当前位置:网站首页>Analysis of tars source code 1
Analysis of tars source code 1
2022-07-04 06:36:00 【Tao song remains the same】
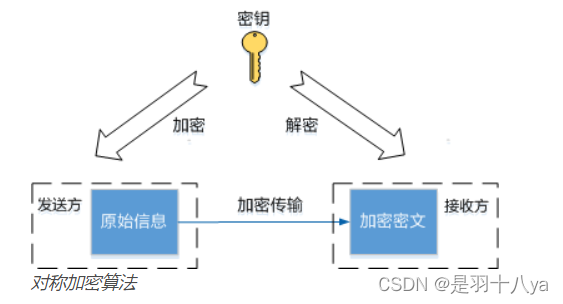
base64 Is a reversible transformation algorithm , Not encryption , Nor is it a hash , Let's take a look at the implementation . I have written before :
#include "util/tc_base64.h"
namespace tars
{
// Base64 Encoding table : Fetch the input data stream every time 6 bit, Use this 6 bit Value (0-63) Look up the table as an index , Output corresponding characters . such , Every time 3 Bytes will be encoded as 4 Characters (3×8 → 4×6); discontent 4 A character with '=' fill .
const char TC_Base64::EnBase64Tab[] = "ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789+/";
// Base64 Decoding table : take 64 The value of printable characters is used as the index , The value obtained by looking up the table ( The scope is 0-63) Connect them in turn to get the decoding result .
// Decoding table size by 256, Illegal characters will be decoded into ASCII 0
const char TC_Base64::DeBase64Tab[] =
{
0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
62, // '+'
0, 0, 0,
63, // '/'
52, 53, 54, 55, 56, 57, 58, 59, 60, 61, // '0'-'9'
0, 0, 0, 0, 0, 0, 0,
0, 1, 2, 3, 4, 5, 6, 7, 8, 9, 10, 11, 12,
13, 14, 15, 16, 17, 18, 19, 20, 21, 22, 23, 24, 25, // 'A'-'Z'
0, 0, 0, 0, 0, 0,
26, 27, 28, 29, 30, 31, 32, 33, 34, 35, 36, 37, 38,
39, 40, 41, 42, 43, 44, 45, 46, 47, 48, 49, 50, 51, // 'a'-'z'
0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0
};
string TC_Base64::encode(const string &data, bool bChangeLine/* = false*/)
{
if(data.empty())
return "";
// Let the original string length be a, The results include carriage return, line feed and '/0', The final length is (a/3+1)*4+(a/3+1)*4*2/76+1, about 1.369*a+6
char *pDst = NULL;
int iBufSize = (int)(data.size()*1.4) + 6;
pDst = new char[iBufSize];
if(pDst == NULL)
return "";
int iDstLen = encode((unsigned char*)data.c_str(), data.size(), pDst, bChangeLine);
string ret(pDst,iDstLen);
delete [] pDst;
return ret;
}
string TC_Base64::decode(const string &data)
{
if(data.empty())
return "";
unsigned char *pDst = NULL;
pDst = new unsigned char[data.size()];
if(pDst == NULL)
return "";
int iDstLen = decode(data.c_str(), data.size(), pDst);
string ret((char*)pDst,iDstLen);
delete [] pDst;
return ret;
}
int TC_Base64::encode(const unsigned char* pSrc, int nSrcLen, char* pDst, bool bChangeLine/* = false*/)
{
unsigned char c1, c2, c3;
int nDstLen = 0;
int nLineLen = 0;
int nDiv = nSrcLen / 3;
int nMod = nSrcLen % 3;
// Every time 3 Bytes , Code as 4 Characters
for (int i = 0; i < nDiv; i ++)
{
c1 = *pSrc++;
c2 = *pSrc++;
c3 = *pSrc++;
*pDst++ = EnBase64Tab[c1 >> 2];
*pDst++ = EnBase64Tab[((c1 << 4) | (c2 >> 4)) & 0x3f];
*pDst++ = EnBase64Tab[((c2 << 2) | (c3 >> 6)) & 0x3f];
*pDst++ = EnBase64Tab[c3 & 0x3f];
nLineLen += 4;
nDstLen += 4;
// relevant RFC More than per line in 76 You need to add carriage return line feed
if (bChangeLine && nLineLen > 72)
{
*pDst++ = '\r';
*pDst++ = '\n';
nLineLen = 0;
nDstLen += 2;
}
}
// Encode the remaining bytes
if (nMod == 1)
{
c1 = *pSrc++;
*pDst++ = EnBase64Tab[(c1 & 0xfc) >> 2];
*pDst++ = EnBase64Tab[((c1 & 0x03) << 4)];
*pDst++ = '=';
*pDst++ = '=';
nLineLen += 4;
nDstLen += 4;
}
else if (nMod == 2)
{
c1 = *pSrc++;
c2 = *pSrc++;
*pDst++ = EnBase64Tab[(c1 & 0xfc) >> 2];
*pDst++ = EnBase64Tab[((c1 & 0x03) << 4) | ((c2 & 0xf0) >> 4)];
*pDst++ = EnBase64Tab[((c2 & 0x0f) << 2)];
*pDst++ = '=';
nDstLen += 4;
}
// Output with a terminator
*pDst = '\0';
return nDstLen;
}
int TC_Base64::decode(const char* pSrc, int nSrcLen, unsigned char* pDst)
{
int nDstLen; // Output character count
int nValue; // Integer used for decoding
int i;
i = 0;
nDstLen = 0;
// take 4 Characters , Decode to a long integer , Then through the shift, we get 3 Bytes
while (i < nSrcLen)
{
// Skip carriage return and line feed
if (*pSrc != '\r' && *pSrc!='\n')
{
if(i + 4 > nSrcLen) // The string to be decoded is illegal , Stop decoding immediately and return
break;
nValue = DeBase64Tab[int(*pSrc++)] << 18;
nValue += DeBase64Tab[int(*pSrc++)] << 12;
*pDst++ = (nValue & 0x00ff0000) >> 16;
nDstLen++;
if (*pSrc != '=')
{
nValue += DeBase64Tab[int(*pSrc++)] << 6;
*pDst++ = (nValue & 0x0000ff00) >> 8;
nDstLen++;
if (*pSrc != '=')
{
nValue += DeBase64Tab[int(*pSrc++)];
*pDst++ =nValue & 0x000000ff;
nDstLen++;
}
}
i += 4;
}
else
{
pSrc++;
i++;
}
}
// Output with a terminator
*pDst = '\0';
return nDstLen;
}
}边栏推荐
- MySQL information_ Schema database
- [March 3, 2019] MAC starts redis
- Learn about the Internet of things protocol WiFi ZigBee Bluetooth, etc. --- WiFi and WiFi protocols start from WiFi. What do we need to know about WiFi protocol itself?
- JSON web token -- comparison between JWT and traditional session login authentication
- What is the sheji principle?
- tars源码分析之10
- 8. Factory method
- Overview of convolutional neural network structure optimization
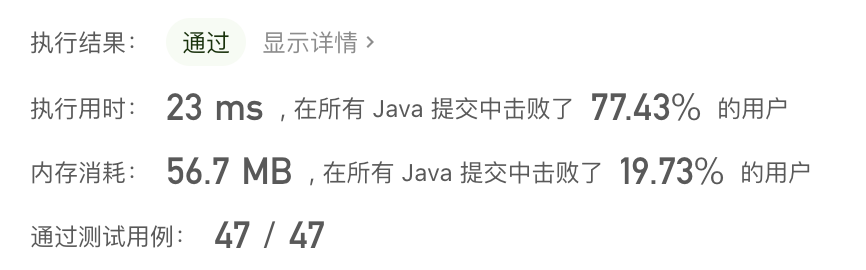
- leetcode 310. Minimum Height Trees
- JSON Web Token----JWT和传统session登录认证对比
猜你喜欢
Native Cloud - SSH articles must be read on Cloud (used for Remote Login to Cloud Server)

198. House raiding
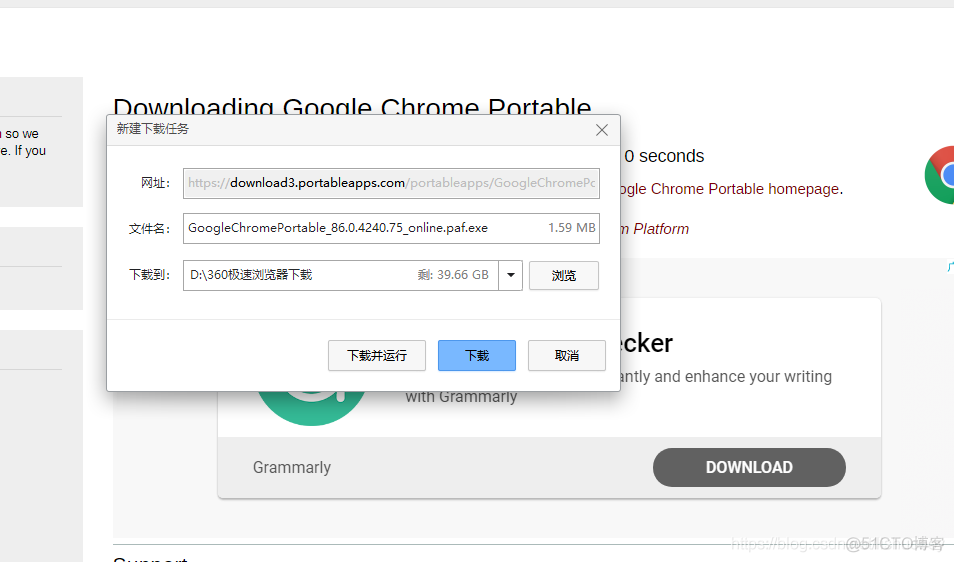
GoogleChromePortable 谷歌chrome浏览器便携版官网下载方式
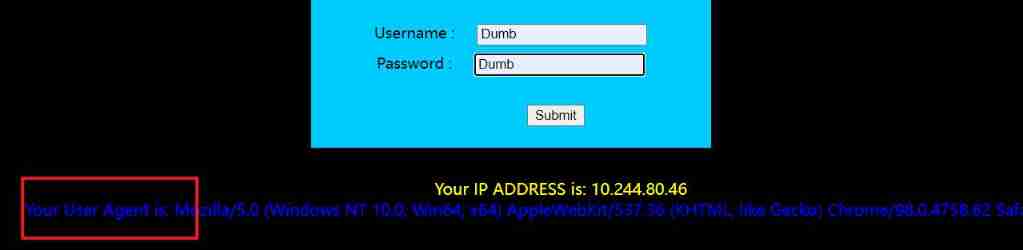
SQL injection SQL lab 11~22
Sword finger offer II 038 Daily temperature
AWT common components, FileDialog file selection box
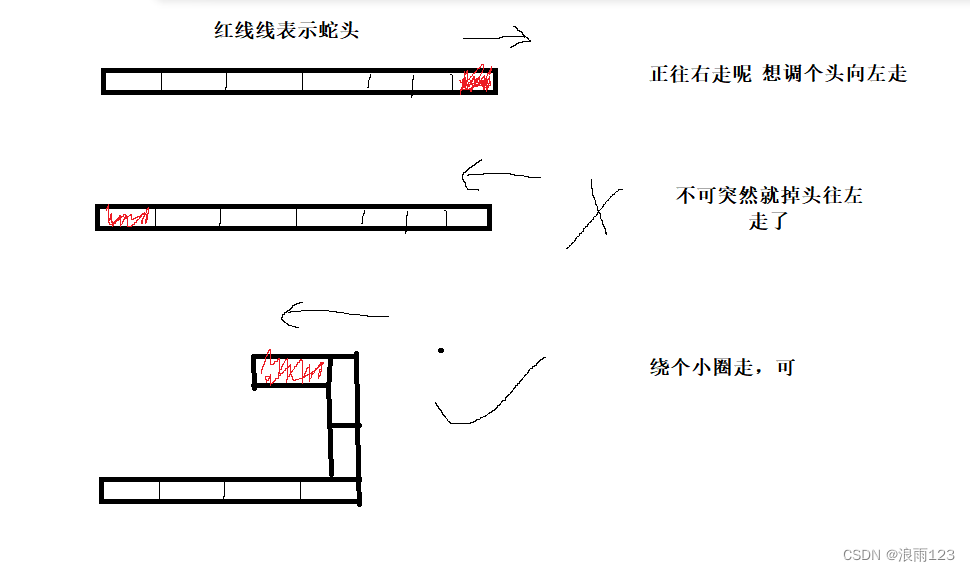
C实现贪吃蛇小游戏
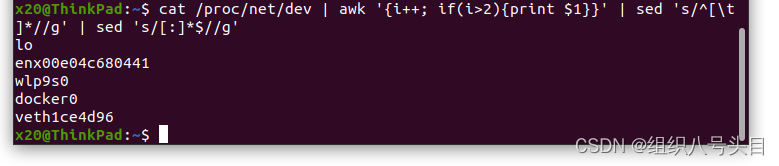
实用的小工具指令
![[backpack DP] backpack problem](/img/7e/1ead6fd0ab61806ce971e1612b4ed6.jpg)
[backpack DP] backpack problem
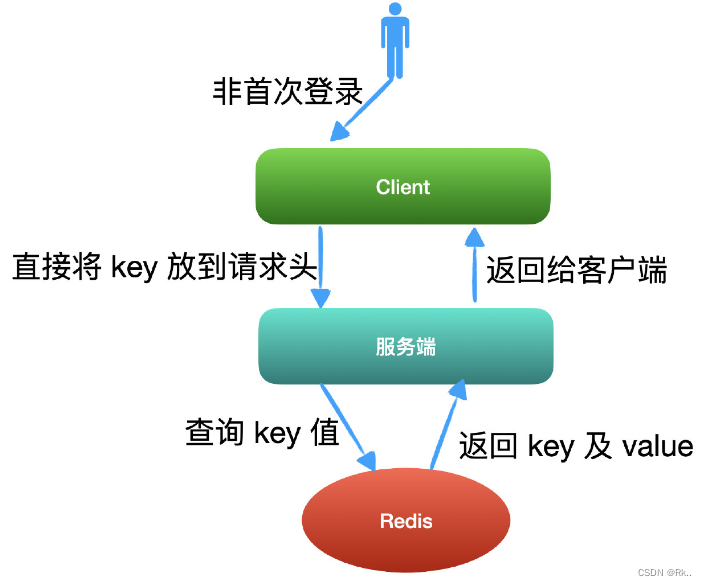
JSON Web Token----JWT和传统session登录认证对比
随机推荐
What is the sheji principle?
JSON Web Token----JWT和传统session登录认证对比
Lightroom import picture gray / Black rectangular multi display
What is the "relative dilemma" in cognitive fallacy?
Realize IIC data / instruction interaction with micro batg135
QT releases multilingual International Translation
Is the insurance annuity product worth buying? Is there a hole?
The width of the picture in rich text used by wechat applet exceeds the problem
Distributed cap theory
JSON Web Token----JWT和傳統session登錄認證對比
leetcode 310. Minimum Height Trees
Vant --- detailed explanation and use of list component in vant
分布式CAP理论
C實現貪吃蛇小遊戲
Explain in one sentence what social proof is
Invalid revision: 3.18.1-g262b901-dirty
MySQL installation and configuration
如何实现视频平台会员多账号登录
Reading notes of Clickhouse principle analysis and Application Practice (4)
ORICO ORICO outdoor power experience, lightweight and portable, the most convenient office charging station