当前位置:网站首页>Step size of ode45 and reltol abstol
Step size of ode45 and reltol abstol
2022-07-01 18:04:00 【Feisy】
The stepsize of ode45 is not constant, but chosen such that the error tolerances you prescribe are met. Thus mean step size can only be controlled indirectly by strengthening (-> smaller stepsize) or weakening (-> larger stepsize) the error tolerances RelTol and AbsTol.
RelTol Is the relative accuracy tolerance , Used to control the correct number of digits in the calculated answer .AbsTol Is the absolute error tolerance , Used to control the difference between the calculated answer and the actual solution . In each step , Solution component i The error in e Will satisfy
|e(i)| ≤ max(RelTol*abs(y(i)),AbsTol(i))
Roughly speaking , This means that you want RelTol Correct the number of digits in all solution components ( But less than the threshold AbsTol(i) Except for the solution component of ). When the weight y(i) Very hour , Even if you are not interested in this weight , You must still specify a small enough AbsTol(i) value , In order to obtain y(i) Some correct digits in , So as to accurately calculate the components you are more interested in .
At each step, the solver estimates the local error e in the ith component of the solution. This error must be less than or equal to the acceptable error, which is a function of the specified relative tolerance, RelTol, and the specified absolute tolerance, AbsTol.
|e(i)| ≤ max(RelTol*abs(y(i)),AbsTol(i))
For relative accuracy, adjust RelTol. For the absolute error tolerance, the scaling of the solution components is important: if |y| is somewhat smaller than AbsTol, the solver is not constrained to obtain any correct digits in y. You might have to solve a problem more than once to discover the scale of solution components.
Roughly speaking, this means that you want RelTol correct digits in all solution components except those smaller than thresholds AbsTol(i). Even if you are not interested in a component y(i) when it is small, you may have to specify AbsTol(i) small enough to get some correct digits in y(i) so that you can accurately compute more interesting components.
边栏推荐
- Openlayers customize bubble boxes and navigate to bubble boxes
- Function, condition, regular expression
- China PBAT resin Market Forecast and Strategic Research Report (2022 Edition)
- Three dimensional anti-terrorism Simulation Drill deduction training system software
- Win10+vs2019 Community Edition compiling OpenSSL
- ACL 2022 | decomposed meta learning small sample named entity recognition
- Small exercise -- subnet division and summary
- The latest intelligent factory MES management system software solution
- Blackwich: the roadmap of decarbonization is the first step to realize the equitable energy transformation in Asia
- The difference and relationship between iteratible objects, iterators and generators
猜你喜欢

ACL 2022 | decomposed meta learning small sample named entity recognition
Product service, operation characteristics
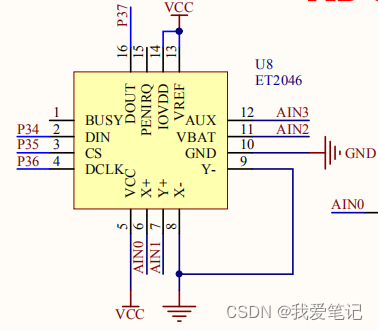
(16) ADC conversion experiment
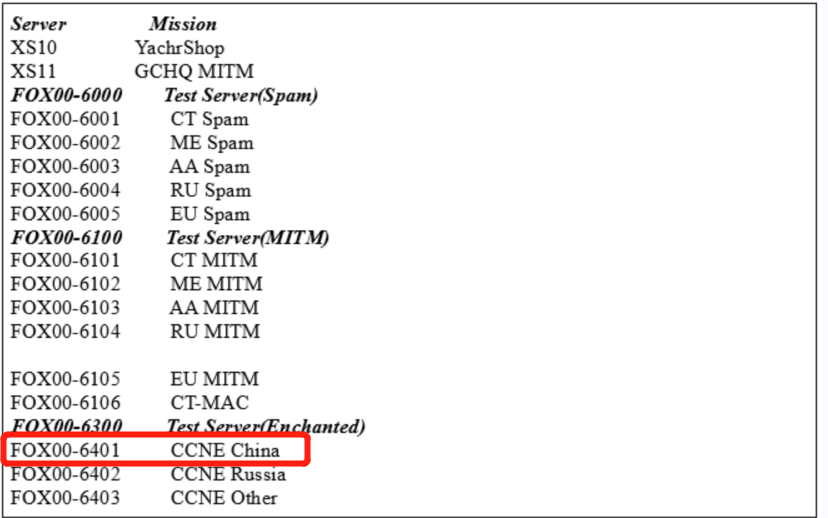
Heavy disclosure! Hundreds of important information systems have been invaded, and the host has become a key attack target

Cassette helicopter and alternating electric field magnetic manometer DPC
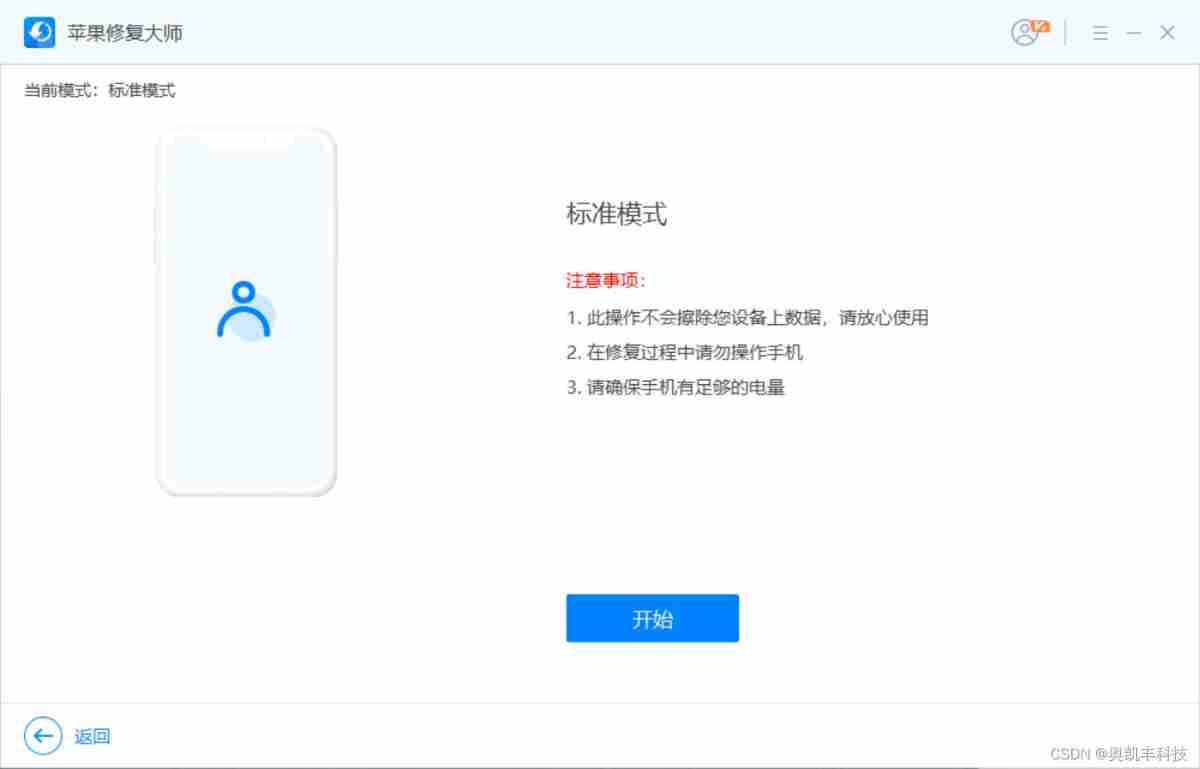
Fix the black screen caused by iPhone system failure

Enter wechat applet
![Htt [ripro network disk link detection plug-in] currently supports four common network disks](/img/e4/c06b94243cdbe391b8b2124ff30789.jpg)
Htt [ripro network disk link detection plug-in] currently supports four common network disks
Review Net 20th anniversary development and 51aspx growth
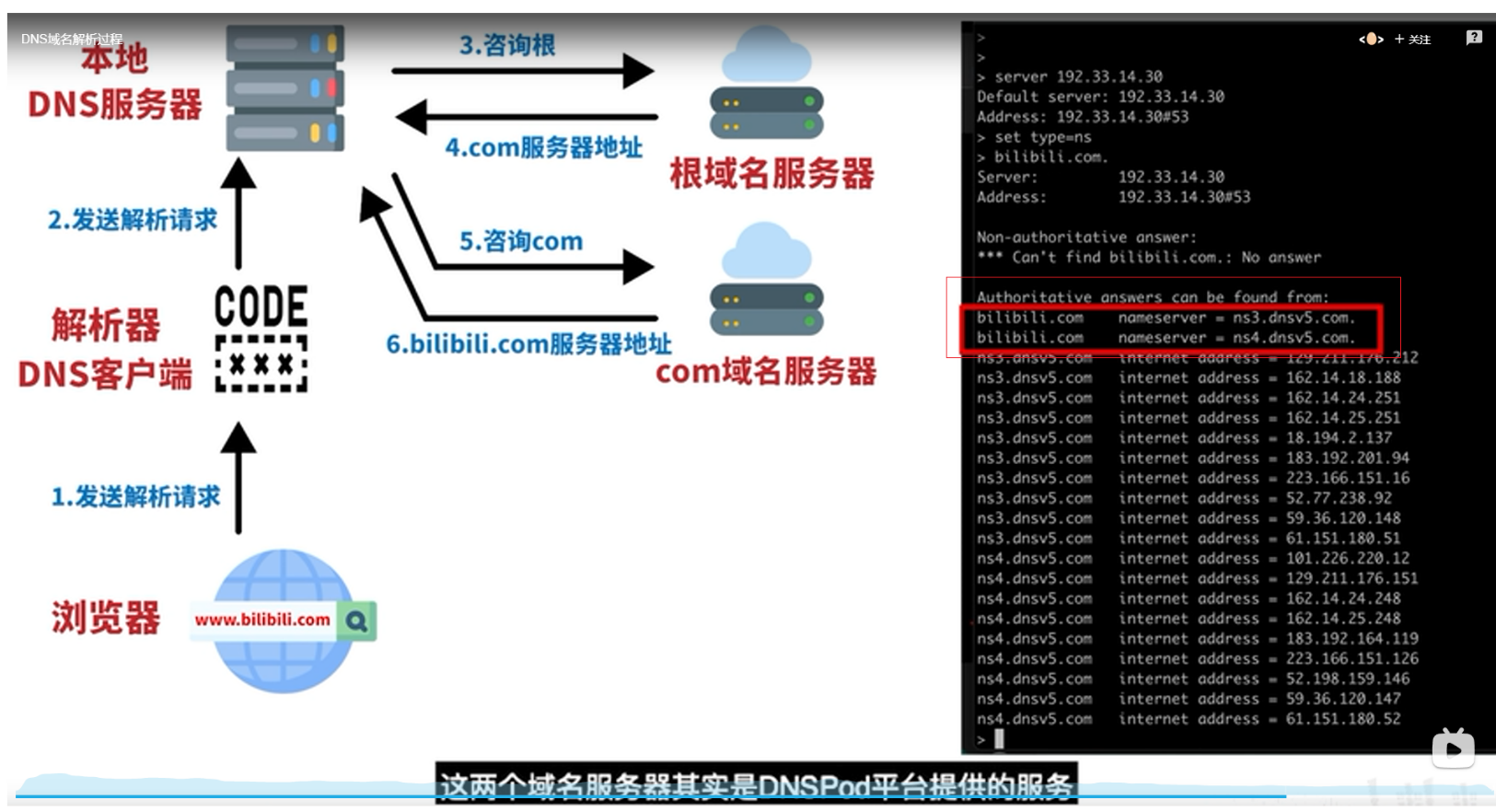
DNS
随机推荐
Pyqt5, draw a histogram on the control
Happy new year | 202112 monthly summary
Glidefast consulting was selected as the elite partner of servicenow in 2022
Penetration practice vulnhub range Tornado
2022 Heilongjiang latest fire protection facility operator simulation test question bank and answers
June issue | antdb database participated in the preparation of the "Database Development Research Report" and appeared on the list of information technology and entrepreneurship industries
Code example of libcurl download file
Unity3d extended toolbar
People help ant help task platform repair source code
Radhat builds intranet Yum source server
China acetonitrile market forecast and strategic consulting research report (2022 Edition)
How to use JMeter function and mockjs function in metersphere interface test
Setting up a time server requires the client to automatically synchronize the time of the server at 9 a.m. every day
Sword finger offer II 105 Maximum area of the island
From comedians to NBA Zhan Huang, check the encrypted advertisements during this super bowl
Euler function: find the number of numbers less than or equal to N and coprime with n
Yolov5 practice: teach object detection by hand
[PHP foundation] realize the connection between PHP and SQL database
How to retrieve the password for opening Excel files
SCP -i private key usage