当前位置:网站首页>Common bit operation skills of C speech
Common bit operation skills of C speech
2022-07-05 01:26:00 【Snowflakes flying all over the sky】
One : Judge parity
void odd_even(int n)
{
if(n & 1 == 1)
{
printf("n Is odd !\n");
}
}Two : Exchange two numbers
int swap(int x, int y)
{
x = x ^ y;
y = x ^ y;
x = x ^ y;
} Based on the following properties of XOR operation :
1. Any variable X XOR with itself , The result is 0, namely X^X=0
2. Any variable X And 0 Xor operation , The result remains unchanged. , namely X^0=X
3. XOR operations are associative , namely a^ b ^ c =(a ^ b)^ c = a ^(b ^ c)
4. XOR operation is exchangeable , namely a ^ b = b ^ a
3、 ... and : Find numbers that are not repeated
int array[] = {1, 2, 3, 4, 5, 1, 2, 3, 4};
use :1 ^ 2 ^ 3 ^ 4 ^ 5 ^ 1 ^ 2 ^ 3 ^ 4;
// Equivalent to :
(1 ^ 1) ^ (2 ^ 2) ^ (3 ^ 3) ^ (4 ^ 4) ^ 5;
// Equivalent to :
0 ^ 0 ^ 0 ^ 0 ^ 5;
// The result is :
5;Four :m Of n Power
Want to solve the problem through binary , You have to break the numbers into binary to observe . For example, calculation m Of 15 Power :
m^15 = m^8 * m^4 * m^2 * m^1; //^ Represents a power operation
Change to binary :
m^1111 = m^1000 * m^0100 * m^0010 * m^0001;
We can go through "& 1" and ">> 1" To read... Bit by bit 1111, be equal to 1 Multiply the multiplier represented by this bit to the final result . The code is as follows :
int Pow(int m, int n)
{
int res = 1;
int tmp = m;
while(n != 0)
{
if(n & 1 == 1)
{
res *= tmp;
}
tmp *= tmp;
n = n >> 1;
}
return res;
}5、 ... and : Detection integer n Whether it is 2 The power of
int ispow(int N)
{
return ((N & (N - 1)) == 0) ? 1 : 0;
}6、 ... and : Find the absolute value
int abs(int n)
{
return (n ^ (n >> 31)) - (n >> 31);
}7、 ... and : Find the maximum of two numbers
int max(int x, int y)
{
return x ^ ((x ^ y) & -(x < y));
}8、 ... and : Bit skill
One 32bit Bits of data 、 Byte read operation
(1) Get single byte :
#define GET_LOW_BYTE0(x) ((x >> 0) & 0x000000ff) /* For the first 0 Bytes */
#define GET_LOW_BYTE1(x) ((x >> 8) & 0x000000ff) /* For the first 1 Bytes */
#define GET_LOW_BYTE2(x) ((x >> 16) & 0x000000ff) /* For the first 2 Bytes */
#define GET_LOW_BYTE3(x) ((x >> 24) & 0x000000ff) /* For the first 3 Bytes */
(2) Get someone :
#define GET_BIT(x, bit) ((x & (1 << bit)) >> bit) /* For the first bit position */
(3) Clear a byte :
#define CLEAR_LOW_BYTE0(x) (x &= 0xffffff00) /* Clear the ground 0 Bytes */
#define CLEAR_LOW_BYTE1(x) (x &= 0xffff00ff) /* Clear the ground 1 Bytes */
#define CLEAR_LOW_BYTE2(x) (x &= 0xff00ffff) /* Clear the ground 2 Bytes */
#define CLEAR_LOW_BYTE3(x) (x &= 0x00ffffff) /* Clear the ground 3 Bytes */
(4) Clear someone :
#define CLEAR_BIT(x, bit) (x &= ~(1 << bit)) /* Clear the ground bit position */
(5) Set a byte to 1:
#define SET_LOW_BYTE0(x) (x |= 0x000000ff) /* The first 0 Byte set 1 */
#define SET_LOW_BYTE1(x) (x |= 0x0000ff00) /* The first 1 Byte set 1 */
#define SET_LOW_BYTE2(x) (x |= 0x00ff0000) /* The first 2 Byte set 1 */
#define SET_LOW_BYTE3(x) (x |= 0xff000000) /* The first 3 Byte set 1 */
(6) Set one to :
#define SET_BIT(x, bit) (x |= (1 << bit)) /* Put in the first place bit position */
(7) Judge the value of some consecutive bits
/* For the first [n:m] The value of a */
#define BIT_M_TO_N(x, m, n) ((unsigned int)(x << (31-(n))) >> ((31 - (n)) + (m)))Nine : Judge the value of a bit
#include <stdio.h>
int main (void){
unsigned int a = 0x68;
if(a & (1 <<3)){
printf("0x68 The third value bit of 1\n");
}else {
printf("0x68 The third value bit of 0\n");
}
}Ten : The remainder
int a=X%Y;Y Must be 2^N.
Formula for :a=X&(2^N-1) perhaps a=X &( ~Y);11、 ... and : Division operations
a=a*4 Change to bit operation a=a<<2;
a=a/4 Change to bit operation a=a>>2;Twelve : Get the value of consecutive digits
#define CALC_MASK(offset,len,mask) \
if((offset+len)>16) \
{ \
return error; \
} \
else \
mask = (((1<<(offset+len)))-(1<<offset))
\\ data obtain bit6 and bit7 Value ;
CALC_MASK(6,2,mask);
usData=(data&mask)>>6;边栏推荐
- Research Report on the overall scale, major producers, major regions, products and application segmentation of agricultural automatic steering system in the global market in 2022
- Hand drawn video website
- 107. Some details of SAP ui5 overflow toolbar container control and resize event processing
- FEG founder rox:smartdefi will be the benchmark of the entire decentralized financial market
- 微信小程序:星宿UI V1.5 wordpress系统资讯资源博客下载小程序微信QQ双端源码支持wordpress二级分类 加载动画优化
- [microprocessor] VHDL development of microprocessor based on FPGA
- [flutter topic] 64 illustration basic textfield text input box (I) # yyds dry goods inventory #
- Compare whether two lists are equal
- Express routing, express middleware, using express write interface
- Database postragesql lock management
猜你喜欢
资深测试/开发程序员写下无bug?资历(枷锁)不要惧怕错误......
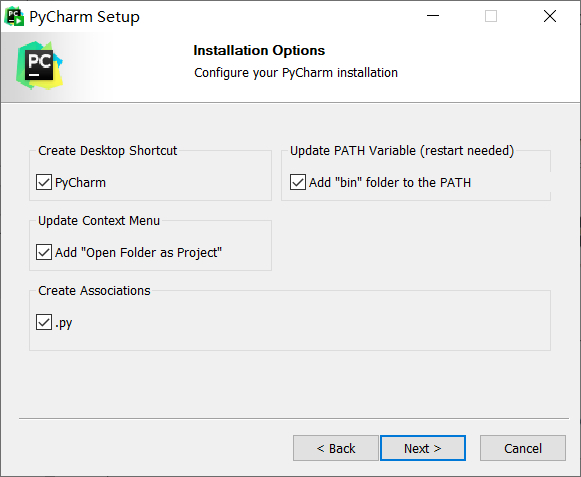
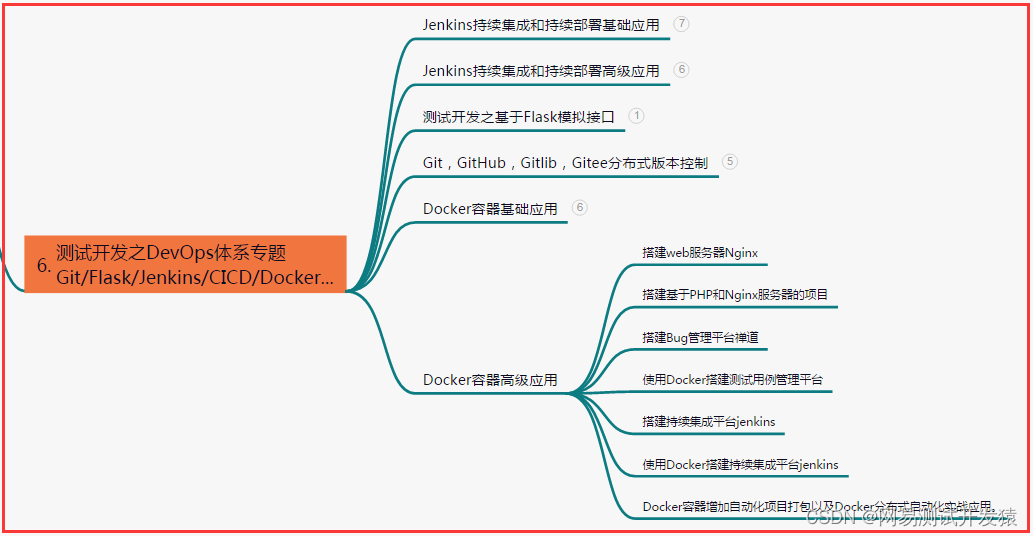
Pycharm professional download and installation tutorial
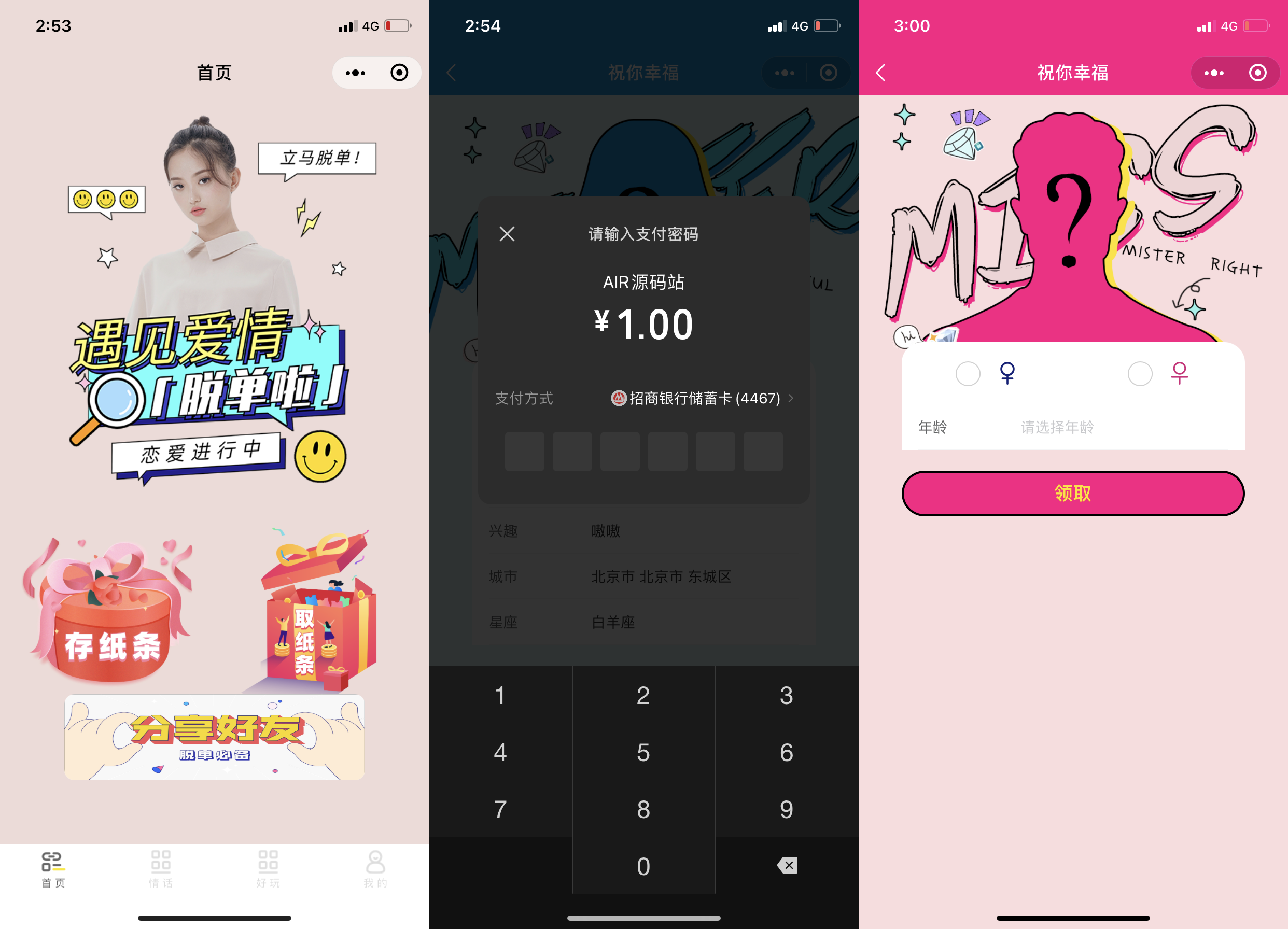
Wechat applet: new independent backstage Yuelao office one yuan dating blind box
Basic operation of database and table ----- phased test II
Senior Test / development programmers write no bugs? Qualifications (shackles) don't be afraid of mistakes
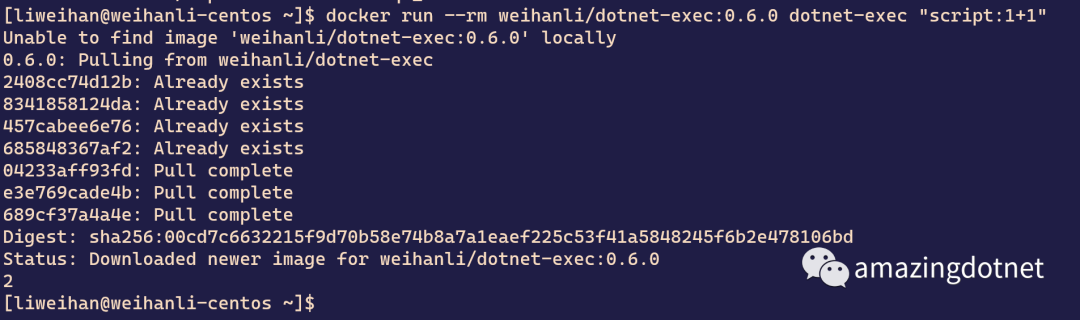
dotnet-exec 0.6.0 released
I was beaten by the interviewer because I didn't understand the sorting
PHP wechat official account development
Inventory of more than 17 typical security incidents in January 2022

26.2 billion! These universities in Guangdong Province have received heavy support
随机推荐
资深测试/开发程序员写下无bug?资历(枷锁)不要惧怕错误......
POAP:NFT的采用入口?
[flutter topic] 64 illustration basic textfield text input box (I) # yyds dry goods inventory #
Inventory of more than 17 typical security incidents in January 2022
Check if this is null - checking if this is null
ROS command line tool
Senior Test / development programmers write no bugs? Qualifications (shackles) don't be afraid of mistakes
User login function: simple but difficult
26.2 billion! These universities in Guangdong Province have received heavy support
小程序直播 + 电商,想做新零售电商就用它吧!
Postman automatically fills headers
微信小程序:星宿UI V1.5 wordpress系统资讯资源博客下载小程序微信QQ双端源码支持wordpress二级分类 加载动画优化
Analysis and comparison of leetcode weekly race + acwing weekly race (t4/t3)
Introduction to the gtid mode of MySQL master-slave replication
Delaying wages to force people to leave, and the layoffs of small Internet companies are a little too much!
Poap: the adoption entrance of NFT?
La jeunesse sans rancune de Xi Murong
抓包整理外篇——————状态栏[ 四]
What happened to those who focused on automated testing?
Using openpyxl module to write the binary list into excel file