当前位置:网站首页>[Jianzhi offer] 62 The last remaining number in the circle
[Jianzhi offer] 62 The last remaining number in the circle
2022-07-05 16:58:00 【LuZhouShiLi】
The finger of the sword Offer 62. The last number in the circle
subject
0,1,···,n-1 this n Number in a circle , From numbers 0 Start , Delete the... From this circle every time m A digital ( Delete and count from the next number ). Find the last number left in the circle .
for example ,0、1、2、3、4 this 5 Numbers make a circle , From numbers 0 Start deleting the 3 A digital , Before deleting 4 The numbers in turn are 2、0、4、1, So the last remaining number is 3.
Ideas
- Create a list Simulate circular linked list
- Add all elements to list in
- Every time m Step . Remove elements , Pay attention to the residual operation
Code
class Solution {
public int lastRemaining(int n, int m) {
// Create a circular linked list to simulate a circle
ArrayList<Integer> list = new ArrayList<>(n);
for(int i = 0; i < n; i++)
{
list.add(i);
}
int idx = 0;
while(n > 1)
{
idx = (idx + m - 1) % n;// Every time I go M Step Remainder Because it's a ring
list.remove(idx);
n--;
}
return list.get(0);
}
}
边栏推荐
- Data access - entityframework integration
- 二叉树相关OJ题
- 【729. 我的日程安排表 I】
- 【 brosser le titre 】 chemise culturelle de l'usine d'oies
- 2020-2022 two-year anniversary of creation
- 解决CMakeList find_package找不到Qt5,找不到ECM
- What is ROM
- Flet tutorial 12 stack overlapping to build a basic introduction to graphic and text mixing (tutorial includes source code)
- 拷贝方式之DMA
- Yarn common commands
猜你喜欢
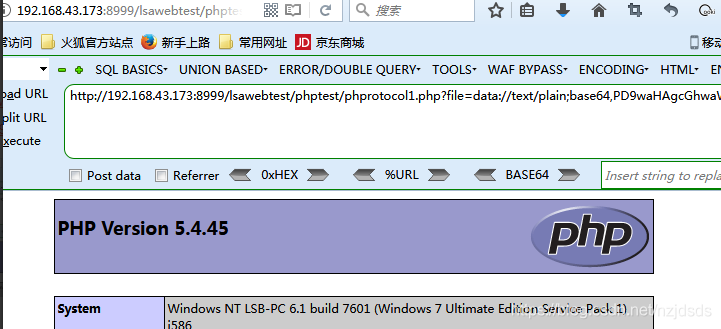
Summary of PHP pseudo protocol of cisp-pte
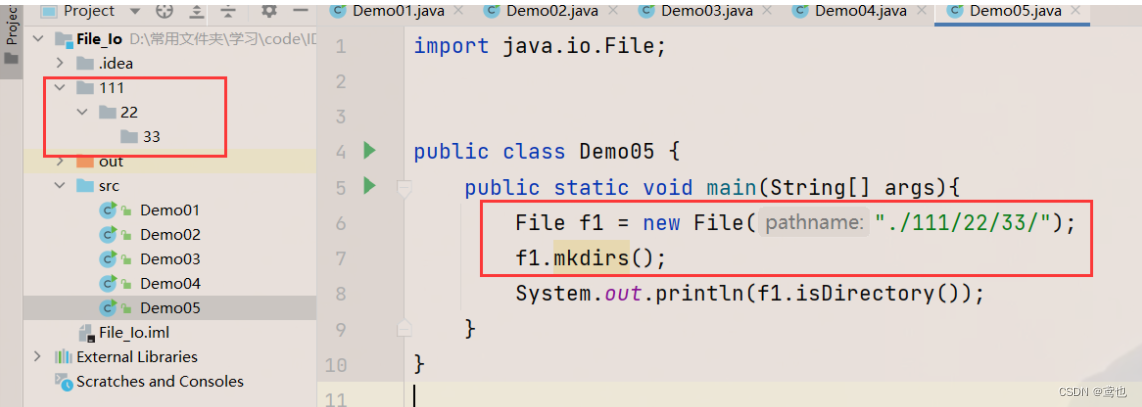
文件操作--I/O
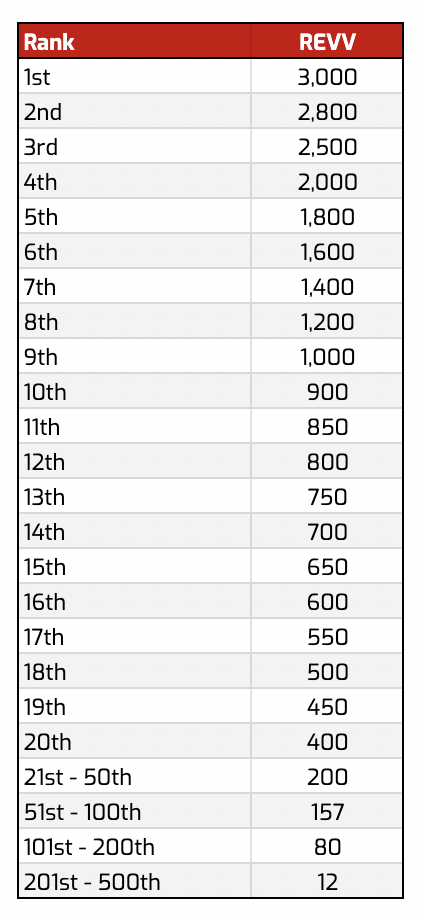
Get ready for the pre-season card game MotoGP ignition champions!
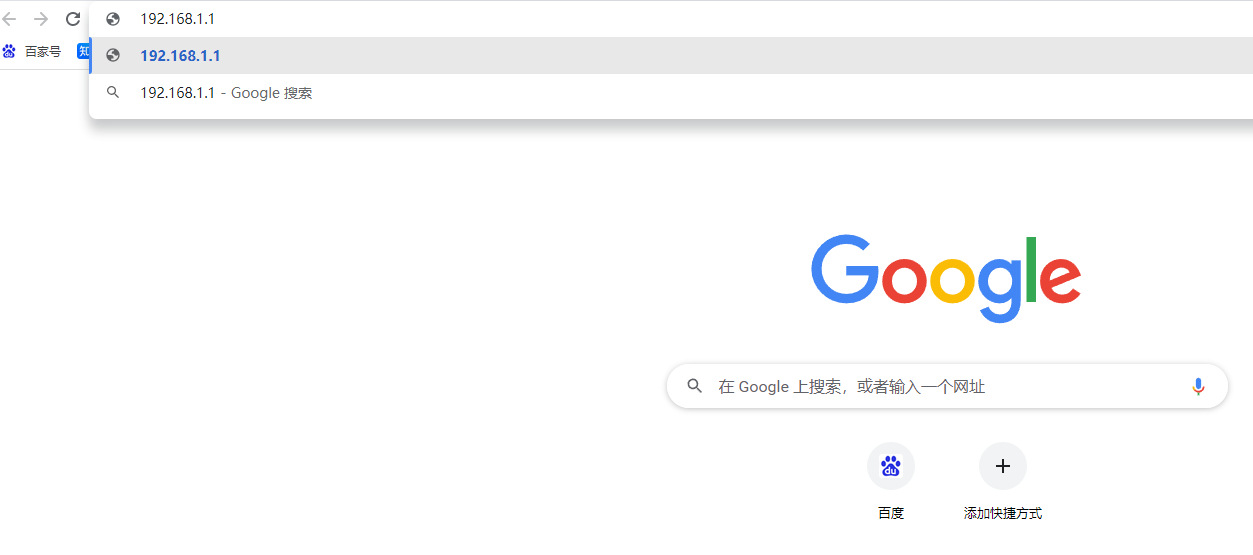
How to set the WiFi password of the router on the computer

Practical example of propeller easydl: automatic scratch recognition of industrial parts
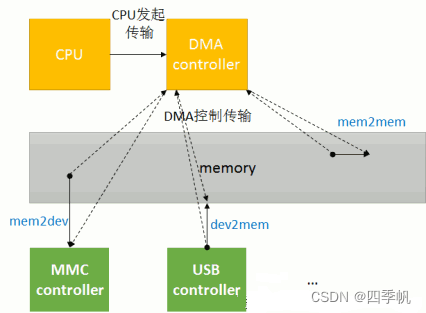
拷贝方式之DMA
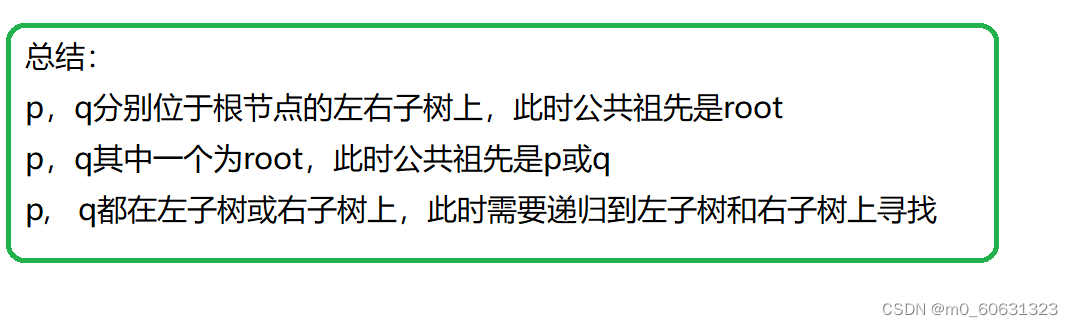
二叉树相关OJ题

PHP人才招聘系统开发 源代码 招聘网站源码二次开发

美国芯片傲不起来了,中国芯片成功在新兴领域夺得第一名
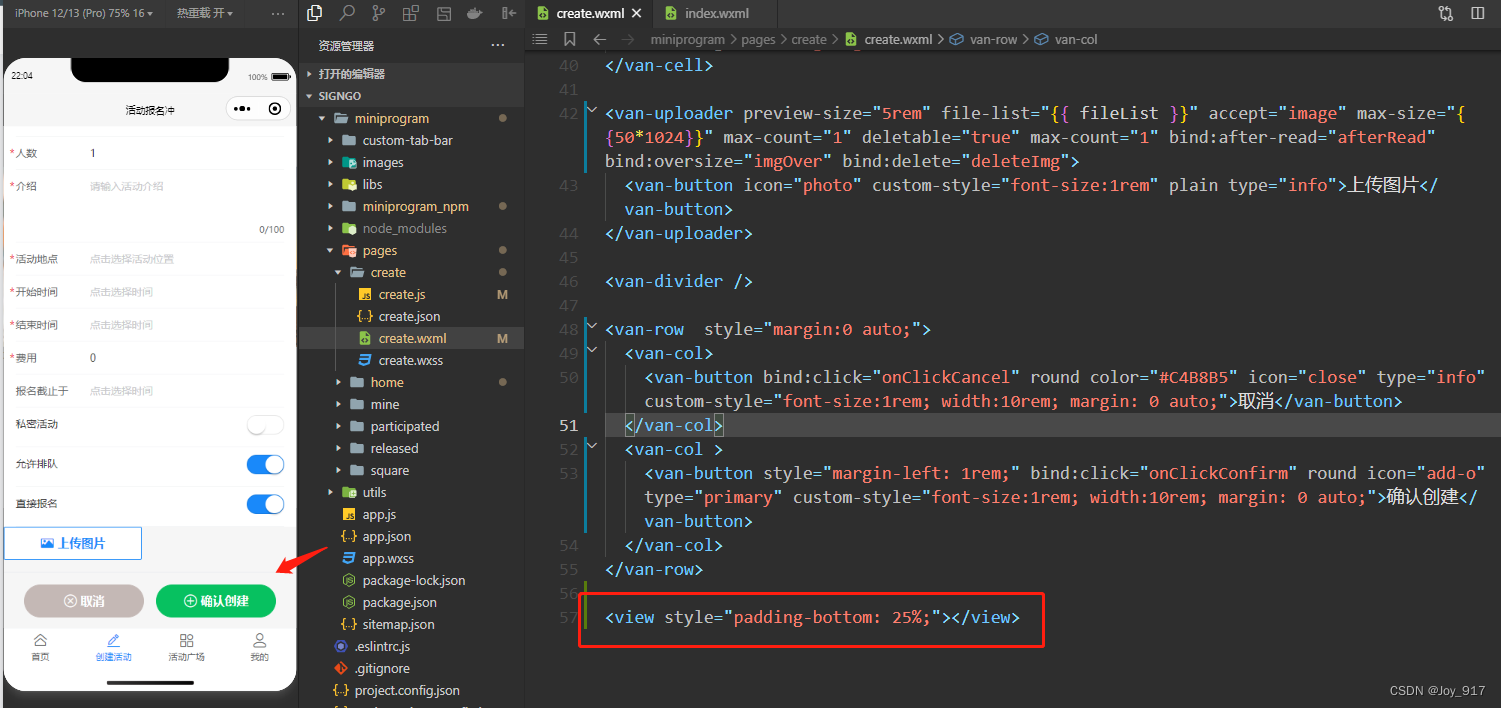
Solution of vant tabbar blocking content
随机推荐
Games101 notes (II)
Solve cmakelist find_ Package cannot find Qt5, ECM cannot be found
What is the difference between EDI license and ICP business license
[es6] 模板字符串内添加if判断或添加三元运算符判断
拷贝方式之DMA
普洛斯数据中心发布DC Brain系统,科技赋能智慧化运营管理
Jarvis OJ Flag
Jarvis OJ simple network management protocol
[deep learning] [original] let yolov6-0.1.0 support the txt reading dataset mode of yolov5
Iphone14 with pill screen may trigger a rush for Chinese consumers
飞桨EasyDL实操范例:工业零件划痕自动识别
Deep dive kotlin synergy (XXI): flow life cycle function
How was the middle table destroyed?
时间戳strtotime前一天或后一天的日期
The two ways of domestic chip industry chain go hand in hand. ASML really panicked and increased cooperation on a large scale
挖财股票开户安全吗?怎么开股票账户是安全?
Android privacy sandbox developer preview 3: privacy, security and personalized experience
Is it safe to open a securities account by mobile phone? Detailed steps of how to buy stocks
How does the outer disk futures platform distinguish formal security?
DenseNet