当前位置:网站首页>Type of fault
Type of fault
2022-07-05 21:58:00 【Short section senior】
Failure within a transaction
Failure within a transaction
Some can be found through the transaction program itself ( See the example of transfer transaction below )
Some are unexpected , That cannot be handled by a transactional program .
for example , Bank transfer transactions , This transaction transfers an amount from one account a to another account b .
BEGIN TRANSACTION
Read the balance of account a BALANCE;
BALANCE=BALANCE-AMOUNT; /*AMOUNT Is the transfer amount */
IF(BALANCE < 0 ) THEN
{
Print ‘ Insufficient amount , Can't transfer ’;
/* Internal transactions may cause transactions to be rolled back */
ROLLBACK; /* Undo the changes just made , Resume business */
}
ELSE
{
Read the balance of account b BALANCE1;
BALANCE1=BALANCE1+AMOUNT;
Write back to BALANCE1;
COMMIT;}
The two update operations included in this example are either completed or not done at all . Otherwise, the database will be in an inconsistent state , For example, only the balance of account a is reduced, but the balance of account B is not increased .
In this procedure, if the balance of account a is insufficient , The application can discover and roll transactions back , Undo the changes made , Restore the database to the correct state .
More failures within the transaction are unexpected , It can't be handled by an application .
Operation overflow
A concurrent transaction has a deadlock and is selected to undo the transaction
Termination for violation of certain integrity restrictions, etc
in the future , Transaction failure only refers to this kind of unexpected failure
Transaction failure means
The transaction did not reach the expected end point (COMMIT Or explicitly ROLLBACK)
The database may be in an incorrect state .
Recovery of transaction failure : Transaction undo (UNDO)
Force rollback (ROLLBACK) This transaction
Undo any changes made to the database by the transaction , Make the transaction seem to have not started at all
System failure
System failure
It's called soft fault , It refers to any event that causes the system to stop working , bring
The system needs to restart .
The normal operation of the whole system was suddenly destroyed
All running transactions terminate abnormally
Do not destroy the database
All information in the database buffer in memory is lost
Common causes of system failures
Specific types of hardware errors ( Such as CPU fault )
Operating system failure
Database management system code error
System power failure
Recovery of system failure
In the event of a system failure , The results of some unfinished transactions may have been sent to the physical database , This may cause the database to be in an incorrect state .
Recovery strategy : When the system restarts , The recovery program rolls back all abnormally terminated transactions , Forcibly withdraw (UNDO) All outstanding transactions
In the event of a system failure , Some completed transactions may be partially or even completely left in the buffer , Not yet written back to the physical database on disk , The system failure makes some or all of the modifications of these transactions to the database lost
Recovery strategy : When the system restarts , The recovery program needs to be redone (REDO) All committed transactions
Media failure
Media failure
It's called hard fault , Refers to external memory failure
Disk damage
Head collision
Instantaneous strong magnetic field interference
Media failure destroys the database or part of the database , And affect all transactions that are accessing this data
Medium failure is much less likely than the first two types of failure , But it's much more destructive
Computer virus
Computer virus
An artificial failure or destruction , It's a computer program developed by some pranksters
It can reproduce and spread , Cause harm to computer system, including database
Types of computer viruses
The only small viruses are 20 Orders , Less than 50B
A large virus is like an operating system , It consists of tens of thousands of instructions
The harm of computer virus
Some viruses spread quickly , Once you invade the system, destroy the system immediately
Some viruses have a long incubation period , Computers don't start to get sick until a few days or months after infection
Some viruses infect all the programs and data of the system
Some are only interested in certain specific programs and data
Computer viruses have become a major threat to computer systems , Naturally, it is also the main threat to the database system
Once the database is damaged, we still need to use recovery technology to recover the database
Breakdown summary
Various faults , There are two possibilities for the impact on the database
One is that the database itself is destroyed
Second, the database has not been damaged , But the data may not be correct , This is caused by the abnormal termination of the transaction .
recovery
Basic principles of recovery operation : redundancy
Use the redundant data stored elsewhere in the system to reconstruct the damaged or incorrect part of the data in the database
Recovery implementation technology : complex
A large database product , The code of the recovery subsystem accounts for 10% above
Welcome to join me for wechat exchange and discussion ( Please note csdn Add )
边栏推荐
- Interview questions for basic software testing
- Evolution of large website architecture and knowledge system
- kingbaseES V8R3数据安全案例之---审计记录清除案例
- GCC9.5离线安装
- Defect detection - Halcon surface scratch detection
- EBS Oracle 11g 克隆步骤(单节点)
- Robot framework setting variables
- Installation of VMware Workstation
- HDU 4391 Paint The Wall 段树(水
- poj 3237 Tree(树链拆分)
猜你喜欢
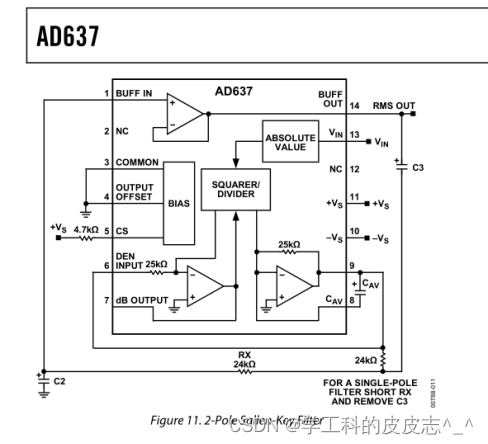
AD637使用筆記
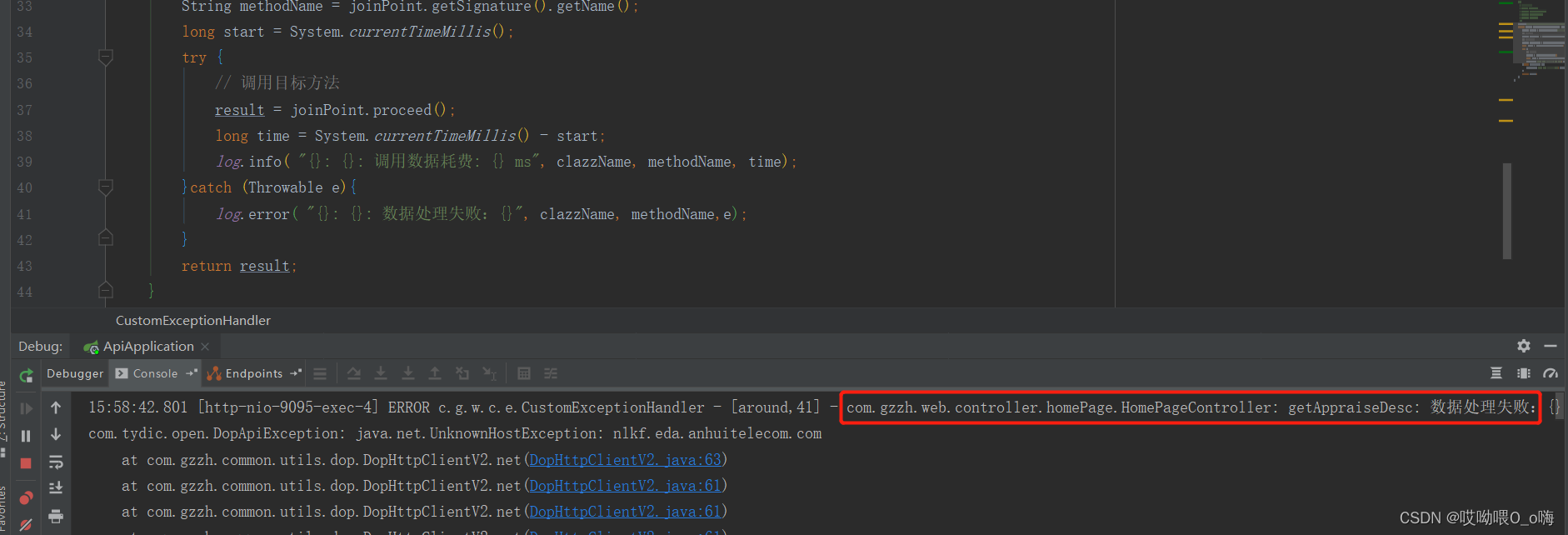
使用Aspect制作全局异常处理类
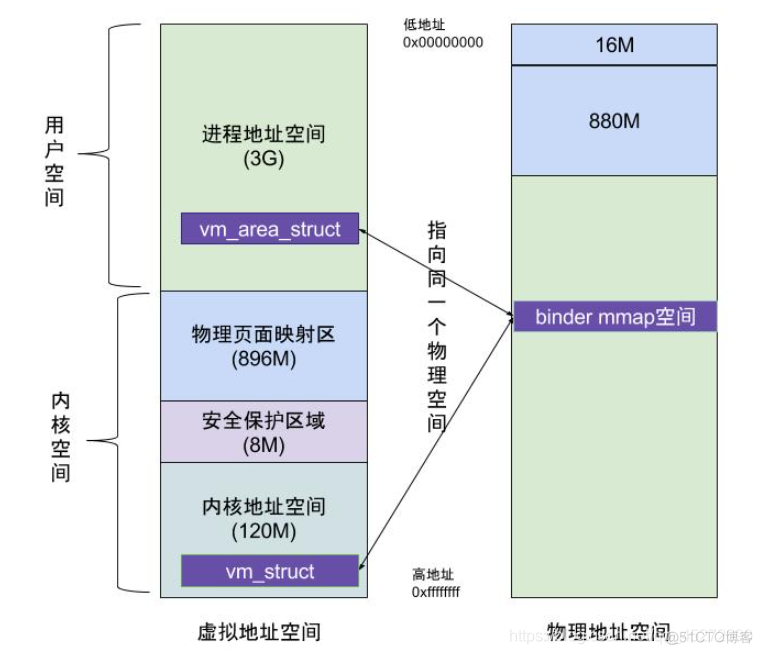
MMAP学习
阿里云有奖体验:用PolarDB-X搭建一个高可用系统
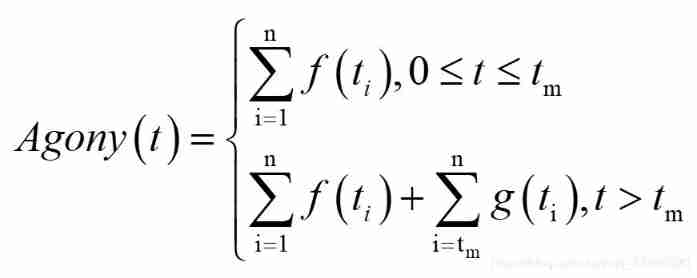
Cold violence -- another perspective of objective function setting
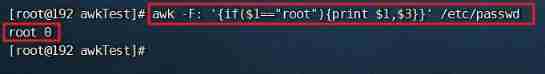
Shell script, awk uses if, for process control
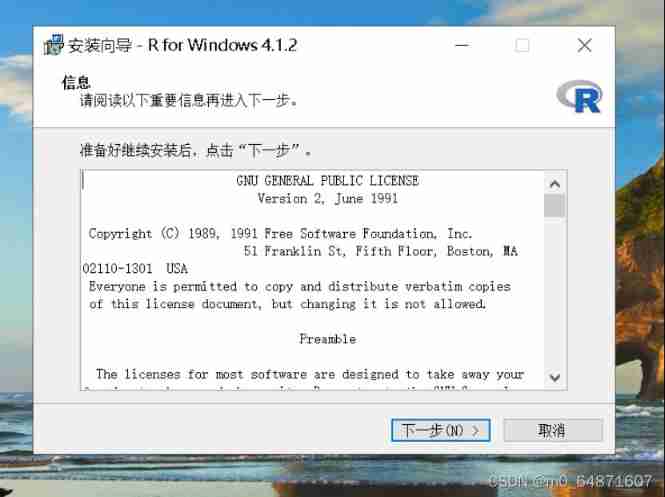
R language learning notes

Parker driver maintenance COMPAX controller maintenance cpx0200h
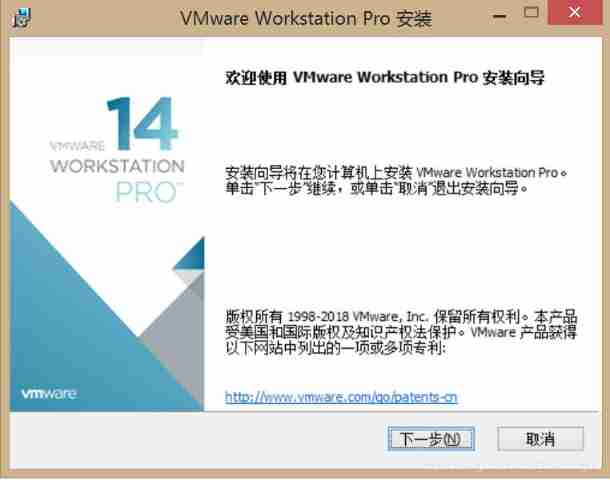
Installation of VMware Workstation
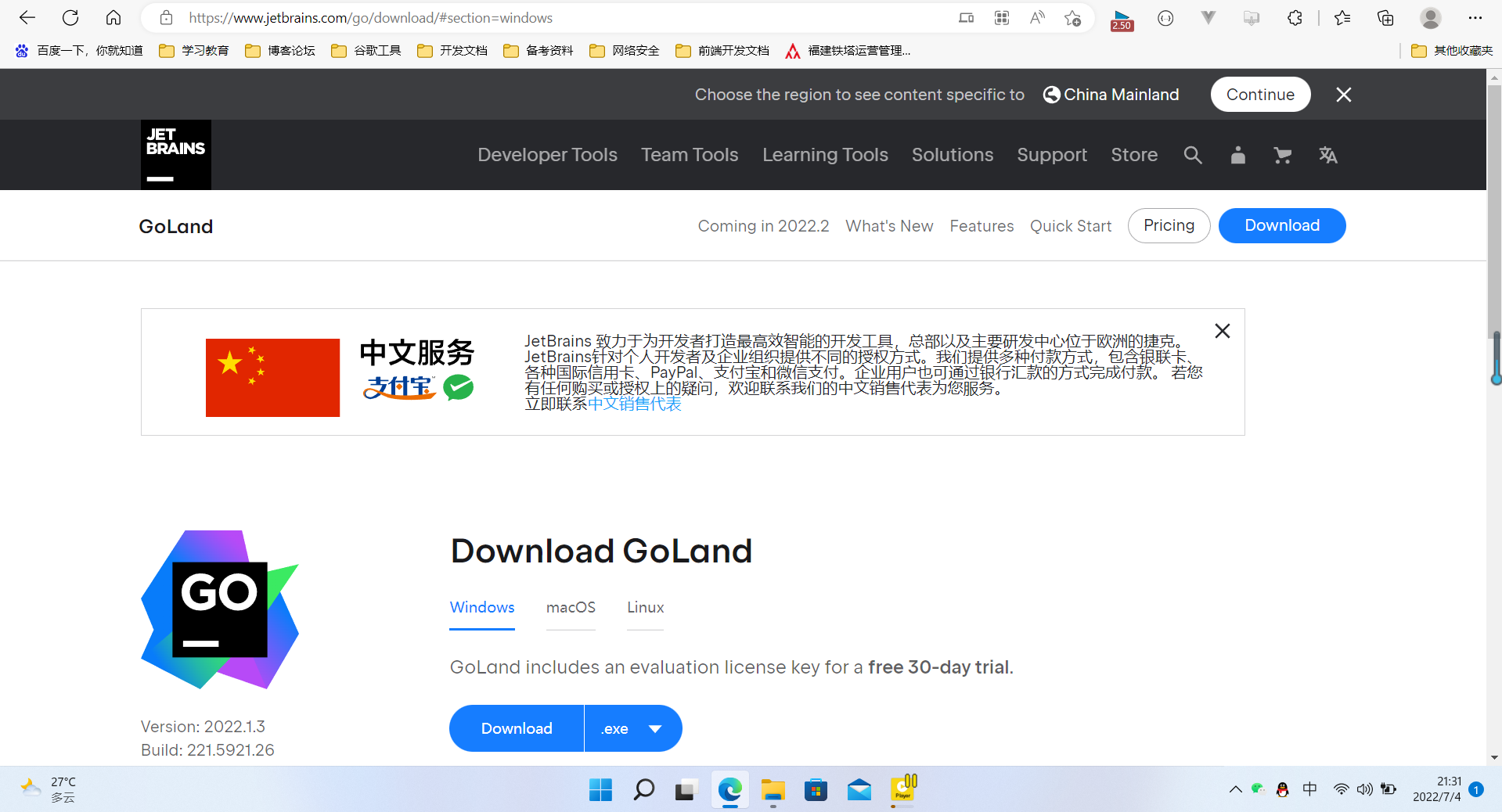
【愚公系列】2022年7月 Go教学课程 003-IDE的安装和基本使用
随机推荐
The primary key is set after the table is created, but auto increment is not set
2.2 basic grammar of R language
Cold violence -- another perspective of objective function setting
阿龙的感悟
PyGame practical project: write Snake games with 300 lines of code
总结出现2xx、3xx、4xx、5xx状态码的原因
Codeforces 12D ball tree array simulation 3 sorting elements
Kingbasees v8r3 data security case - audit record clearing case
深信服X计划-网络协议基础 DNS
多家呼吸机巨头产品近期被一级召回 呼吸机市场仍在增量竞争
Problems encountered in office--
Objects in the list, sorted by a field
Parker driver maintenance COMPAX controller maintenance cpx0200h
Create a virtual machine on VMware (system not installed)
Kingbasees v8r3 cluster maintenance case -- online addition of standby database management node
Deeply convinced plan X - network protocol basic DNS
Zhang Lijun: penetrating uncertainty depends on four "invariants"
Shell script, awk condition judgment and logic comparison &||
Multiplexing of Oracle control files
Some common processing problems of structural equation model Amos software