当前位置:网站首页>Serious security vulnerabilities reported by moxa mxview network management software
Serious security vulnerabilities reported by moxa mxview network management software
2022-07-03 02:40:00 【Khan security team】
Some effects have been disclosed Moxa MXview be based on Web Technical details of the security vulnerability of the network management system , Some of them may be linked by unauthenticated attackers , To achieve remote code execution on unpatched servers .
Claroty Security researcher Noam Moshe In a report released this week , These five security vulnerabilities “ May allow remote 、 An unauthenticated attacker executes code on the host with the highest available privileges :NT AUTHORITY\SYSTEM” .
Moxa MXview Designed to configure 、 Designed to monitor and diagnose network equipment in Industrial Networks . These affect network management software 3.x to 3.2.2 The defect of the version is 2021 year 10 After the coordinated disclosure process in January, it will be in 3.2.4 Or later .
“ Successful exploitation of these vulnerabilities may allow attackers to create or overwrite critical files to execute code 、 Access program 、 Obtain the credentials 、 Disable Software 、 Read and modify other inaccessible data 、 Allow remote connection to internal communication channels or interaction and remote use MQTT,” U.S. cybersecurity and Infrastructure Security Agency (CISA) In an announcement, it said .
MQTT It refers to a message passing protocol that promotes remote asynchronous communication , Support in MXview Messages are transferred between different components in the environment .
The list of defects is as follows ——
- CVE-2021-38452(CVSS score :7.5)- Path traversal vulnerability in applications , Allow access to or overwrite key files used to execute code
- CVE-2021-38454(CVSS fraction :10.0)- Allow remote connections to MQTT Misconfigured service , Thus, it can interact and use communication channels remotely
- CVE-2021-38456(CVSS fraction :9.8)- Use hard coded passwords
- CVE-2021-38458(CVSS fraction :9.8)- Improper neutralization of special elements , It may cause unauthorized commands to be executed remotely
- CVE-2021-38460(CVSS fraction :7.5)- Password disclosure cases that may allow attackers to obtain credentials
The above three vulnerabilities ——CVE-2021-38452、CVE-2021-38454 and CVE-2021-38458 Can be strung together , In vulnerable areas with system privileges MXView Implement pre validated remote code execution on the instance .
stay Claroty In the hypothetical attack scenario designed ,CVE-2021-38452 May be abused , By reading the configuration file gateway-upper.ini To get plain text MQTT password , And then use it CVE-2021-38454 Inject hooligans MQTT news , The command injection on the server triggers code execution .
“ The attacker directed at MQTT The agent injects malicious messages , Bypass all input validation performed by the server , And pass OS Command injection vulnerability enables arbitrary remote code execution ,”Moshe explains .
边栏推荐
- [translation] the background project has joined the CNCF incubator
- Gbase 8C system table PG_ attribute
- 4. Classes and objects
- [flutter] example of asynchronous programming code between future and futurebuilder (futurebuilder constructor setting | handling flutter Chinese garbled | complete code example)
- 二维格式数组格式索引下标连续问题导致 返回json 格式问题
- GBase 8c 触发器(一)
- GBase 8c 函数/存储过程参数(二)
- ASP. Net core 6 framework unveiling example demonstration [02]: application development based on routing, MVC and grpc
- Gbase 8C function / stored procedure parameters (II)
- A2L file parsing based on CAN bus (2)
猜你喜欢
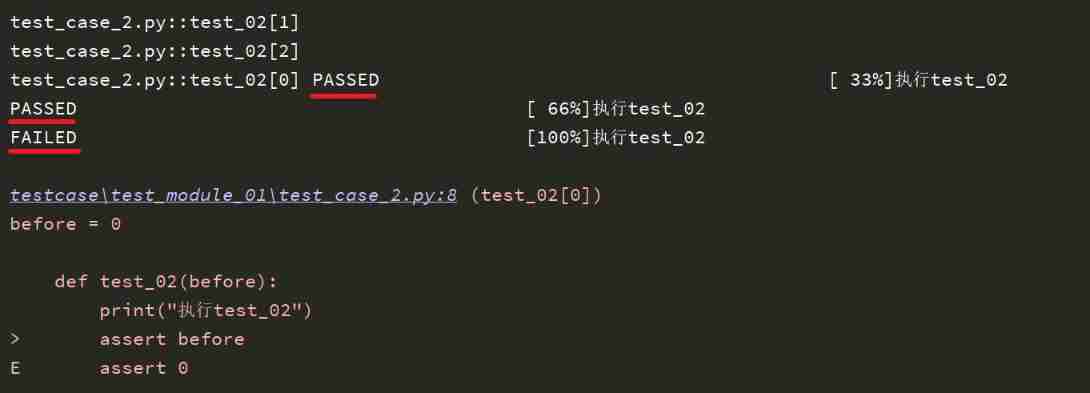
Pytest (6) -fixture (Firmware)
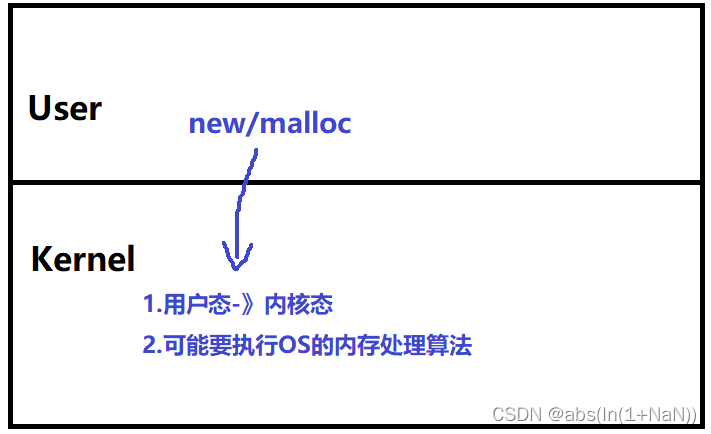
内存池(内核角度理解new开辟空间的过程)
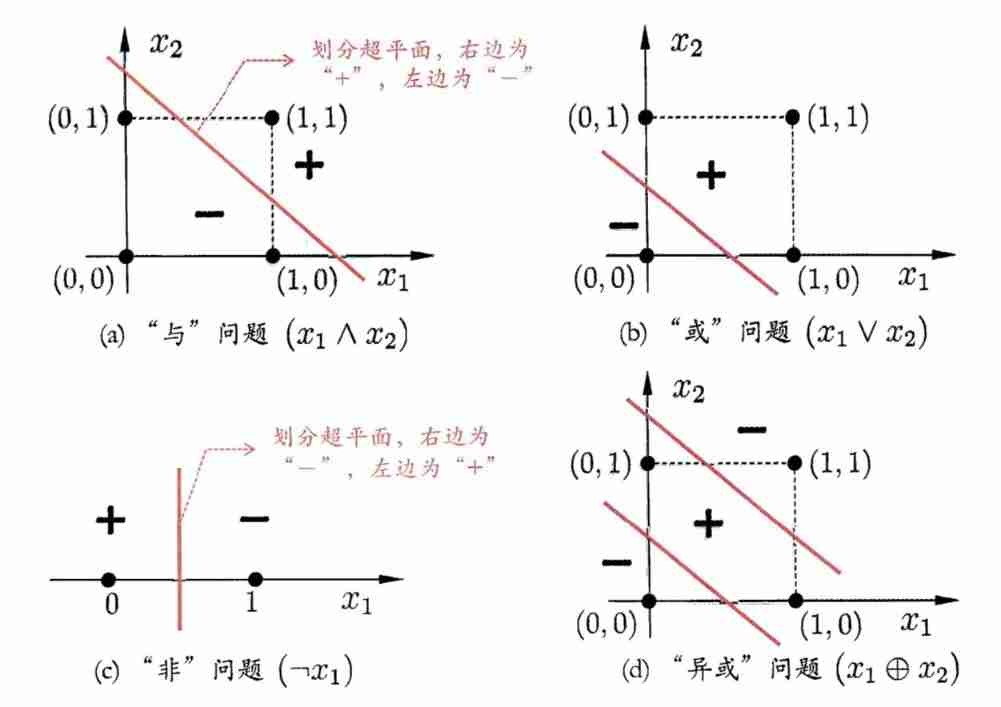
Deep learning: multi-layer perceptron and XOR problem (pytoch Implementation)

Producer consumer model based on thread pool (including blocking queue)
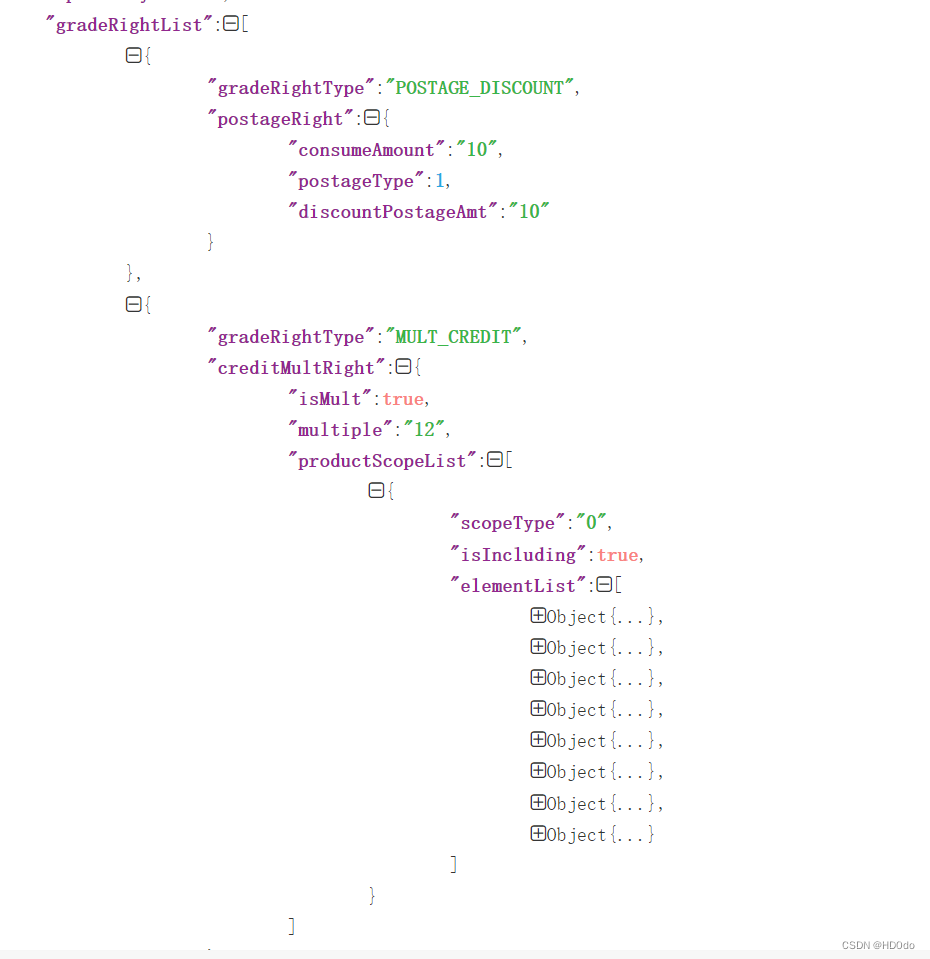
The use of Flink CDC mongodb and the implementation of Flink SQL parsing complex nested JSON data in monggo
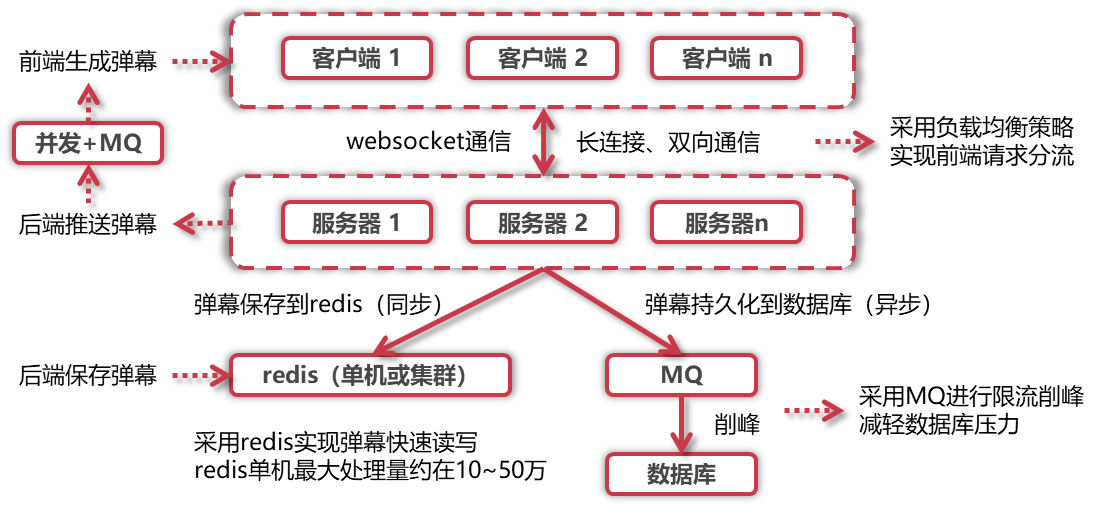
Summary of interview project technology stack
[advanced ROS] Lesson 6 recording and playback in ROS (rosbag)

HW initial preparation
![[fluent] listview list (map method description of list set | vertical list | horizontal list | code example)](/img/e5/c01f760b07b495f5b048ea367e0c21.gif)
[fluent] listview list (map method description of list set | vertical list | horizontal list | code example)
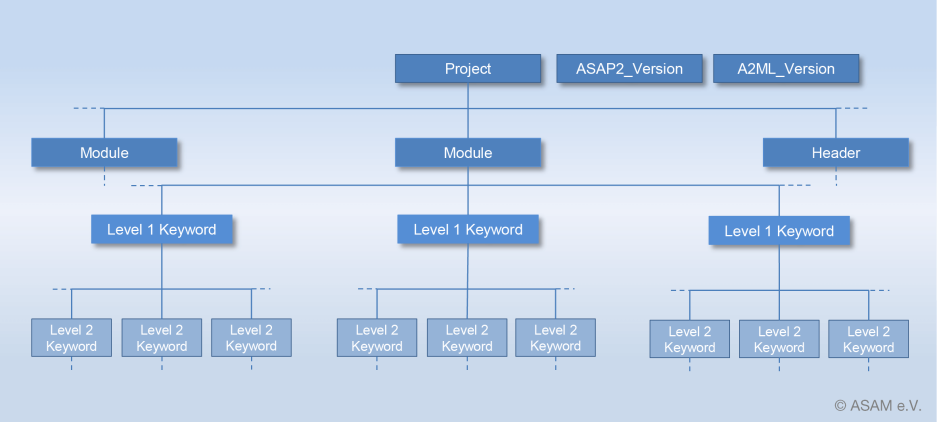
基于can总线的A2L文件解析(2)
随机推荐
Gbase 8C system table PG_ auth_ members
What is the way out for children from poor families?
Oauth2.0 authentication, login and access "/oauth/token", how to get the value of request header authorization (basictoken)???
Gbase 8C system table PG_ collation
[shutter] setup of shutter development environment (supplement the latest information | the latest installation tutorial on August 25, 2021)
sql server 查詢指定錶的錶結構
Error invalid bound statement (not found): com ruoyi. stock. mapper. StockDetailMapper. XXXX solution
Tongda OA homepage portal workbench
[fluent] future asynchronous programming (introduction | then method | exception capture | async, await keywords | whencomplete method | timeout method)
Thread safe singleton mode
[fluent] JSON model conversion (JSON serialization tool | JSON manual serialization | writing dart model classes according to JSON | online automatic conversion of dart classes according to JSON)
Gbase 8C function / stored procedure parameters (II)
Gbase 8C function / stored procedure parameters (I)
Create + register sub apps_ Define routes, global routes and sub routes
Mathematical statistics -- Sampling and sampling distribution
Simple understanding of SVG
[fluent] listview list (map method description of list set | vertical list | horizontal list | code example)
Kubernetes family container housekeeper pod online Q & A?
The Linux server needs to install the agent software EPS (agent) database
Gbase 8C system table PG_ class
![[advanced ROS] Lesson 6 recording and playback in ROS (rosbag)](/img/84/abde1c0d5441eb8dec2bacb60d19e9)