当前位置:网站首页>2022-06-30 advanced network engineering (XIV) routing strategy - matching tools [ACL, IP prefix list], policy tools [filter policy]
2022-06-30 advanced network engineering (XIV) routing strategy - matching tools [ACL, IP prefix list], policy tools [filter policy]
2022-07-03 19:24:00 【A goose】
Matching tool
ACL( Access control list )
See
Relevant orders supplement
Use time-range Tool set time range
[R1]time-range qyt 8:30 to 17:30 working-day ACL--- Examples of matching time ranges
[R1-acl-basic-2000]rule 5 permit time-range qyt source 1.1.1.1 0 IP-Prefix List(IP The prefix list )
IP The prefix list (IP-Prefix List) Is the network address of the routing entry 、 Mask length as a filter for matching , It can be used when routing protocols publish and receive routes .
differ ACL,IP-Prefix List Can match at the same time IP Address prefix length and mask length , Enhanced the accuracy of matching .

1、ip-prefix-name: Address prefix list name
2、 Serial number : The sequence number of this match in the address prefix list , Match according to the sequence number from small to large
3、 action :permit/deny, The matching mode of the address prefix list is allow / Refuse , Represents a match / Mismatch
4、IP Network segment and mask : The network address matching the route , And limit the number of the first digits of the network address to be strictly matched
5、 Mask range : Match the route prefix length , Matching range of mask length mask-length<=greater-equal-value<=less-equal-value<=32.greater-equal Represents greater than or equal to ,less-equal-value Represents less than or equal to , The minimum value is the mask value set previously , The maximum value is 32. Indicates that the capture set mask value is up to 32 Mask range between .
Strategy tools
Filter-Policy( Filter - Strategy )
Filter-Policy( Filter - Strategy ) It is a very common routing information filtering tool , Be able to receive 、 Release 、 The introduced route is filtered , It can be applied to IS-IS、OSPF、BGP Such agreement .
See
2022-05-25 Advanced network engineering ( 7、 ... and )OSPF- Factors that affect the establishment of neighborhood relations 、 Route revocation 、 Route summary 、 Route filtering 、Silent-Interface、 Message authentication _ Goose blog -CSDN Blog _ospf Message authentication Route aggregation route aggregation is also called route aggregation , That is to aggregate a group of routes with the same prefix into one route , So as to reduce the size of routing table and optimize the utilization of equipment resources , We call this group of routes before convergence as fine routing or detailed routing , The route after aggregation is called aggregation route or aggregation route .OSPF The type of route summary is ABR Execute route summary : Perform route summary for routes between regions . stay ASBR Execute route summary : Perform route summary on the incoming external routes . stay NSSA Area ,ABR It's also execution ASBR A summary of the . It's right 7 After class aggregation, it is converted to 5 class . The relevant orders are in ABR Execute route summary [R1-ospf-1-https://blog.csdn.net/x629242/article/details/124624154#t62022-06-28 Advanced network engineering ( 13、 ... and )IS-IS- Route filtering 、 Route summary 、 authentication 、 influence ISIS The factors of establishing neighborhood relationship 、 Other commands and features _ Goose blog -CSDN Blog IS-IS The protocol and OSPF You can also filter routes , Filter in and out directions respectively . In direction out direction IS-IS The protocol and OSPF Route summary can also be carried out . The level added after the summary indicates the area to be published IS-IS Authentication is an authentication method based on the requirements of network security , By means of IS-IS The authentication field is added in the message to authenticate the message . When the local router receives the message sent by the remote router IS-IS message , If the authentication passwords do not match , Then discard the received message , To achieve the goal of self-protection . Interface authentication : Configure... In the interface view , Yes Level-1 and Level-2 Of Hello Message authentication . District
https://blog.csdn.net/x629242/article/details/125502592#t0 In addition to the above blog posts, you can call the matching tool ACL, You can also call the matching tool IP-Prefix List
for example
[R1]ip ip-prefix qyt index 5 permit 1.1.1.1 24 greater-equal 26 less-equal 30
[R1-ospf-1]filter-policy ip-prefix qyt export Route-Policy( route - Strategy )
Route-Policy It's a strategic tool , be used for Filter routing information , And for the filtered routing information Set routing properties .
One Route-Policy from One or more nodes (Node) constitute , Each node can be a series Conditional statements ( Matching condition ) as well as Execute statement ( Executive action ) Set , These sets are numbered from small to large .
Each node can contain multiple conditional statements . Between multiple conditional statements within a node The relationship is “ And ”, That is, only when all conditional statements are matched can the actions in this node be executed .
The relationship between nodes by “ or ”,route-policy Execute from small to large according to the node number and size , A node in the match will not continue to match downward .
Route-Policy The composition of
One Route-Policy Composed of one or more nodes .
for example
[R1]route-policy qyt permit node 5permit or deny: Appoint Route-Policy The matching mode of nodes is allow or deny .
node: Appoint Route-Policy Node number of . Integer form , The value range is 0~65535.
Each node includes multiple if-match and apply Clause .
for example
[R1-route-policy]if-match ip-prefix qyt
[R1-route-policy]apply cost 10if-match Clause : Define the matching criteria for this node .
apply Clause : Define the operation to be performed on the matched route .
notes :Route-Policy Can be Filter-Policy call
边栏推荐
- 【Proteus仿真】用24C04与1602LCD设计的简易加密电子密码锁
- 第一章:三位阶乘和数,图形点扫描
- Chapter 1: extend the same code decimal sum s (D, n)
- Bad mentality leads to different results
- FBI warning: some people use AI to disguise themselves as others for remote interview
- Day11 ---- 我的页面, 用户信息获取修改与频道接口
- Go home early today
- 【LeetCode】【SQL】刷题笔记
- 2022-06-28 网工进阶(十三)IS-IS-路由过滤、路由汇总、认证、影响ISIS邻居关系建立的因素、其他命令和特性
- 【学术相关】顶级论文创新点怎么找?中国高校首次获CVPR最佳学生论文奖有感...
猜你喜欢
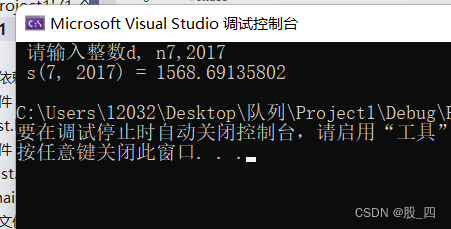
Chapter 1: simplify the same code decimal sum s (D, n)

我们做了一个智能零售结算平台

Ctrip will implement a 3+2 work system in March, with 3 days on duty and 2 days at home every week

2022.2.14 Li Kou - daily question - single element in an ordered array
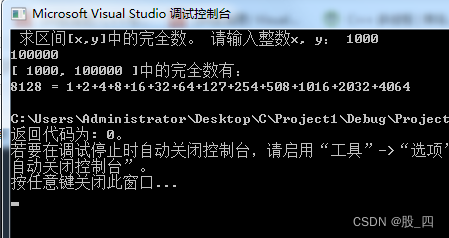
第二章:求长方体数组,指定区间内的完全数,改进指定区间内的完全数

Detailed explanation of shuttle unity interworking principle

Flume learning notes

【疾病识别】基于matlab GUI机器视觉肺癌检测系统【含Matlab源码 1922期】
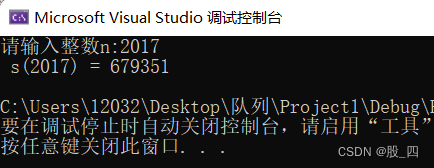
第一章:求奇因数代数和,求同吗小数和s(d, n),简化同码小数和s(d, n),拓广同码小数和s(d, n)
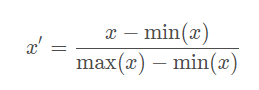
Why should we do feature normalization / standardization?
随机推荐
Use unique_ PTR forward declaration? [repetition] - forward declaration with unique_ ptr? [duplicate]
Thinking about festivals
Chapitre 1: le roi de shehan a mal calculé
P1891 crazy LCM (Euler function)
EGO Planner代码解析bspline_optimizer部分(1)
Go home early today
【Proteus仿真】用24C04与1602LCD设计的简易加密电子密码锁
Record: pymysql is used in pycharm to connect to the database
Bad mentality leads to different results
[leetcode] [SQL] notes
第一章:喝汽水,阶梯电费计算,阶梯电费计算函数,个人所税,求解平方根不等式,简化求解平方根不等式,求解调和级数不等式,解不等式:d<1+1/2-1/3+1/4+1/5-1/6+..士1/n
我们做了一个智能零售结算平台
【光学】基于matlab介电常数计算【含Matlab源码 1926期】
Record the errors reported when running fluent in the simulator
[optics] vortex generation based on MATLAB [including Matlab source code 1927]
Find the median of two positive arrays
Read the paper glodyne global topology preserving dynamic network embedding
第一章: 舍罕王失算
Ego planner code parsing Bspline_ Optimizer section (2)
Php based campus lost and found platform (automatic matching push)