当前位置:网站首页>Qixi Festival earn badges
Qixi Festival earn badges
2022-08-05 04:00:00 【step on step from step on】
The Chinese Valentine's Day is coming!It's time to show the romance of programmers!How are you going to show your love to someone you love?Flower gift?Code confession?Or creative DIY?Or... whatever form, come and show us!
Record the days we walked together
Speaking of single people are not worthy, write code quietly, and bugs are waiting for you. What are you going to do on Qixi Festival? Of course, programmers have to work overtime.After the work is done, the code written can not be reused, and it is not only a view, forget it, it is not a matter of learning the technical documentation, this is life.
Speaking of you want an object,,,,,,,,, okay, I'll give you a new object(); If you want a good figure and good looks, forget it, I'm embarrassed to write it in the constructor.
Speaking of now, it's easy to make an object. You don't have to create a new one yourself, you can just take it directly in the container (just think about it), it's really that simple, and there are places for isolation.No matter how to communicate, by the way, don't we have the container of the whole country.It's really not possible to communicate directly on the phone.Or more advanced communication, you know.Pull away.
Now I like to use middlemen, but it is really easy to use ha,,,,,,,, ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha ha now.
I'm talking about Sa, I don't know, I just wrote it out, this article is completely a badge of water hahaha.
Creative code confession
Sprinkle dog food in the way of programmers, professional and romantic, and worth having!
Let's write a little bit.
1.sql injection official point
SQL injection means web application does not judge the legitimacy of the user input data or the filtering is not strict, the attacker can add a pre-defined query statement in the web application by addingAdditional SQL statement, inIllegal operations are implemented without the administrator's knowledge to achieve deceptionDatabase Server executes any unauthorized query to further obtain corresponding data information.
In my opinion, those hackers at nb point are doing things, hijacking and replacing, adding spaces, and they can still be executed successfully in the database.
So there are two solutions
Placeholder, check if there is more
We all know that placeholders are also the easiest way, but there is a disadvantage that single quotation marks are automatically added, which is ok for normal conditions
For the field or group by or database name is not enough, then how to do it, of course, use the security framework to verify the data and strictly limit the user input to only contain a-zA-Z0-9_-. character This will ensure security,
In fact, you can write it yourself and use the SecurityUtil.trimSql of the security framework to strictly limit the data, and this thing must be done in the place where sql injection is required. You can do this in some java code. It is also useless and may be hijacked., that is, in mybatis
${@ [email protected](filde)}
That's it.
The solution is much older, but I will introduce it later,
2. What is the locking problem?
Ordinary locks lock the current thread. For the granularity, like jdk, these are the granularity of the current thread, which cannot be refined. If you want to make the granularity smaller, we can use a custom lock to controlA field blocks the current thread and stores the data that needs to be blocked by an intermediate storage tool.And the fields are not the same whether the thread can pass.Then you can create a lock based on your business.
This field can be placed in the middleware or in the database at will.
The principle is the same.And then the specific implementation, I still don't write it for the time being.This article is for the water badge (mainly because there is not so much time for the time being, I will introduce it in detail later in a special article)
边栏推荐
- 多御安全浏览器新版下载 | 功能优秀性能出众
- 将故事写成我们
- There are several common event handling methods in Swing?How to listen for events?
- ffmpeg enumeration decoders, encoders analysis
- How to wrap markdown - md file
- [Paper Notes] MapReduce: Simplified Data Processing on Large Clusters
- public static
List asList(T... a) What is the prototype? - 国学*周易*梅花易数 代码实现效果展示 - 梅花心易
- In the WebView page of the UI automation test App, the processing method when the search bar has no search button
- Web3.0 Dapps——通往未来金融世界的道路
猜你喜欢
35岁的软件测试工程师,月薪不足2W,辞职又怕找不到工作,该何去何从?
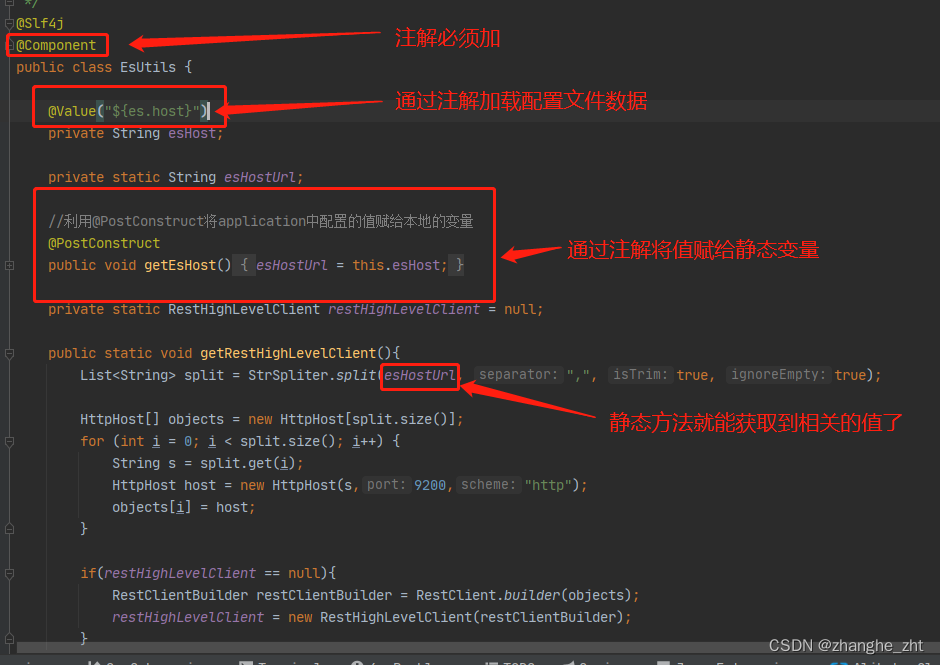
Static method to get configuration file data
![[BSidesCF 2019]Kookie](/img/29/19e7c244feb86b37ab32a53aa11f25.png)
[BSidesCF 2019]Kookie
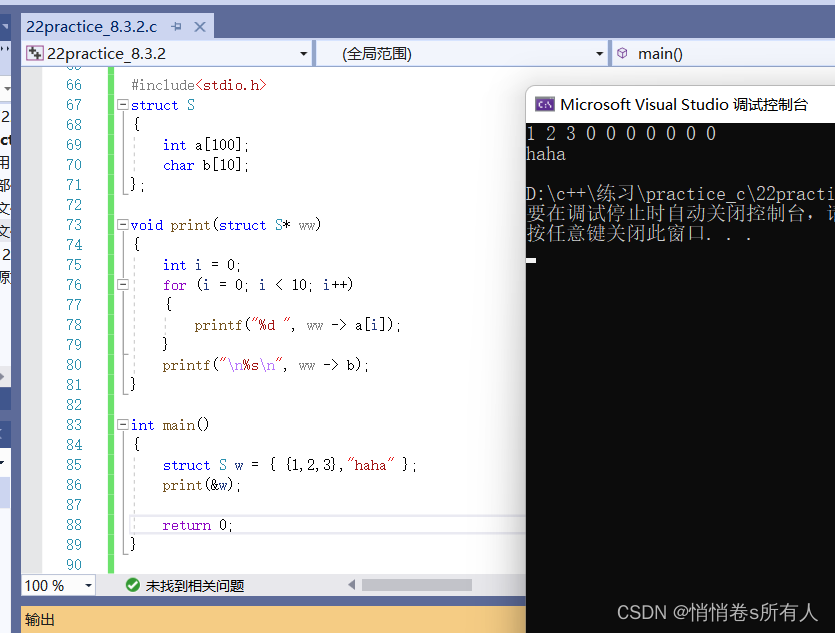
结构体初解
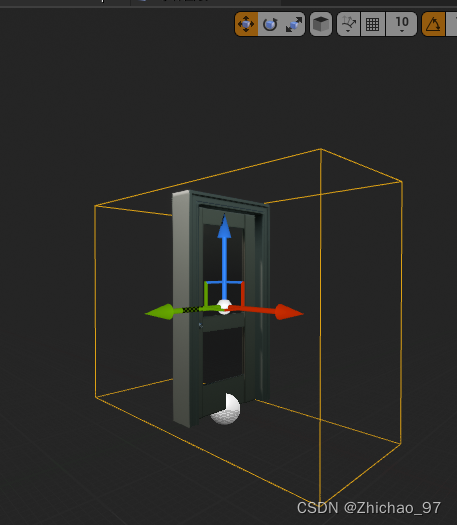
UE4 opens doors with overlapping events
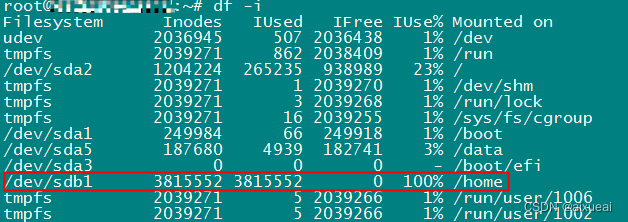
4T硬盘剩余很多提示“No space left on device“磁盘空间不足
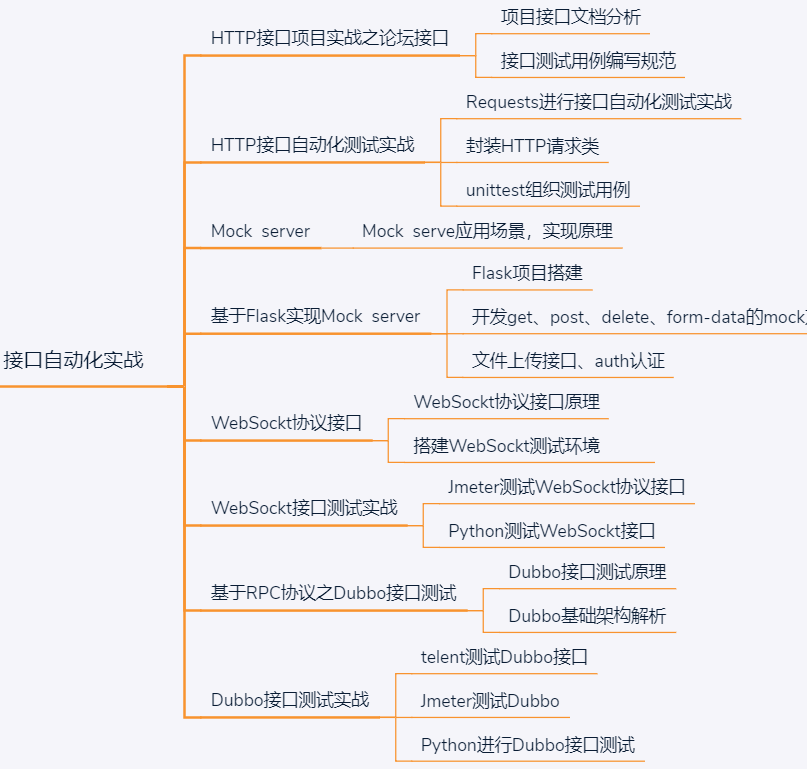
A 35-year-old software testing engineer with a monthly salary of less than 2W, resigns and is afraid of not finding a job, what should he do?
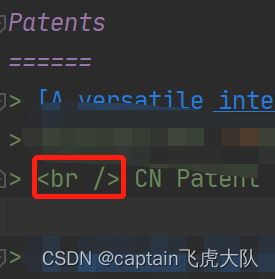
markdown如何换行——md文件
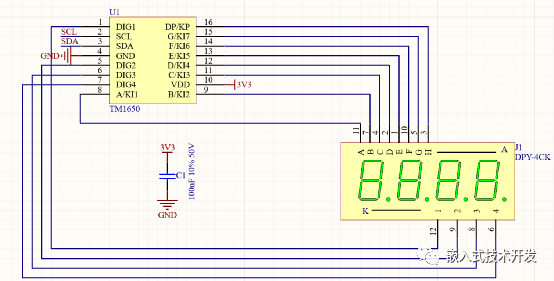
四位数显表头设计
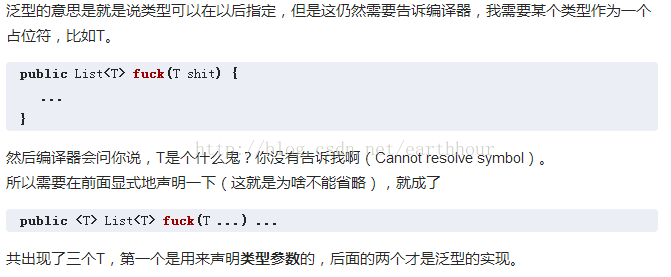
public static
List asList(T... a) What is the prototype?
随机推荐
Mathematics - Properties of Summation Symbols
日志导致线程Block的这些坑,你不得不防
Redis key basic commands
1007 Climb Stairs (greedy | C thinking)
The sword refers to Offer--find the repeated numbers in the array (three solutions)
程序开发的一些常规套路(一)
Ffmpeg - sources analysis
shell脚本:for循环与while循环
重载运算符
Index Mysql in order to optimize paper 02 】 【 10 kinds of circumstances and the principle of failure
新人如何入门和学习软件测试?
What is the function of industrial-grade remote wireless transmission device?
将故事写成我们
iMedicalLIS listener (2)
You may use special comments to disable some warnings. 报错解决的三种方式
队列题目:最近的请求次数
概率论的学习和整理8: 几何分布和超几何分布
There are several common event handling methods in Swing?How to listen for events?
ffmpeg enumeration decoders, encoders analysis
Web3.0 Dapps - the road to the future financial world