当前位置:网站首页>SQL injection - secondary injection and multi statement injection
SQL injection - secondary injection and multi statement injection
2022-07-07 05:05:00 【In a word, the Trojan horse (the growth road of Wang an Xiaobai)】
The secondary injection
One 、 Definition of secondary injection
Simply put, secondary injection is the user input that has been stored in the database , Go in when reading again SQL Injection in query statement .
Two 、 The principle of secondary injection
First step : Insert malicious data
When inserting data into the database for the first time , Only special characters are escaped , When writing to the database, the original data is retained , But the data itself contains malicious content .
The second step : Reference malicious data
After saving into the database , Developers believe that the data is credible , The next time you need to query , Propose malicious data directly from the database , No further inspection and treatment , Will cause sql Secondary injection data of
3、 ... and 、 Demonstration of the principle of secondary injection
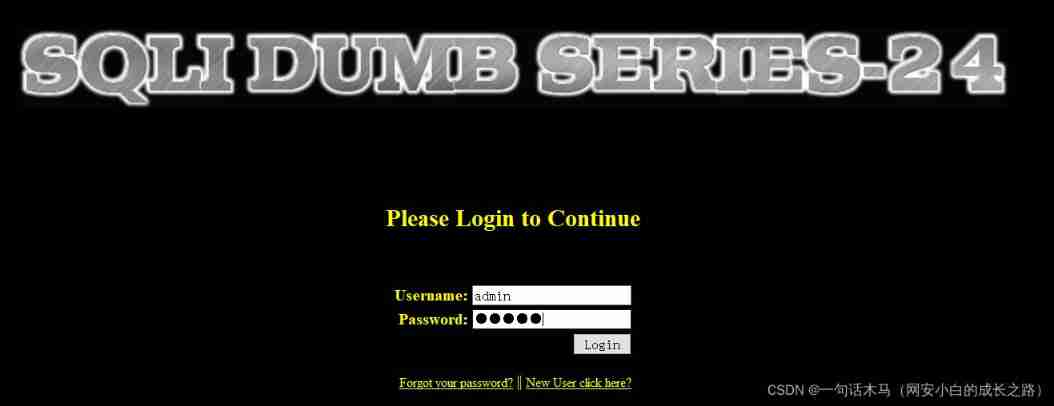
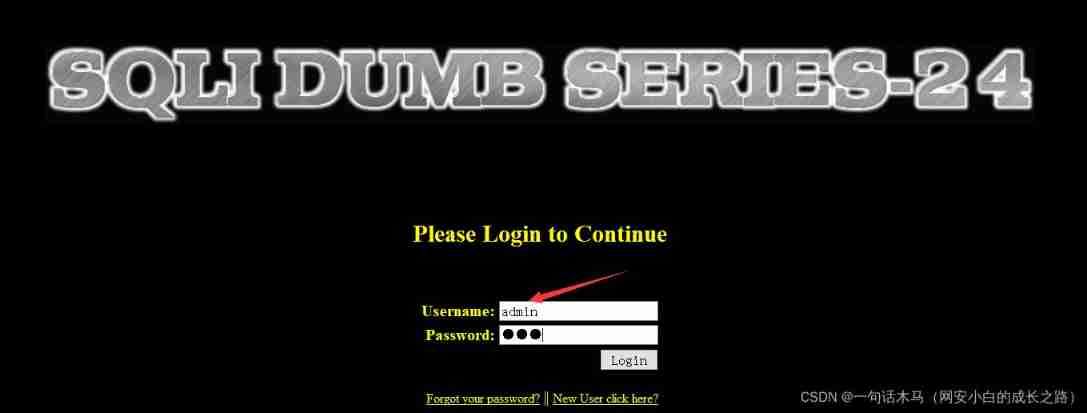
1. open http://localhost/sqlilabs/Less-24/ , Is a user login page , Input admin;admin Log in
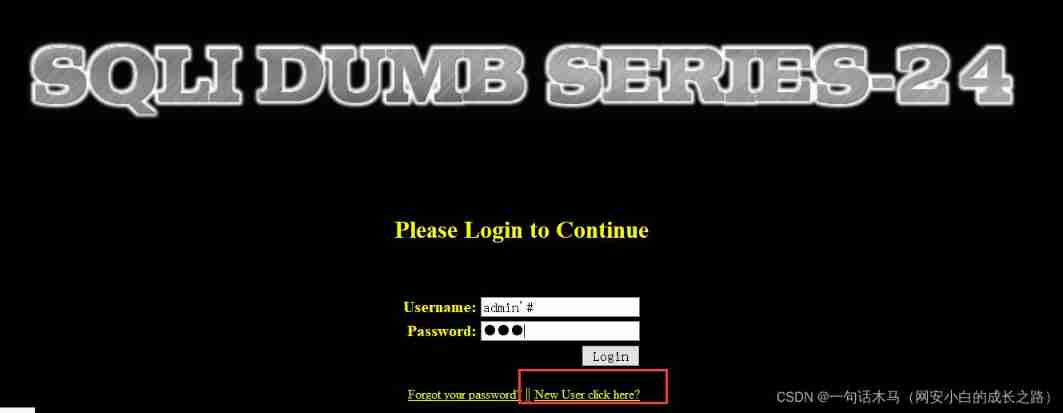
2. First, we click to register a new user
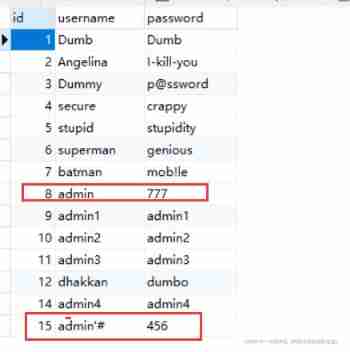
username:admin'# password:456
3. Change the password of the current user again Change it to :777
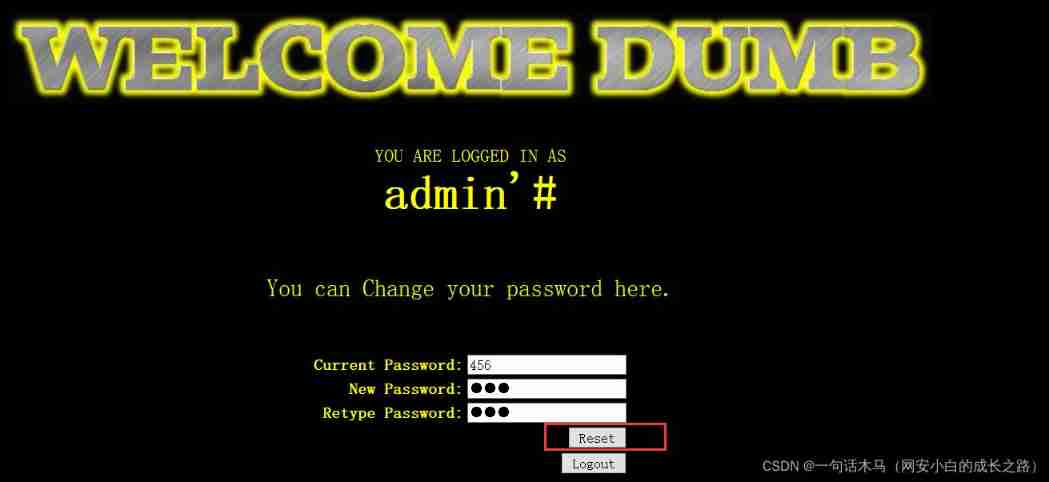
4. Return to the main page to log in admin account number , Use the original password :admin , Found an error
5. In the login admin account number , Use the one just changed admin'# Password :777, Found successful login

6. stay Navicat View database table in
Multi statement injection
One 、 Prerequisites for multi statement injection
Source code usage mysqli_multi_query(); Multi statement query function , You can execute multiple at a time sql sentence , But in reality , Such as PHP In order to prevent SQL Mechanism , The functions that are often used to call the database are mysqli_ query() function , It can only execute one statement , What follows the semicolon will not be executed , Therefore, it can be said that the use conditions of stack injection are very limited , Once it can be used , It may pose a great threat to the website .
边栏推荐
猜你喜欢
If you‘re running pod install manually, make sure flutter pub get is executed first.

Monitoring cannot be started after Oracle modifies the computer name
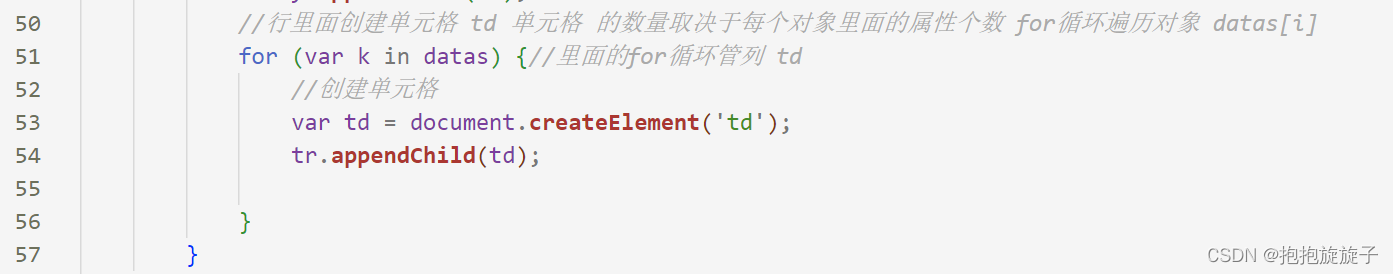
动态生成表格
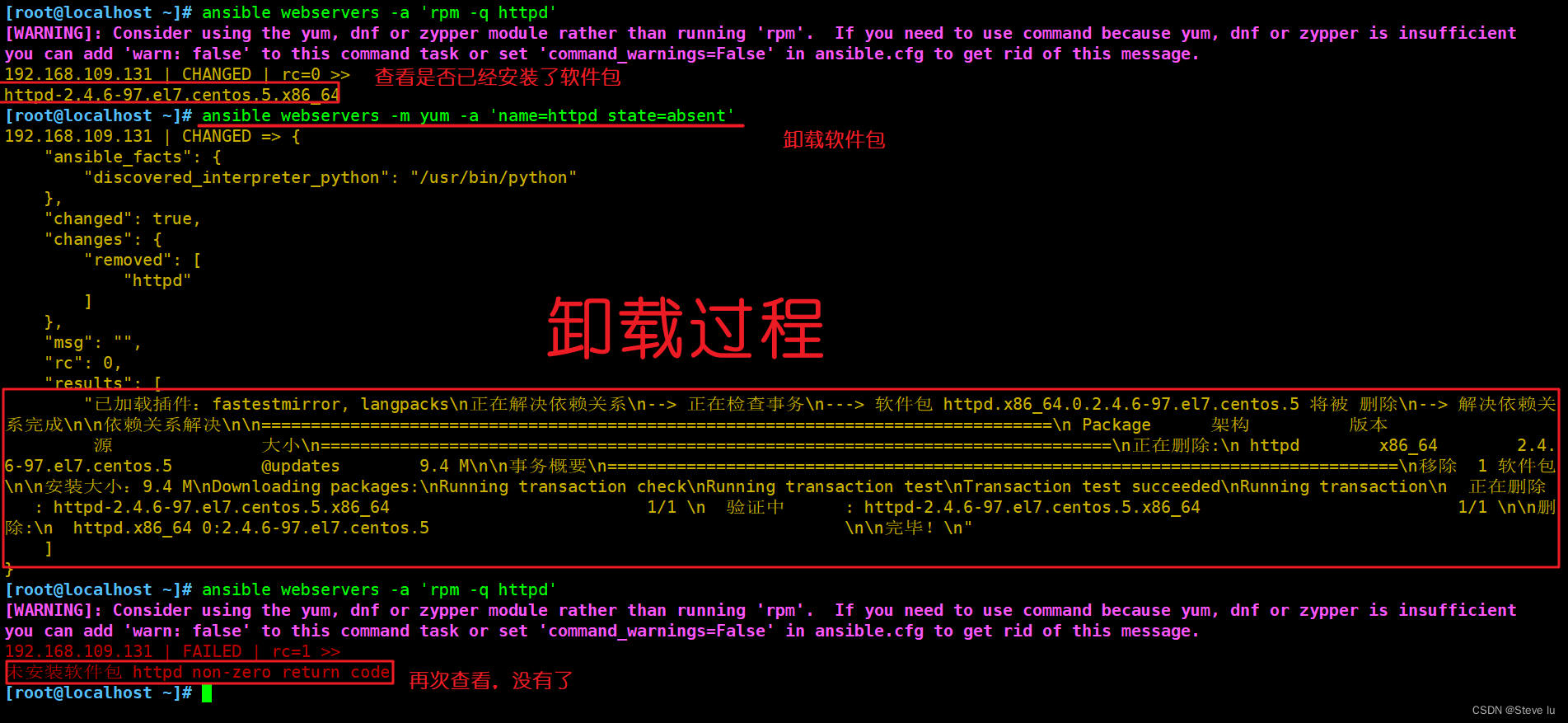
Ansible概述和模块解释(你刚走过了今天,而扑面而来的却是昨天)
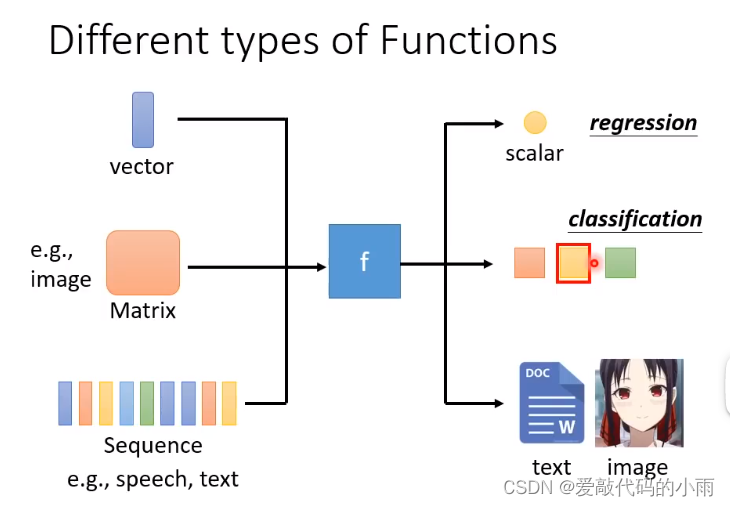
01机器学习相关规定
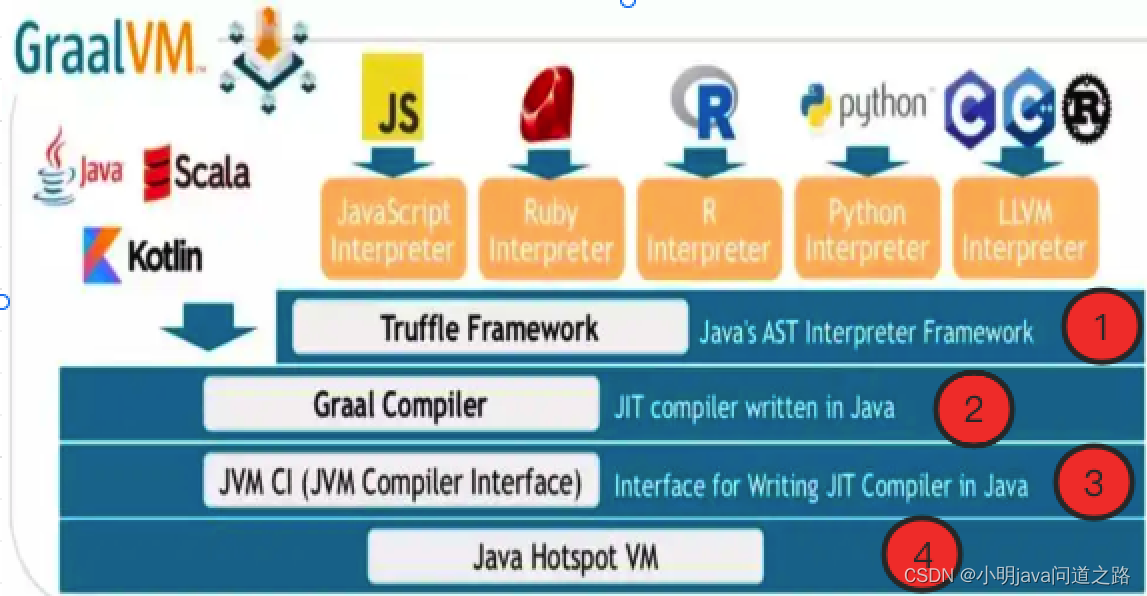
【问道】编译原理

为什么很多人对技术债务产生误解
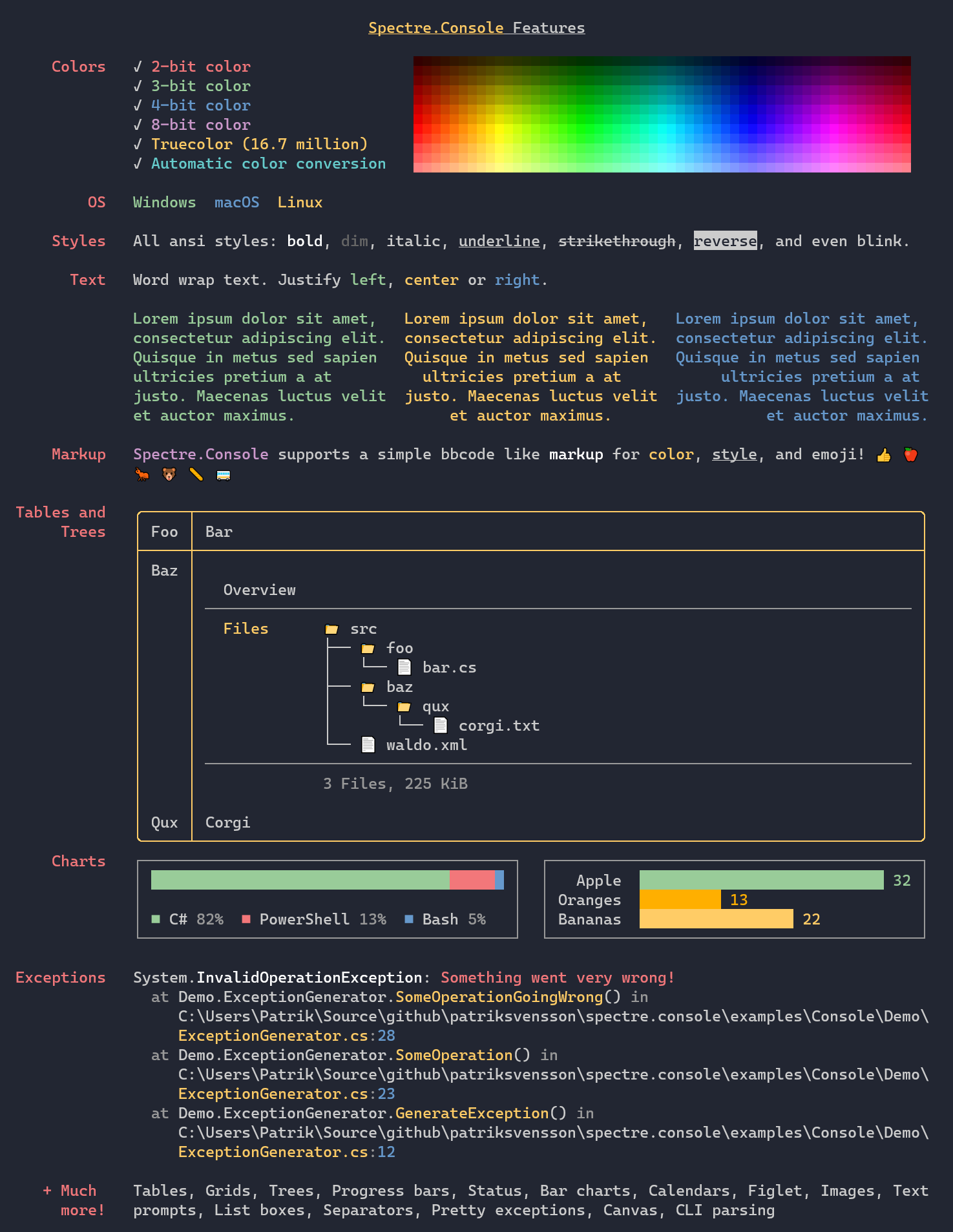
一个酷酷的“幽灵”控制台工具
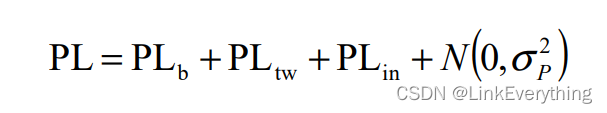
Basic knowledge of road loss of 3GPP channel model

How to choose an offer and what factors should be considered
随机推荐
第一篇论文的写作流程
当 Knative 遇见 WebAssembly
Analyse approfondie de kubebuilder
拿到PMP认证带来什么改变?
vector和类拷贝构造函数
Tree map: tree view - draw covid-19 array diagram
AttributeError: module ‘torch._C‘ has no attribute ‘_cuda_setDevice‘
JS variable case
U++4 interface learning notes
JS variable plus
Talk about the importance of making it clear
npm ERR! 400 Bad Request - PUT xxx - “devDependencies“ dep “xx“ is not a valid dependency name
Addressable 预下载
Analysis -- MySQL statement execution process & MySQL architecture
JS variable
Field data acquisition and edge calculation scheme of CNC machine tools
Redis如何实现多可用区?
ThinkPHP关联预载入with
CentOS 7.9安装Oracle 21c历险记
[hand torn STL] list