当前位置:网站首页>SCP -i private key usage
SCP -i private key usage
2022-07-01 17:57:00 【inrese】
scp -i xxx.pem xxx.zip [email protected]:/home/ubuntu/
边栏推荐
- Quick foundation of group theory (5): generators, Kelley graphs, orbits, cyclic graphs, and "dimensions" of groups?
- About selenium element positioning being overwritten
- js如何将带有分割符的字符串转化成一个n维数组
- Gold, silver and four job hopping, interview questions are prepared, and Ali becomes the champion
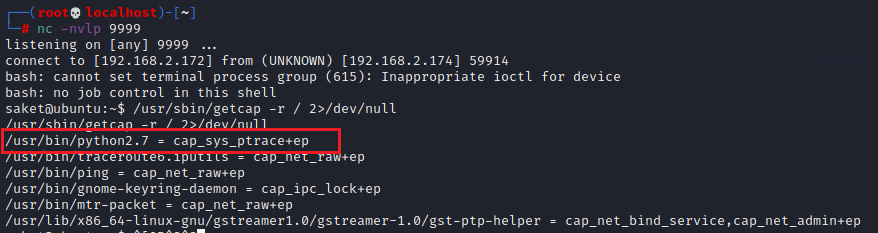
- Penetration practice vulnhub range Nemesis
- Software construction scheme of smart factory collaborative management and control application system
- Is it safe to open a stock account by mobile phone? What do you need to bring with you to open an account?
- Kia recalls some K3 new energy with potential safety hazards
- Penetration practice vulnhub range Keyring
- Yuancosmos game farmersworld farmers world - core content of the second conference in China!
猜你喜欢

Gold, silver and four job hopping, interview questions are prepared, and Ali becomes the champion
![[PHP foundation] realize the connection between PHP and SQL database](/img/eb/c8953eddfe3b19b0adb5529957d275.jpg)
[PHP foundation] realize the connection between PHP and SQL database

From comedians to NBA Zhan Huang, check the encrypted advertisements during this super bowl

An example of data analysis of an old swatch and an old hard disk disassembly and assembly combined with the sensor of an electromagnetic press

Wechat applet blind box - docking wechat payment

Euler function: find the number of numbers less than or equal to N and coprime with n

New patent applications and transfers
Vulnhub range hacker_ Kid-v1.0.1

Leetcode 1380. Lucky numbers in the matrix (save the minimum number of each row and the maximum number of each column)
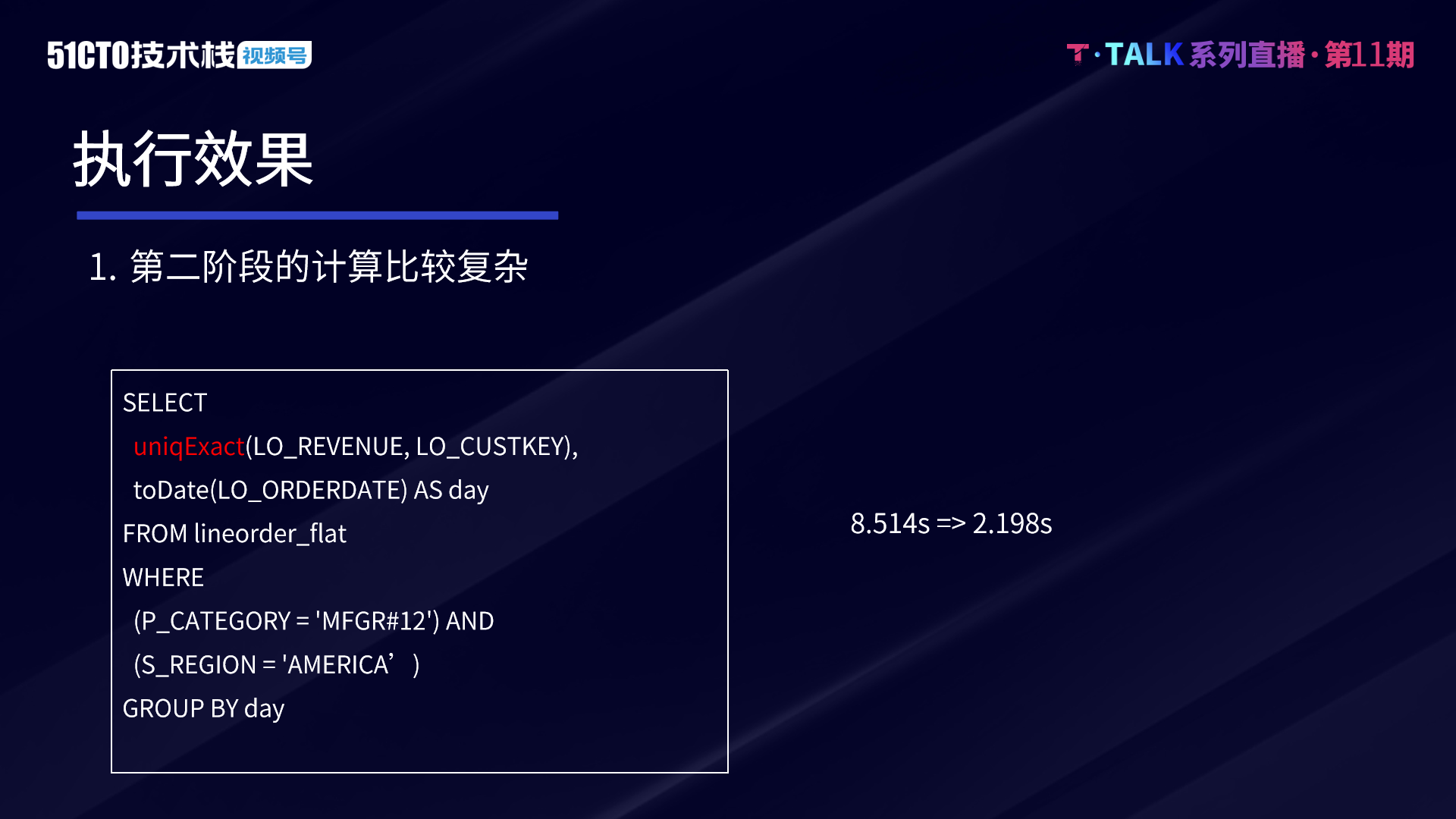
Technical secrets of ByteDance data platform: implementation and optimization of complex query based on Clickhouse
随机推荐
Development cost of smart factory management system software platform
Cassette helicopter and alternating electric field magnetic manometer DPC
. Net cloud native architect training camp (permission system code implements actionaccess) -- learning notes
What are the six steps of the software development process? How to draw software development flow chart?
Data warehouse (3) star model and dimension modeling of data warehouse modeling
[beauty detection artifact] come on, please show your unique skill (is this beauty worthy of the audience?)
Key points on February 15, 2022
[2. Basics of Delphi grammar] 4 Object Pascal operators and expressions
Unity3d extended toolbar
EasyCVR通过国标GB28181协议接入设备,出现设备自动拉流是什么原因?
Three dimensional anti-terrorism Simulation Drill deduction training system software
ArrayList扩容详解
In depth Research Report on China's disposable sanitary products production equipment industry (2022 Edition)
Blackwich: the roadmap of decarbonization is the first step to realize the equitable energy transformation in Asia
js如何将带有分割符的字符串转化成一个n维数组
MES production equipment manufacturing execution system software
Apache iceberg source code analysis: schema evolution
Petrv2: a unified framework for 3D perception of multi camera images
Is it safe to open an ETF account online? What are the steps?
Is online stock account opening safe? Is it reliable?