当前位置:网站首页>Misc (eternal night), the preliminary competition of the innovation practice competition of the National College Students' information security competition
Misc (eternal night), the preliminary competition of the innovation practice competition of the National College Students' information security competition
2022-07-06 02:41:00 【Like to drink Wangzai's Wangwang】
The tense final is finally over , I just have time to sum up one of the competitions some time ago misc subject , Layers of dolls are very interesting .
Title Attachment :
link :https://pan.baidu.com/s/1lZ6YCyyY3hdMx2_ymLlsyA
Extraction code :viy2
-- From Baidu network disk super member V1 The share of
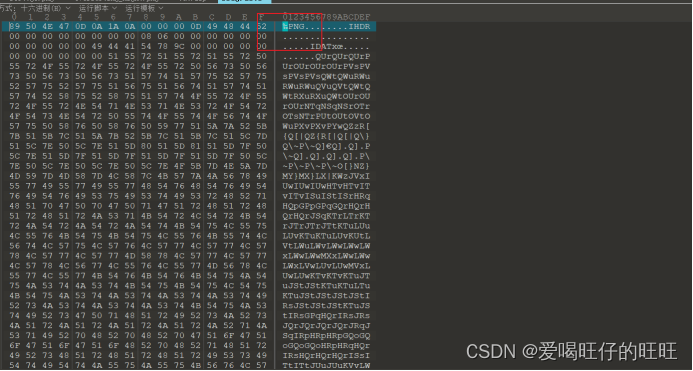
Get the picture , The old rules use 010 Open file :
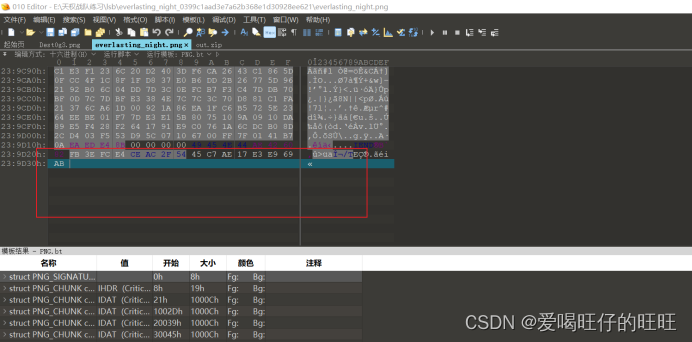
A string of abnormal data is found at the end of the file
Question prompt this question is lsb Steganography
Use the tool to analyze the color trace of the picture
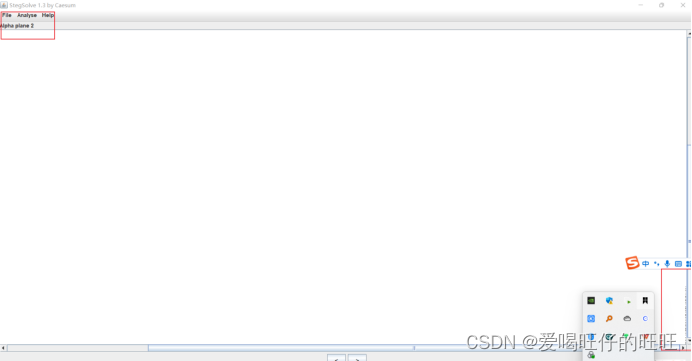
In this color channel, I found a string of things similar to moss code
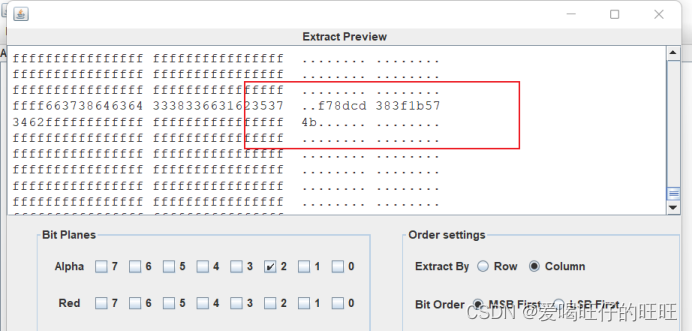
Analyze the file corresponding to the color track and find this string of ciphertext
 The title also suggests a little use password Of lsb Steganography , Associated with the github Last project cloacked-pixel
The title also suggests a little use password Of lsb Steganography , Associated with the github Last project cloacked-pixel
Project address :GitHub - livz/cloacked-pixel: LSB steganography and detection
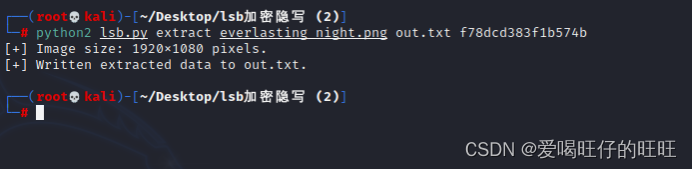
utilize a2 The information in the channel is read out, and the hidden information is output as a txt file
open txt file
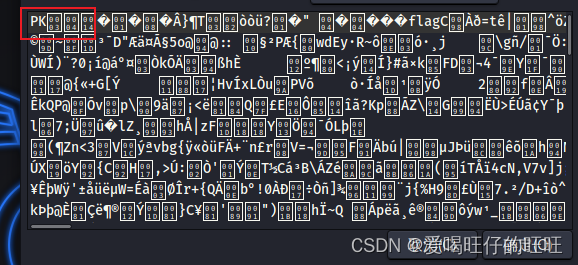
pk The file header Obviously compressed package Change the suffix of the file to zip Prompt for password
At this time, we think of the last string of data in the picture at the beginning Try various decryption methods Last use md5 figure out

Get the final decompression password
decompression Get a picture
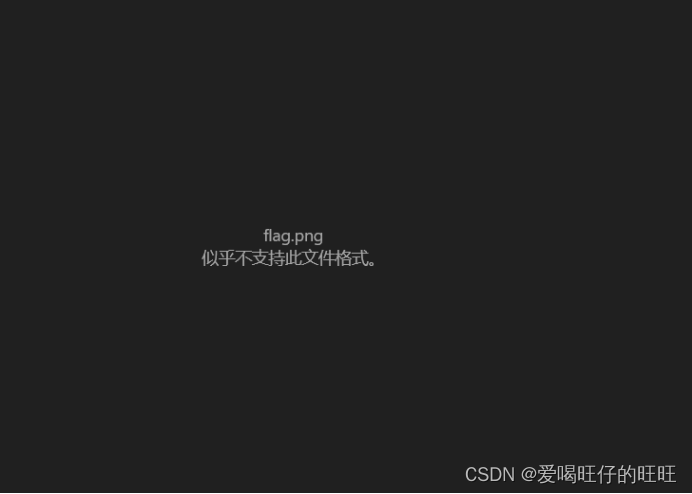
Unable to open The prompt file is corrupt
The conventional thinking here is based on crc Explode the correct width and height of the picture , Let the picture parse normally . Here is a more ingenious way
Change the picture name to flag.data Reuse gimp Open the picture Adjust the width to get the final flag

边栏推荐
- 球面透镜与柱面透镜
- A copy can also produce flowers
- Shell script updates stored procedure to database
- Which ecology is better, such as Mi family, graffiti, hilink, zhiting, etc? Analysis of five mainstream smart brands
- Introduction to robotframework (III) Baidu search of webui automation
- Large scale DDoS attacks take Myanmar offline
- After changing the GCC version, make[1] appears in the compilation: cc: command not found
- PMP practice once a day | don't get lost in the exam -7.5
- How to check the lock information in gbase 8C database?
- Redis skip table
猜你喜欢
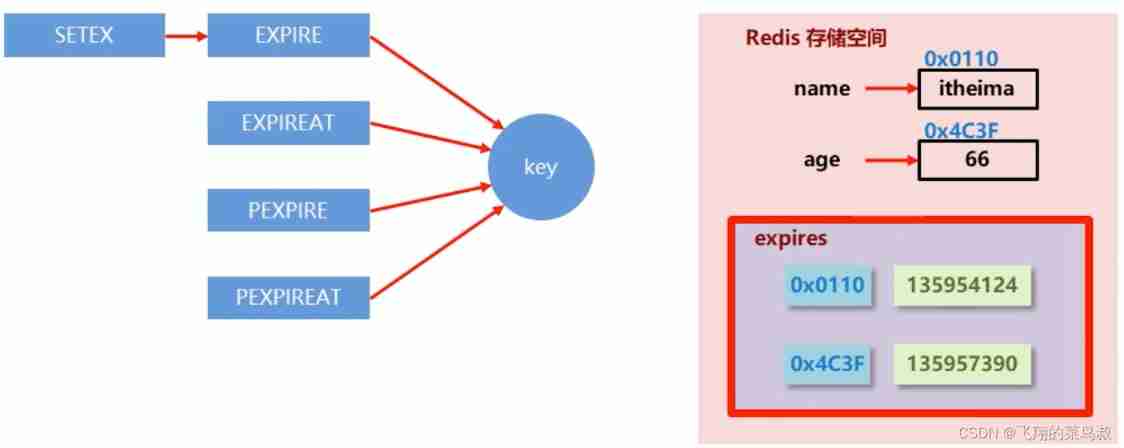
Redis delete policy
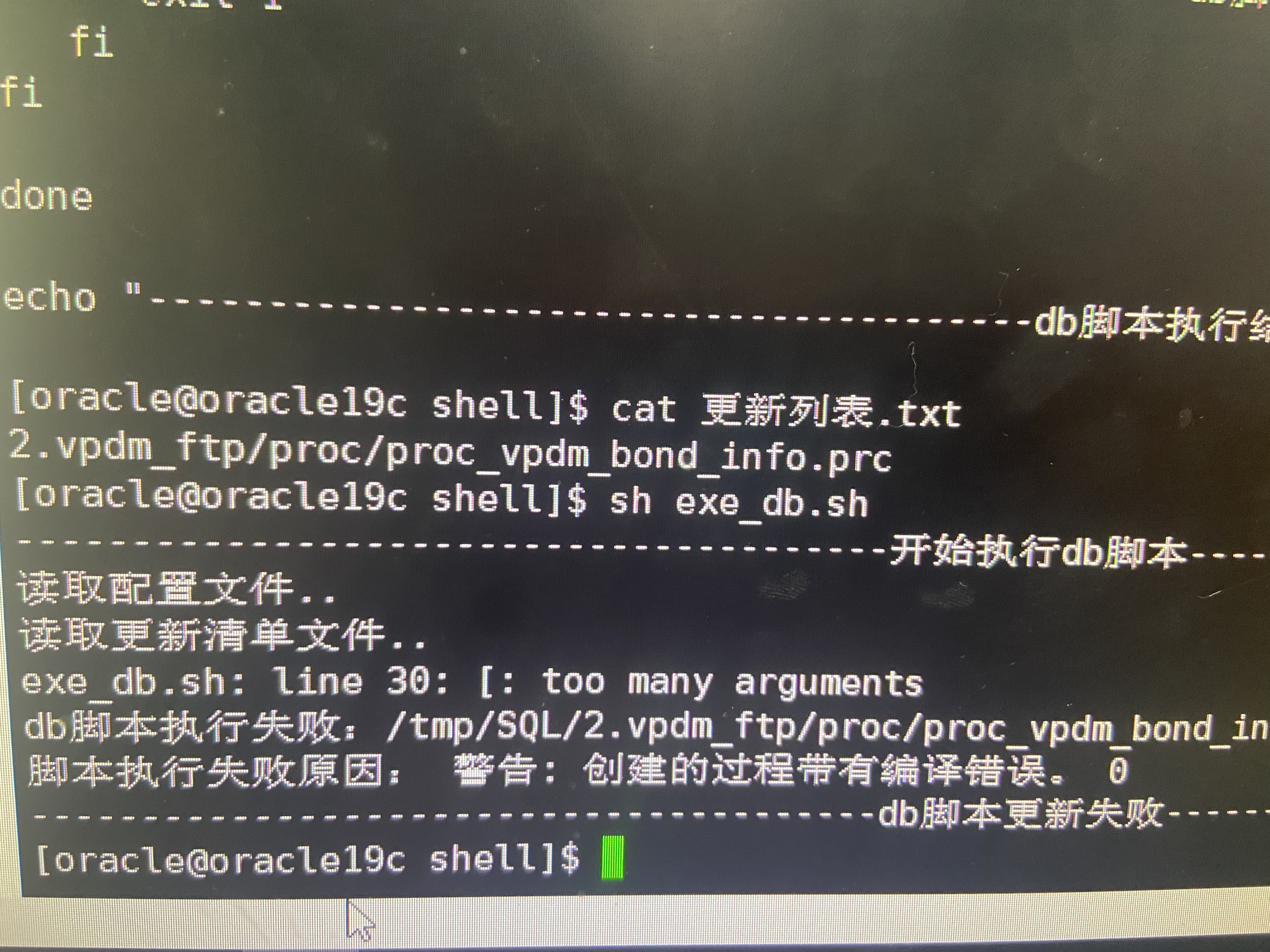
Shell script updates stored procedure to database
![[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 12](/img/b1/926d9b3d7ce9c5104f3e81974eef07.jpg)
[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 12
![[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 9](/img/ed/0edff23fbd3880bc6c9dabd31755ac.jpg)
[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 9
![[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 19](/img/7c/f728e88ca36524f92c56213370399b.jpg)
[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 19

2022.02.13
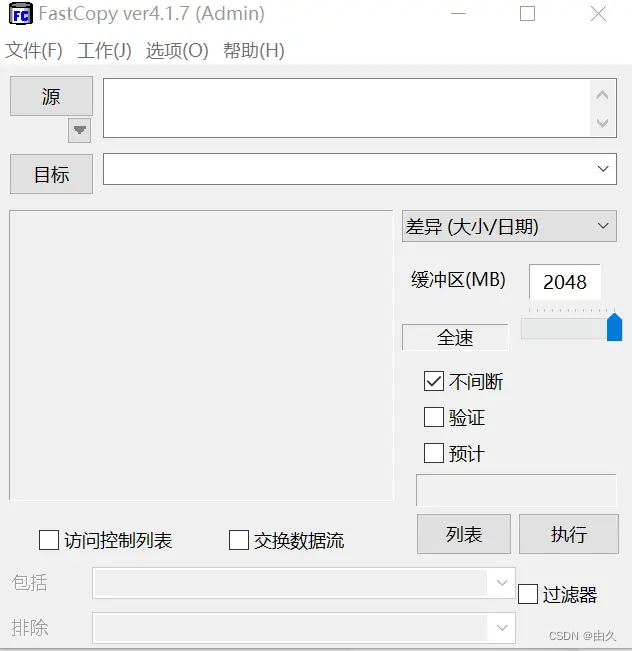
一个复制也能玩出花来

如何精准识别主数据?
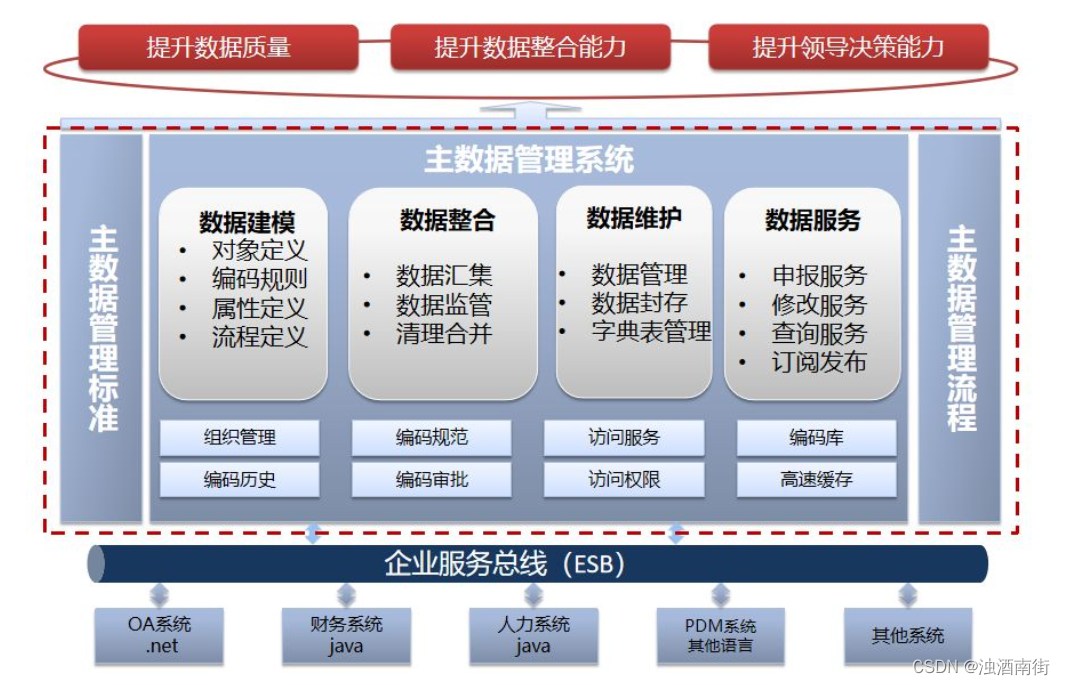
Master data management theory and Practice
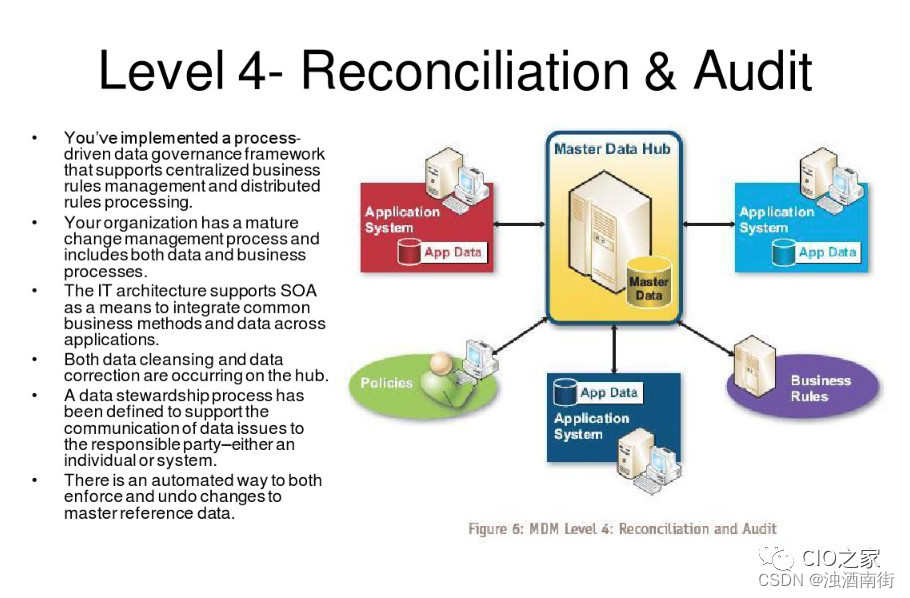
Maturity of master data management (MDM)
随机推荐
2020.02.11
Qt发布exe软件及修改exe应用程序图标
球面透镜与柱面透镜
[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 24
A doctor's 22 years in Huawei
主数据管理理论与实践
MySQL winter vacation self-study 2022 11 (7)
全国大学生信息安全赛创新实践赛初赛---misc(永恒的夜)
Network Security Learning - Web vulnerabilities (Part 1)
Deeply analyze the chain 2+1 mode, and subvert the traditional thinking of selling goods?
技术分享 | undo 太大了怎么办
[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 14
Pure QT version of Chinese chess: realize two-man, man-machine and network games
3D drawing ()
"Hands on learning in depth" Chapter 2 - preparatory knowledge_ 2.5 automatic differentiation_ Learning thinking and exercise answers
Data preparation
力扣今日題-729. 我的日程安排錶 I
DDoS attacks - are we really at war?
Zero basic self-study STM32 wildfire review of GPIO use absolute address to operate GPIO
Zero foundation self-study STM32 - Review 2 - encapsulating GPIO registers with structures