当前位置:网站首页>Interviewer: what is XSS attack?
Interviewer: what is XSS attack?
2022-07-04 21:34:00 【SS, shuaihai】
1 What is? XSS attack ?
xss The full name is (cross site scripting ( Cross site scripting ), In order to and CSS distinguish , So it's called xss.XSS An attack is the execution of a malicious script in a browser ( Whether it's cross domain or co domain ), So as to get the user's information and operate .
These operations can generally accomplish the following things :
- steal cookie.
- Monitor user behavior , For example, input the account password and send it directly to the hacker server .
- modify DOM Fake login forms .
- Create a floating window ad on the page .
General situation ,XSS There are three ways to attack ―— Storage type 、 Reflective and document . The principles are relatively simple , First come — Let me introduce it .
(1) Storage type
Storage type , As the name implies, it stores malicious scripts , exactly , Storage type XSS The script is stored in the database of the server , Then execute these scripts on the client side , So as to achieve the effect of attack .
A common scenario is to submit a script code in the comment area , If the front and back ends don't do a good job of escaping , The comments are stored in the database , Execute directly during page rendering , It's equivalent to executing an unknown logic JS Code , It's very scary . This is the storage type XSS attack .
(2) reflective
reflective XSS Refers to malicious script as Part of the network request .
So let's say I type in :
http://sanyuan.com?q=<script>alert(" You're done. ")</script> such , On the server side, you will get q Parameters , Then return the content to the browser , The browser uses this content as HTML Part of the analysis , Discovery is a script , Direct execution , So it's attacked .
It is called reflective , Because the malicious script is passed as a parameter of the network request , Through the server , And then reflect back to HTML In the document , Execution Analysis . Unlike the storage type , The server does not store these malicious scripts .
(3) Document type
Document type XSS The attack doesn't go through the server , It's the role of an intermediary , Hijack to network packet during data transmission , then Modify the html file !
Such hijackings include WIFI Router hijacking or local malware .
Two Preventive measures
I understand three kinds of XSS Principle attacks , We can find one thing in common ; It's all about allowing malicious scripts to execute directly in the browser .
Then guard against it , It is to avoid the execution of these script code .
To accomplish this , We must have a belief , Two use .
(1) A belief
Never trust any user's input !
Both in the front end and the server end , It's all about user input Transcoding or filtering .
such as
<script>alert(' You're done. ')</script> After transcoding, it becomes :
<script>alert(' You're done. ')</script>(2) utilize CSP
CSP, That is, the content security policy in the browser , Its core idea is that the server decides which resources the browser loads , Specifically, the following functions can be completed :
- Restrict resource loading under other domains .
- Do not submit data to other domains .
- Provide reporting mechanism , Can help us to find out in time XSS attack .
(4) utilize HttpOnly
quite a lot XSS Attack scripts are used to steal Cookie, And set up Cookie Of HttpOnly After attribute ,JavaScript Can't read Cookie Value . This can also be a good defense XSS attack .
summary
XSS An attack is the execution of a malicious script in a browser , Then get the user's information to operate . It is mainly divided into storage type 、( Reflective and document . Precautions include :
- A belief : Don't trust user input , Transcode or filter the input content , Make it unenforceable .·
- Two use : utilize CSP, utilize Cookie Of HttpOnly attribute .
边栏推荐
- Jerry's ad series MIDI function description [chapter]
- 巅峰不止,继续奋斗!城链科技数字峰会于重庆隆重举行
- Jerry's ad series MIDI function description [chapter]
- Golang interview finishing three resumes how to write
- Kubeadm初始化报错:[ERROR CRI]: container runtime is not running
- 2021 CCPC 哈尔滨 B. Magical Subsequence(思维题)
- 奋斗正当时,城链科技战略峰会广州站圆满召开
- 类方法和类变量的使用
- flink1.13 sql基础语法(一)DDL、DML
- redis03——Redis的网络配置与心跳机制
猜你喜欢

Shutter textfield example

OMS系统实战的三两事
![[public class preview]: basis and practice of video quality evaluation](/img/fd/42b98a08b5a0fd89c119f1d1a8fe1b.png)
[public class preview]: basis and practice of video quality evaluation

【公开课预告】:视频质量评价基础与实践
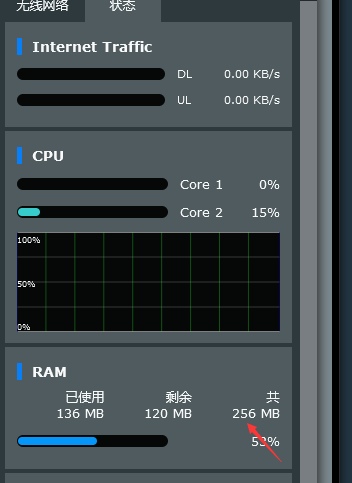
NetWare r7000 Merlin system virtual memory creation failed, prompting that the USB disk reading and writing speed does not meet the requirements. Solution, is it necessary to create virtual memory??
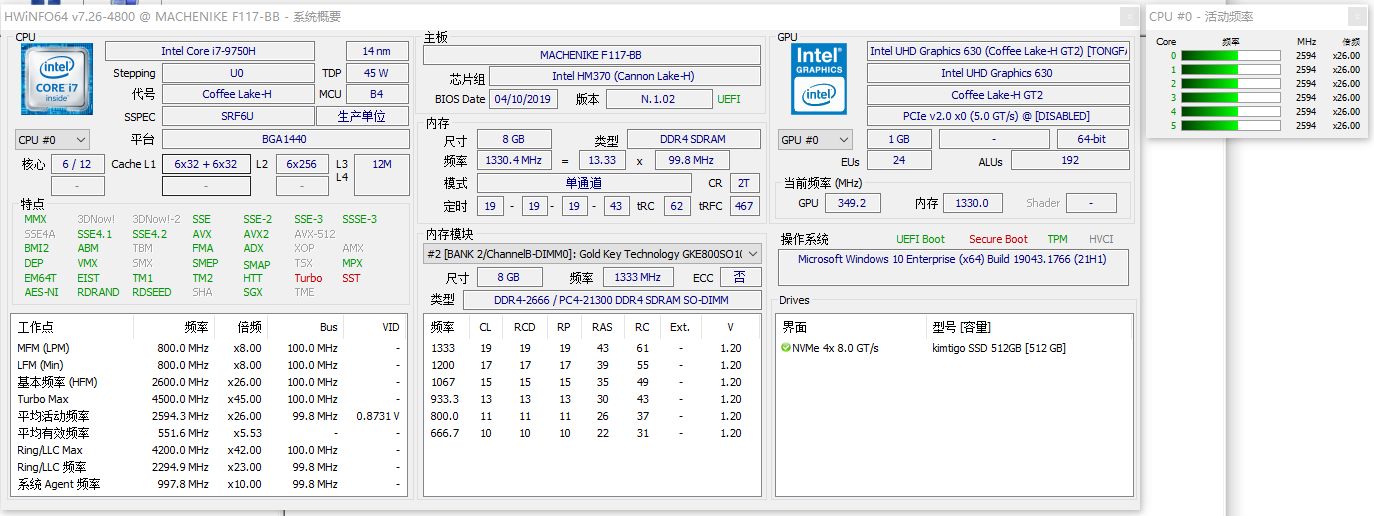
Hwinfo hardware detection tool v7.26 green version
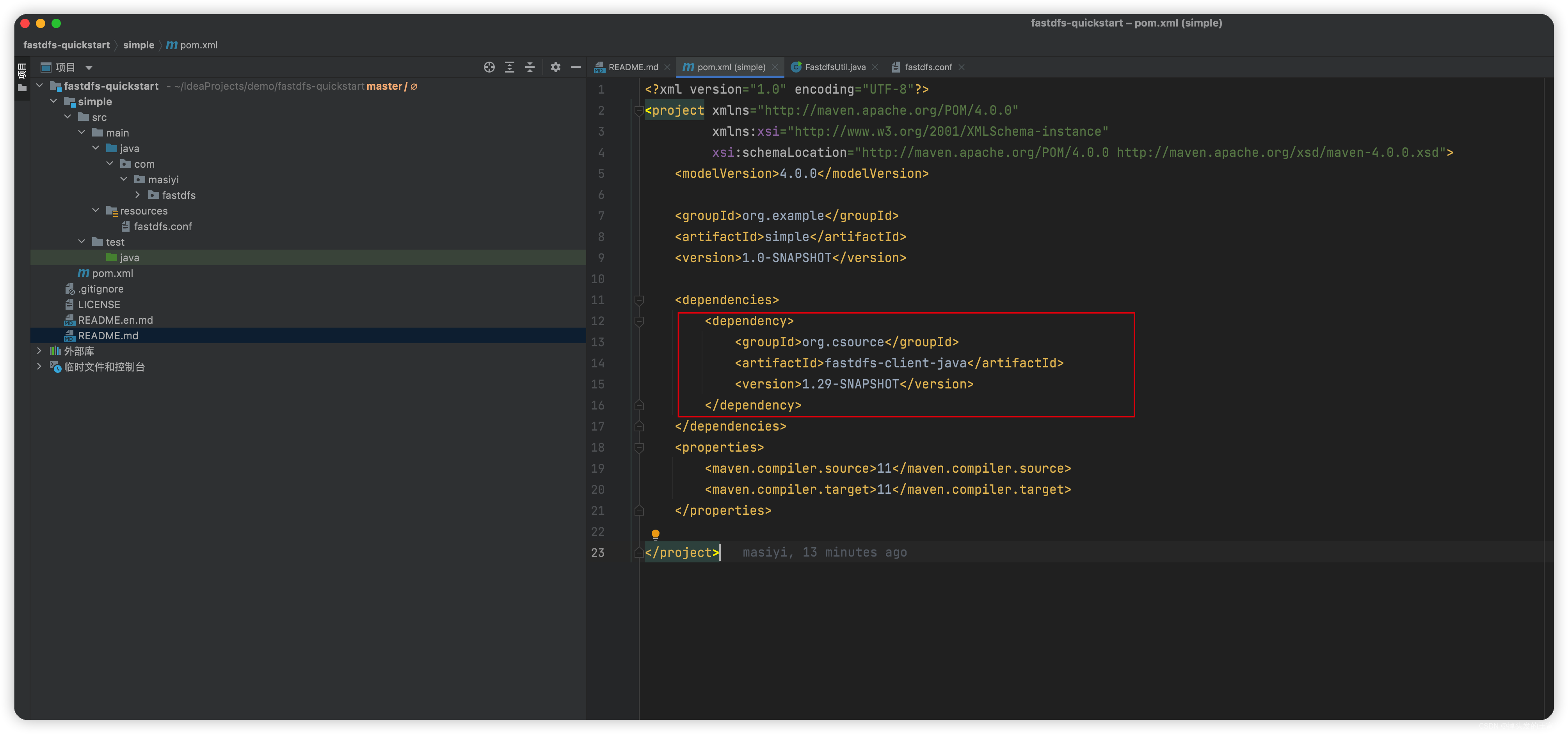
A quick start to fastdfs takes you three minutes to upload and download files to the ECS

Maidong Internet won the bid of Beijing life insurance
![[weekly translation go] how to code in go series articles are online!!](/img/bf/77253c87bfa1512f4b8d3d8f7ebe80.png)
[weekly translation go] how to code in go series articles are online!!
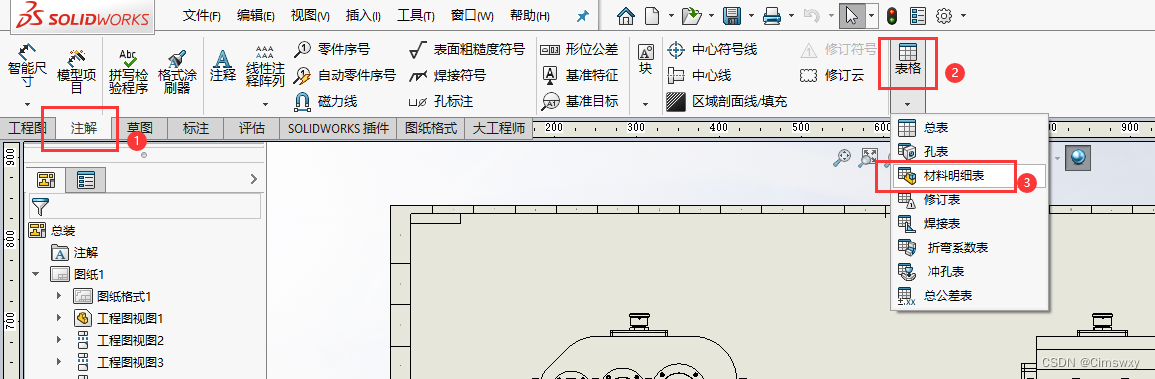
SolidWorks工程图添加材料明细表的操作
随机推荐
MYSQL 用!=查询不出等于null的数据,解决办法
How was MP3 born?
async await 在map中使用
Lambdaquerywrapper usage
Actual combat simulation │ JWT login authentication
Maya lamp modeling
Poster cover of glacier
宝塔 7.9.2 宝塔控制面板绕过 手机绑定认证 绕过官方认证
【C語言】符號的深度理解
Use of redis publish subscription
Redis cache
偷窃他人漏洞报告变卖成副业,漏洞赏金平台出“内鬼”
Difference between ApplicationContext and beanfactory (MS)
Gobang go to work fishing tools can be LAN / man-machine
Nmap scan
Redis pipeline
Day24: file system
华为ensp模拟器 实现多个路由器的设备可以相互访问
【LeetCode】17、电话号码的字母组合
Hwinfo hardware detection tool v7.26 green version