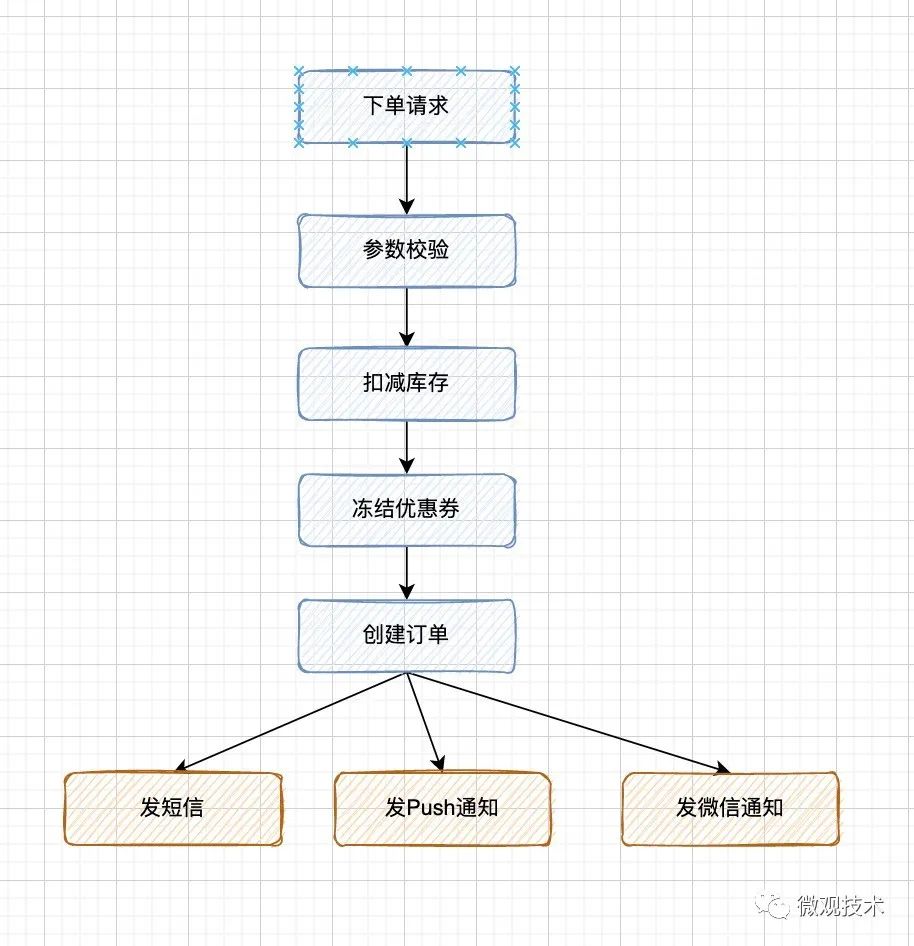
聊聊异步编程的 7 种实现方式
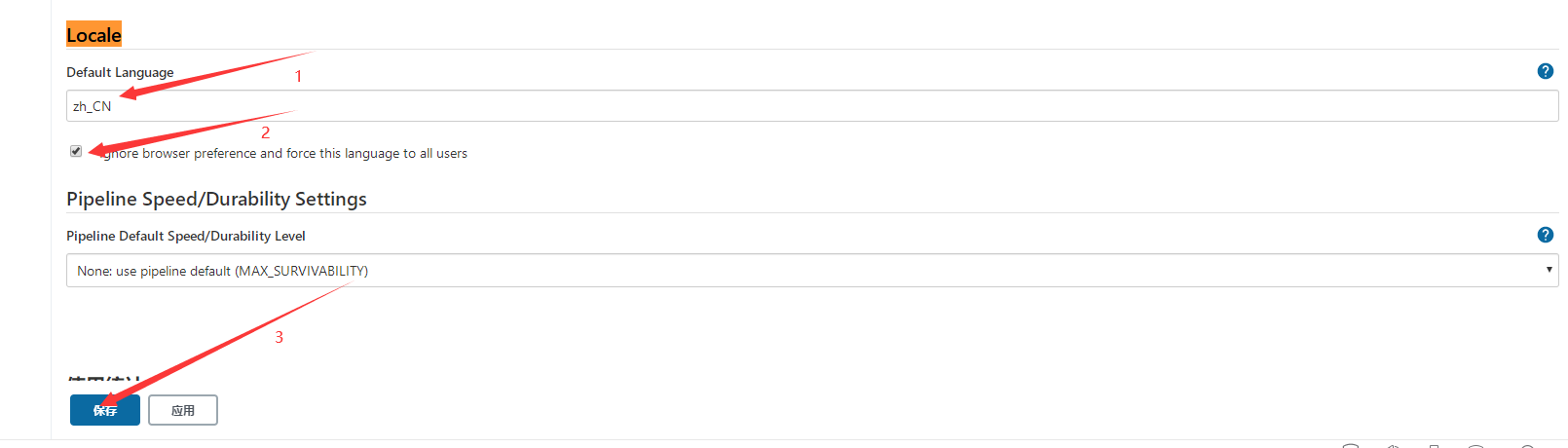
jenkins安装
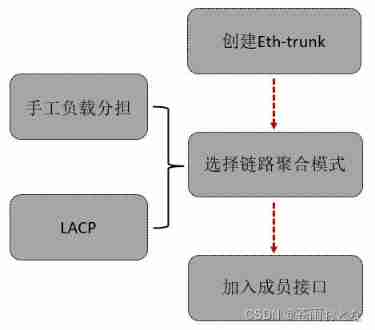
MSTP and eth trunk
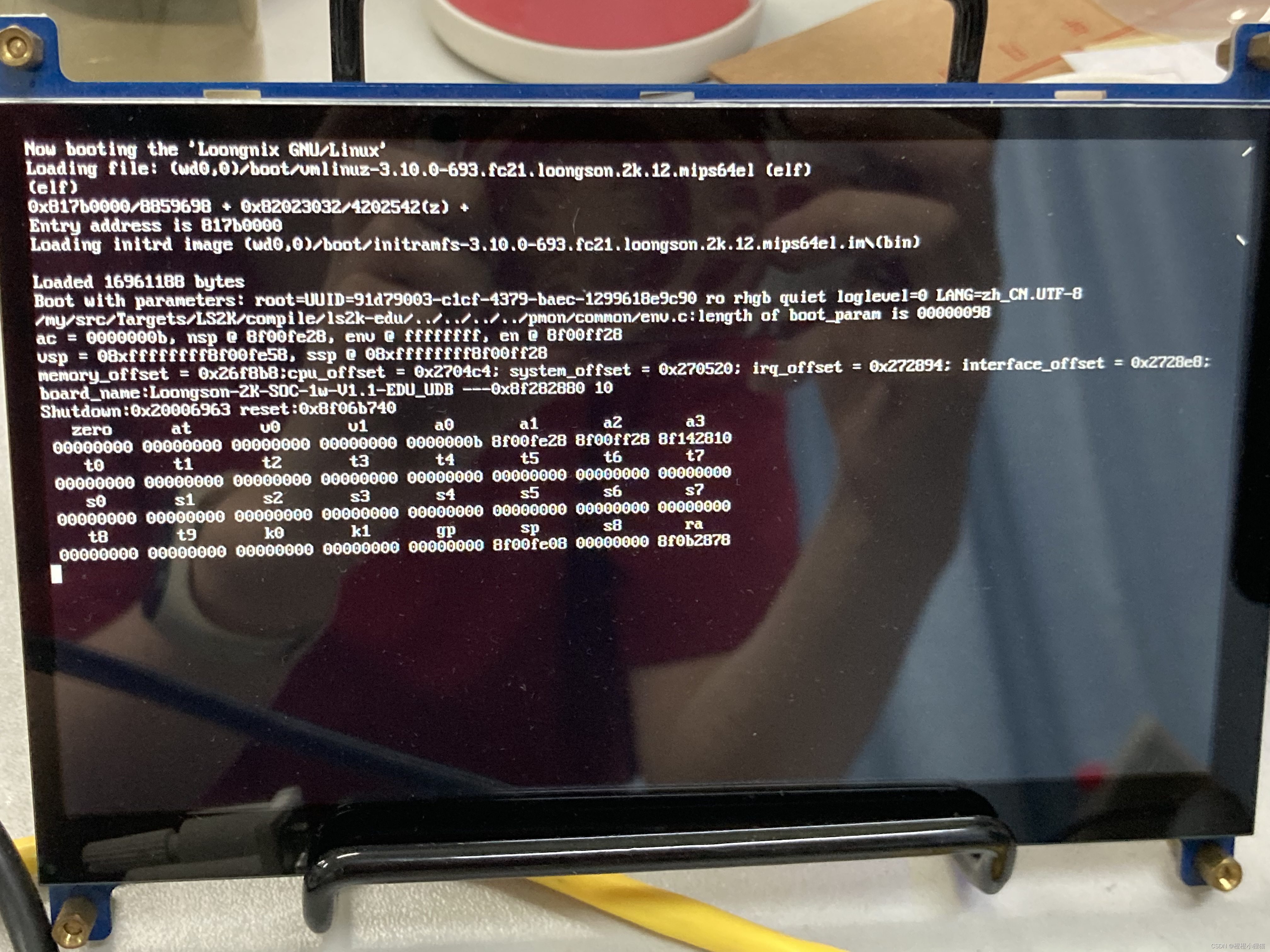
龙芯派2代烧写PMON和重装系统
随机推荐
#从源头解决# 自定义头文件在VS上出现“无法打开源文件“XX.h“的问题
Could not set property ‘id‘ of ‘class XX‘ with value ‘XX‘ argument type mismatch 解决办法
法国学者:最优传输理论下对抗攻击可解释性探讨
通讯录(链表实现)
这18个网站能让你的页面背景炫酷起来
[notes of in-depth study paper]uctransnet: rethink the jumping connection in u-net from the perspective of transformer channel
[deep learning paper notes] hnf-netv2 for segmentation of brain tumors using multimodal MR imaging
"Baidu Cup" CTF competition in September, web:sql
C object storage
MySQL --- 数据库查询 - 排序查询、分页查询
Prefix, infix, suffix expression "recommended collection"
手把手带你入门Apache伪静态的配置
How to apply the updated fluent 3.0 to applet development
A detailed explanation of ASCII code, Unicode and UTF-8
RHCSA10
【MySQL 使用秘籍】一网打尽 MySQL 时间和日期类型与相关操作函数(三)
MMSeg——Mutli-view时序数据检查与可视化
Notion 类笔记软件如何选择?Notion 、FlowUs 、Wolai 对比评测
【Hot100】34. 在排序数组中查找元素的第一个和最后一个位置
go 字符串操作

