当前位置:网站首页>Significance and measures of source code confidentiality
Significance and measures of source code confidentiality
2022-07-07 03:15:00 【Cnsidna. No.1】
Why keep source code confidential
Various embedded R & D and platform software R & D industries , Each has its own core data and core documents , User data and other sensitive information , These information data have the following commonalities :
It belongs to the core confidential information , In case of leakage, it will have a bad impact on
There are many types of core data , Source code data , Employees have high computer skills
A lot of data is in the business system , It's not a document
If you don't control , Designers and users can easily copy the data through various ways , Cause leakage .
Common secret related ways for R & D personnel
Because R & D personnel are more proficient in computers than ordinary office personnel , In addition to the common network , mail ,U disc ,QQ And other data diffusion methods , There are many other methods that are very easy for developers ( Not listed completely ):
Physical method :
Network cable direct connection , Unplug the network cable from the wall , Then connect directly to an uncontrolled computer ;
winPE start-up , Via CD or U Discoid winPE start-up , Even directly ISO The image starts .
virtual machine , Through installation VMWare virtual machine , Use peripherals in the virtual machine U disc , The Internet .
Other uncontrolled computers , That is, copy the data to other uncontrolled computers in the network , transit
Upload online , By building an upload server on the public network , Bypass Internet Behavior Management
Data distortion :
Write a console program , Print the code to DOS On the console, and then save the screen information as ;
Write the code to Log Log file , Or write code to shared memory , Then another program reads away .
Write interprocess communication program , Pass the code through socket, news ,LPC,COM,mutex, Shear plate , Pipeline and other interprocess communication methods , Transfer to send the data ;
adopt IIS/Tomcat etc. web The parser transfers , Publish the code data as a web page , Then browse the browser and save as , Or just write txt box , Copy all the code during initialization ;
Peripheral transfer
For embedded development scenarios , You can use the serial port ,U mouth , The network port burns the code to the equipment and leaks the secret
SDC Sandbox anti disclosure software
Developed by shenxinda SDC Sandbox leak proof products , Adopt kernel defense in depth , It is a driver level anti disclosure Software . Do not encrypt files , A sandbox is like a container , The container contains our confidential information . The documents we work on are all in sandboxes . The sandbox is completely isolated from ordinary computers . You might ask , What if I want to access the Internet , All programs to access the Internet are launched from the tray , Such as browser , Chat software, etc .SDC The sandbox is divided into the following parts : The management end , Confidential end , Documents are sent out , client .
The management end : Sandbox Control Center , Control all clients . The control of the client covers all aspects . Let me give you a few control functions : Reverse screenshot When someone wants to view some confidential information of the company remotely to the employee's computer ,SDC The client will control the remote software , Remote people see a black screen . But the computers on the staff side are in normal use . If you can control, you can let go . clipboard In sandbox mode, employees want to copy and paste company data such as files to the Internet through the clipboard ,SDC Sandbox is controlled , You can control the maximum number of clipping words .
Confidential end : Escort the server , Ordinary computers do not have access to confidential servers . Only sandbox computers can access , Do not encrypt the company's data , Protect data to the greatest extent .
client : Normal mode and sandbox mode . All software installation should be in sandbox mode . Work must be in sandbox mode , Because all the working data are on the encrypted disk , Sandbox can only be accessed in encrypted mode . In sandbox mode, it is isolated from the outside world . To access the Internet, only programs launched from the tray can , And follow the principle of only getting in and not getting out , Can get files from the Internet to the sandbox computer , However, to send documents from this machine to the Internet, you have to go through document approval .
Documents are sent out : A file distribution system is installed on a computer . The of this computer ip That is, the address where the document is sent out . Each sandbox employee matches an account number for sending out files . The specific approval method is not cumbersome here .

边栏推荐
- 美国空军研究实验室《探索深度学习系统的脆弱性和稳健性》2022年最新85页技术报告
- Jerry's transmitter crashed after the receiver shut down [chapter]
- How to find file accessed / created just feed minutes ago
- 应用程序启动速度的优化
- Es6中Promise的使用
- The solution of unable to create servlet file after idea restart
- SQL Tuning Advisor一个错误ORA-00600: internal error code, arguments: [kesqsMakeBindValue:obj]
- Analysis of USB network card sending and receiving data
- How does C language (string) delete a specified character in a string?
- Redis Getting started tutoriel complet: positionnement et optimisation des problèmes
猜你喜欢
centerX: 用中国特色社会主义的方式打开centernet
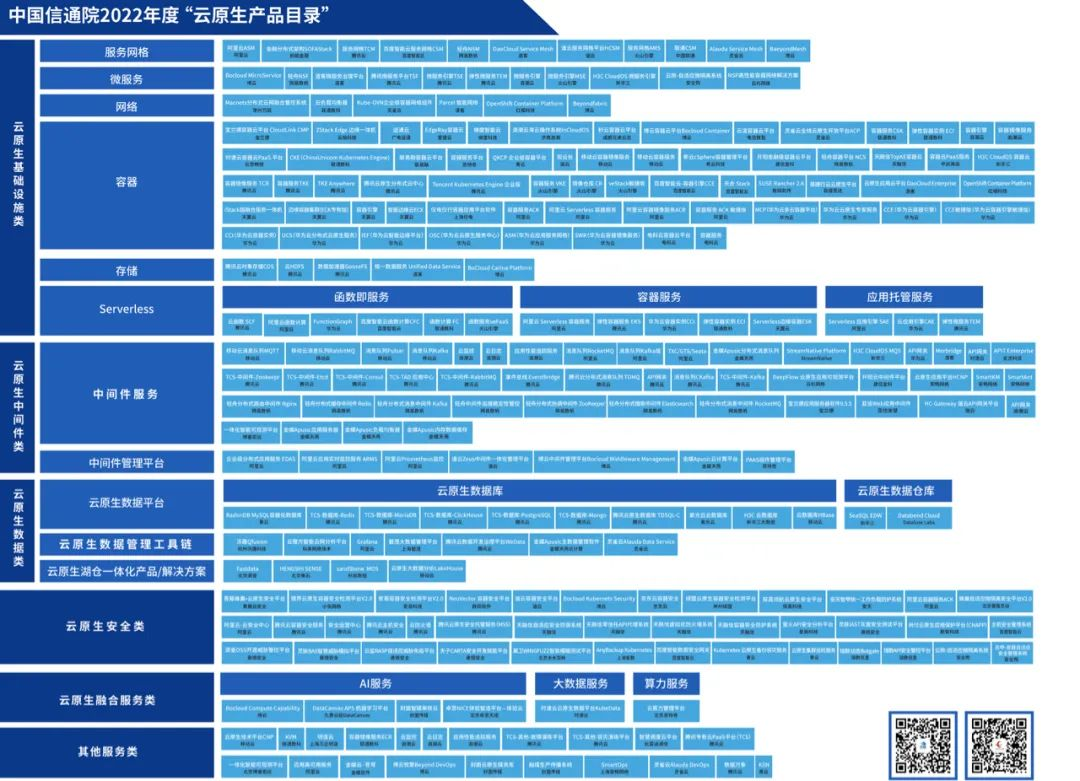
腾讯云原生数据库TDSQL-C入选信通院《云原生产品目录》

“去虚向实”大潮下,百度智能云向实而生

Development of wireless communication technology, cv5200 long-distance WiFi module, UAV WiFi image transmission application
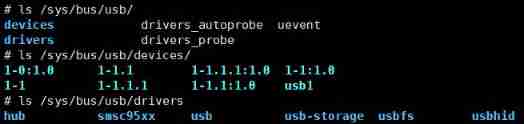
Analysis of USB network card sending and receiving data
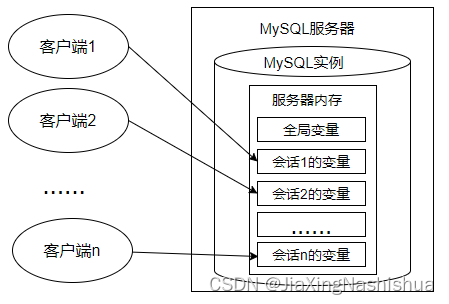
变量、流程控制与游标(MySQL)
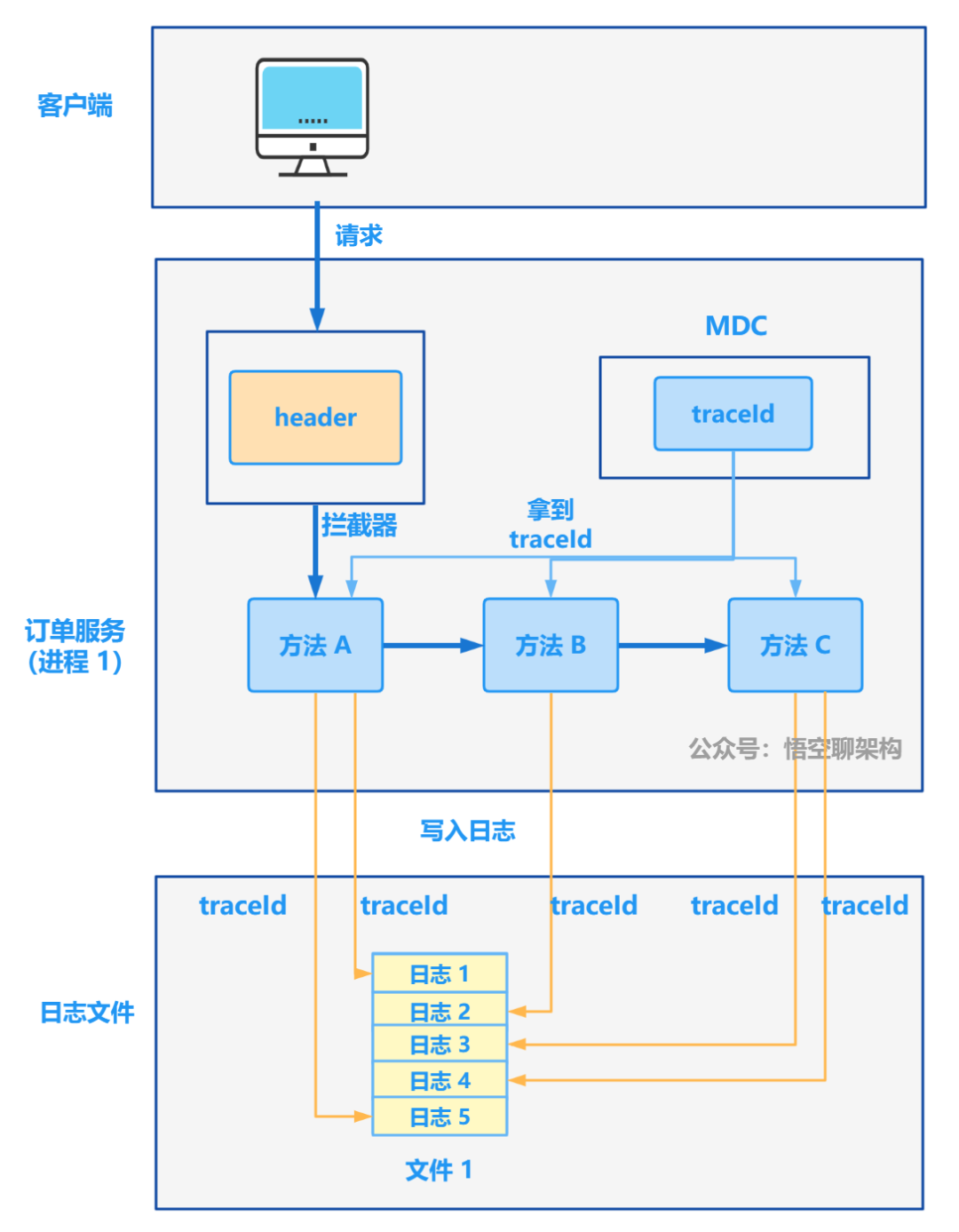
从 1.5 开始搭建一个微服务框架——日志追踪 traceId
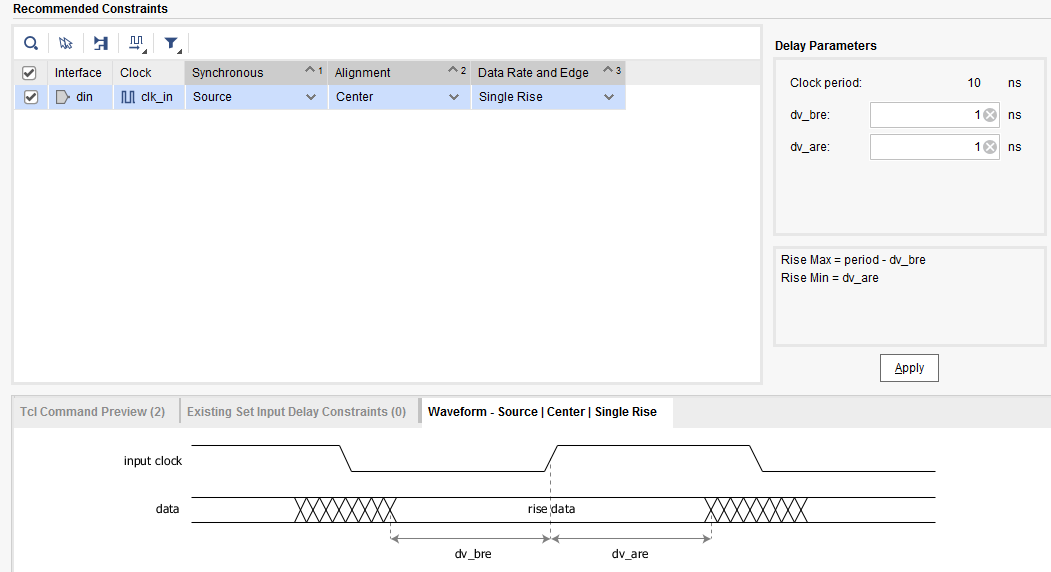
input_ delay
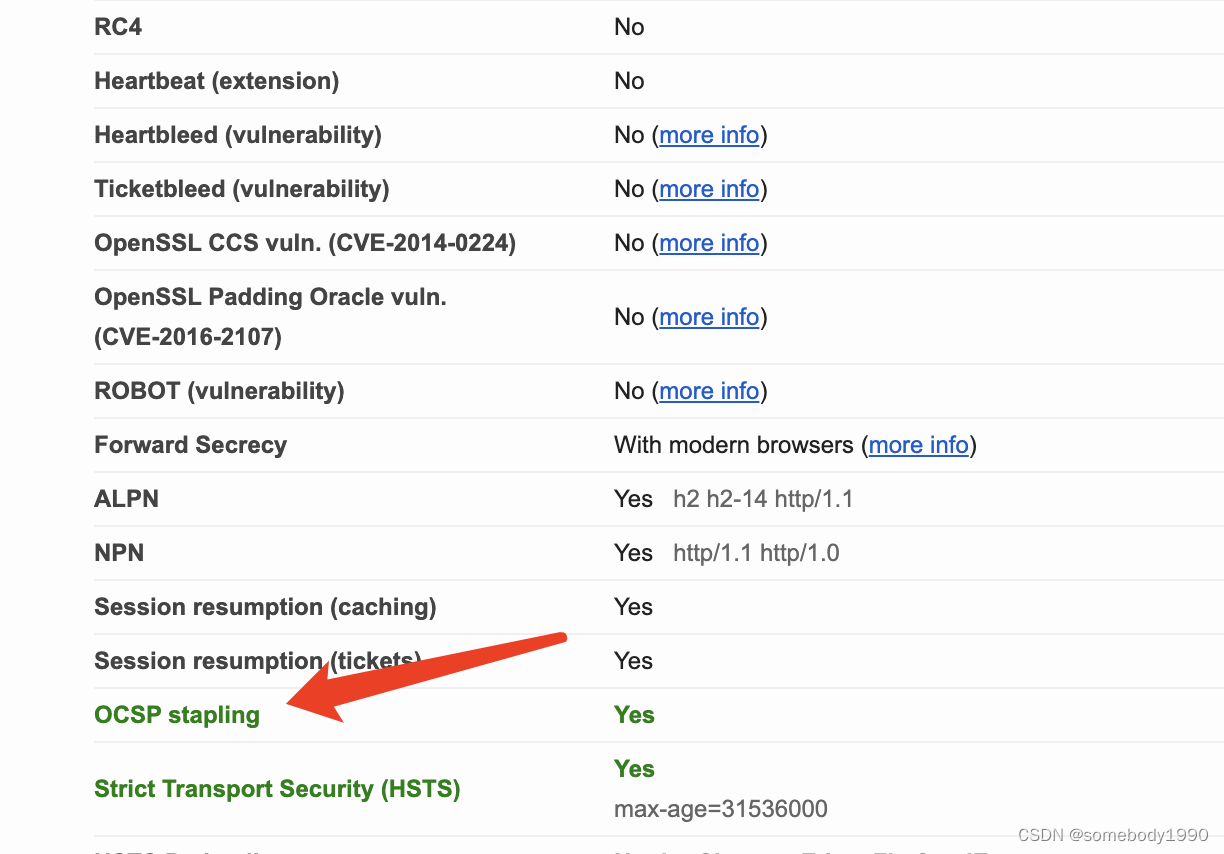
Cryptography series: detailed explanation of online certificate status protocol OCSP
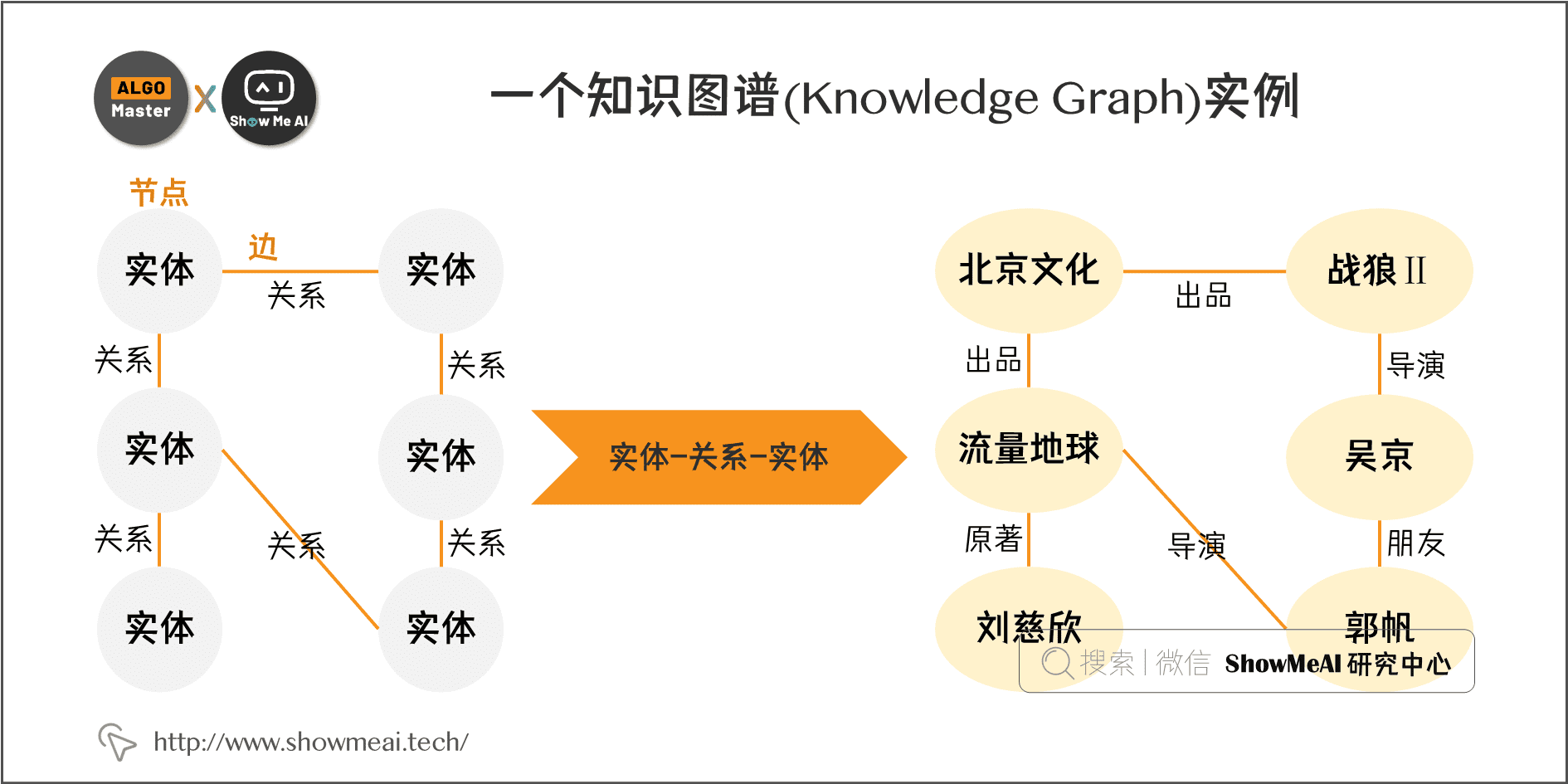
知识图谱构建全流程
随机推荐
Oauth2协议中如何对accessToken进行校验
Laravel php artisan 自动生成Model+Migrate+Controller 命令大全
2022 information security engineer examination outline
Detailed explanation of 19 dimensional integrated navigation module sinsgps in psins (initial assignment part)
DOMContentLoaded和window.onload
硬件之OC、OD、推挽解释
C language string sorting
unrecognized selector sent to instance 0x10b34e810
Babbitt | metauniverse daily must read: is IP authorization the way to break the circle of NFT? What are the difficulties? How should holder choose the cooperation platform
杰理之播内置 flash 提示音控制播放暂停【篇】
杰理之FM 模式单声道或立体声选择设置【篇】
【达梦数据库】添加自动收集统计信息的任务
mos管實現主副電源自動切換電路,並且“零”壓降,靜態電流20uA
Netperf and network performance measurement
Development of wireless communication technology, cv5200 long-distance WiFi module, UAV WiFi image transmission application
Make (convert) ICO Icon
Appx代码签名指南
Household appliance industry under the "retail is king": what is the industry consensus?
Jerry's FM mode mono or stereo selection setting [chapter]
Redis getting started complete tutorial: common exceptions on the client