当前位置:网站首页>Niuke real problem programming - day18
Niuke real problem programming - day18
2022-07-07 14:53:00 【weixin_ forty-five million seven hundred and fifty thousand fou】
Compile environment :c++
1、 Expression legal judgment
describe :
Write a piece of code , Judge one including '{','[','(',')',']','}' Whether the expression of is legal ( Pay attention to the legal rules in the sample .)
You can see a legal expression , The left and right parentheses must correspond to each other .
Given an expression A, Please return one bool value , Represents whether it is legal .
Algorithmic thought :
The title does not give a clear description , You can pass the test without considering the order of the left and right parentheses , Therefore, you only need to judge whether the number of left and right parentheses matches , Left bracket self addition 1, The right bracket is subtracted , If the last count is 0, Then it's legal .
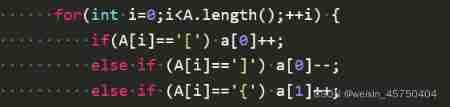
The code part implements :
2、 Remove duplicate characters
describe :
Niuniu has a string of lowercase letters s, stay s There may be some repeated letters in . For example "banana" in , Letter 'a' And letters 'n' Three times and two times respectively .
But Niuniu doesn't like repetition . For the same letter , He just wants to keep the first appearance and delete the following letters . Please help Niuniu finish the right s The operation of .
Algorithmic thought :
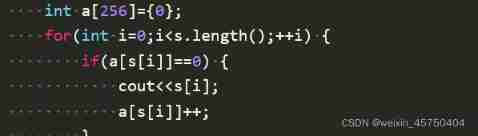
Using character conversion ascii Code for the number of times each letter appears , When count is 0 when , Output the string element that appears for the first time .
3、 Fort attack
describe
After Rambo taught Timo , Then discuss the Yodel people with Timo , Talking about the Yodel people , Naturally, there is no shortage of one person , that It's heimerdinger ------ The greatest scientist in the history of the Yodel people . Timo said , Heimodinger has been thinking about a problem recently : Heimerdinger has three forts , The fort can attack at a distance of less than or equal to R The enemy of ( The distance between two points is the linear distance between two points , for example (3,0),(0,4) The distance between them is 5), If a fort can attack To the enemy , Then it will cause 1× The damage of . Heimerdinger put three forts on N*M On the dot in the square , And give the enemy Coordinates of . ask : How much damage will the enemy suffer ?
Algorithmic thought :
The topic has multiple sets of use case input , For each use case input , Record the point coordinates of the corresponding fort and the enemy , Calculate the distance between two points respectively and compare with the range of the fort .
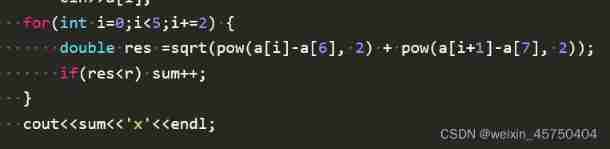
The code part implements :
边栏推荐
- Niuke real problem programming - day13
- Pandora IOT development board learning (HAL Library) - Experiment 12 RTC real-time clock experiment (learning notes)
- 拼多多败诉,砍价始终差0.9%一案宣判;微信内测同一手机号可注册两个账号功能;2022年度菲尔兹奖公布|极客头条...
- 广州开发区让地理标志产品助力乡村振兴
- Instructions d'utilisation de la trousse de développement du module d'acquisition d'accord du testeur mictr01
- 关于后台动态模板添加内容的总结 Builder使用
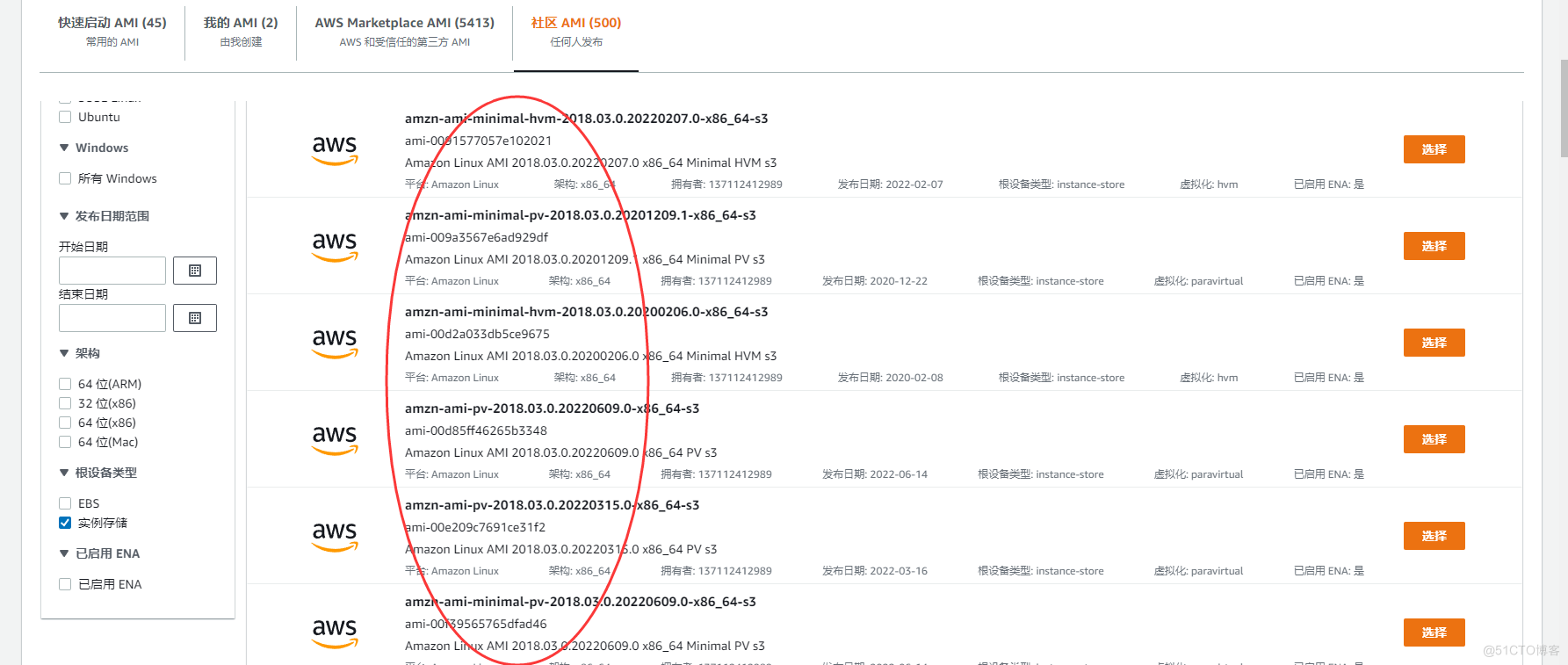
- AWS学习笔记(三)
- 用于增强压缩视频质量的可变形卷积密集网络
- Niuke real problem programming - day16
- 6、Electron无边框窗口和透明窗口 锁定模式 设置窗口图标
猜你喜欢
随机推荐
Lidar knowledge drops
Stm32cubemx, 68 sets of components, following 10 open source protocols
数据库如何进行动态自定义排序?
Yyds dry goods inventory # solve the real problem of famous enterprises: cross line
广州开发区让地理标志产品助力乡村振兴
Webrtc audio anti weak network technology (Part 1)
PLC:自动纠正数据集噪声,来洗洗数据集吧 | ICLR 2021 Spotlight
数据湖(九):Iceberg特点详述和数据类型
Classification of regression tests
word中删除一整页
Niuke real problem programming - Day9
Xiaomi's path of chip self-development
Cocos creator direction and angle conversion
⼀个对象从加载到JVM,再到被GC清除,都经历了什么过程?
PyTorch模型训练实战技巧,突破速度瓶颈
WebRTC 音频抗弱网技术(上)
Promoted to P8 successfully in the first half of the year, and bought a villa!
【服务器数据恢复】某品牌StorageWorks服务器raid数据恢复案例
2022云顾问技术系列之高可用专场分享会
Navigation — 这么好用的导航框架你确定不来看看?