当前位置:网站首页>IOS upload app store error: this action cannot be completed - 22421 solution
IOS upload app store error: this action cannot be completed - 22421 solution
2020-11-08 00:43:00 【waha231】
iOS Upload App Store Report errors :this action cannot be completed -22421 Solution
Reference article :
(1)iOS Upload App Store Report errors :this action cannot be completed -22421 Solution
(2)https://www.cnblogs.com/yajunLi/p/6002807.html
Just remember .
版权声明
本文为[waha231]所创,转载请带上原文链接,感谢
边栏推荐
- ROS学习---远程启动ROS节点
- 使用jsDelivr加速你的网站
- The emergence and significance of micro service
- 【解决方案】分布式定时任务解决方案
- High concurrency in ngnix cluster
- 来自不同行业领域的50多个对象检测数据集
- supervisor和Python多进程multiprocessing使用 子进程残留问题
- Download, installation and configuration of Sogou input method in Ubuntu
- Sentry 安装
- The road of cloud computing: a free AWS cloud server
猜你喜欢
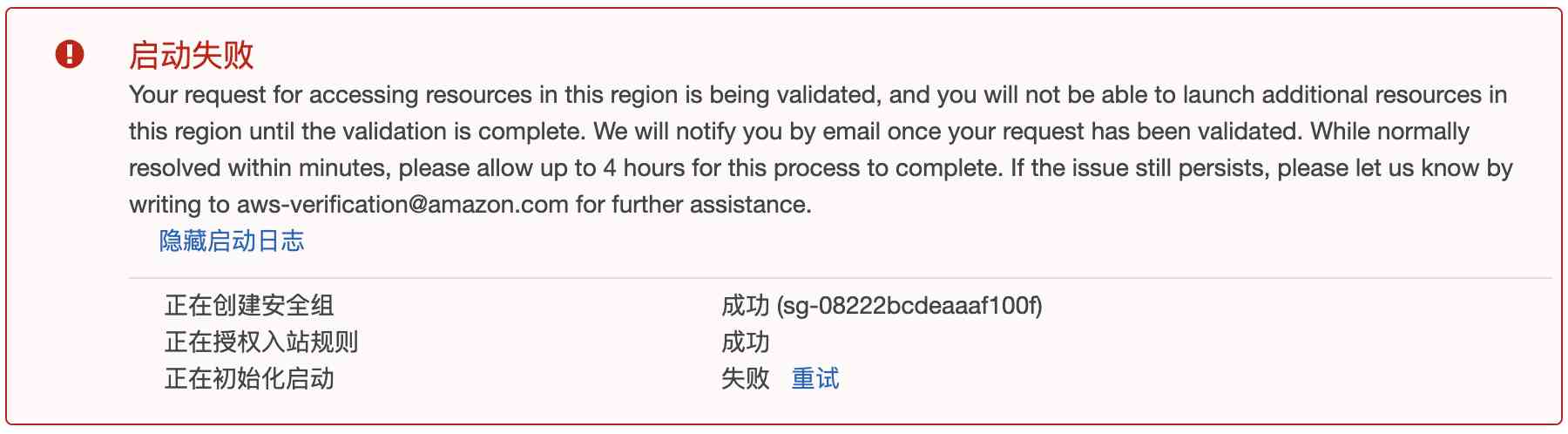
云计算之路-出海记:整一台 aws 免费云服务器

The real-time display of CPU and memory utilization rate by Ubuntu
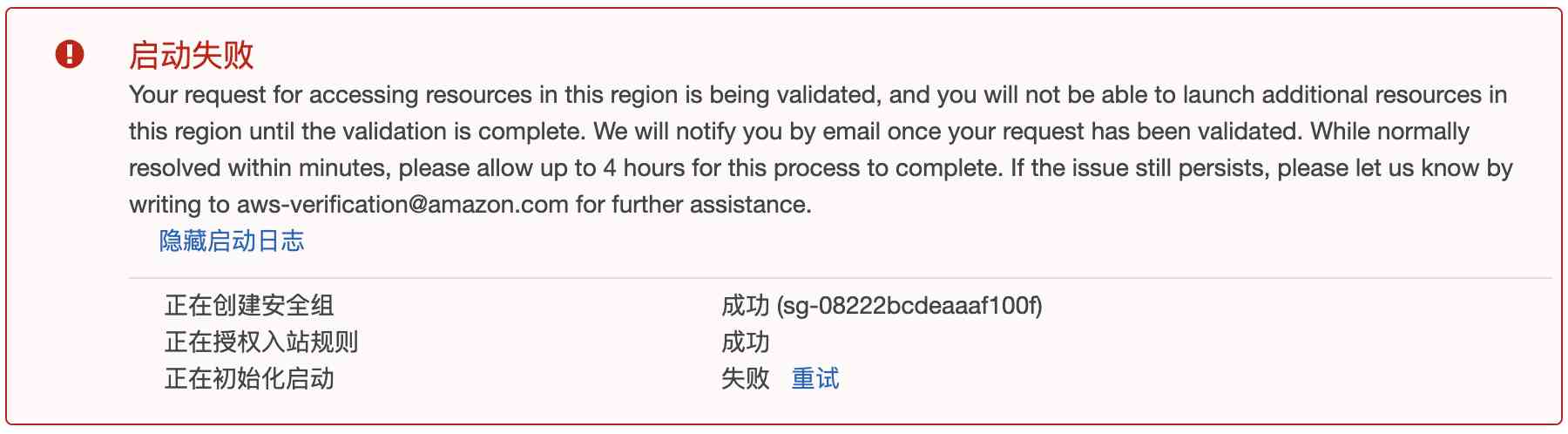
The road of cloud computing: a free AWS cloud server
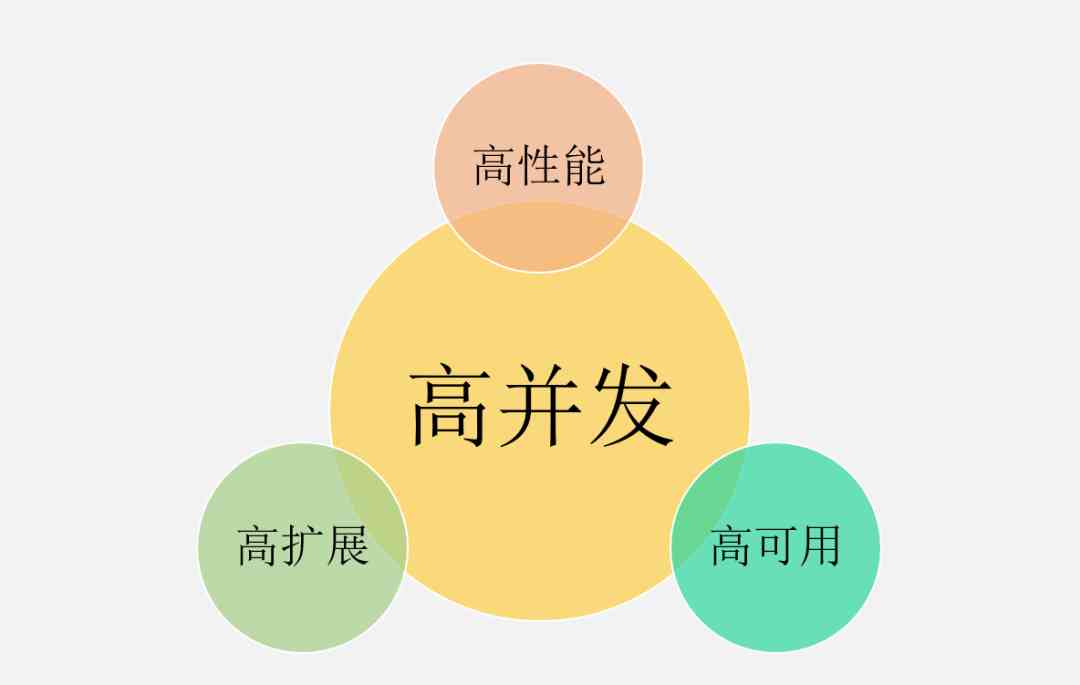
高并发,你真的理解透彻了吗?

什么都2020了,LINQ查询你还在用表达式树
关于晋升全栈工程师,从入门到放弃的神功秘籍,不点进来看一看?

What kind of technical ability should a programmer who has worked for 1-3 years? How to improve?

use Xunit.DependencyInjection Transformation test project

爆一个VS2015 Update1更新带来的编译BUG【已有解决方案】
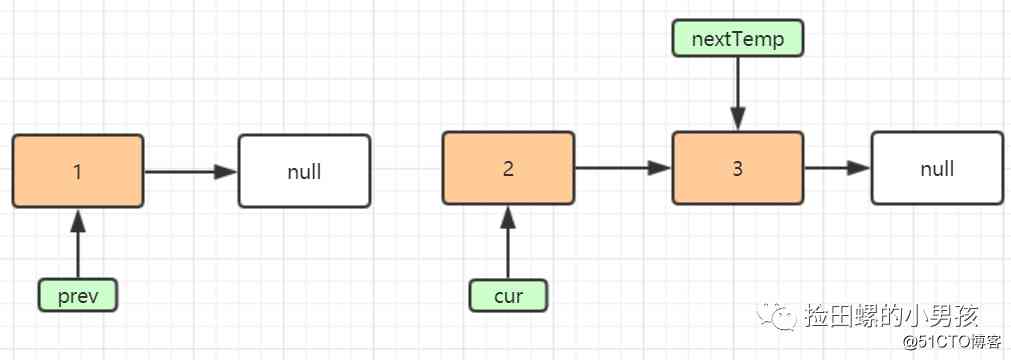
看一遍就理解,图解单链表反转
随机推荐
Basic operation of database
Windows下子系统Ubuntu安装
What kind of technical ability should a programmer who has worked for 1-3 years? How to improve?
Judging whether paths intersect or not by leetcode
See once to understand, graphic single chain table inversion
Adobe Lightroom /Lr 2021软件安装包(附安装教程)
看一遍就理解,图解单链表反转
Web Security (3) -- CSRF attack
delphi10的rest.json与system.json的踩坑
Writing method of field and field comparison condition in where condition in thinkphpp6
1.深入Istio:Sidecar自动注入如何实现的?
Introduction to ucgui
What details does C + + improve on the basis of C
Go之发送钉钉和邮箱
Web安全(三)---CSRF攻击
Experience the latest version of erofs on Ubuntu
wanxin金融
在Ubuntu上体验最新版本EROFS
The software in your host has terminated an established connection. resolvent
Face recognition: attack types and anti spoofing techniques