当前位置:网站首页>CTF competition problem solution STM32 reverse introduction
CTF competition problem solution STM32 reverse introduction
2022-07-04 23:10:00 【Hetian network security laboratory】
The firmware security
One 、 Preface
Today's learning record
Two 、 Reappear
1、SCTF 2020 Password Lock
Title Description
This is a STM32F103C8T6 MCU Password lock it has 4 A button , Respectively 1, 2, 3, 4. They correspond to each other GPIO_PA1, GPIO_PA2, GPIO_PA3, GPIO_PA4flag1 The format is SCTF{ Correct key password } Enter the correct password , It will pass the serial port (PA9–TX) send out flag2
Their thinking
The attachment of the title gives a Intel hex file , And given the chip information, we can determine the memory layout of the program and the correspondence between peripheral registers and memory . The key to reverse is to understand the meaning of program code , Next, we will analyze this step by step hex file .
1. hex File structure
Intel hex The file format consists of plain text , It contains information such as the loading address and entry address of the program , Reading this information can help us quickly locate the starting entry of the program instead of ida To configure .
Read Intel hex file
We can use a text editor to open the title attachment , The key information is as follows :
:020000040800F2 ... ... :04000005080000ED02 :00000001FF
The program loading address is
0x08000000The program entry address is
0x080000EDProcedure to
:00000001FFendingThe rest is all file data
2、 Memory layout
Find the website of the chip manual :https://www.alldatasheet.com/ Inside we can find STM32F103C8T6 Manuals , The first page finds some information we need

Flash memory:32-to-128 Kbytes
SRAM:6-to-20 Kbytes
31 page Memory Map It can let us more intuitively understand the detailed layout of memory

To sum up, we got the complete memory layout information of the program :
Flash Memory: 0x8000000 ~ 0x801FFFF (128K)
SRAM: 0x20000000 ~ 0x20004FFF (20K)
Peripherals: 0x40000000 ~ 0x40023400
【---- Help network security learn , All the following learning materials are free ! Add weix:yj009991, remarks “ csdn ” obtain !】
① Thinking map of the growth path of Network Security Learning
② 60+ Network security classic common toolkit
③ 100+SRC Vulnerability analysis report
④ 150+ Network security attack and defense technology ebook
⑤ The most authoritative CISSP Certification test guide + Question bank
⑥ super 1800 page CTF Practical skills manual
3、IDA analysis
After the analysis just now, we know the memory layout of the program , among Flash In addition to containing code , And interrupt vector table .Periphers The register in the segment is that we need to have a general understanding of alignment in the reverse process . And for hex Through the analysis of the file, we learned that in addition to the loading address and entry address , Everything else is gone hex In file , So we need to manually configure these memory layout information to tell IDA How to identify . open ida Tools , According to the manual just now, we can find that the chip is arm32 Armv7-M framework , Select the configuration as shown in the following figure, and then click ok
You can see that some functions can be recognized , among start The address of the function is analyzed with us hex The program entry address found in the file structure is the same .

If hex The entry address information is not given in the file. We can also find RESET Interrupt handler function to determine program entry function . among RESET The address of the interrupt function can be in STM32 Chinese Reference Manual V10.pdf Find relevant information in

Reference resources STM32 The location of the interrupt vector table 、 Redirect We can see in the interrupt vector table RESET The address of 0x8000004 The address is fixed , What is changeable is the loading address of the program . We jump to 0x8000004 On this address , Press keyboard D The key divides the above data into 4 Byte form found reset The address for 0x8000101

Jump to RESET Interrupt handling function , There are two jumps . Jump to for the first time nullsub_1 Up and put the address of the next instruction into LR register ,nullsub_1 The function is to jump back LR Address in register , So the first jump is meaningless . The second jump is ours start Address , So you can use this method to locate the entry address of the program .

You can find this program by following the entry address all the time main Where is the function , But after entering, you can find a large red mark on the left , Observing these red areas is actually IDA Unrecognized address , That is, the memory segments we need to add before analyzing the memory layout .

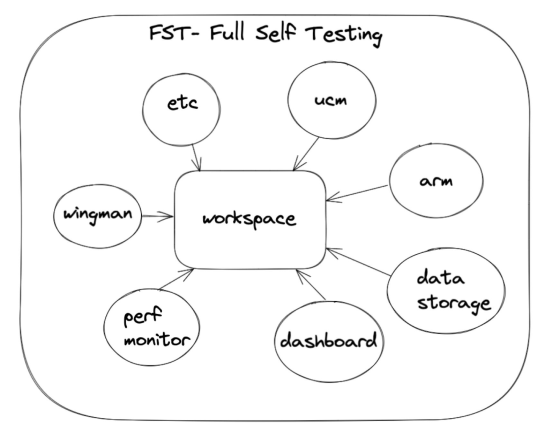
We are IDA New China Segment, As shown in the figure below :

At this time, as long as we click again F5 You can turn these red signs into memory for normal recognition

4、 Fix interrupt vector table
Use IDApython Recover the information before the program entry address
for i in range(0x8000000,0x80000eb,1):
del_items(i)
for i in range(0x8000000,0x80000eb,4):
create_dword(i) After the repair, we observe the address inside , You will find many duplicate addresses 0x800016D, You will find that there is no function defined in these addresses . Continue to check the interrupt vector table and you will find the following different memory addresses

Reference resources STM32 Chinese Reference Manual V10.pdf We can find these in EXTI Address of the interrupt handling function

stm32-EXTI
Follow up these function addresses and you will find IDA It is not recognized as a function , So let's first press... At the starting address of the function P key , Then disassemble to see these interrupt handling functions , Here I use EXTI_4 Take the interrupt handling function of as an example to briefly introduce the functions of these interrupt handling functions .
int EXTI_4()
{
int result; // r0
EXTI_LINE = 16;
switch ( sum )
{
case 1:
unk_20000006 = 116;
return sum++ + 1;
case 2:
unk_20000010 = 95;
return sum++ + 1;
case 4:
unk_2000000E = unk_20000001;
return sum++ + 1;
default:
result = 0;
sum = 0;
break;
}
return result;
} The program starts with an interrupt / Event line ,EXTI_4 The interrupt / The event line is 0x10, Then use a piece of memory ( It's written here sum) As the storage location of the accumulated number . We can see when sum The value of 1、2、4 when sum It's worth it +1, If not, it will start again . So we can judge 1、2、4 Namely EXTI_4 The number of digits appearing in the password , Similarly, the other three buttons are the same , Through these sequences, we can get the final flag by flag{1442413}, And we can find in main In the function, the program first simulated the input of a password , By comparing the above value with EXTI_LINE We can also get flag value .
2、2021 HWS Enter the camp -STM32
After the introduction of the previous question, let's practice another question , open IDA Type selection segment arm32, Schema selection ARMv7-M framework .
Next, set the loading address and reading address of the program to 0x8000000, The loading address refers to IDA What is the analysis address loaded , and Input File It refers to where the firmware should be loaded , After setting, we click OK Complete set .

After entering, you will find IDA No function was recognized , Don't worry, we can locate reset Interrupt processing to find main Position of function . take 0x8000004 The byte at the address becomes 4 byte , obtain reset Interrupt handler address 0x8000101.

You can find that the end of the address is an odd digit , stay arm This represents thumb Pattern . We can do it in 0x8000101 Address press C Key to generate code

Follow the program all the time and we will find main Function location sub_80003C0, And found the function that needs to be reversed sub_8000314
_BYTE *sub_8000314()
{
_BYTE *v0; // r4
char *v1; // r5
int v2; // r6
char v3; // t1
v0 = (_BYTE *)sub_80003F0(48);
v1 = &byte_8000344;
v2 = 0;
while ( v2++ != 0 )
{
v3 = *v1++;
*v0++ = (v3 ^ 0x1E) + 3;
sub_8000124(v1);
}
return v0;
}
Write a problem-solving script to get flag value
li = [0x7D, 0x77, 0x40, 0x7A, 0x66, 0x30, 0x2A, 0x2F, 0x28, 0x40, 0x7E, 0x30, 0x33, 0x34, 0x2C, 0x2E, 0x2B, 0x28, 0x34, 0x30, 0x30, 0x7C, 0x41, 0x34, 0x28, 0x33, 0x7E, 0x30, 0x34, 0x33, 0x33, 0x30, 0x7E, 0x2F, 0x31, 0x2A, 0x41, 0x7F, 0x2F, 0x28, 0x2E, 0x64]
print(''.join(chr((i ^ 0x1E) + 3) for i in li))边栏推荐
- Qt加法计算器(简单案例)
- ECS settings SSH key login
- Redis:Redis消息的发布与订阅(了解)
- 【室友用一局王者荣耀的时间学会了用BI报表数据处理】
- Google Earth engine (GEE) - globfire daily fire data set based on mcd64a1
- mamp下缺少pcntl扩展的解决办法,Fatal error: Call to undefined function pcntl_signal()
- Docker镜像的缓存特性和Dockerfile
- HMS core unified scanning service
- [machine learning] handwritten digit recognition
- Redis: redis transactions
猜你喜欢

The small program vant tab component solves the problem of too much text and incomplete display
Duplicate ADMAS part name
On-off and on-off of quality system construction
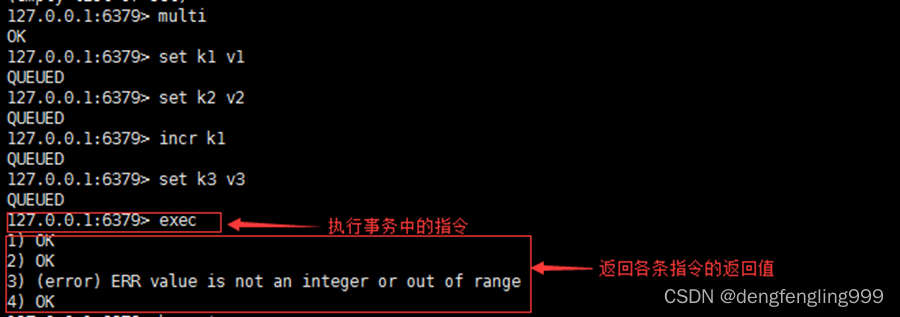
Redis: redis transactions
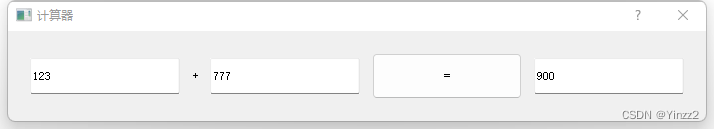
Qt加法计算器(简单案例)
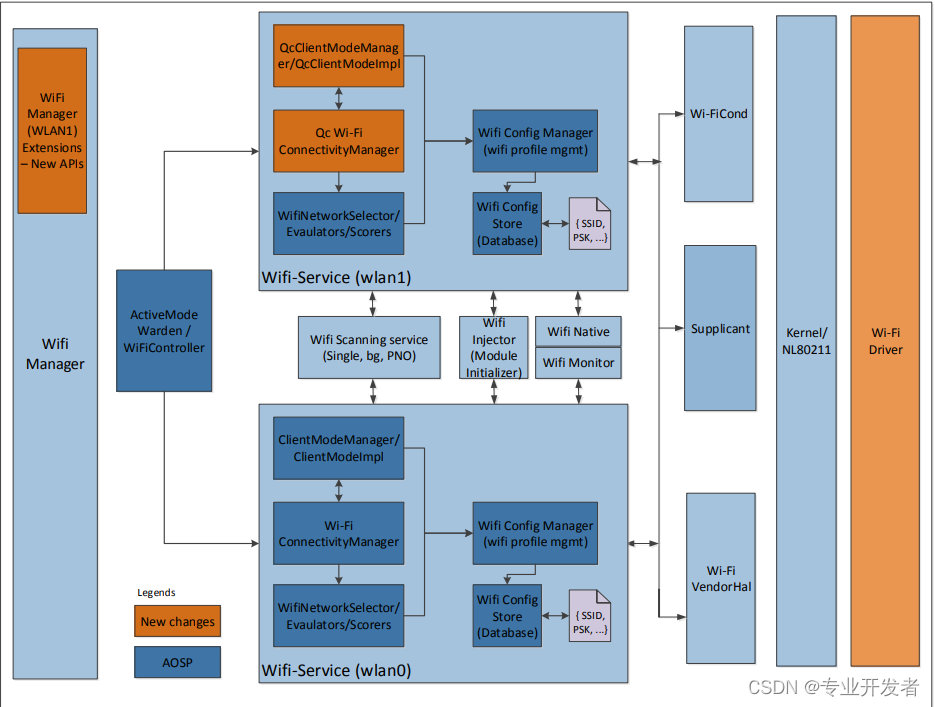
高通WLAN框架学习(30)-- 支持双STA的组件
PS style JS webpage graffiti board plug-in

OSEK标准ISO_17356汇总介绍
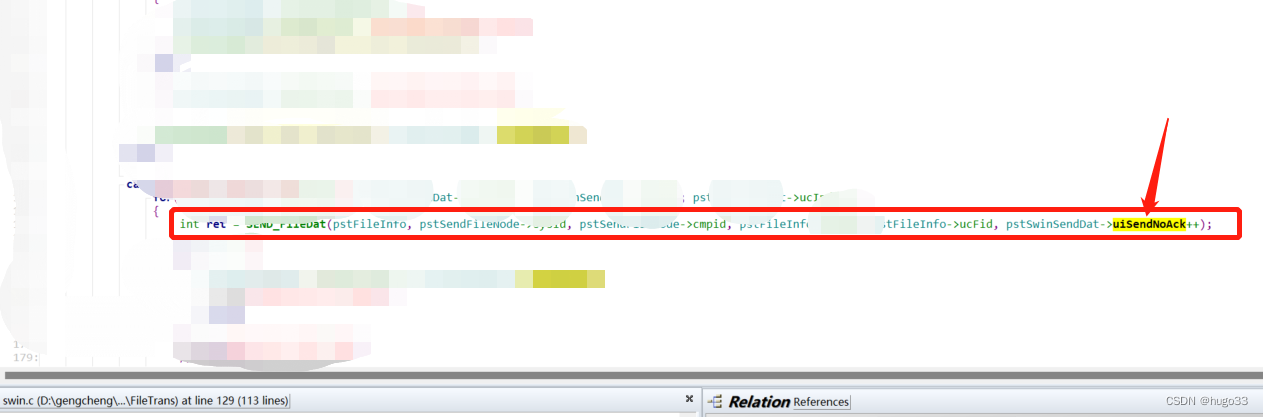
Analysis of the self increasing and self decreasing of C language function parameters

为什么信息图会帮助你的SEO
随机推荐
The small program vant tab component solves the problem of too much text and incomplete display
【taichi】用最少的修改将太极的pbf2d(基于位置的流体模拟)改为pbf3d
初试为锐捷交换机跨设备型号升级版本(以RG-S2952G-E为例)
图片懒加载的原理
VIM editor knowledge summary
金融市场,资产管理与投资基金
LIst 相关待整理的知识点
heatmap. JS picture hotspot heat map plug-in
【机器学习】手写数字识别
Redis入门完整教程:Redis使用场景
JS 3D explosive fragment image switching JS special effect
常用技术指标之一文读懂BOLL布林线指标
Redis:Redis的事务
Redis入门完整教程:初识Redis
Sword finger offer 65 Add without adding, subtracting, multiplying, dividing
Advanced area a of attack and defense world misc Masters_ good_ idea
One of the commonly used technical indicators, reading boll Bollinger line indicators
debug和release的区别
【图论】拓扑排序
P2181 对角线和P1030 [NOIP2001 普及组] 求先序排列