当前位置:网站首页>UCI and data multiplexing are transmitted on Pusch (Part 4) --small block lengths
UCI and data multiplexing are transmitted on Pusch (Part 4) --small block lengths
2022-07-03 09:39:00 【Communication pawn】
Block length encoding
There are three kinds of codes with small and fast coding length , The first is the length 1, The second is the length 2, The third is the length 3~11. There are different ways to deal with .
1. The length is 1 perhaps 2 The coding

x,y It's a placeholder , When scrambling , Placeholder and normal data processing are different .
This is right with Qm And the corresponding relationship between modulation mode 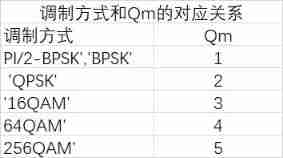
% Encode, with placeholder bits
x = -1;
y = -2;
if length(uciBits)==1 % A=1
if Qm==1
out = uciBits;
else
out = [uciBits; y; repmat(x,Qm-2,1)];
end
else % A=2
c2 = xor(uciBits(1),uciBits(2));
if Qm==1
out = [uciBits; c2];
else
ib = reshape(repmat([uciBits; c2],2,1),2,3);
xb = repmat(x,Qm-2,3);
out = reshape([ib;xb],[],1);
end
end
2. The length is 3~11 Use RM code

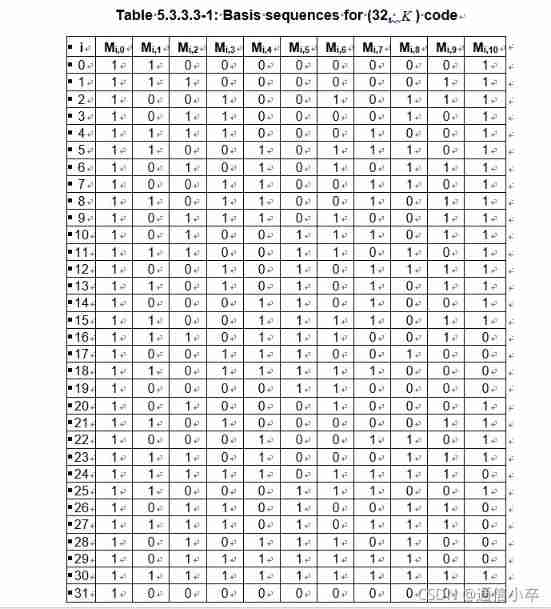
%#codegen
% Table 5.3.3.3-1, Section 5.3.3.3, TS 38.212.
basisSeq = [1 1 0 0 0 0 0 0 0 0 1
1 1 1 0 0 0 0 0 0 1 1
1 0 0 1 0 0 1 0 1 1 1
1 0 1 1 0 0 0 0 1 0 1
1 1 1 1 0 0 0 1 0 0 1
1 1 0 0 1 0 1 1 1 0 1
1 0 1 0 1 0 1 0 1 1 1
1 0 0 1 1 0 0 1 1 0 1
1 1 0 1 1 0 0 1 0 1 1
1 0 1 1 1 0 1 0 0 1 1
1 0 1 0 0 1 1 1 0 1 1
1 1 1 0 0 1 1 0 1 0 1
1 0 0 1 0 1 0 1 1 1 1
1 1 0 1 0 1 0 1 0 1 1
1 0 0 0 1 1 0 1 0 0 1
1 1 0 0 1 1 1 1 0 1 1
1 1 1 0 1 1 1 0 0 1 0
1 0 0 1 1 1 0 0 1 0 0
1 1 0 1 1 1 1 1 0 0 0
1 0 0 0 0 1 1 0 0 0 0
1 0 1 0 0 0 1 0 0 0 1
1 1 0 1 0 0 0 0 0 1 1
1 0 0 0 1 0 0 1 1 0 1
1 1 1 0 1 0 0 0 1 1 1
1 1 1 1 1 0 1 1 1 1 0
1 1 0 0 0 1 1 1 0 0 1
1 0 1 1 0 1 0 0 1 1 0
1 1 1 1 0 1 0 1 1 1 0
1 0 1 0 1 1 1 0 1 0 0
1 0 1 1 1 1 1 1 1 0 0
1 1 1 1 1 1 1 1 1 1 1
1 0 0 0 0 0 0 0 0 0 0];
uciBitsD = cast(uciBits,'double');
out = zeros(32,1);
for idx = 1:length(uciBits)
out = out + uciBitsD(idx).*basisSeq(:,idx);
end
cout = cast(mod(out,2),class(uciBits));
end
边栏推荐
- numpy. Reshape() and resize() functions
- Directory and switching operation in file system
- [solution to the new version of Flink without bat startup file]
- Jetson Nano 自定义启动图标kernel Logo cboot logo
- Usage of pandas to obtain MySQL data
- Apply for domain name binding IP to open port 80 record
- Flink learning notes (VIII) multi stream conversion
- Spark overview
- Leetcode daily question (985. sum of even numbers after queries)
- Design and development of biological instruments
猜你喜欢

Nr-prach:prach format and time-frequency domain

Definition and use of enum in C language

CATIA automation object architecture - detailed explanation of application objects (III) systemservice
文件系统中的目录与切换操作
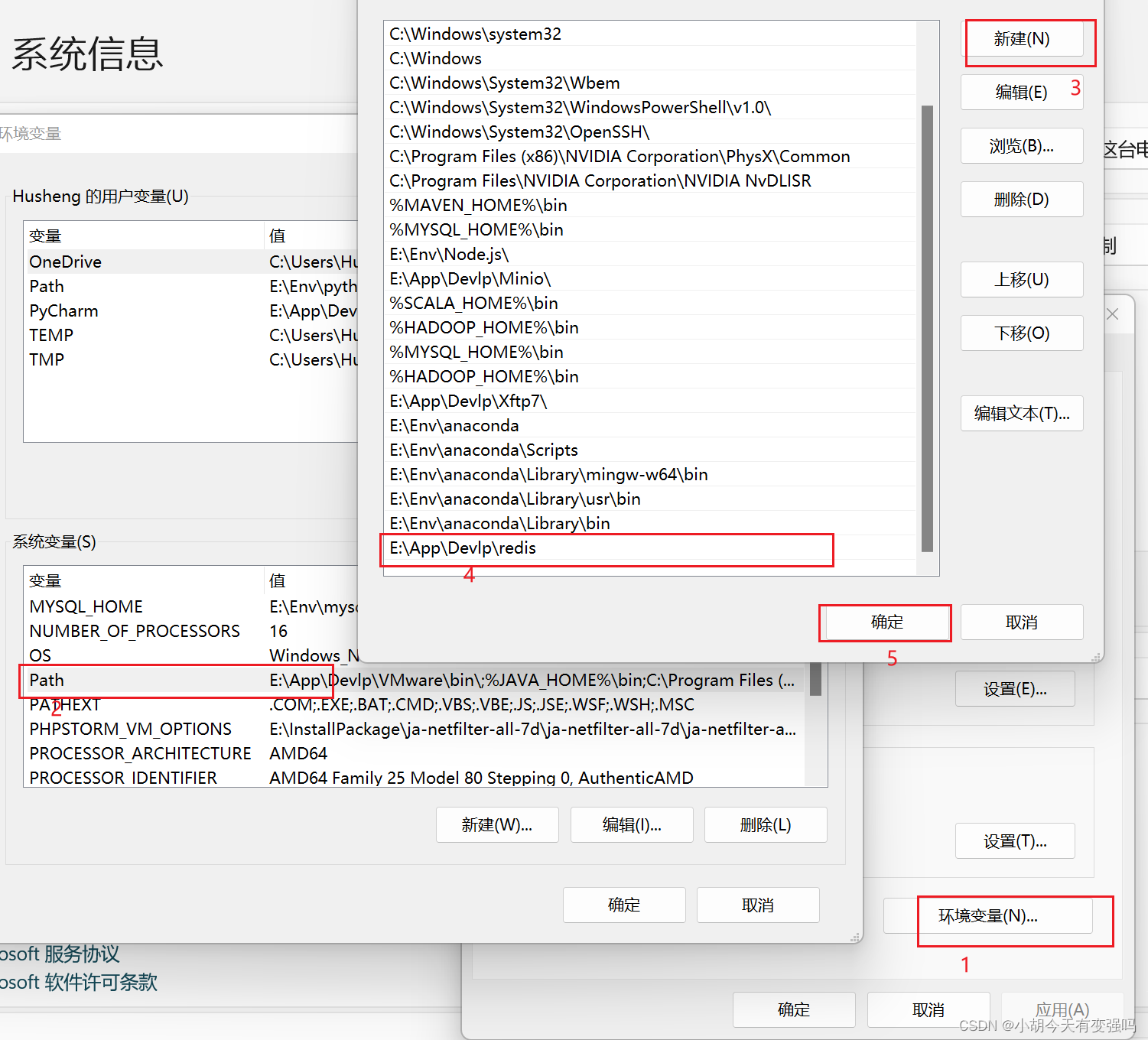
Detailed steps of windows installation redis

Please tell me how to set vscode

PolyWorks script development learning notes (I) - script development environment

Nr-prach: access scenario and access process

Difference of EOF
![[kotlin learning] control flow of higher-order functions -- lambda return statements and anonymous functions](/img/a3/b442508af9b059d279cffb34dee9bf.png)
[kotlin learning] control flow of higher-order functions -- lambda return statements and anonymous functions
随机推荐
The number of weak characters in the game (1996)
Usage of pandas to obtain MySQL data
Equality judgment of long type
Leetcode daily question (1856. maximum subarray min product)
Flink学习笔记(十)Flink容错机制
Flink学习笔记(十一)Table API 和 SQL
Nr-prach: access scenario and access process
Spark structured stream writing Hudi practice
Flink学习笔记(九)状态编程
Flink-CDC实践(含实操步骤与截图)
Patent inquiry website
数字身份验证服务商ADVANCE.AI顺利加入深跨协 推进跨境电商行业可持续性发展
Common software open source protocols
顺利毕业[3]-博客系统 更新中。。。
Implementing distributed lock with redis
LeetCode每日一题(2305. Fair Distribution of Cookies)
MySQL Data Definition Language DDL common commands
Installation and uninstallation of pyenv
Find all possible recipes from given supplies
How MySQL modifies null to not null