当前位置:网站首页>Database postragesql client authentication
Database postragesql client authentication
2022-07-05 01:04:00 【wx5d0241bb88268】
Chapter 20. Client side authentication
When a client application connects to a database server , It will specify which PostgreSQL Database user name connection , It's like we log in to a certain user Unix It's the same with computers . stay SQL Environment , The active database user name determines access to database objects — See Chapter 21. therefore , It is essentially what database users can connect to .
Such as Chapter 21 In the book ,PostgreSQL Actually “ role ” For permission management . In this chapter , We use database users to express “ Have LOGIN The role of authority ”.
Authentication is the process of establishing the client identity of the database server , And the server decides the client application ( Or the user running the client application ) Whether to be allowed to connect with the requested database user name .
PostgreSQL Provides a variety of different client authentication methods . The method used to authenticate a particular client connection can be based on ( client ) The host address 、 The database and the user choose .
PostgreSQL The database user name is logically independent of the user name in the operating system running on the server . If all users of a particular server have accounts on that server's machine , Then it makes sense to assign a database user name that matches the operating system user name . however , A server that accepts remote connections may have many users without local operating system accounts , And in this case, there is no need for any connection between the database user and the operating system user name .
20.1. pg_hba.conf file
Client authentication is made up of a configuration file ( Usually called pg_hba.conf And is stored in the database cluster directory ) control (HBA Represents host based authentication ). stay initdb When initializing the data directory , It will install a default pg_hba.conf file . However, we can also put the authentication configuration file in other places ; Refer to the hba_file Configuration parameters .
pg_hba.conf The common format of a file is a set of records , One in each line . Blank lines will be ignored , # Any text after the comment character is also ignored . Records cannot cross lines . A record consists of several spaces and / Or tab separated fields . If the field value is enclosed in double quotation marks , So it can contain blanks . In the database 、 In a user or address field Quote a keyword ( for example ,all or replication) Will make the word lose its special meaning , And it just matches a database with that name 、 User or host .
Each record specifies a connection type 、 One client IP Address range ( If it's related to the connection type )、 A database name 、 A user name and the authentication method used for connections that match these parameters . The first match connection type 、 Client address 、 The database of the connection request and the record of the user name will be used to perform authentication . There is no such thing as “ Lost ” perhaps “ backup ” That's what I'm saying : If a record is selected and authentication fails , Then the later records will no longer be considered . If there is no matching record , Then access will be denied .
Records can be in one of seven formats :
local database
user
auth-method [auth-options]
host database
user
address
auth-method [auth-options]
hostssl database
user
address
auth-method [auth-options]
hostnossl database
user
address
auth-method [auth-options]
host database
user
IP-address
IP-mask
auth-method [auth-options]
hostssl database
user
IP-address
IP-mask
auth-method [auth-options]
hostnossl database
user
IP-address
IP-mask
auth-method [auth-options]
- 1.
- 2.
- 3.
- 4.
- 5.
- 6.
- 7.
- 8.
- 9.
- 10.
- 11.
- 12.
- 13.
- 14.
- 15.
- 16.
- 17.
- 18.
- 19.
- 20.
- 21.
- 22.
- 23.
- 24.
- 25.
- 26.
- 27.
- 28.
- 29.
- 30.
- 31.
- 32.
- 33.
- 34.
- 35.
- 36.
- 37.
- 38.
- 39.
- 40.
- 41.
- 42.
- 43.
- 44.
- 45.
- 46.
- 47.
- 48.
- 49.
- 50.
- 51.
- 52.
- 53.
The meaning of each domain is as follows :
local
This record matches an attempt to use Unix Domain socket connection . If there is no record of this type , Not allowed Unix Domain socket connection .
host
This record matches an attempt to use TCP/IP Established connection .host Record matching SSL He Fei SSL The connection attempt of .
Unless the server comes with the right listen_addresses Configuration parameter values start , Otherwise, it will be impossible to carry out remote TCP/IP Connect , Because the default behavior is to listen only to the local loopback address localhost Upper TCP/IP Connect .
hostssl
This record matches an attempt to use TCP/IP Established connection , But you have to use SSL Encrypted connections . To use this option , When compiling the server, you must turn on SSL Support . Besides , When the server is started, it must be set up ssl Configuration parameters ( See Section 18.9) open SSL. otherwise ,hostssl Records will be ignored , And a warning will be recorded saying that it cannot match any connection .
hostnossl
The behavior of this record is related to hostssl contrary ; It only matches those in TCP/IP Don't use SSL The connection attempt of .
database
Specifies the database name that the record matches . value all Specifies that the record matches all databases . value sameuser Specifies if the requested database has the same name as the requested user , The match . value samerole Specifies that the requested user must be a member of a role with the same name as the database (samegroup It's an abandoned one , But it's still accepted samerole A synonym for ). For one that is used for samerole The role of purpose , Super users are not considered members of it , Unless they are explicit members of the role ( Directly or indirectly ), Not because of the super user .
value replication Specifies that if a physical replication connection is requested, the record matches ( Note that the replication connection does not specify any specific database ). In other cases , This is a specific PostgreSQL Database name . You can specify multiple databases by separating them with commas , You can also do this by putting @ To specify a file containing the database name .
user
Specify which database user names this record matches . value all Specifies that it matches all users . otherwise , It's either the name of a particular database user or a prefix + The group name of ( Think about it , stay PostgreSQL in , There is no real difference between users and groups ,+ The actual expression is “ Any direct or indirect member roles that match this role ”, But not + The token name matches only the specified role ). For this purpose , If the superuser is explicitly a member of a role ( Directly or indirectly ), Then the superuser will be considered only as a member of the role, not as a superuser . Multiple user names can be provided in a comma separated way . A file containing a user name can be created by adding @ To specify the .
address
Specify the address of the client machine that this record matches . This domain can contain a host name 、 One IP Address range or one of the special keywords mentioned below .
One IP The address range is specified by the standard numeric notation of the starting address of the range , And then there's a slash (/) And a CIDR Mask length . The mask length indicates the client IP The number of high order bits that the address must match . In the given IP In the address , The bit to the right of this length must be zero . stay IP Address 、/ and CIDR There must be no white space between mask lengths .
This method specifies a IPv4 A typical example of an address range is : 172.20.143.89/32 For a host ,172.20.143.0/24 For a small network , 10.6.0.0/16 For a large network . A single host IPv6 The address range looks like this :::1/128(IPv6 Return address ), A small network of IPv6 The address range is similar to :fe80::7a31:c1ff:0000:0000/96. 0.0.0.0/0 Express all IPv4 Address , also ::0/0 Express all IPv6 Address . To specify a single host ,IPv4 Use a length of 32 Of CIDR Mask or IPv6 use The length is 128 Of CIDR Mask . In a network address , Don't omit the zero at the end .
One by IPv4 The items given in the format will only match IPv4 Connect and one with IPv6 The items given in the format will only match IPv6 Connect , Even if the corresponding address is in IPv4-in-IPv6 Within the scope of . Please note that if the system C Library does not support IPv6 Address , that IPv6 Items in the format will be rejected .
You can also write all To match any IP Address 、 Write samehost To match any of the server's own IP Address or write samenet To match any address of any subnet to which this server is directly connected .
If you specify a host name ( Any division IP All other than address units or special keywords are treated as host names ), The name will be associated with the client's IP Address reverse name resolution ( For example, using DNS The reverse of time DNS lookup ) Compare the results . Host name comparison is case sensitive . If match up , Then a forward name resolution will be performed on the host name ( For example, positive DNS lookup ) To check that any address it resolves to is equal to the client's IP Address . If both directions match , Then the item is considered to match (pg_hba.conf The host name used in should be the client IP Address address to name resolution return result , Otherwise, the row will not match . Some host name databases allow a IP Address associated with multiple host names , But when asked to parse a IP Address time , The operating system will return only one host name ).
One with a dot (.) The starting host name declaration matches the suffix of the actual host name . therefore .example.com Will match foo.example.com( But don't match example.com).
When the host name is in pg_hba.conf When it is specified in , You should make sure that name resolution is fast . Create a similar nscd The local name resolution cache is a good choice . in addition , You may want to enable configuration parameters log_hostname To see the client's host name in the log instead of IP Address . This field only applies to host、 hostssl and hostnossl Record .
Users sometimes wonder why the host names processed in this way look complicated , Because it takes two name resolution ( Including once client IP Reverse lookup of address ).
In the reverse of the client DNS Item does not create or get some unexpected host In the case of names , This approach can complicate the use of this feature . This is mainly for efficiency : In this way , once Connection attempts require up to two parser lookups , once
Reverse and once forward . If there is a parser that has a problem with the address , It's just a client problem . A hypothetical alternative implementation is to just look forward , This method has to be used in every connection Parsing during the attempt pg_hba.conf Each host name mentioned in . If you list a lot of names , It's going to be slow . And if one of the hostnames has a parser problem , It will become a problem for everyone .
in addition , A reverse lookup is also required to implement the suffix matching feature , Because you need to know the actual client host name to match the pattern .
Note that this behavior is consistent with other popular host name based access control implementations , for example Apache HTTP Server and TCP Wrappers.
IP-address/IP-mask
These two domains can be used as IP-address/ mask-length Alternative to notation . The mask and the specified length are different , The actual mask is referred to In a separate column . for example ,255.0.0.0 Express IPv4 CIDR Mask length 8, and 255.255.255.255 Express CIDR Mask length 32.
These fields only apply to host、hostssl and hostnossl Record .
auth-method
Specifies that when a connection matches this record , Authentication method to be used . The following is an overview of the possible options , See Section 20.3.
trust
Allow the connection unconditionally . This method allows anyone who can be associated with PostgreSQL The database server connects users with whatever they expect PostgreSQL Log in as database user , You don't need a password or any other authentication . See Section 20.4.
reject
Refuse to connect unconditionally . This helps from a group “ Filter out ” Specific host , For example, one reject Line can block a specific host connection , The next line allows the rest of the hosts in a particular network to connect .
scram-sha-256
perform SCRAM-SHA-256 Authentication to verify the user's password . See Section 20.5.
md5
perform SCRAM-SHA-256 or MD5 Authentication to verify the user's password . See Section 20.5.
password
Ask the client to provide an unencrypted password for authentication . Because passwords are sent over the network in clear text , So we shouldn't use this on untrusted networks . See Section 20.5.
gss
use GSSAPI Authenticated user . Only right TCP/IP Connection available . See Section 20.6.
sspi
use SSPI To authenticate users . Only in Windows Available on the . See Section 20.7.
ident
By contacting the client's ident The server gets the operating system name of the client , And check that it matches the requested database user name .Ident Certification can only be done in TCIP/IP Use... On the connection . When specifying this authentication method for local connections , Will use peer Certification to replace . See Section 20.8.
peer
The operating system user who obtains the client from the operating system , And check that it matches the requested database user name . This is only available for local connections . See Section 20.9.
ldap
Use LDAP Server authentication . See Section 20.10.
radius
use RADIUS Server authentication . See Section 20.11.
cert
Use SSL Client certificate authentication . See Section 20.12.
pam
Using the pluggable authentication module service provided by the operating system (PAM) authentication . See Section 20.13.
bsd
Use... Provided by the operating system BSD Authentication services to authenticate . See Section 20.14.
auth-options
stay auth-method After the domain , It can be in the form of name=value The domain of , They specify options for authentication methods . For details of which authentication methods and which options are available, see below .
In addition to the method related options listed below , There is also a method independent authentication option clientcert, It can be in any hostssl The record specifies . When set to 1 when , This option requires the client to present a valid ( credible )SSL certificate .
use @ Structure contains files that are read as a list of names , They can be separated by blanks or commas . With notes # introduce , As in the pg_hba.conf In the , And allow nesting @ structure . Unless you're following @ The following file name is an absolute path , File names are considered relative to the directory that contains the referenced file .
Because every connection attempt is checked sequentially pg_hba.conf Record , So the order of these records is critical . Usually , The top records have strict connection matching parameters and weak authentication methods , The later records have loose matching parameters and stronger authentication methods . for example , We want to be local TCP/IP Connection to use trust authentication , And for remote TCP/IP The connection requires a password . In this case, from 127.0.0.1 The connection of the trust Authenticated records will appear for a wider range of clients IP Address specifies password authentication in front of the record .
After startup and the master server process receives SIGHUP Signal time ,pg_hba.conf The file will be read . If you edit the file on the active system , You will need to inform postmaster( Use pg_ctl reload or kill -HUP) Reread the file .
The previous explanation is in Microsoft Windows It's not true : stay Windows On ,pg_hba.conf Any changes in the file are immediately applied to subsequent new connections .
The system view pg_hba_file_rules Help to pre test for pg_hba.conf Changes to documents , This view can also be used to diagnose problems when the loading of the file does not produce the desired effect . This view has non empty error The line of the field indicates that there is a problem in the corresponding line of the file .
To connect to a specific database , A user must not only pass through pg_hba.conf Check , There must also be... On the database CONNECT jurisdiction . If you want to limit which users can connect to which databases , grant / revoke CONNECT Authority is usually greater than in pg_hba.conf Item rules are simple to set .
边栏推荐
- I was beaten by the interviewer because I didn't understand the sorting
- Single step debugging of master data reading of SAP commerce cloud products
- [microprocessor] VHDL development of microprocessor based on FPGA
- [development of large e-commerce projects] performance pressure test - Performance Monitoring - heap memory and garbage collection -39
- BGP comprehensive experiment
- Expansion operator: the family is so separated
- 【C】 (written examination questions) pointer and array, pointer
- Hologres query management and timeout processing
- 每日刷题记录 (十三)
- 程序员SQL数据脚本编码能力弱,BI做不出来怎么办?
猜你喜欢
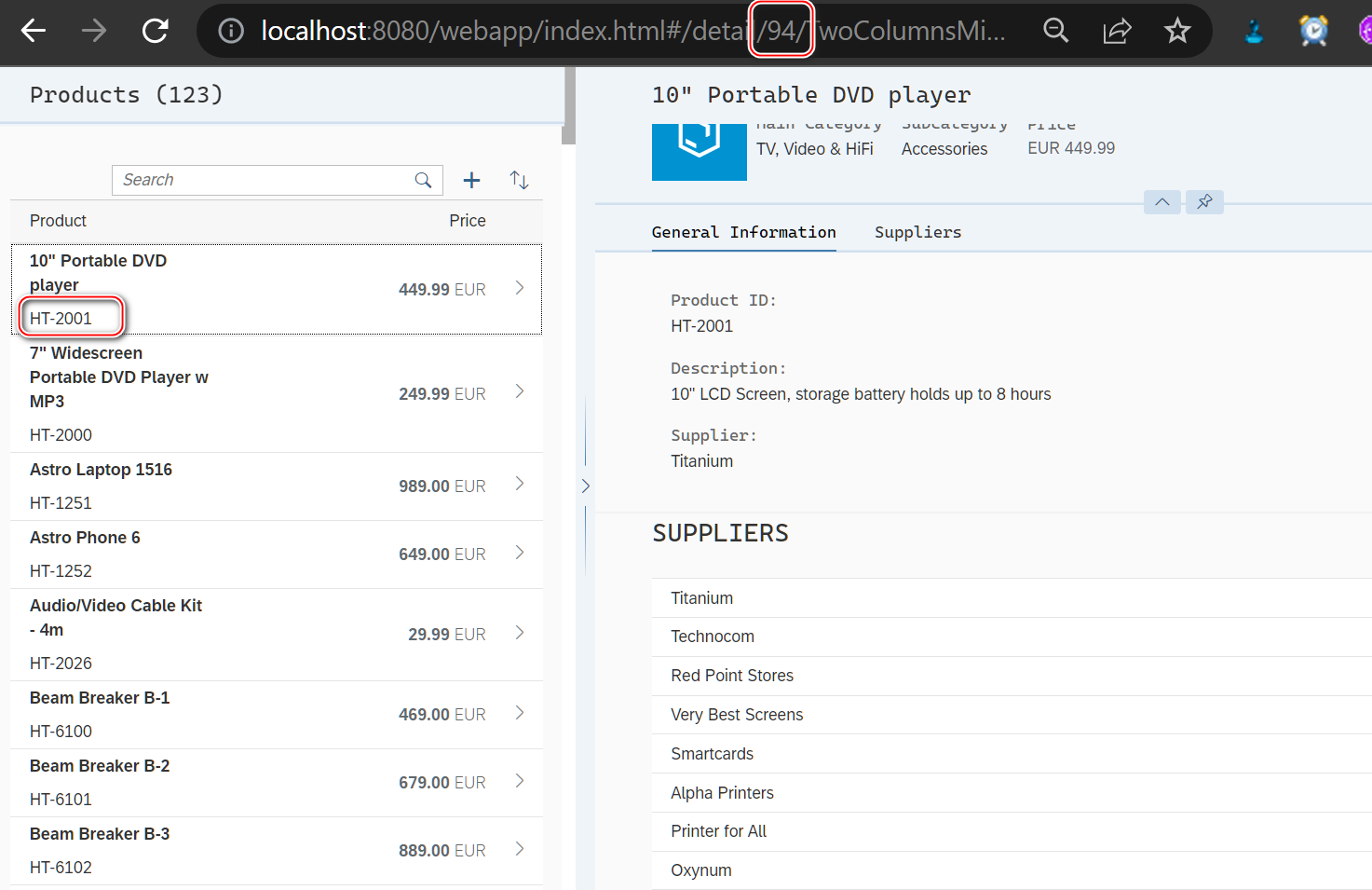
SAP UI5 应用开发教程之一百零六 - 如何提高 SAP UI5 应用路由 url 的可读性试读版
![[development of large e-commerce projects] performance pressure test - Optimization - impact of middleware on performance -40](/img/e4/0bdee782a65028b2bc87db85d48738.png)
[development of large e-commerce projects] performance pressure test - Optimization - impact of middleware on performance -40
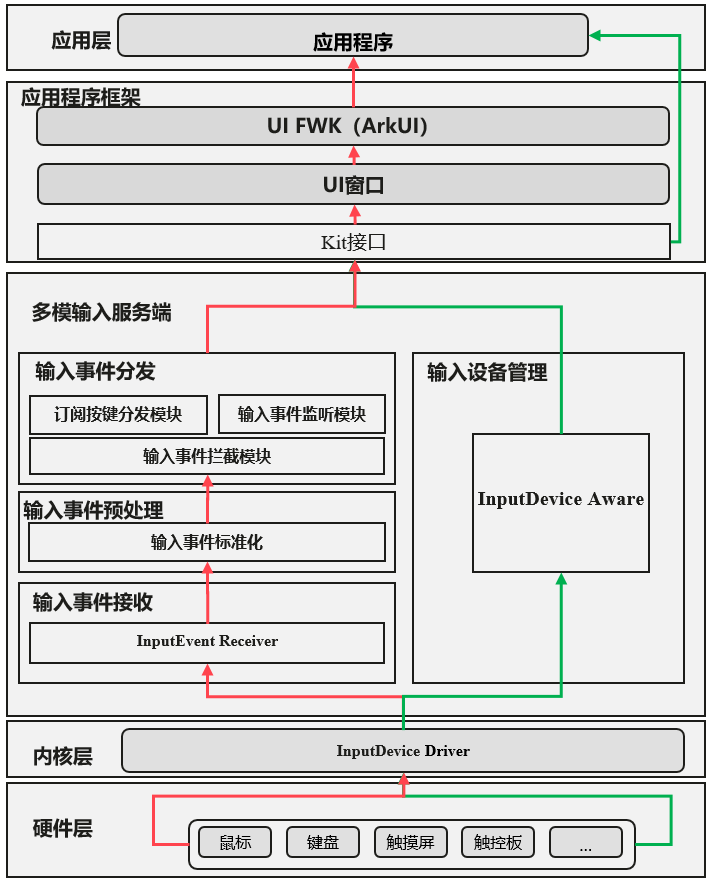
Detailed explanation of multi-mode input event distribution mechanism
![Grabbing and sorting out external articles -- status bar [4]](/img/88/8267ab92177788ac17ab665a90b781.png)
Grabbing and sorting out external articles -- status bar [4]
每日刷题记录 (十三)
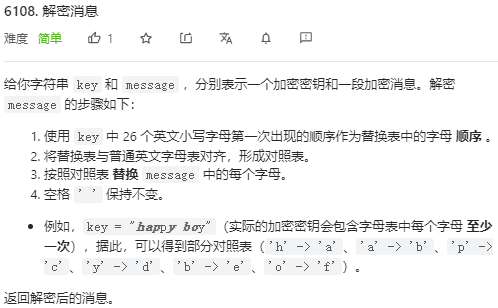
2022.07.03 (LC 6108 decryption message)
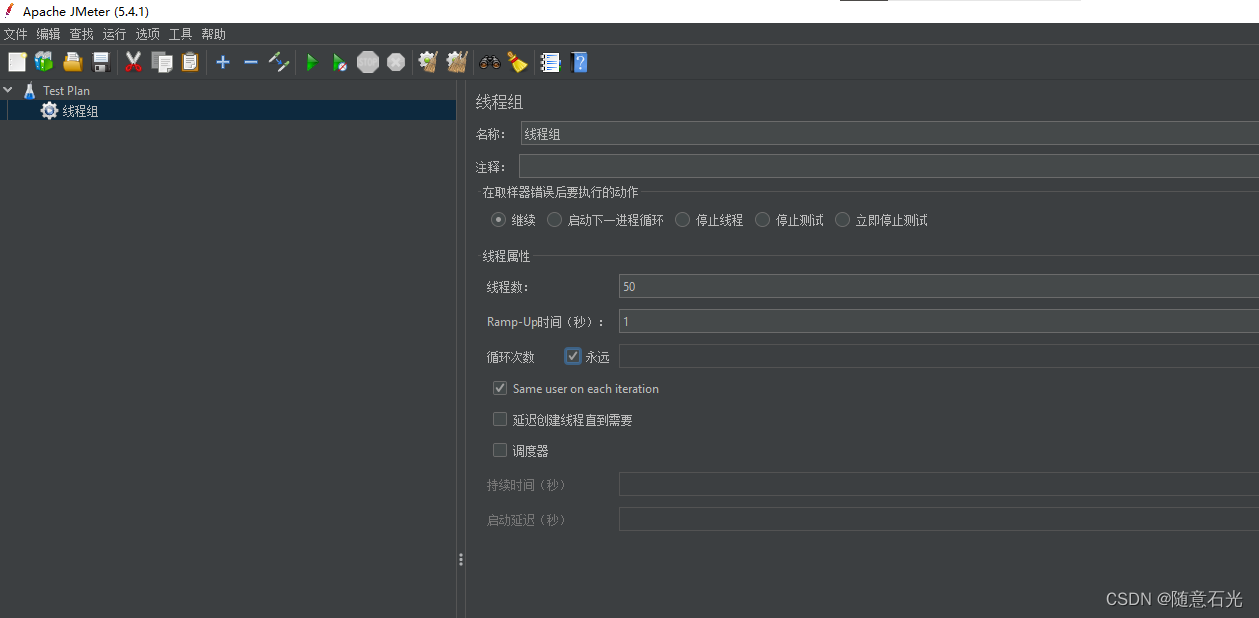
【大型电商项目开发】性能压测-优化-中间件对性能的影响-40
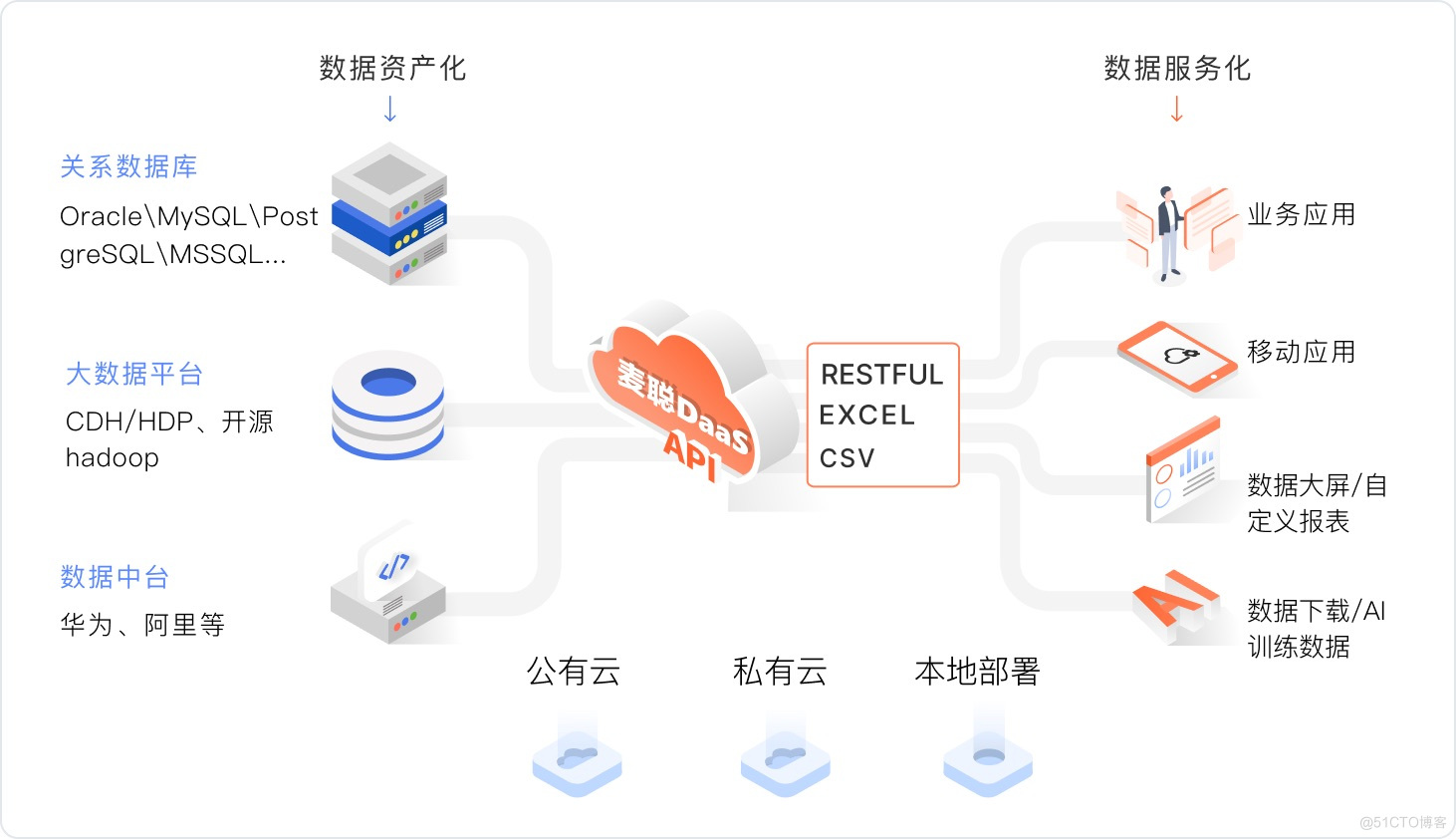
华为百万聘请数据治理专家!背后的千亿市场值得关注
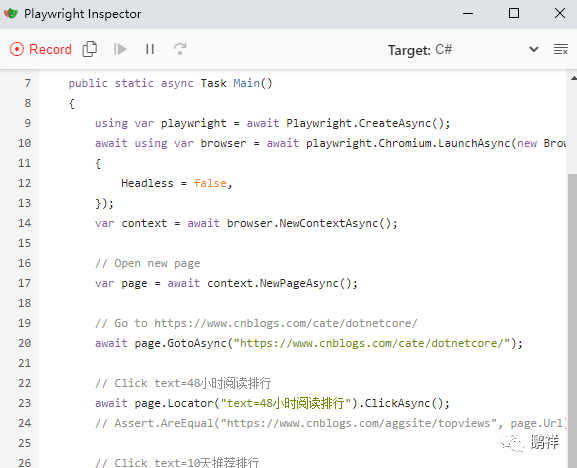
Playwright recording
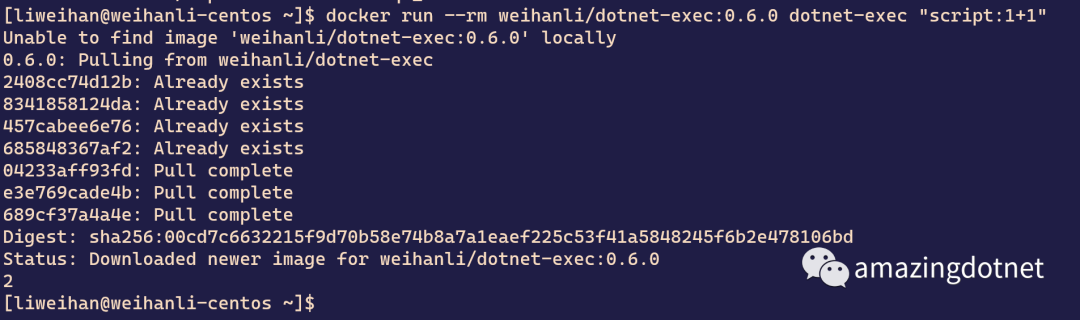
dotnet-exec 0.6.0 released
随机推荐
Introduction to the gtid mode of MySQL master-slave replication
【纯音听力测试】基于MATLAB的纯音听力测试系统
[Yocto RM]10 - Images
Basic operations of database and table ----- delete index
Les phénomènes de « salaire inversé » et de « remplacement des diplômés » indiquent que l'industrie des tests a...
SAP ui5 application development tutorial 107 - trial version of SAP ui5 overflow toolbar container control introduction
【C】 (written examination questions) pointer and array, pointer
【海浪建模1】海浪建模的理论分析和matlab仿真
LeetCode周赛 + AcWing周赛(T4/T3)分析对比
Query for Boolean field as "not true" (e.g. either false or non-existent)
dotnet-exec 0.6.0 released
Playwright recording
整理混乱的头文件,我用include what you use
Leetcode70 (Advanced), 322
Several simplified forms of lambda expression
Binary conversion problem
SAP ui5 application development tutorial 106 - how to improve the readability of SAP ui5 application routing URL trial version
Global and Chinese markets for industrial X-ray testing equipment 2022-2028: Research Report on technology, participants, trends, market size and share
【大型电商项目开发】性能压测-性能监控-堆内存与垃圾回收-39
全栈开发提效神器——ApiFox(Postman + Swagger + Mock + JMeter)