当前位置:网站首页>7. Agency mode
7. Agency mode
2022-07-04 06:20:00 【Muzi's day and night】
package proxyPattern;
import sun.net.www.content.image.gif;
/**
* Common implementation
*
* scene : tom know dany dany Meet Lily however tom I don't know Lily however however tom I want to go after lily Just want to give lily a present
*
* @author LiMing E-mail:[email protected]
* @date 2017 year 6 month 11 Japan Afternoon 7:44:03
*/
public class Commonly {
public static void main(String[] args) {
Girl girl = new Girl(" lily ");
Pursuit tom = new Pursuit(girl); // There's a problem here tom I don't know Lily Not directly accessible
// Send roses
tom.giveRose();
//
}
}
// handsome guy
class Pursuit {
Girl girl;
public Pursuit(Girl girl) {
this.girl = girl;
}
public void giveRose(){
System.out.println(" send "+girl.name+" Rose ");
}
public void giveLollipop(){
System.out.println(" send "+girl.name+" lollipop ");
}
}
// Cool mushroom
class Girl {
String name;
public Girl() {
}
public Girl(String name) {
this.name = name;
}
}
- 1.
- 2.
- 3.
- 4.
- 5.
- 6.
- 7.
- 8.
- 9.
- 10.
- 11.
- 12.
- 13.
- 14.
- 15.
- 16.
- 17.
- 18.
- 19.
- 20.
- 21.
- 22.
- 23.
- 24.
- 25.
- 26.
- 27.
- 28.
- 29.
- 30.
- 31.
- 32.
- 33.
- 34.
- 35.
- 36.
- 37.
- 38.
- 39.
- 40.
- 41.
- 42.
- 43.
- 44.
- 45.
- 46.
- 47.
- 48.
- 49.
- 50.
package proxyPattern;
/**
* The proxy pattern The proxy pattern : Provides a proxy for other objects to control access to this object
*
*
* Remote agent :
* To provide local representation of an object in different address spaces . This hides the fact that an object exists in different address spaces (webService )
* The remote proxy provides a local representation object for an object located in a different address space , This different address space can be in this machine ,
* It can also be in another machine , Remote agent has a cool name : Ambassador .
* Local applications -》 Local agent -》 Server agent -》 Remote services
*
* Virtual agent :
* Create expensive objects as needed . It takes a long time to store objects through her ( For example, when a web page loads an image, it uses an object to store the address and name of the image But don't load pictures in time )
*
* Security agent :
* It is used to control the access rights of real objects ( Objects have different access rights )
*
* Smart agents :
* Intelligent guidance When calling real objects Agents deal with other things
*
* other xx agent Welcome to add Correction and correction
* @author LiMing E-mail:[email protected]
* @date 2017 year 6 month 11 Japan Afternoon 7:43:35
*/
public class ProxyPattern {
public static void main(String[] args) {
Girls girls = new Girls(" lily ");
//tom
Pursuits pursuits = new Pursuits(girls);
//dany
Proxy proxy = new Proxy(pursuits);
// Send lollipops
proxy.giveLollipops();
}
}
// Give gifts
interface IGiveGift {
abstract public void giveRoses();
abstract public void giveLollipops();
}
class Pursuits implements IGiveGift {
Girls girls;
public Pursuits(Girls girls) {
this.girls = girls;
}
public void giveRoses() {
System.out.println(" send " + girls.name + " Rose ");
}
public void giveLollipops() {
System.out.println(" send " + girls.name + " lollipop ");
}
}
// proxy class
class Proxy implements IGiveGift {
Pursuits pursuits;
public Proxy() {
}
public Proxy(Pursuits pursuits) {
this.pursuits = pursuits;
}
public void giveRoses() {
pursuits.giveRoses();
}
public void giveLollipops() {
pursuits.giveLollipops();
}
}
// Cool mushroom
class Girls {
String name;
public Girls() {
}
public Girls(String name) {
this.name = name;
}
}
- 1.
- 2.
- 3.
- 4.
- 5.
- 6.
- 7.
- 8.
- 9.
- 10.
- 11.
- 12.
- 13.
- 14.
- 15.
- 16.
- 17.
- 18.
- 19.
- 20.
- 21.
- 22.
- 23.
- 24.
- 25.
- 26.
- 27.
- 28.
- 29.
- 30.
- 31.
- 32.
- 33.
- 34.
- 35.
- 36.
- 37.
- 38.
- 39.
- 40.
- 41.
- 42.
- 43.
- 44.
- 45.
- 46.
- 47.
- 48.
- 49.
- 50.
- 51.
- 52.
- 53.
- 54.
- 55.
- 56.
- 57.
- 58.
- 59.
- 60.
- 61.
- 62.
- 63.
- 64.
- 65.
- 66.
- 67.
- 68.
- 69.
- 70.
- 71.
- 72.
- 73.
- 74.
- 75.
- 76.
- 77.
- 78.
- 79.
- 80.
- 81.
- 82.
- 83.
- 84.
- 85.
- 86.
- 87.
- 88.
- 89.
- 90.
- 91.
- 92.
- 93.
- 94.
- 95.
边栏推荐
- Tf/pytorch/cafe-cv/nlp/ audio - practical demonstration of full ecosystem CPU deployment - Intel openvino tool suite course summary (Part 2)
- How to expand all collapse panels
- Learn about the Internet of things protocol WiFi ZigBee Bluetooth, etc. --- WiFi and WiFi protocols start from WiFi. What do we need to know about WiFi protocol itself?
- High performance parallel programming and optimization | lesson 02 homework at home
- 27-31. Dependency transitivity, principle
- Grounding relay dd-1/60
- QT 获取随机颜色值设置label背景色 代码
- Matlab remainder
- 配置交叉编译工具链和环境变量
- How to implement lazy loading in El select (with search function)
猜你喜欢
Tf/pytorch/cafe-cv/nlp/ audio - practical demonstration of full ecosystem CPU deployment - Intel openvino tool suite course summary (Part 2)
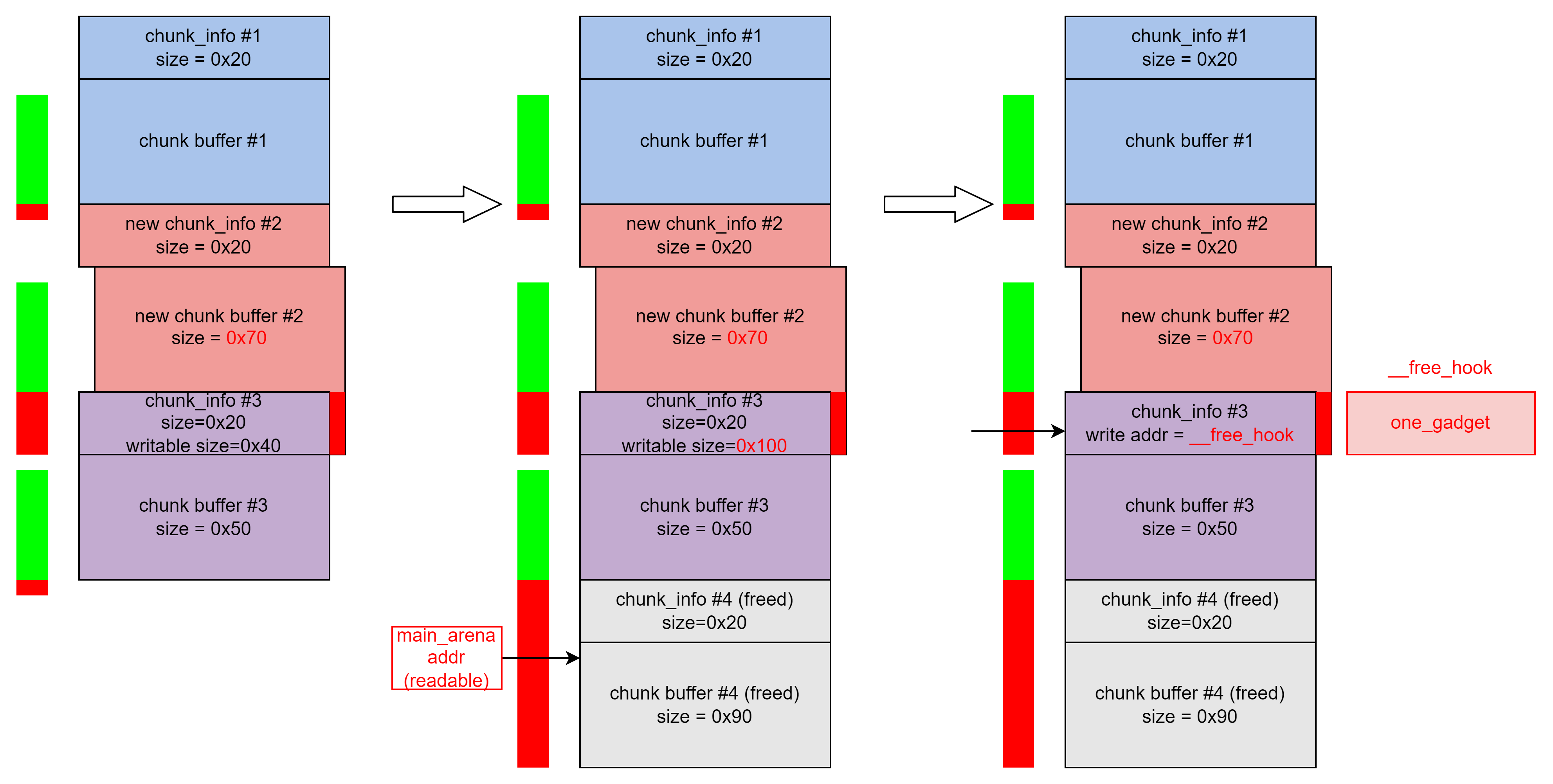
buuctf-pwn write-ups (8)

The end of the Internet is rural revitalization
【无标题】

LayoutManager布局管理器:FlowLayout、BorderLayout、GridLayout、GridBagLayout、CardLayout、BoxLayout
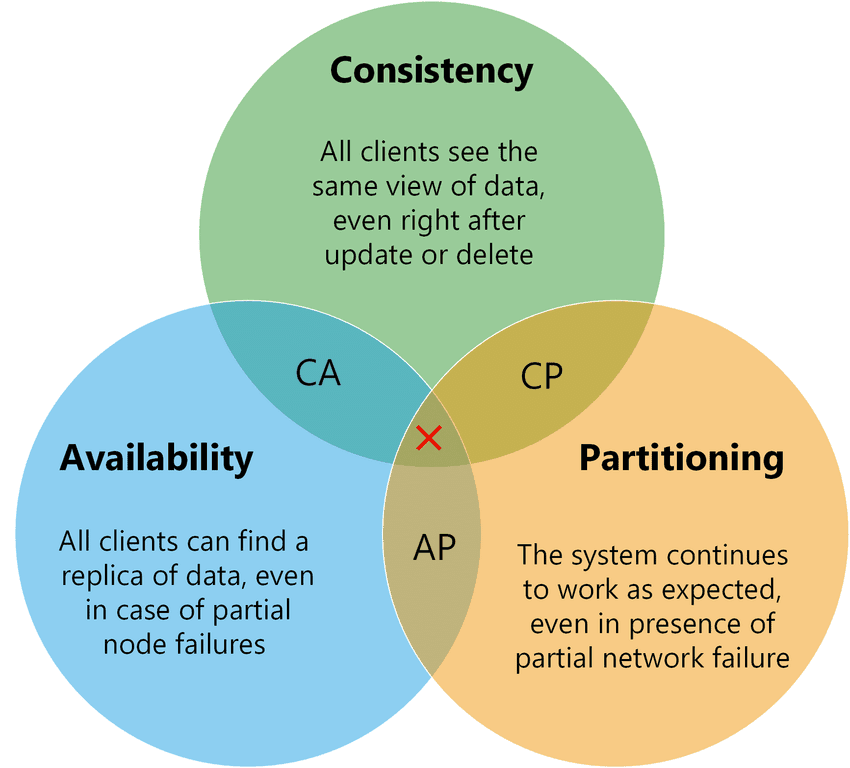
分布式CAP理论
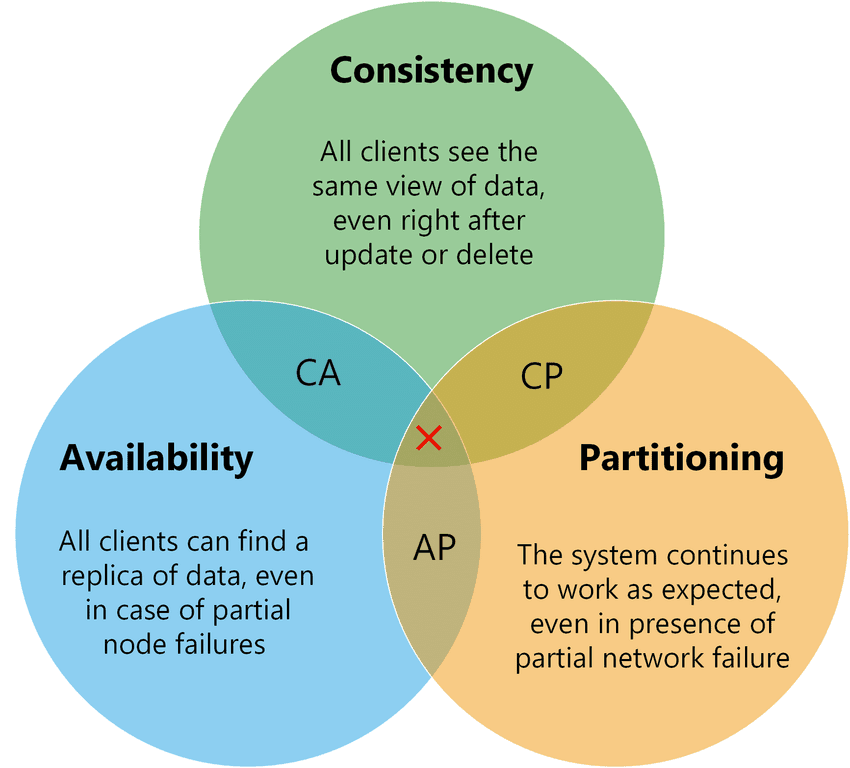
Distributed cap theory
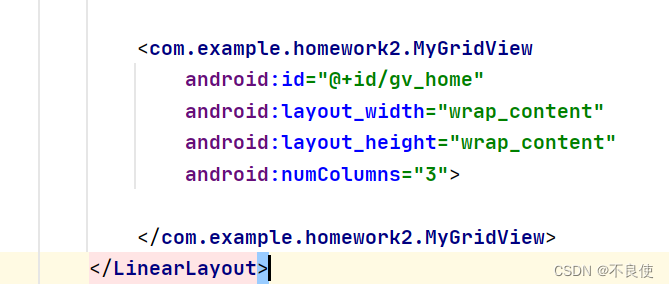
Gridview出现滚动条,组件冲突,如何解决
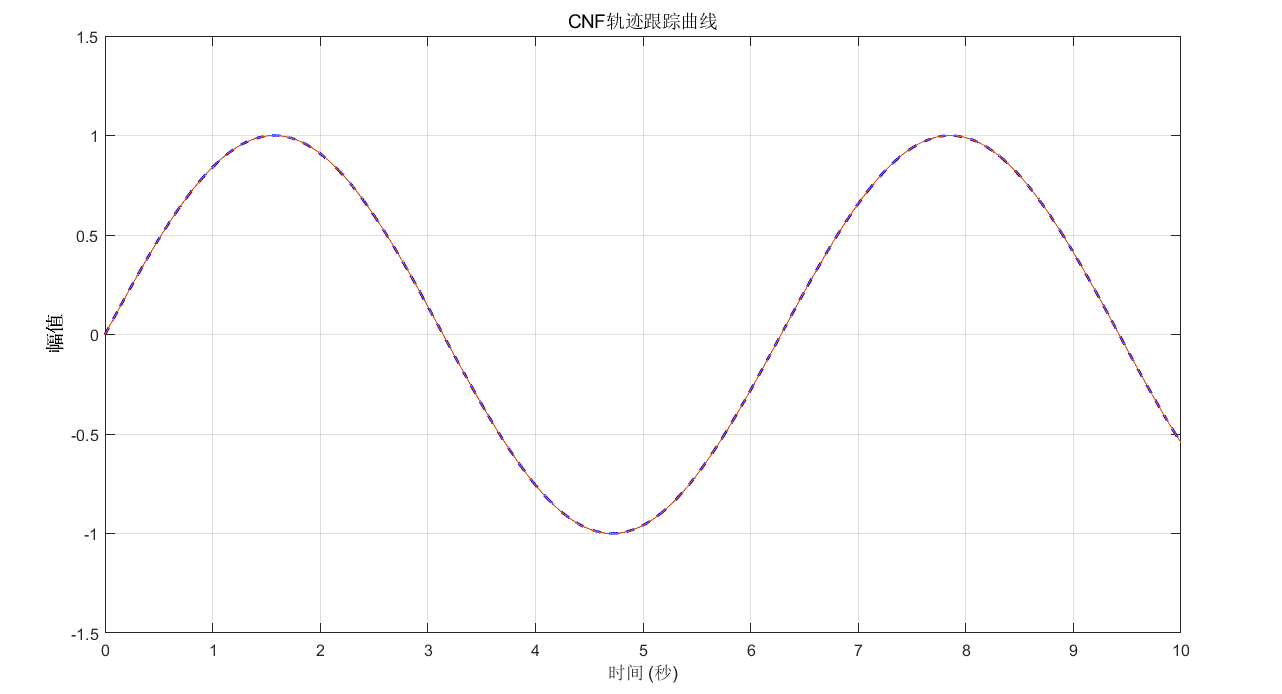
Compound nonlinear feedback control (2)
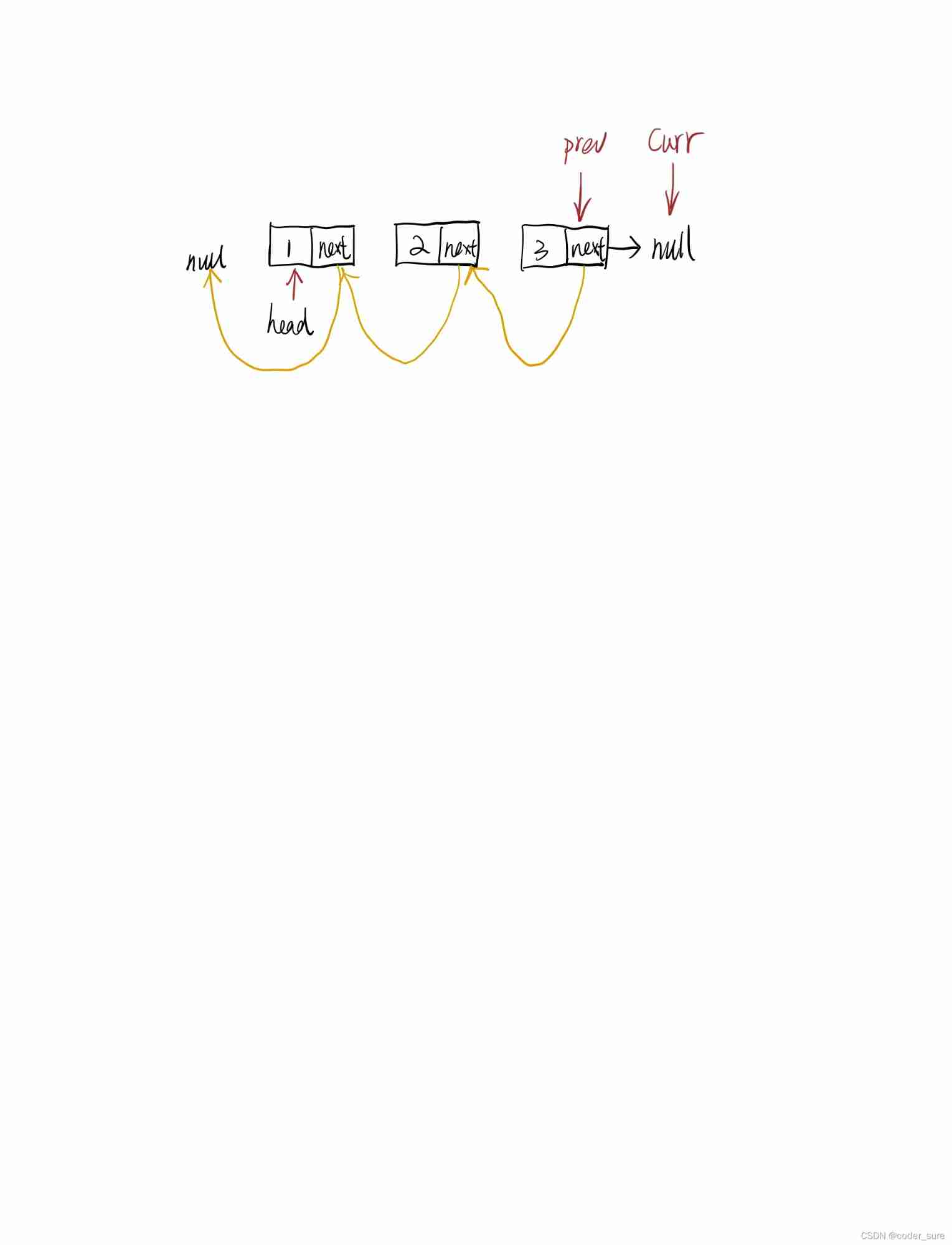
Leetcode question brushing record | 206_ Reverse linked list
随机推荐
Which water in the environment needs water quality monitoring
17-18. Dependency scope and life cycle plug-ins
Learning multi-level structural information for small organ segmentation
Considerations for testing a website
STC8H开发(十二): I2C驱动AT24C08,AT24C32系列EEPROM存储
Practical gadget instructions
MySQL information_ Schema database
双色球案例
lightroom 导入图片灰色/黑色矩形 多显示器
HMS v1.0 appointment. PHP editid parameter SQL injection vulnerability (cve-2022-25491)
Notes and notes
Kubernets first meeting
After the festival, a large number of people change careers. Is it still time to be 30? Listen to the experience of the past people
24 magicaccessorimpl can access the debugging of all methods
Leakage detection relay jy82-2p
Fast power (template)
Webrtc quickly set up video call and video conference
Configure cross compilation tool chain and environment variables
2022.7.3-----leetcode. five hundred and fifty-six
Kubernets first meeting