当前位置:网站首页>Hedhat firewall
Hedhat firewall
2022-07-05 01:11:00 【weixin_ fifty-one million four hundred and twenty-eight thousan】
The firewall will read the configured policy rules from top to bottom , Immediately after the match is found, the matching work is finished and the behavior defined in the match is executed ( To release or prevent ). If there is no match after reading all the policy rules , Go ahead and implement the default strategy . generally speaking , There are two kinds of firewall policy rules :“ through ”( Let's go ) and “ Block up ”( That is to prevent ). When the default policy of firewall is reject ( Block up ), It's about setting the allow rule ( through ), Otherwise no one can come in ; If the default policy of the firewall is allow , It's about setting rejection rules , Otherwise everyone can come in , Firewall also lost the role of prevention .
iptables The service refers to the policy entries used to process or filter traffic as rules , Multiple rules can form a rule chain , The rule chain is classified according to the location of packet processing , As follows :
Process packets before routing (PREROUTING);
Process incoming packets (INPUT);
Process outgoing packets (OUTPUT);
Process forwarded packets (FORWARD);
Process packets after routing (POSTROUTING).
Generally speaking , The traffic sent from the intranet to the Internet is generally controllable and benign , So the most used is INPUT Rule chain , The rule chain can make it more difficult for hackers to invade the intranet from the external network .
For example, in the community where you live , Property management companies have two provisions : Prohibit hawkers from entering the community ; All kinds of vehicles must be registered when entering the community . Obvious , These two rules should be applied to the front door of the community ( Where the flow must pass ), Not on the security door of every house . According to the matching order of firewall policies mentioned above , There may be many situations . such as , The visitors are vendors , Will be directly rejected by the security of the property company , There is no need to register the vehicle . If visitors enter the main gate of the community in a car , be “ Prohibit hawkers from entering the community ” The first rule of is not matched , So match the second strategy in order , That is, the vehicle needs to be registered . If you are a community resident, you need to enter the main entrance , Then these two provisions will not match , Therefore, the default release policy will be implemented .
however , Only policy rules cannot guarantee the safety of the community , The security guard should also know what actions to take to deal with these matching traffic , such as “ allow ”“ Refuse ”“ registration ”“ Ignore it ”. These actions correspond to iptables The terms of service are ACCEPT( Allow flow through )、REJECT( Reject traffic through )、LOG( Logging information )、DROP( Reject traffic through ).“ Allow flow through ” and “ Logging information ” It's easy to understand , What needs to be emphasized here is REJECT and DROP The difference between . Just DROP Come on , It directly discards traffic and does not respond ;REJECT Then it will reply one more message after rejecting the traffic “ The message has been received , But it was thrown away ” Information , So that the traffic sender can clearly see the response information of data rejected .
边栏推荐
- Pycharm professional download and installation tutorial
- Pandora IOT development board learning (RT thread) - Experiment 4 buzzer + motor experiment [key external interrupt] (learning notes)
- Query for Boolean field as "not true" (e.g. either false or non-existent)
- Summary of the function and usage of const, volatile and restrict
- Basic operations of database and table ----- delete index
- 资深测试/开发程序员写下无bug?资历(枷锁)不要惧怕错误......
- [FPGA tutorial case 9] design and implementation of clock manager based on vivado core
- 【纯音听力测试】基于MATLAB的纯音听力测试系统
- Ruby tutorial
- Database postragesql lock management
猜你喜欢
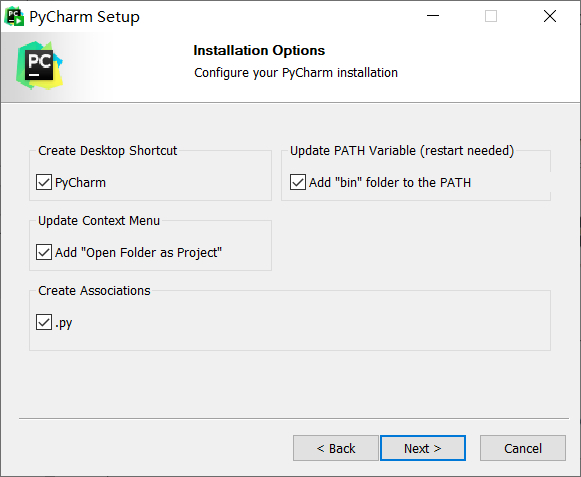
Pycharm professional download and installation tutorial

Basic operations of database and table ----- create index
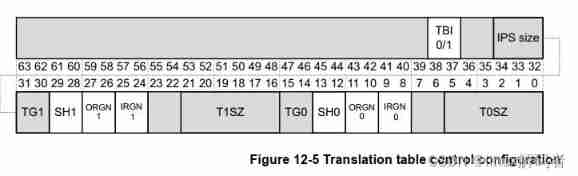
Armv8-a programming guide MMU (3)
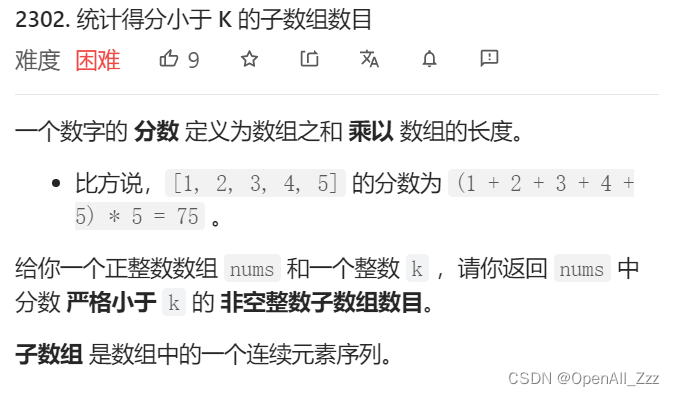
LeetCode周赛 + AcWing周赛(T4/T3)分析对比
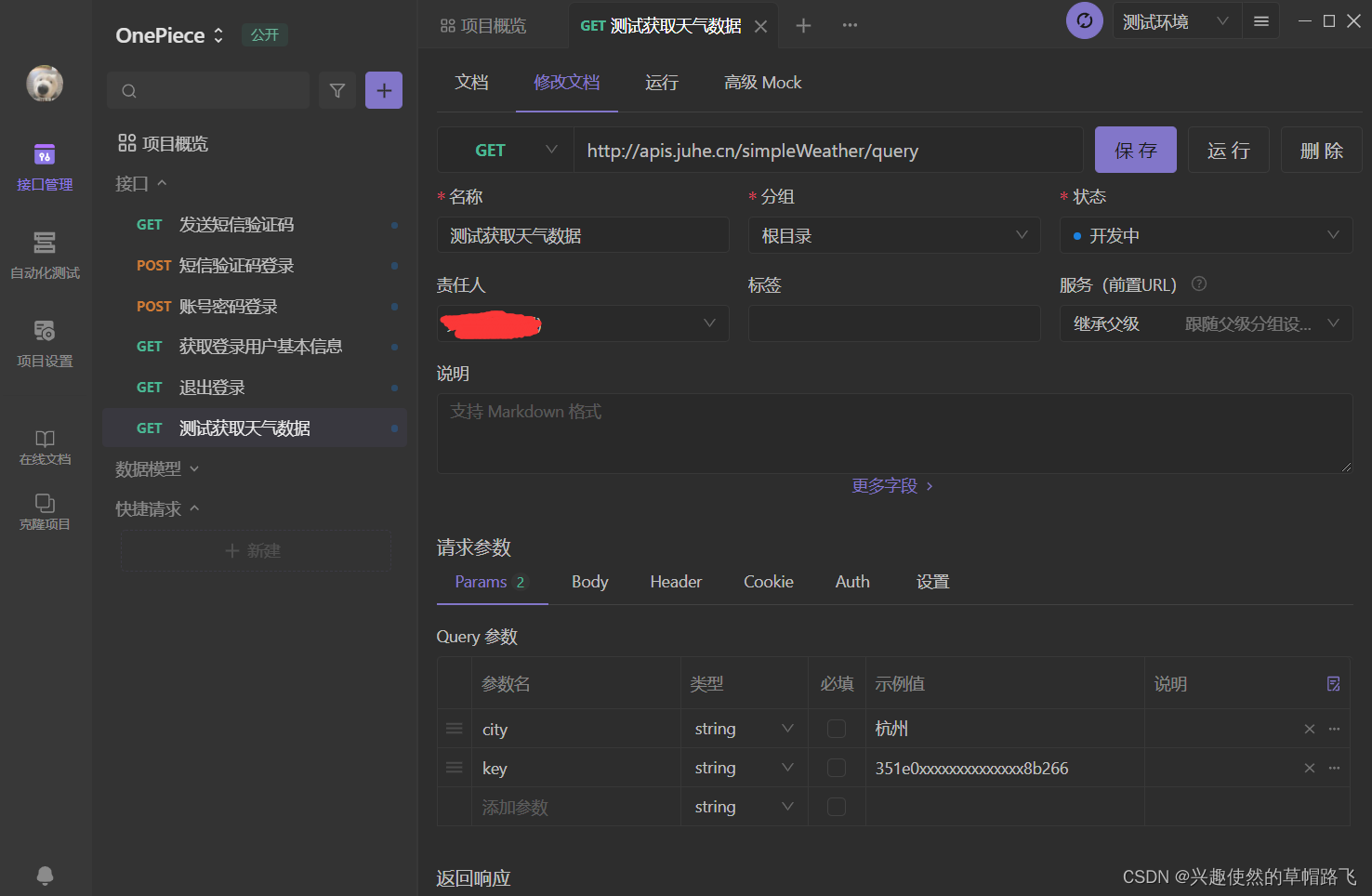
Apifox (postman + swagger + mock + JMeter), an artifact of full stack development and efficiency improvement
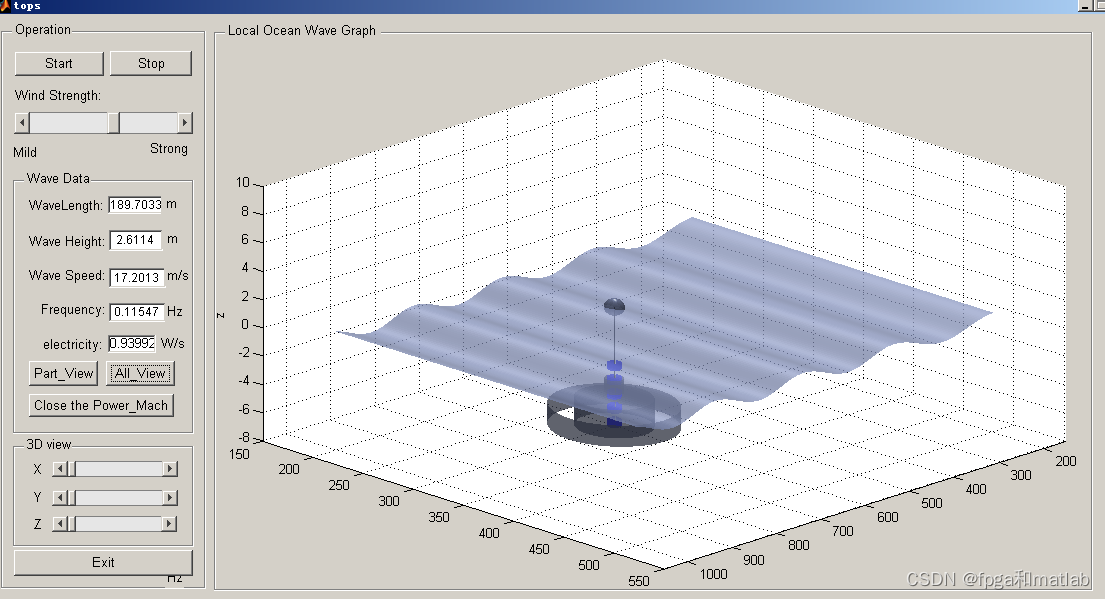
【海浪建模2】三维海浪建模以及海浪发电机建模matlab仿真
College degree, what about 33 year old Baoma? I still sell and test, and my monthly income is 13K+
![[development of large e-commerce projects] performance pressure test - Performance Monitoring - heap memory and garbage collection -39](/img/60/d5951ffb4cc271d2e7a3add9293f23.png)
[development of large e-commerce projects] performance pressure test - Performance Monitoring - heap memory and garbage collection -39

Roads and routes -- dfs+topsort+dijkstra+ mapping
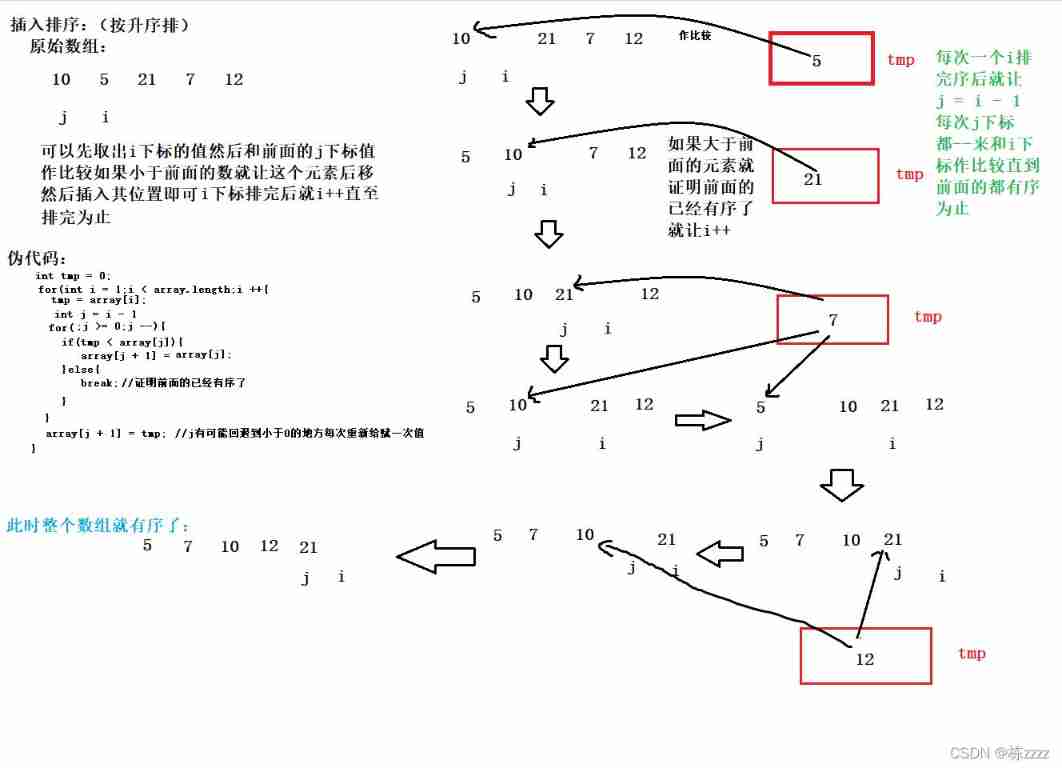
Insert sort of sort
随机推荐
[FPGA tutorial case 10] design and implementation of complex multiplier based on Verilog
华为百万聘请数据治理专家!背后的千亿市场值得关注
Mongodb series learning notes tutorial summary
I was beaten by the interviewer because I didn't understand the sorting
||Interview questions you will encounter
[Chongqing Guangdong education] National Open University spring 2019 1042 international economic law reference questions
Detailed explanation of multi-mode input event distribution mechanism
微信小程序:全网独家小程序版本独立微信社群人脉
全网最全正则实战指南,拿走不谢
Single step debugging of master data reading of SAP commerce cloud products
MySQL uses the explain tool to view the execution plan
BGP comprehensive experiment
Postman automatically fills headers
Are you still writing the TS type code
User login function: simple but difficult
Package What is the function of JSON file? What do the inside ^ angle brackets and ~ tilde mean?
Which financial products with stable income are good
Basic concept and usage of redis
La jeunesse sans rancune de Xi Murong
SAP UI5 应用的主-从-从(Master-Detail-Detail)布局模式的实现步骤