当前位置:网站首页>According to the atlas of data security products and services issued by the China Academy of information technology, meichuang technology has achieved full coverage of four major sectors
According to the atlas of data security products and services issued by the China Academy of information technology, meichuang technology has achieved full coverage of four major sectors
2022-07-02 16:29:00 【Ink Sky Wheel】

In recent days, , By China Academy of information and communication 、 China Communications Standardization Association , The big data industry summit hosted by the big data technology standards Promotion Committee of China Communications Standardization Association was held . At the meeting , China information and Communication Research Institute officially released 《 Database Development Research Report (2022)》 and 《 Global database industry map 》、《 Map of data security products and services 1.0》.
Meichuang technology was selected 《 Global database industry map 》 The database security camp represents enterprises , Products and services are fully covered 《 Map of data security products and services 》 Data security protection detection 、 Data security operation and maintenance 、 Data security sharing and circulation 、 Data security services 4 Large plate , shortlisted 12 Item segmentation .
《 Global database industry map 》

Involving data ( library ) More than ten years in the field of safety , Meichuang technology is based on the in-depth study of database kernel technology , A leading data security product service matrix has been formed , Participate in data desensitization 、( database ) A firewall 、 Data backup and recovery, etc 10 More than national standards are formulated ,5 Department of database technology and data security research works , It is the technical support unit of the national network and information security information notification mechanism 、CNCERT Provincial support unit for network security emergency service 、 Zhejiang meichuang Sensitive Information Security Research Institute .
The development of digitalization puts forward new requirements for data security , Based on the new generation of zero trust data security architecture 、 Intrusion lifecycle 、 Risk management , Meichuang Technology From data security governance consulting 、 Product capability configuration in the whole life cycle of data 、 Data security operation platform based on comprehensive data security capability , Build overlay data access security for users 、 Data flow security 、 External intrusion security 、 A new generation of active data security protection system under the scenes of blackmail virus protection .
1
Consulting planning based on data security governance : Take data security governance as the starting point , Help users build more comprehensive 、 More targeted data security planning and compliance construction .
2
Product system based on the whole life cycle of data : With database security 、 Audit cloud management 、 Terminal security 、 Disaster recovery replication 、 Flow control and other complete product lines , Security protection covering the whole life cycle of data .
3
Data security operation platform based on comprehensive data security capability : Standardize management with assets 、 Secure multi terminal linkage 、 High efficiency intelligent management ability of operational value-added , Fully activate the data security protection scenario , Improve the overall operation level of data security .
《 Map of data security products and services 》

《 Map of data security products and services 1.0》 Including data security protection detection 、 Data security operation and maintenance 、 Data security sharing and circulation 、 There are four parts of data security services . Meichuang covers all , Involving terminal safety protection ( Anti blackmail )、 Database firewall 、 Data desensitization 、 Data watermark traceability 、 Database audit, etc 12 Item segmentation , With first-class product technology ability and continuous innovation accumulation , Widely in the government 、 Finance 、 Medical care 、 Logistics, transportation and other industries , Fully recognized by the market .

Data desensitization :1 National standards 、5 Participate in the formulation of local industry standards , Two years in a row CCIA Network security innovation product excellence award .
Database firewall : Firewall national standard - The core drafting unit of database firewall
Noah anti blackmail : Zero trust blackmail software protection represents manufacturers , a 2020 CCIA Network security Double award recognition for excellent and most investment value of fully innovative products
Data watermark traceability : It was selected into the first edition of software application and promotion guidance directory in Zhejiang Province
Database security audit : The first batch passed the functional evaluation of data security products of China Academy of communications 、 Golden wisdom award annual excellent product award

Data security management platform :2022 Leading scientific and technological achievement award of data blog , The unique multi tenant function has been successfully implemented in the big data Bureau
Dark data discovery and classification : The first batch passed the authoritative evaluation of China Academy of communications ( The first four companies ), government affairs 、 Finance 、 Take the lead in manufacturing .
Data security operation platform : Innovative combination CARTA Model , The whole scene 、 Closed loop data security operation

Data flow control platform :API Level data flow control 、 Data protection and value mining , Master the data flow situation of the whole link

Data security governance consulting : Finance 、 The government 、 Energy enterprises took the lead in landing , Help users acquire the data security governance capability of China Academy of communications (DSG) Evaluate excellent grade
Data security risk assessment : Improve the data security risk assessment system and professional consulting team ,500 Strong enterprise 、 Large energy groups have successful cases
Blackmail virus defense Insurance : The first blackmail Protection Insurance , Realize the whole process risk prevention and control of extortion defense
Besides , In the field of data security training , Ad hoc art and entrepreneurship College , It is the national plan for improving the ability of electronic information talents - Training base , Have a perfect curriculum system and lecturer team ; Emergency response and drill , yes Technical support unit of national network and information security information notification mechanism 、CNCERT Provincial support sheet for network security emergency services position 、 Network security technical support unit of Network Information Office of Zhejiang provincial Party committee ; Data classification , With a perfect landing methodology 、 The consulting team and product solutions are practiced in various industries .
At this conference , Hebaohong, director of the Institute of cloud computing and big data, China Academy of communications and communications, released “2022 Ten key words of big data ”. He Baohong pointed out that , With data officially becoming a factor of production ,2022 year , Policies in the field 、 idea 、 technology 、 Security and other aspects are booming around this main line .
policy :“ Data elements unify the big market 、 Data management capability maturity ” Further improve the top-level design ; In terms of concept :“ Data center 、 Data valuation 、DataOps” Continue to consolidate the theoretical foundation of enterprise digital intelligence transformation ; Technical aspects ,“ Innovative database 、 Privacy computing all-in-one machine 、 Figure calculation ” Strongly support the value mining and efficient circulation of data elements ; security ,“ Data security compliance 、 Data classification ” Promote further clarity of the red line of the data industry .







边栏推荐
- Maui learning road (III) -- in depth discussion of winui3
- Song of cactus - throwing stones to ask the way (3)
- Yyds dry inventory KVM new inventory to expand space for home
- 数学分析_笔记_第6章:一元函数的Riemann积分
- 2022 the latest and most detailed will successfully set the background image in vscade and solve unsupported problems at the same time
- Yyds dry inventory executor package (parameter processing function)
- 数据安全产业系列沙龙(三)| 数据安全产业标准体系建设主题沙龙
- Classifier visual interpretation stylex: Google, MIT, etc. have found the key attributes that affect image classification
- 总结|机器视觉中三大坐标系及其相互关系
- Figure database | Nepal graph v3.1.0 performance report
猜你喜欢

头条 | 亚控科技产品入选中纺联《纺织服装行业数字化转型解决方案重点推广名录》

月报总结|Moonbeam6月份大事一览

mysql min() 求某条件下最小的值出现多个结果

MySQL calculates the data within the longitude and latitude range

Summary | three coordinate systems in machine vision and their relationships

解决** WARNING ** : Your ApplicationContext is unlikely to start due to a @ComponentScan of the defau
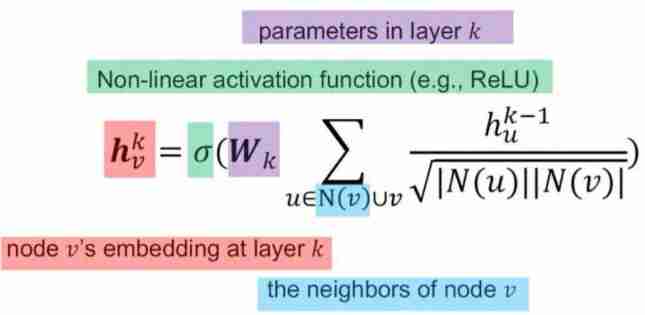
dried food! Understand the structural vulnerability of graph convolution networks

华为云服务器安装mysqlb for mysqld.service failed because the control process exited with error code.See “sys
SSM integration exception handler and project exception handling scheme

Write your own CPU Chapter 11 - learning notes
随机推荐
Register as a harmonios developer and install deveco studio 3.0 beta2 for harmonios
End time processing method of wechat v3native payment settings
Foreign enterprise executives, continuous entrepreneurs, yoga and skiing masters, and a program life of continuous iteration and reconstruction
图书管理系统(山东农业大学课程设计)
OSPF - detailed explanation of NSSA area and full NSSA area (including configuration command), LSA type 7 lsa-7
[fluent] dart language (DART language features | JIT instant compilation | AOT static compilation)
mysql 计算经纬度范围内的数据
Text intelligent expansion and contraction control of swiftui text component (tutorial includes source code)
Aike AI frontier promotion (2.15)
Understand the key technology of AGV -- the difference between laser slam and visual slam
2022 the latest and most detailed will successfully set the background image in vscade and solve unsupported problems at the same time
day4
Yyds dry inventory method of deleting expired documents in batch
Solve * * warning * *: your ApplicationContext is unlikely to start due to a @componentscan of the defau
Best practices for building multi architecture images
数学分析_笔记_第6章:一元函数的Riemann积分
电脑设备打印机驱动安装失败如何解决
死锁的条件及解决方法
Seal Library - installation and introduction
Dimension table and fact table in data warehouse