当前位置:网站首页>security CSRF Vulnerability Protection
security CSRF Vulnerability Protection
2022-08-02 00:07:00 【Three or two lines of program】
I. Overview of CSRF
xss exploits user trust in websites
csrf exploits the website's trust in the user's browser
Example

Second, CSRF defense
1. Defense strategy
Through the token synchronization mode, in addition to the default cookie parameter in each http request, the server generates a random string called csrf token. After opening, the httpsession saves a copy, and the front-end request arrivesWhen comparing the requested csrf token information with the server, if they are not equal, the http request will be rejected
Considering that the website may place external links, it is required to be idempotent when requesting, so there is no need to use CSRF tokens for methods such as HEAD OPTIONS TRACE. Forcible use may lead to token leakage
2. Traditional web development configuration
@Configurationpublic class SecurityConfig extends WebSecurityConfigurerAdapter {@Overrideprotected void configure(HttpSecurity http) throws Exception {http.authorizeRequests().anyRequest().authenticated().and().formLogin().and()//Open csrf.csrf();}}
3. Front-end and back-end separation configuration
The default is that csrf is stored in the server httpsession. In front-end and back-end separation, it is necessary to put the generated csrf into the cookie and obtain the token in the cookie for submission when requesting.
Modify csrf into cookie
@Configurationpublic class SecurityConfig extends WebSecurityConfigurerAdapter {@Overrideprotected void configure(HttpSecurity http) throws Exception {http.authorizeRequests().anyRequest().authenticated().and().formLogin().and()//Open csrf.csrf()//Save the token to the cookie and allow the cookie front end to get it.csrfTokenRepository(CookieCsrfTokenRepository.withHttpOnlyFalse());}}Visit the login interface to view cookies

Send request with token
The first type: request other interfaces and carry it in the request header
X-XSRF-TOKEN:value in cookie
The second type: carry in the request parameters
_csrf:value in cookie
边栏推荐
猜你喜欢

TCP 可靠吗?为什么?

邻接表与邻接矩阵

security CSRF漏洞保护
一个有些意思的项目--文件夹对比工具(一)

Excel表格数据导入MySQL数据库
Docker实践经验:Docker 上部署 mysql8 主从复制
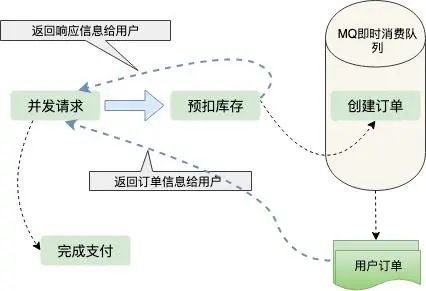
12306抢票,极限并发带来的思考?

使用Ganache、web3.js和remix在私有链上部署并调用合约

Secondary Vocational Network Security Competition B7 Competition Deployment Process

cdh6 opens oozieWeb page, Oozie web console is disabled.
随机推荐
【Leetcode】1206. Design Skiplist
类型“FC<Props>”的参数不能赋给类型“ForwardRefRenderFunction<unknown, Props>”的参数。 属性“defaultProps”的类型不兼容。 不
GIF制作-灰常简单的一键动图工具
递归:方法调用自身
Enterprise firewall management, what firewall management tools are there?
The Spark of Sql join on the and and where
UI自动化测试框架搭建-标记性能较差用例
【ACWing】230. 排列计数
The third chapter of the imitation cattle network project: develop the core functions of the community (detailed steps and ideas)
asyncawait和promise的区别
ICLR 2022 Best Paper: Partial Label Learning Based on Contrastive Disambiguation
ELK日志采集
云原生DevOps环境搭建
Wincc报表教程(SQL数据库的建立,wincc在数据库中保存和查询数据,调用Excel模板把数据保存到指定的位置和打印功能)
TexturePacker使用文档
Thymeleaf简介
Spark Sql之union
在linux下MySQL的常用操作命令
20220725 Information update
QML包管理