当前位置:网站首页>Application DDoS attack principle and defense method
Application DDoS attack principle and defense method
2022-06-24 19:19:00 【Warner cloud IDC service provider】
DDoS An attack is a hidden danger , Keep hiding webmasters , And block the access process of the application . Due to damage and shutdown , We have become accustomed to DDoS attack As headlines . however , We often miss some details , These details may suggest how we can avoid such attacks . Warner cloud gives you a brief introduction to the application DDoS The basic attack principle of the attack and its defense methods .
One 、 know OSI Model
In order to grasp all kinds of DDoS attack , First of all, we need to understand how data travels through network connections .OSI Model ( Open Systems Interconnection ) It is the process of negotiating different levels of network connection .OSI The level of the model is as follows :
• Applications : Identify partner tiers .
• demonstration : Usually part of the operating system , Data can be converted into various formats .
• conversation : establish , Coordinate and terminate the dialogue .
• transmission : Convert data into packets for easy transmission .
• The Internet : Handling addressing and routing data .
• Data links : Establish links across physical networks .
• Physics : Transport data streams , Also known as bitstream .
please remember , Data from OSI Start at the bottom of the model , All the way to the top . In short , Data will traverse OSI All levels of the model , Until it reaches its intended destination . The top layer communicates only through the lower layer , Until the data request is completed . Whenever you click Web When the link on sends a request , These connections are made at lightning speed . If data is lost at any level , Then the connection will terminate and the connection will be lost .DDoS Attacks are designed to disrupt these levels of communication , Thus flooding the network and terminating the connection .
How-To-Choose-The-Best-DDoS-Protection-Service.jpg
Two 、 In the first 7 layer : Application level attacks
Although there are various DDoS attack , But the application layer ( That is to say 7 layer ) Attacks surge . If you view the above OSI Model , be “ Application level ” Is the top of the data connection . This type of DDoS Attacks are often much more complex , And it needs less resources to destroy the connection of the target website . Because less resources are needed , So the first 7 The creation cost of layer attack is low . And due to various interference sources , They are also difficult to mitigate .
The first 7 Layer attacks may cause websites to crawl slowly , And often take them completely offline . When an attacker aims to pass through a large number of HTTP Request to utilize system resources , A shutdown will occur . Zombie programs and infected computer systems will be single HTTP The request is sent to the target network . One HTTP The request is very easy to resolve , however , When requests are made quickly and continuously , The network will soon be overloaded .
Warner cloud CDN Expert tips ,“ To resist 7 layer DDoS The only way to attack is , Applications and websites need to upgrade their networks to handle the load .” This translates into an increase in server level resources and redundancy . about V/P/S trusteeship , Many administrators will scale up and add additional nodes , To ensure that large-scale DDoS The connection will not be lost during the attack . In order to protect your website from the 7 layer DDoS A serious attack , Warner cloud launched advanced anti DDoS server in Hong Kong 、 Hong Kong advanced defense IP And other products and services , They are based on automatic intelligent attack identification and second level trigger cleaning mechanism , Finally, large-scale DDoS The effect of attack defense . Warner cloud advanced anti DDoS server in Hong Kong and advanced anti DDoS in Hong Kong IP, Support defense beyond 500Gbps A serious attack of scale , Can ensure that the website /web Apps are always online . Its advanced anti DDoS server in Hong Kong supports stress testing , Support defense against invalid refund commitments . Its Hong Kong advanced defense IP, Just put your website / Off site web Application resolution to advanced anti DDoS IP Can be in 5 Get defense support quickly in minutes , And no matter http still https Websites are perfectly defensible .
边栏推荐
- cdc+mysql connector从维表中join的日期时间字段会被+8:00,请问阿里云托管的
- Building MVC system based on three-tier structure
- Introduction, download and use of global meteorological data CRU ts from 1901 to 2020
- Xiaobai, let me ask you guys, is MySQL binlog extracted by CDC in strict order
- 为什么生命科学企业都在陆续上云?
- [computer talk club] Lecture 3: how to raise key issues?
- A detailed explanation of the implementation principle of go Distributed Link Tracking
- Spatial simulation model acquisition future land cover tutorial
- NFT质押流动性挖矿系统开发技术
- Why is nodejs so fast?
猜你喜欢

Volcano becomes spark default batch scheduler
微信小程序轮播图怎么自定义光标位置
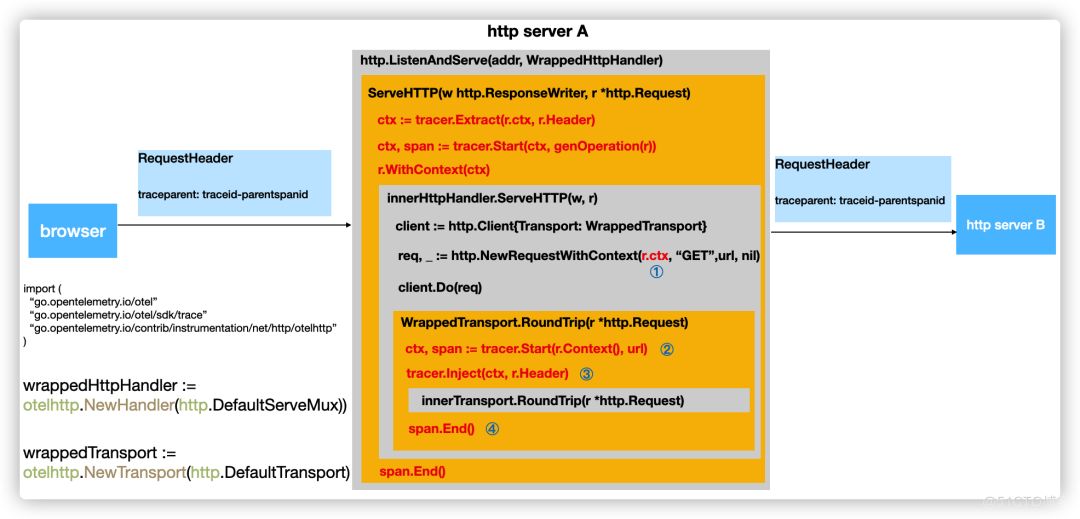
A detailed explanation of the implementation principle of go Distributed Link Tracking

西北工业大学遭黑客攻击?双因素认证改变局面!

Introduction and tutorial of SAS planet software

The verifiable certificate of geoscience remote sensing industry

网络安全审查办公室对知网启动网络安全审查

一文理解OpenStack网络

一次 MySQL 误操作导致的事故,高可用都不顶不住!

Introduction and download of nine npp\gpp datasets
随机推荐
Fabric 账本数据块结构解析(一):如何解析账本中的智能合约交易数据
Does version 2.2.0 support dynamic addition of MySQL synchronization tables
应用程序DDoS攻击原理及防御方法
Fabric ledger data block structure analysis (I): how to analyze the smart contract transaction data in the ledger
ls 常用参数
优维低代码:构件渲染子构件
Vite+web3: referenceerror: process is not defined
Spatial simulation model acquisition future land cover tutorial
电源噪声分析
cdc+mysql connector从维表中join的日期时间字段会被+8:00,请问阿里云托管的
论文解读(SR-GNN)《Shift-Robust GNNs: Overcoming the Limitations of Localized Graph Training Data》
Volcano becomes spark default batch scheduler
小滴课堂海量数据处理商用短链平台大课
What do I mean when I link Mysql to report this error?
Module V
一文详解|Go 分布式链路追踪实现原理
8 challenges of BSS application cloud native deployment
Multi cloud mode is not a "master key"
程序员大部分时间不是写代码,而是。。。
香港服务器租用错误可能导致严重后果