当前位置:网站首页>The MySQL database in Alibaba cloud was attacked, and finally the data was found
The MySQL database in Alibaba cloud was attacked, and finally the data was found
2022-07-07 01:09:00 【I pretend to be strong】
Introduce
When I posted my website yesterday , I found that I couldn't go up , Because it uses springboot Written , Stored in Alibaba cloud lightweight ECS , So I went backstage to check the log , I found that I couldn't find the data .
At this time, it was found that there was a problem with the database , Then I opened my own remote database through graphical tools , I found that all the databases I built were missing , I checked for a long time and didn't find out what was going on , At this time, I found Alibaba's customer service after being reminded by others , They assigned me engineers , The engineer helped me determine the scope of the investigation 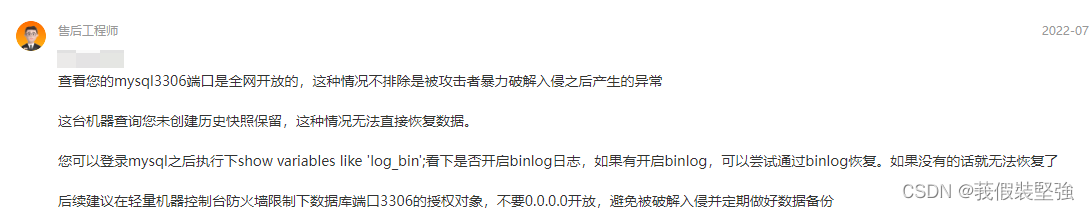
Finally, it was found by checking the binary file that it was attacked by foreign hackers
The following words probably mean to let me spend money to buy back the data, or sell my data , Fortunately, data is not very important .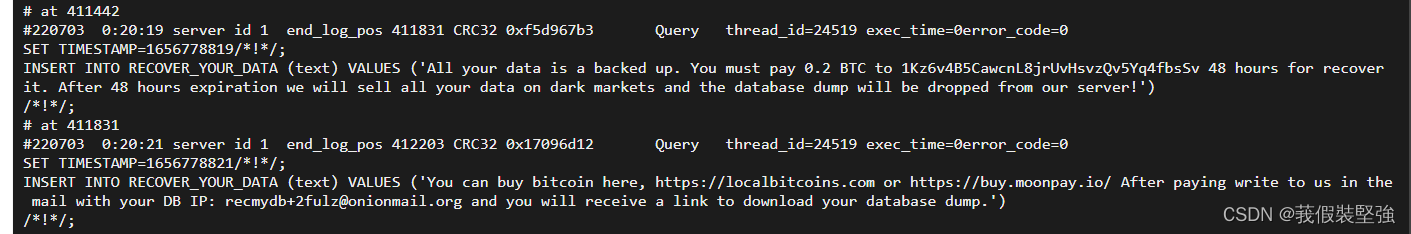
And deleted all my databases
mysql Configuration of
mysql5.6.46 In Alibaba cloud server mysql database , It has been used for less than a year
binlog
What is? binlog
In simple terms , In fact, it is a log that records all addition, deletion and modification operations . We can recover the misoperated data through it , Of course, it can also be used to synchronize master-slave databases .
binlog Three models of :
①statement: Record every piece of modified data sql.
advantage : The log file is small , save io operation , Good performance .
shortcoming : Only record execution statements , Therefore, it is also necessary to ensure that the same results are obtained in the master-slave execution . So the accuracy is poor .
②row: Save which record has been modified .
advantage : It's accurate .
shortcoming : The log file is large .
③mixed: Take into account the advantages of the first two .( I belong to this )
Actual operation :
① see binlog Has it been turned on : If it's not turned on , It's completely cool , There is little chance of recovery , But you can find an attacker to buy back the data
stay mysql Enter command in :SHOW VARIABLES LIKE ‘log_bin’; As shown below 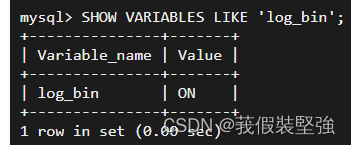
You can see Value yes ON
If it's not turned on , You can refer to the following article ,
https://blog.csdn.net/qq_21996541/article/details/107280382
You can also use fuzzy query , See more information 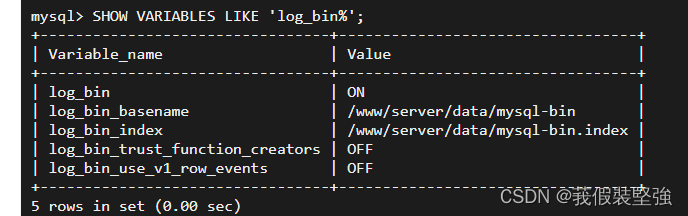
③ see binlog journal :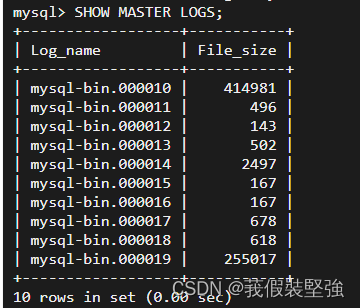
Through the command :SHOW MASTER STATUS; You can check which log file is currently in ,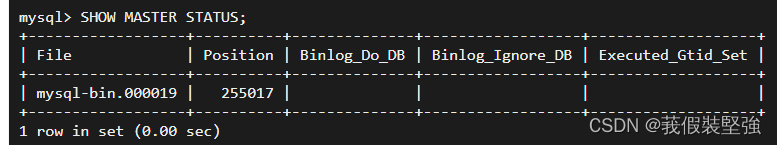
Through the command :FLUSH LOGS; Log files can be truncated , Redirect to a new log file , When we are actually operating , Every operation binlog Before recovery , You need to execute this command , It can ensure that the previous log file will not have new logs in this file , Impact recovery .
There will be another one when you check again after execution 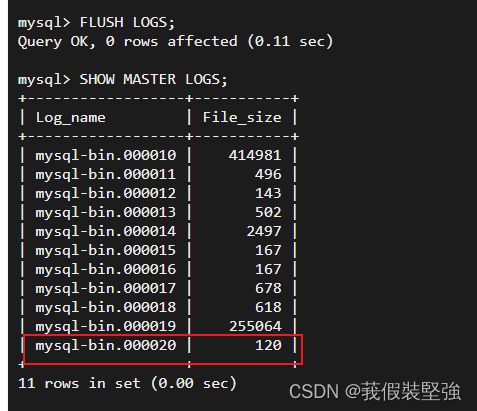
then , According to the order :show variables like ‘%datadir%’; Find the path where these log files are saved 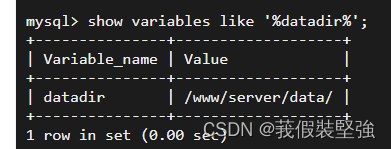
We're on the server ,cd Go to this directory , These files do exist . But these files are binary files , use cat/vi These commands cannot be viewed normally .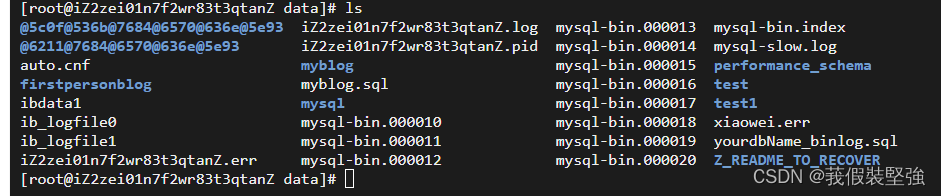
We need our mysqlbinlog This order is on the stage ,
First , We enter the command in the server :mysqlbinlog /www/serverl/data/mysql-bin.000020;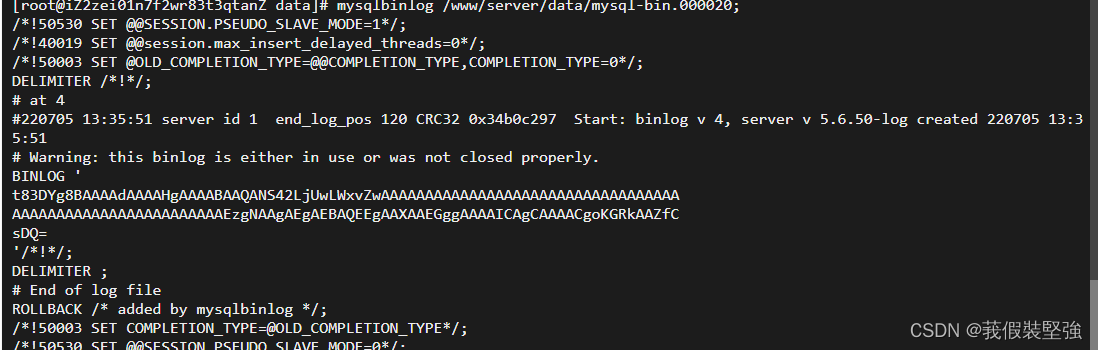
If you enter the above command and an error is reported , You can enter the following command
Enter the command :mysqlbinlog --no-defaults /www/server/data/mysql-bin.000020; You can see the following file information .
However, we can also mysql Enter command in :SHOW BINLOG EVENTS IN 'mysql-bin.000020';
In this way, you can also see binlog Some events recorded in :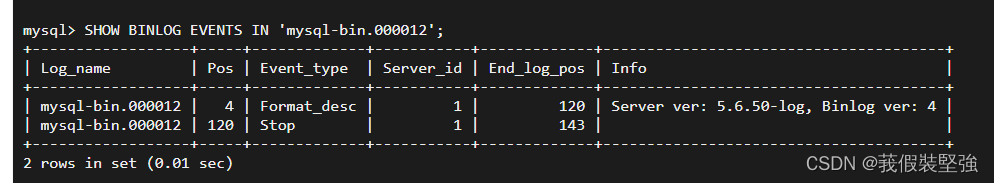
among ,server_id =1, Because we didn't set up , It means the default host ,Pos What I understand is an offset pointer , It is similar to a time node , What operations have been completed at this time node .event_type It means the event type ,xid Business ,query Inquire about ,write rows Means insert data ,delete_rows Delete data , It's easy to recognize .
④ adopt binlog Data recovery :
By looking at , I found my data base in mysql-bin.000010 In this binary file
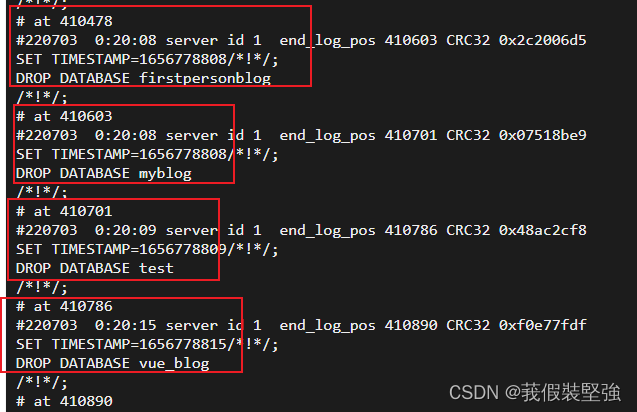
In this file, you can clearly see that the last operation time before my database was deleted is 7 month 2 Number 10:35:34
The time before deleting the database is 7 month 3 Number 0:20:06, It didn't stop until one o'clock .
Ah , flowers 40 Attack a useless database for more than minutes , I feel a little unworthy , And it's still in the middle of the night .
You can see the name of the deleted database , Yes 8 A database , But for me , The more important one is , A few are built during normal testing , There are few data in it ,
Just for the most important , I must get it back , As long as there is a trace .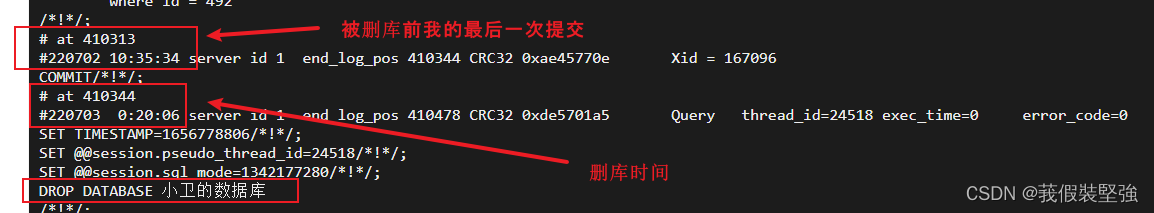

Because for me, what is more important is a database , There are no other data , Not very important , All are restored by restoring the specified database .
Generate by the following command sql file , And then through sql File for recovery
mysqlbinlog --no-defaults --database=xiaochengxu_ks --skip-gtids --stop-position=410161 /www/server/data/mysql-bin.000010 > /xiaochengxu_ks.sql
among xiaochengxu_ks Is the name of the database you want to recover --stop-position=410161 The position before the deleted database corresponds to at Number followed by /www/server/data/mysql-bin.000010 The specific location of the binary file /xiaochengxu_ks.sql Generated from binary files sql The location of the file 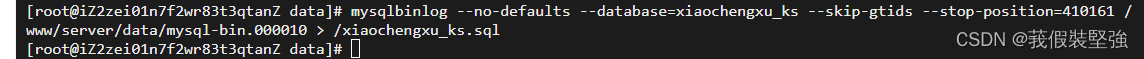
Generate corresponding sql The file is under the change directory 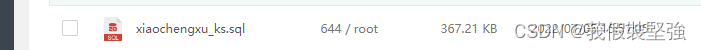
stay MySQL The client command line enters xaiochengxu_ks database , perform source /xiaochengxu_ks.sql Just restore the data .
You can also set the start and end points , But I don't think it's necessary , Through or through time interval
- Start locator
mysqlbinlog --start-position=249 binlog.000006 - End locator
mysqlbinlog --stop-position=249 binlog.000006
summary
I used to think that network security is not very important , That's because it didn't happen to me , These days, I feel its extremely important , Swear to pay attention to network security in the future , At the same time, strengthen your own examples , Avoid recurrence
边栏推荐
- 腾讯云 WebShell 体验
- 【JVM调优实战100例】04——方法区调优实战(上)
- LLDP兼容CDP功能配置
- 斗地主游戏的案例开发
- ARM裸板调试之JTAG原理
- Do you understand this patch of the interface control devaxpress WinForms skin editor?
- Make a simple graphical interface with Tkinter
- Windows installation mysql8 (5 minutes)
- [hfctf2020]babyupload session parsing engine
- 筑梦数字时代,城链科技战略峰会西安站顺利落幕
猜你喜欢
Dell笔记本周期性闪屏故障
![[牛客] B-完全平方数](/img/bd/0812b4fb1c4f6217ad5a0f3f3b8d5e.png)
[牛客] B-完全平方数
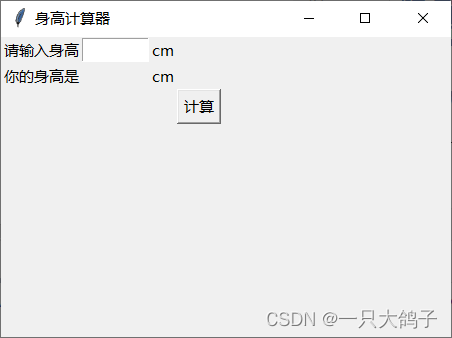
Make a simple graphical interface with Tkinter
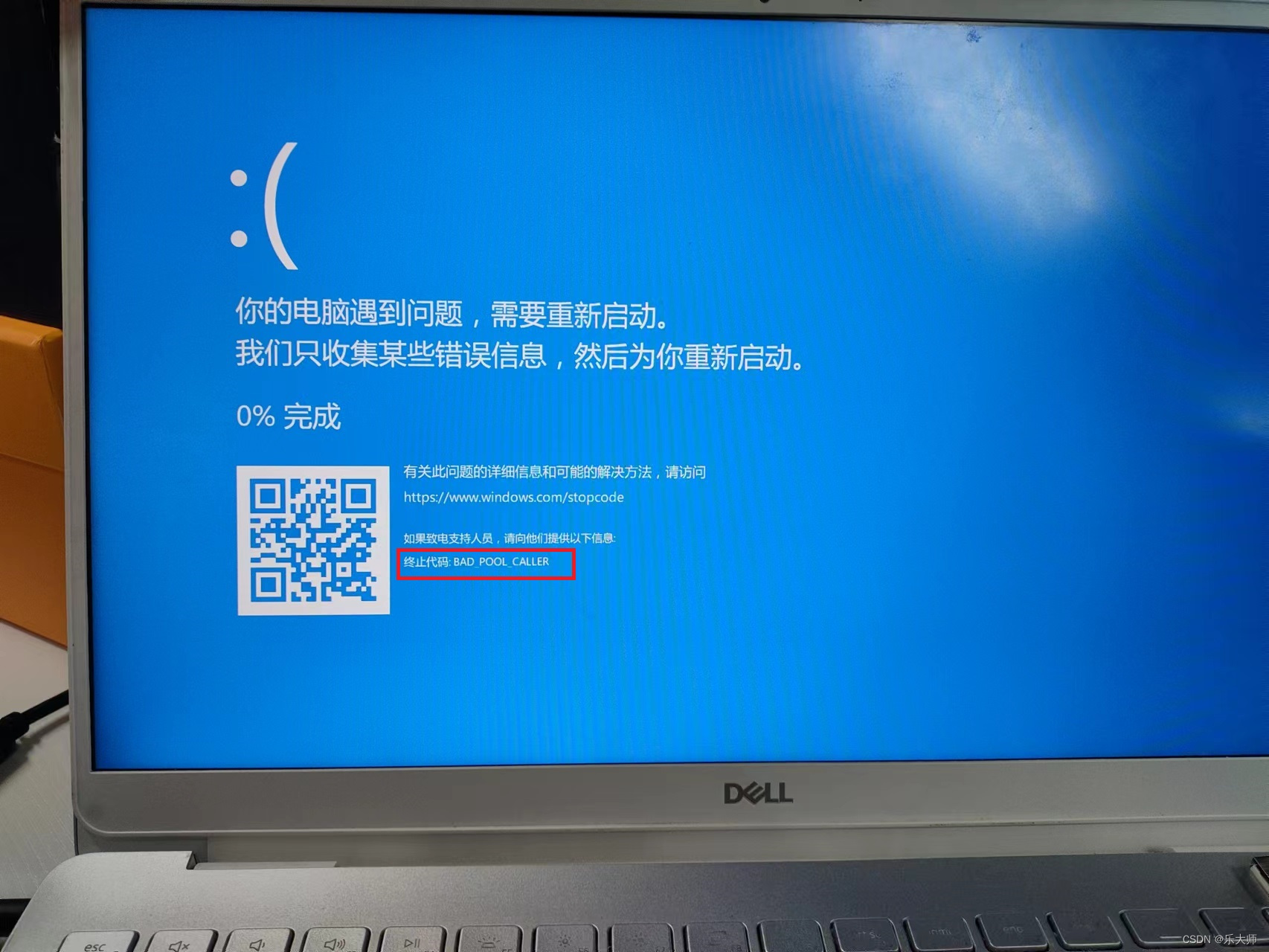
Dell筆記本周期性閃屏故障
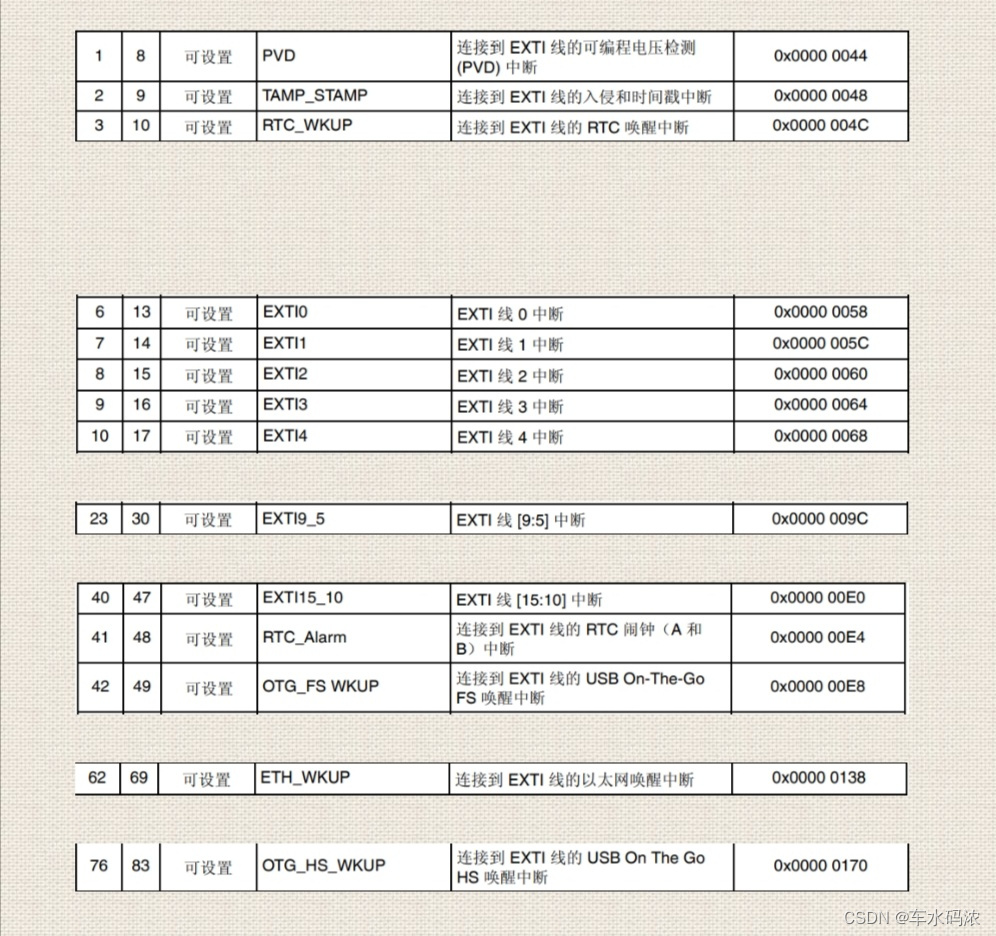
第四篇,STM32中断控制编程
Activereportsjs 3.1 Chinese version | | | activereportsjs 3.1 English version
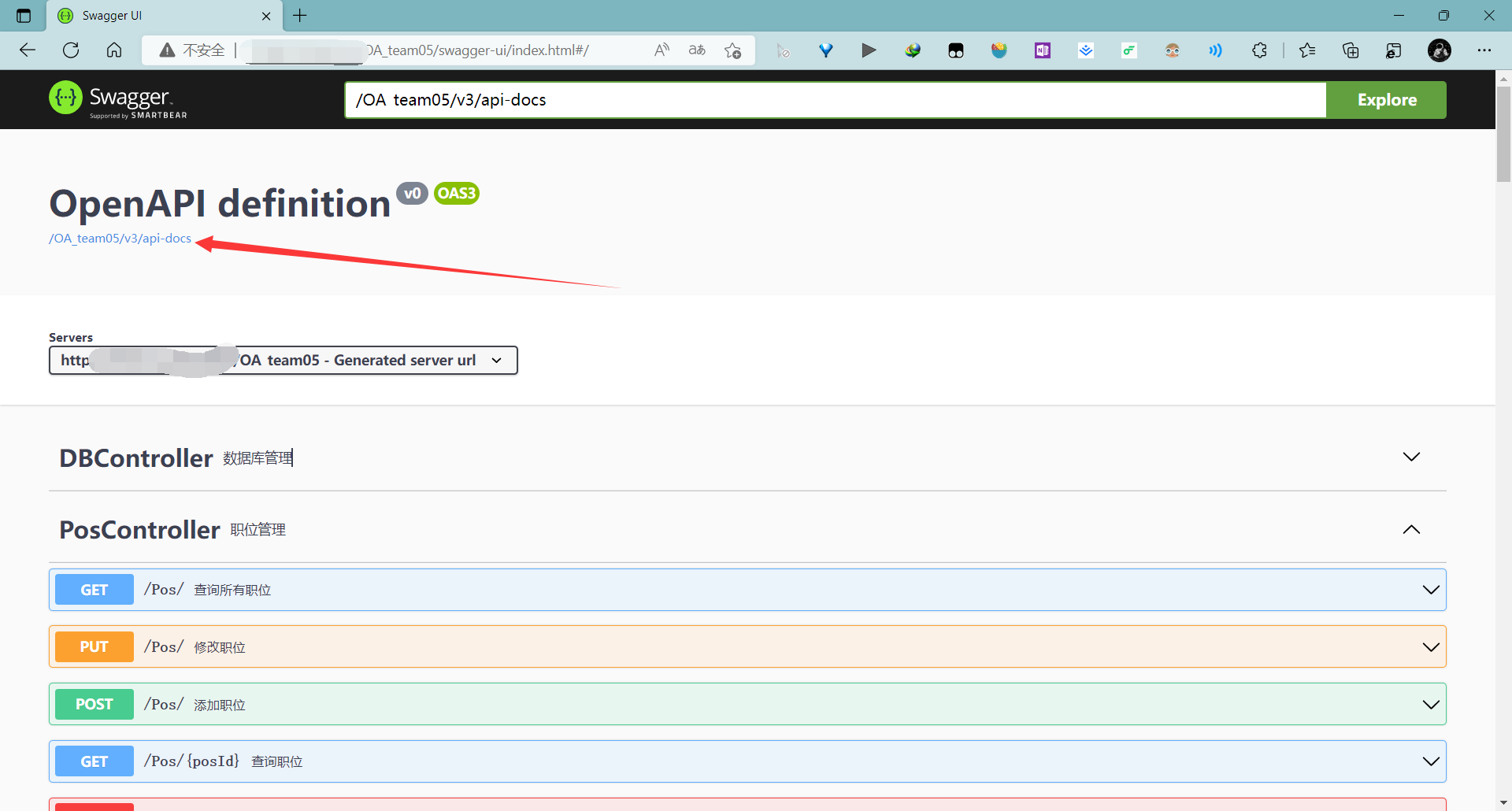
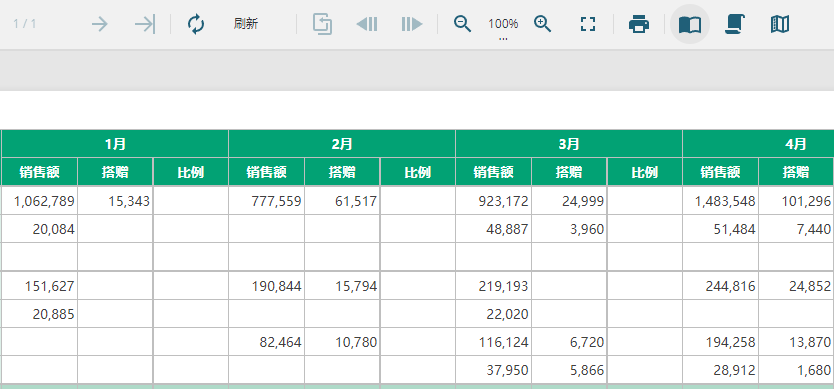
Learn to use code to generate beautiful interface documents!!!
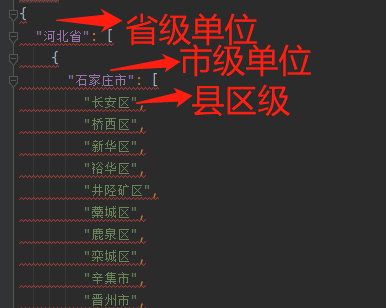
批量获取中国所有行政区域经边界纬度坐标(到县区级别)

Building a dream in the digital era, the Xi'an station of the city chain science and Technology Strategy Summit ended smoothly

.class文件的字节码结构
随机推荐
The printf function is realized through the serial port, and the serial port data reception is realized by interrupt
省市区三级坐标边界数据csv转JSON
Part VI, STM32 pulse width modulation (PWM) programming
【JokerのZYNQ7020】AXI_ EMC。
Learn self 3D representation like ray tracing ego3rt
Address information parsing in one line of code
C# 计算农历日期方法 2022
Learn to use code to generate beautiful interface documents!!!
OSPF configuration command of Huawei equipment
ActiveReportsJS 3.1中文版|||ActiveReportsJS 3.1英文版
Link sharing of STM32 development materials
Dell筆記本周期性閃屏故障
Informatics Olympiad YBT 1171: factors of large integers | 1.6 13: factors of large integers
Chapter 5 DML data operation
实现mysql与ES的增量数据同步
Learning notes 5: ram and ROM
随时随地查看远程试验数据与记录——IPEhub2与IPEmotion APP
「笔记」折半搜索(Meet in the Middle)
Installation of torch and torch vision in pytorch
Zabbix 5.0:通过LLD方式自动化监控阿里云RDS