当前位置:网站首页>Dry goods | summarize the linkage use of those vulnerability tools
Dry goods | summarize the linkage use of those vulnerability tools
2022-07-07 13:46:00 【Network security self-study room】
0x00 Introduction to missed scanning
Introduction for web Level vulnerability scanning , And the linkage use of some tools to improve efficiency , Because different objects need to use different types of scanning , for example awvs For domestic cms The framework may not scan so efficiently , Compare awvs It is a foreign maintenance update , So in this case, not a missed scan can solve all the problems , This is also an easy problem for novice Xiaobai to talk about in the test .
0x01 Burpsuite linkage xray Leakage and app 0x02 AWVS linkage Xray At the same time, missed scanning detection 0x03 awvs linkage bp linkage xray 0x04 afrog Leakage and 0x05 vulmap,pocassist Leakage and 0x06 Goby linkage awvs&xray&fofa 0x07 Single point tool
0x01 Burpsuite linkage xray Leakage and app
Flow trend : Simulator app data (192.168.181.1:8888)–>Burpsuite( monitor 192.168.181.1:8888, Forwarding traffic 127.0.0.1:8888)–>Xray( monitor 127.0.0.1:8888)
Project address :xray:https://github.com/chaitin/xray/releases
Use : Burpsuite monitor app Traffic :  Burpsuite Forwarding traffic :
Burpsuite Forwarding traffic : 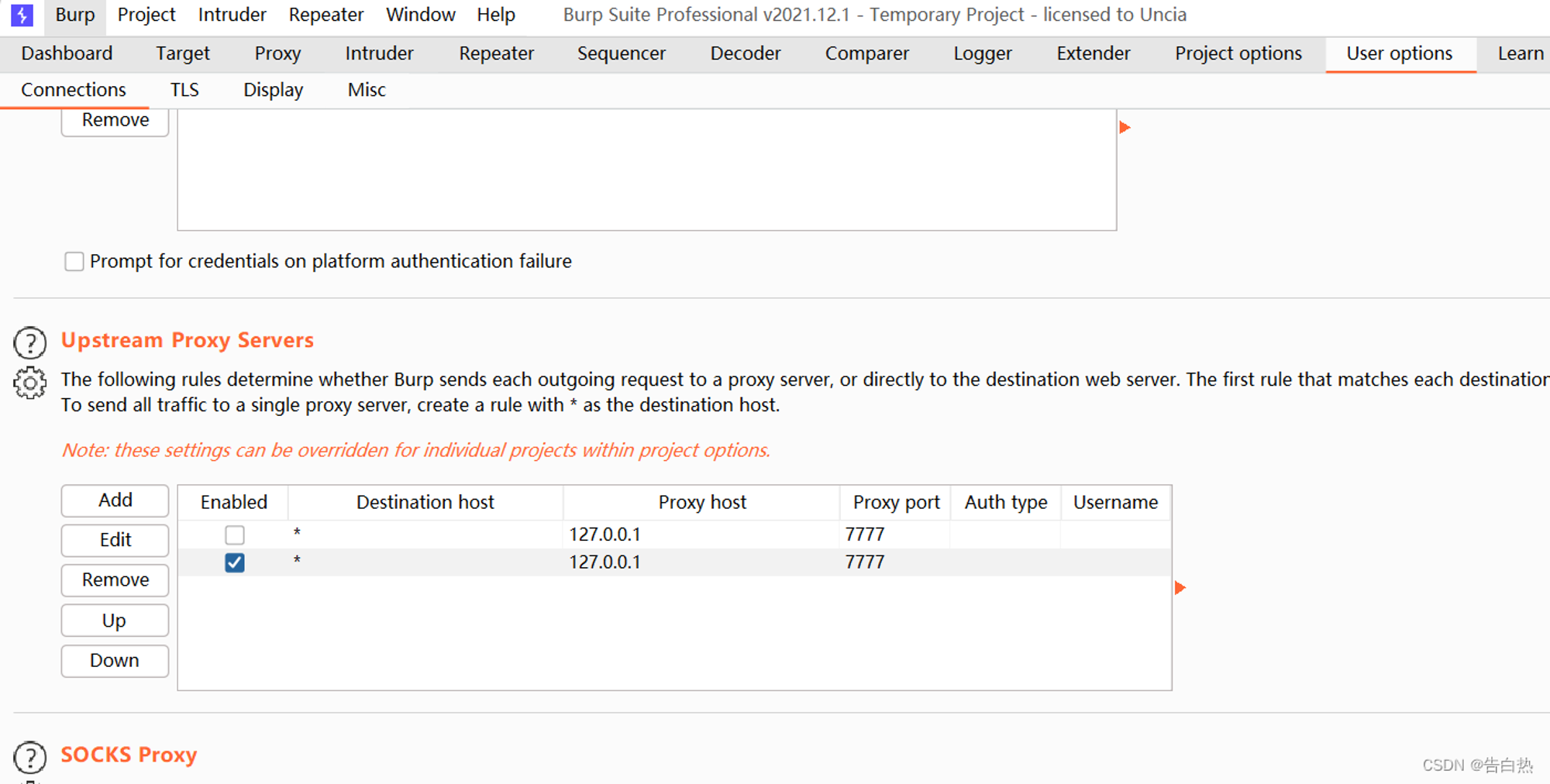
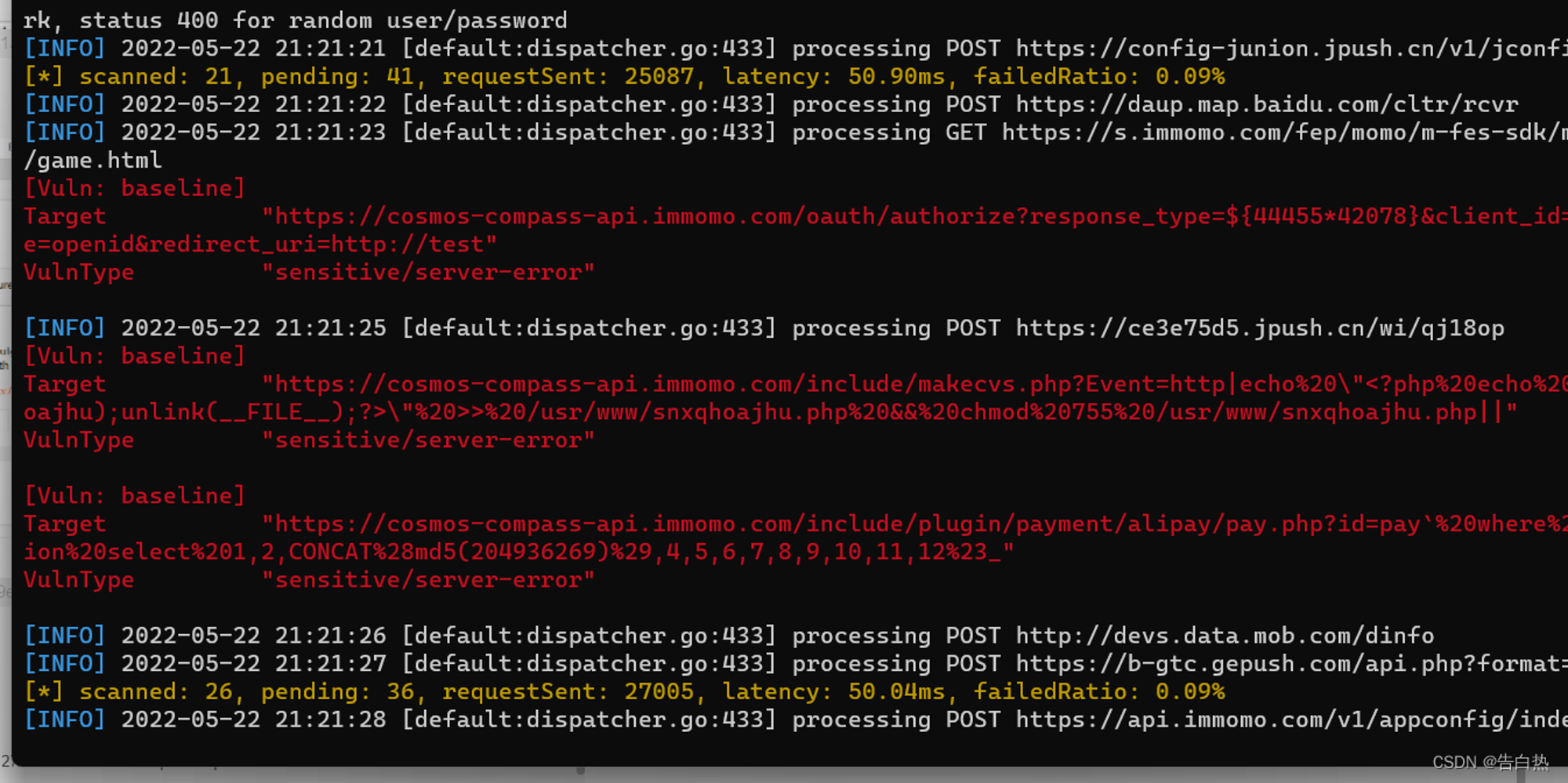
xray Detect traffic packets :
.\xray_windows_amd64.exe webscan --listen 127.0.0.1:7777 --html-output mniqi.html
0x02 AWVS linkage Xray At the same time, missed scanning detection
Flow trend : awvs Test object ( And send the traffic to IP1)–>Xray Monitor any traffic (0.0.0.0 Test flow leakage scanning )
Project address : awvs:https://www.ddosi.org/awvs14-6-log4j-rce/ Use : awvs After setting the scanning object, forward the traffic to 127.0.0.1:1111: 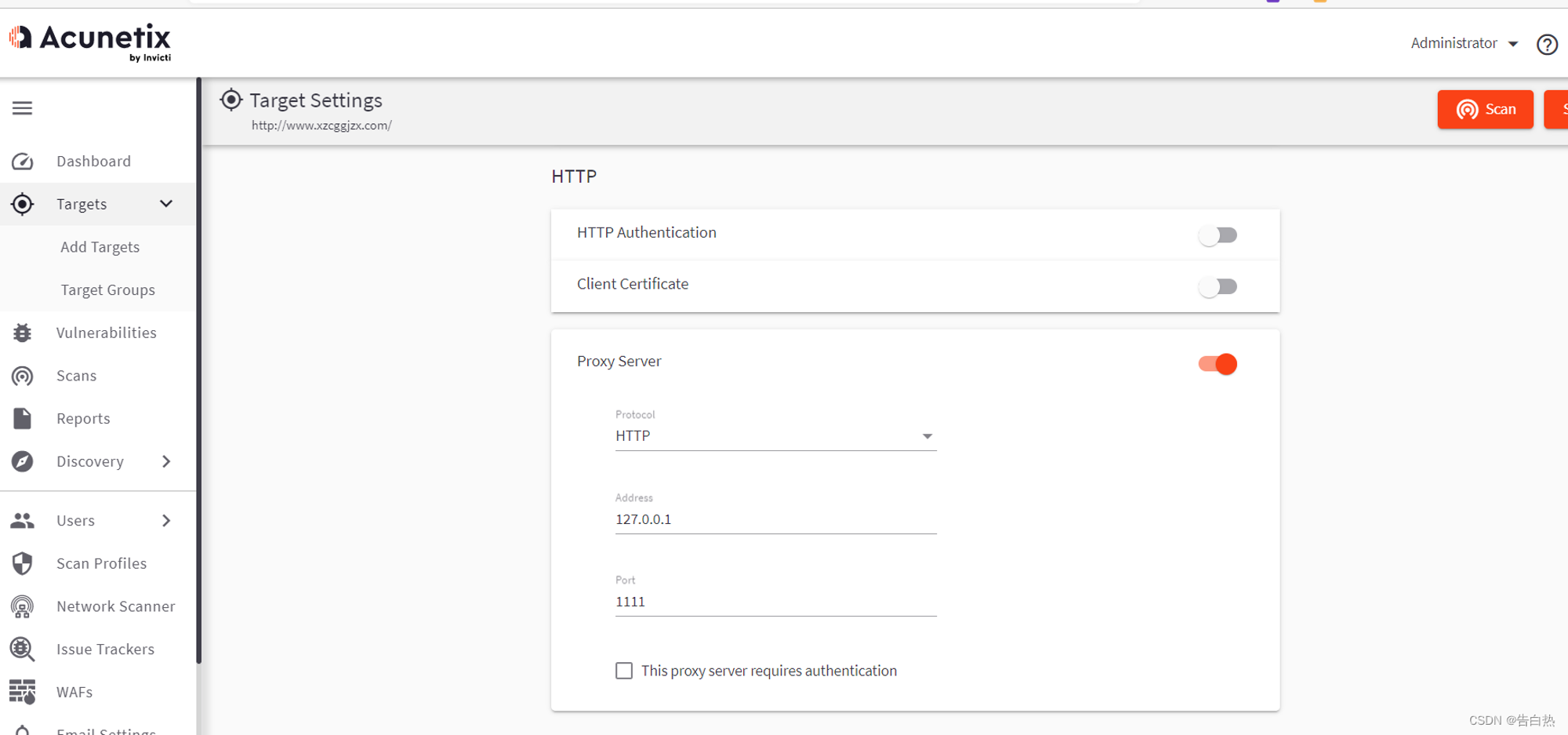 xray monitor 127.0.0.1:1111 Flow and scan :
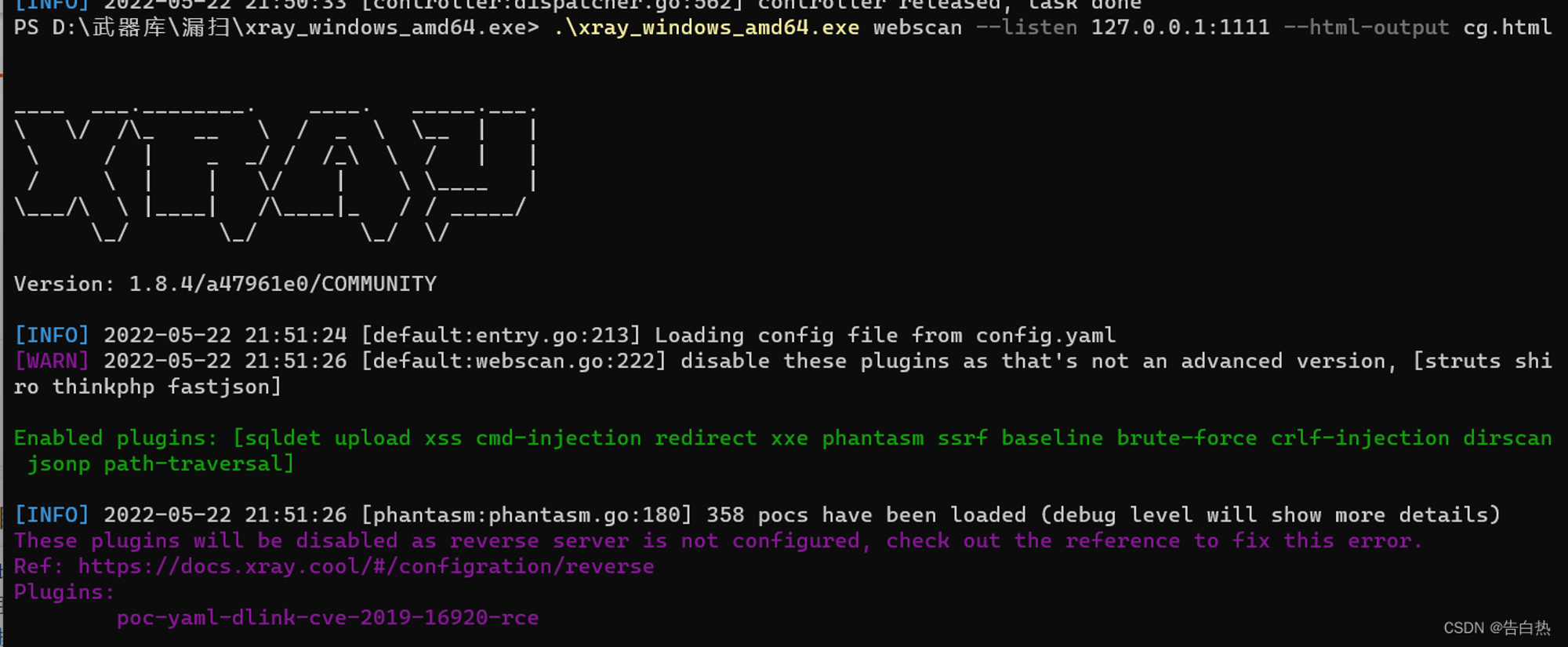
xray monitor 127.0.0.1:1111 Flow and scan :
.\xray_windows_amd64.exe webscan --listen 127.0.0.1:1111 --html-output cg.html
 Linkage scanning :
Linkage scanning : 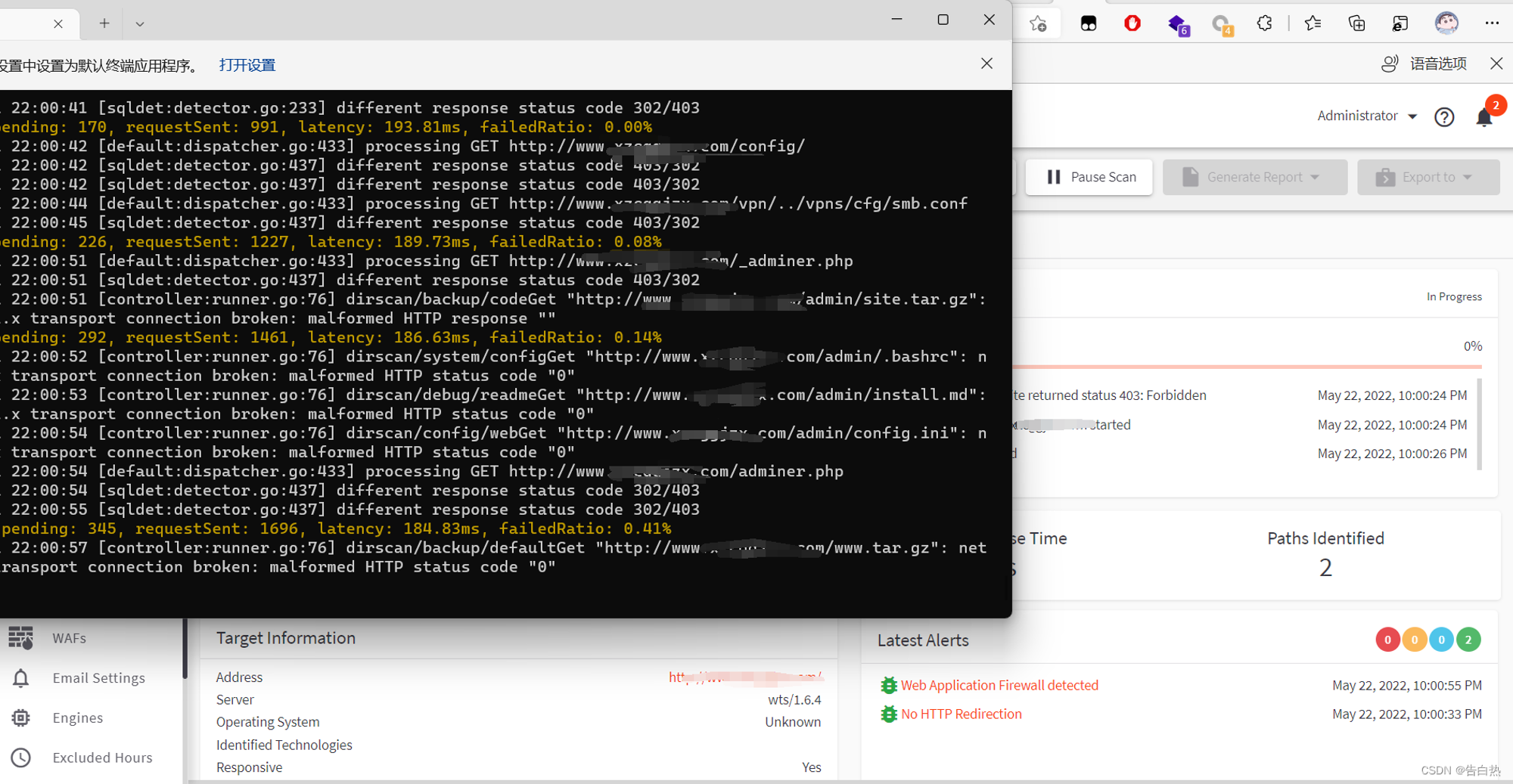
0x03 awvs linkage bp linkage xray
Flow trend :awvs Traffic –>Burpsuite–>Xray Test flow
Same as above , The effect is almost the same , Just forward the traffic in several layers
0x04 afrog Leakage and
afrog It is a high-performance 、 Fast and steady 、PoC Customizable vulnerability scanning ( Dig a hole ) Tools ,PoC involve CVE、CNVD、 Default password 、 Information disclosure 、 fingerprint identification 、 Unauthorized access 、 Arbitrary file reading 、 Command execution and other vulnerability types , Help network security practitioners quickly verify and repair vulnerabilities in time .
Project use :
Scanning a single target :
afrog -t http://127.0.0.1 -o result.html
Scan multiple targets :
afrog -T urls.txt -o result.html
for example :urls.txt
http://192.168.139.129:8080
http://127.0.0.1
Test individual PoC file :
afrog -t http://127.0.0.1 -P ./testing/poc-test.yaml -o result.html
Test multiple PoC file :
afrog -t http://127.0.0.1 -P ./testing/ -o result.html
Output after scanning html The report , You can intuitively see the existing vulnerabilities , Then test and use : 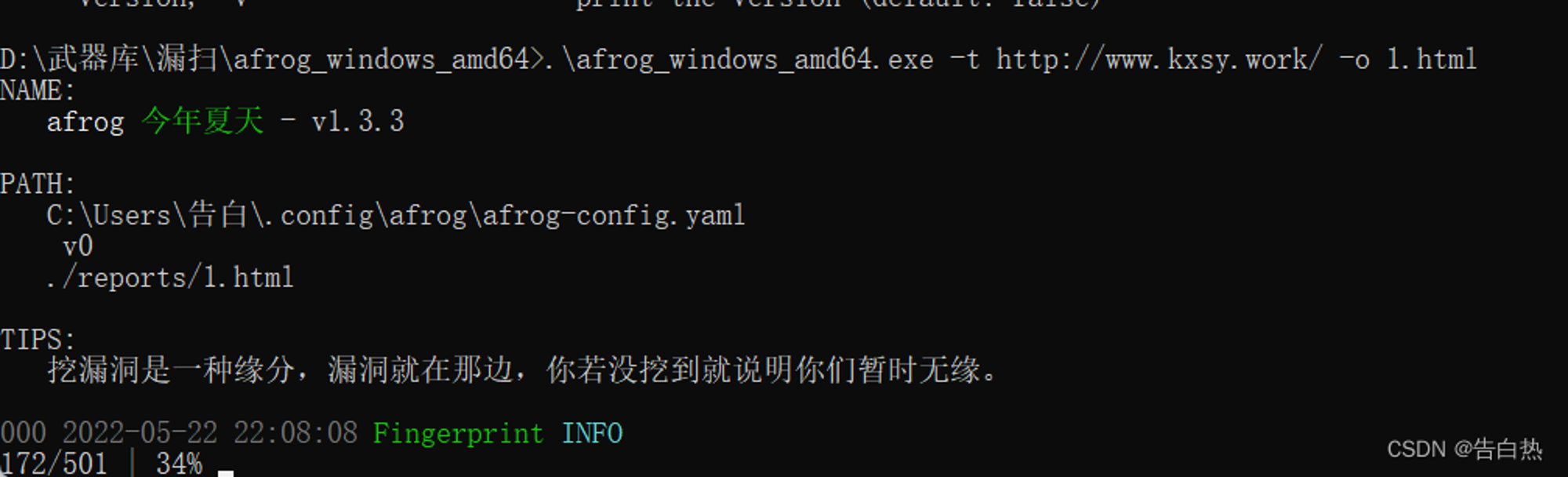
0x05 vulmap,pocassist Leakage and
The missed scan is in an un updated state , The project gives , You can't do the experiment yourself Project address : vulmap:https://github.com/zhzyker/vulmap/releases pocassist:https://github.com/jweny/pocassist/releases
0x06 Goby linkage awvs&xray&fofa
Goby It is a next-generation network security tool based on cyberspace mapping technology . It generates emergency response to network security incidents and vulnerabilities by establishing a comprehensive asset knowledge base for the target network . Goby Provide the most comprehensive asset identification .Goby Preset 100,000 Multiple rule recognition engines , It can automatically identify and classify hardware equipment and software business systems , And comprehensively analyze the business systems existing in the network .
Project address :https://github.com/gobysec/Goby/releases
Plug in linkage : If there are too many, we won't make a demonstration ,goby It can play a good role in asset sorting , Very recommended 
0x07 Single point tool
In general testing , Missed scan is to detect the whole target , But often when using a single weapon , It can have a very bad effect when penetrating , Here are some common individual weapons :
Graphical penetration Arsenal :GUI_TOOLS_V6.1_by Safety circle little prince –bugfixed 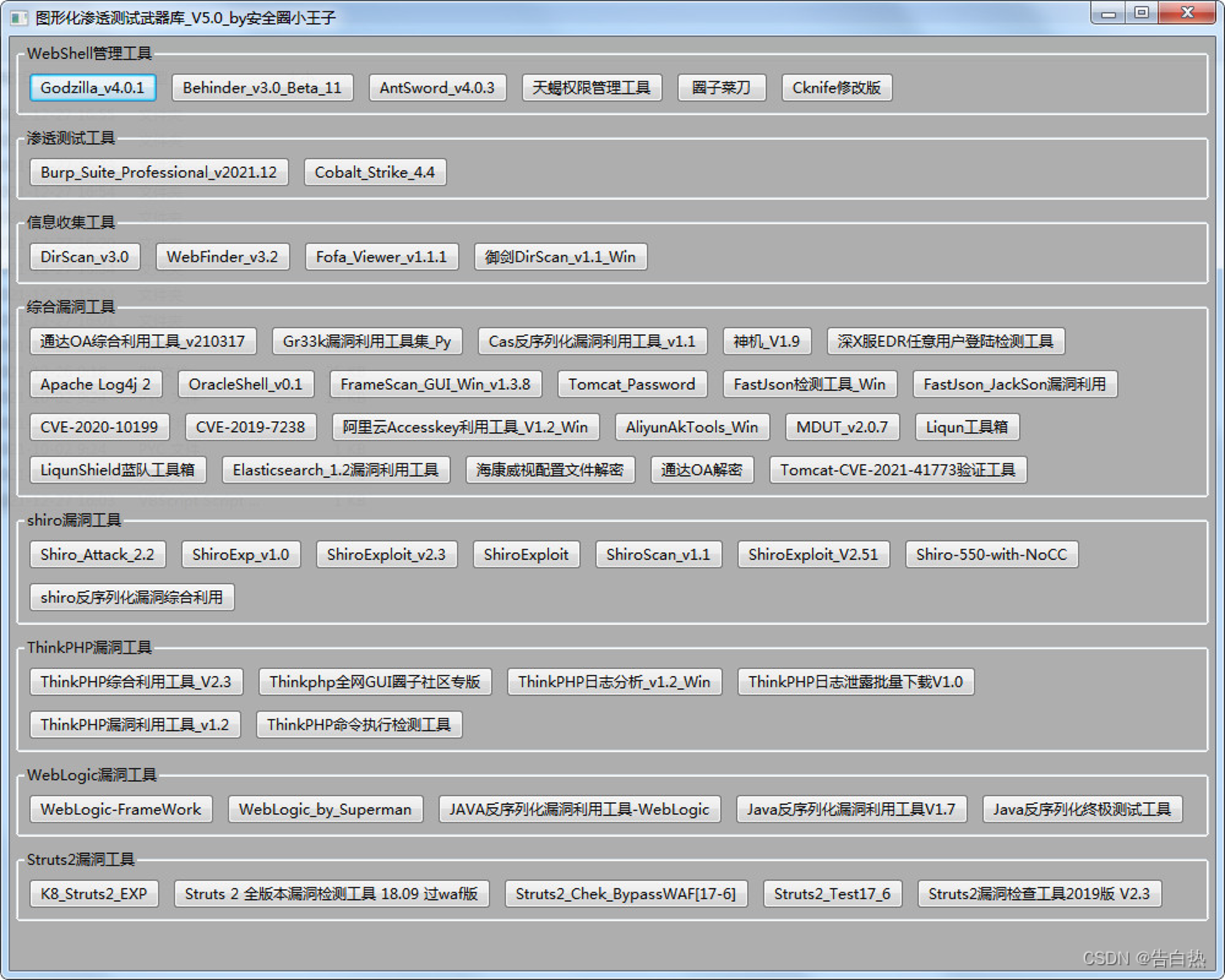
CMS Vulnerability scanner name Supported by CMS platform :
Droopescan WordPress,Joomla,Drupal,Moodle,SilverStripe
CMSmap WordPress,Joomla,Drupal,Moodle
CMSeeK WordPress,Joomla,Drupal etc.
WPXF WordPress
WPScan WordPress
WPSeku WordPress
WPForce WordPress
JoomScan Joomla
JoomlaVS Joomla
JScanner Joomla
Drupwn Drupal
Typo3Scan Typo3
Zhiyuan OA Comprehensive utilization tools https://github.com/Summer177/seeyon_exp
Accessible OA Comprehensive utilization tools https://github.com/xinyu2428/TDOA_RCE TDOA_RCE
Lan Ling OA Exploit tools / The front desk is unconditional RCE/ File is written to https://github.com/yuanhaiGreg/LandrayExploit
Pan Wei OA Vulnerability comprehensive utilization script https://github.com/z1un/weaver_exp weaver_exp
Ruijie network EG Easy gateway RCE Batch safety inspection https://github.com/Tas9er/EgGateWayGetShell EgGateWayGetShell
CMSmap For popular CMS Tools for security scanning https://github.com/Dionach/CMSmap CMSmap
Use Go Developed WordPress Vulnerability scanning tool https://github.com/blackbinn/wprecon wprecon
One Ruby frame , To help with WordPress Perform penetration test on the system https://github.com/rastating/wordpress-exploit-framework
WPScan WordPress Security scanners https://github.com/wpscanteam/wpscan wpscan
WPForce Wordpress Attack Suite https://github.com/n00py/WPForce WPForce
边栏推荐
- 【堡垒机】云堡垒机和普通堡垒机的区别是什么?
- 566. Reshaping the matrix
- 2022-7-7 Leetcode 844.比较含退格的字符串
- Show the mathematical formula in El table
- Redis只能做缓存?太out了!
- 【日常训练】648. 单词替换
- 【面试高频题】难度 2.5/5,简单结合 DFS 的 Trie 模板级运用题
- Sliding rail stepping motor commissioning (national ocean vehicle competition) (STM32 master control)
- MongoDB的导入导出、备份恢复总结
- Shell batch file name (excluding extension) lowercase to uppercase
猜你喜欢
OSI 七层模型
交付效率提升52倍,运营效率提升10倍,看《金融云原生技术实践案例汇编》(附下载)
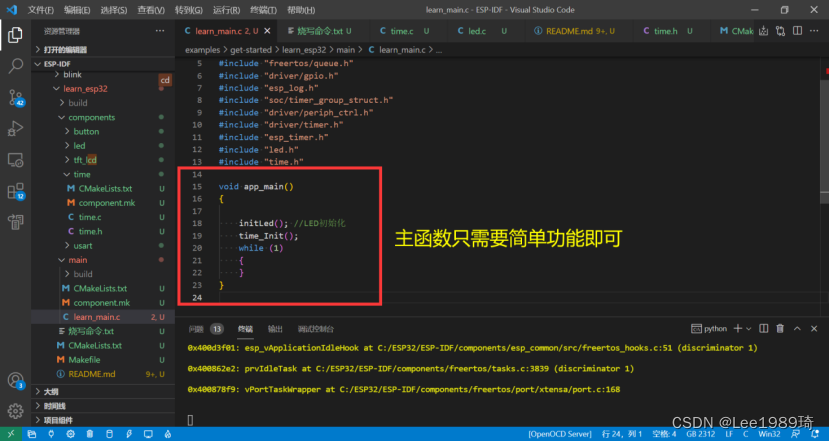
Esp32 construction engineering add components
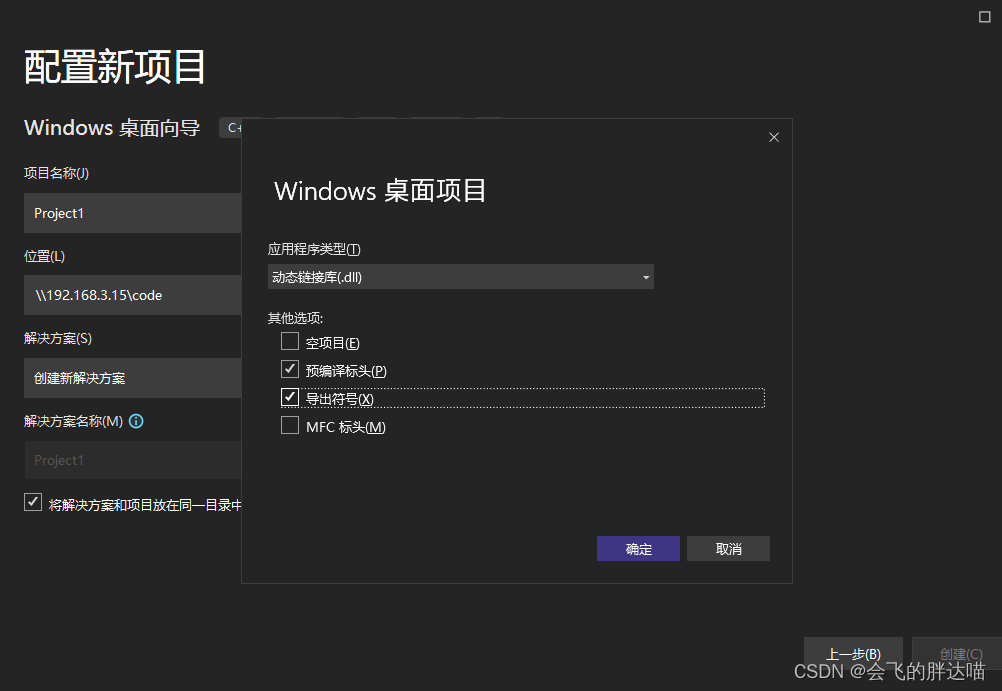
Error lnk2019: unresolved external symbol
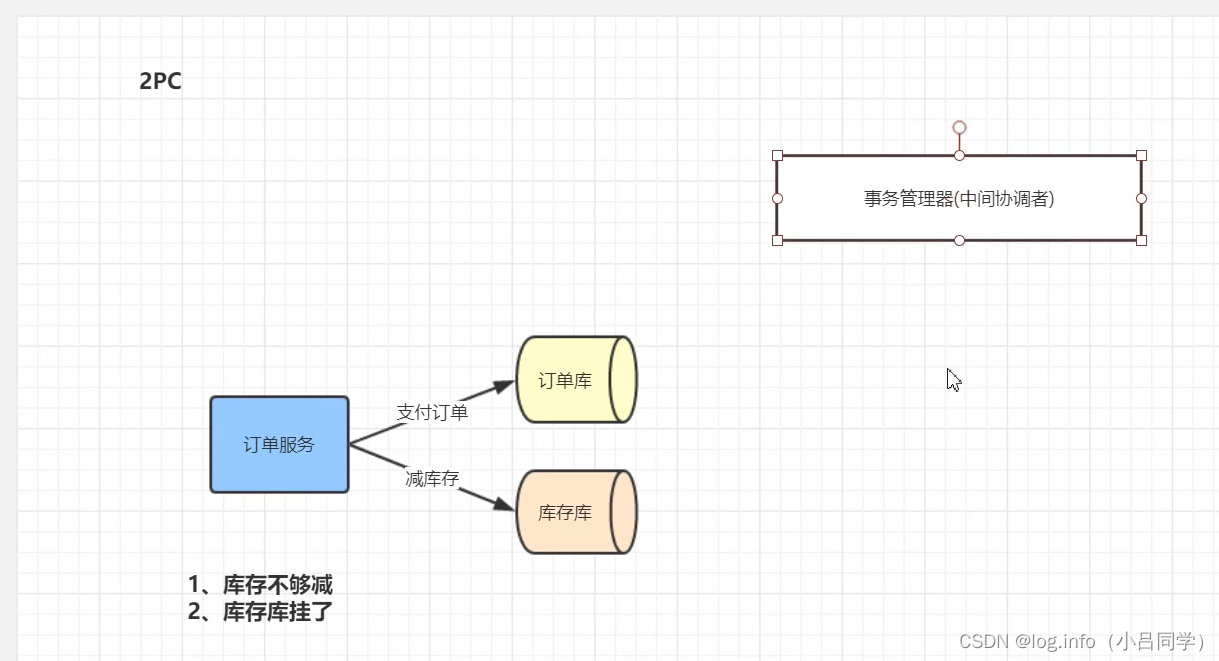
Distributed transaction solution
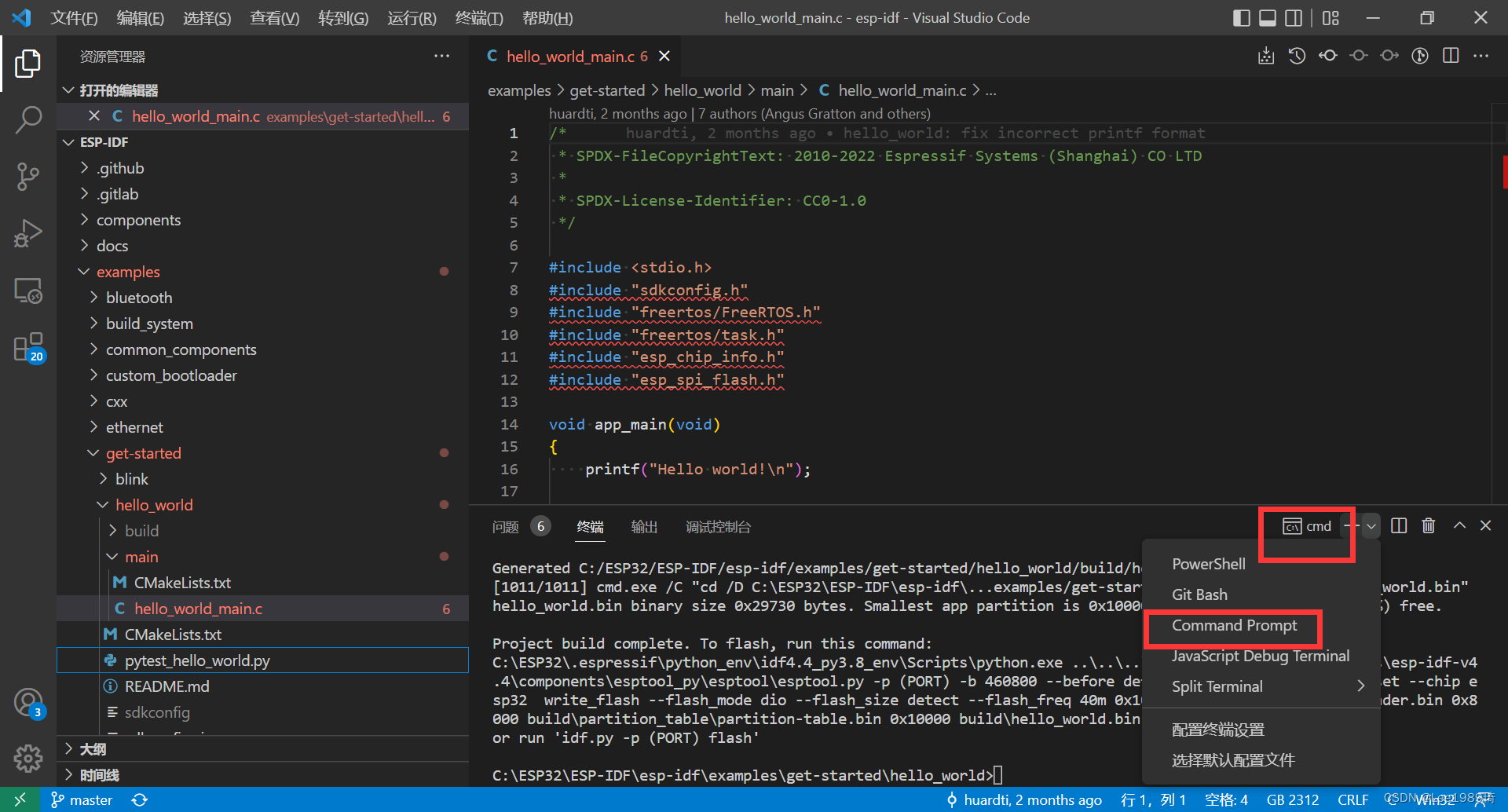
Esp32 ① compilation environment
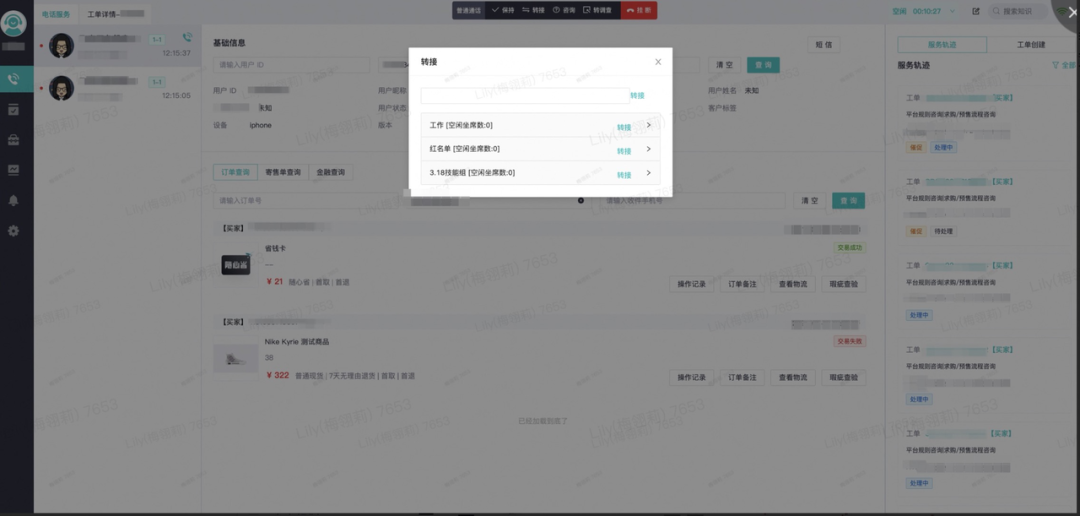
得物客服热线的演进之路
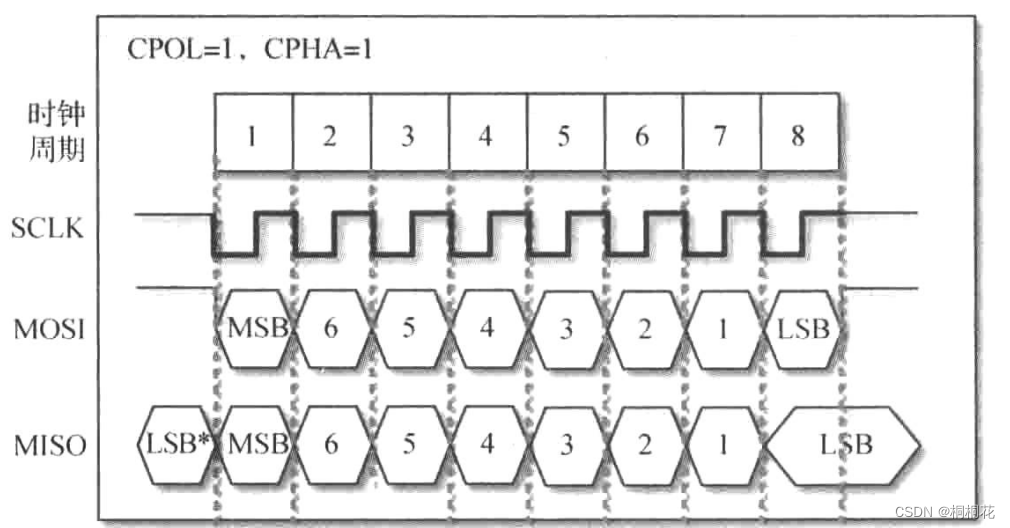
数字ic设计——SPI
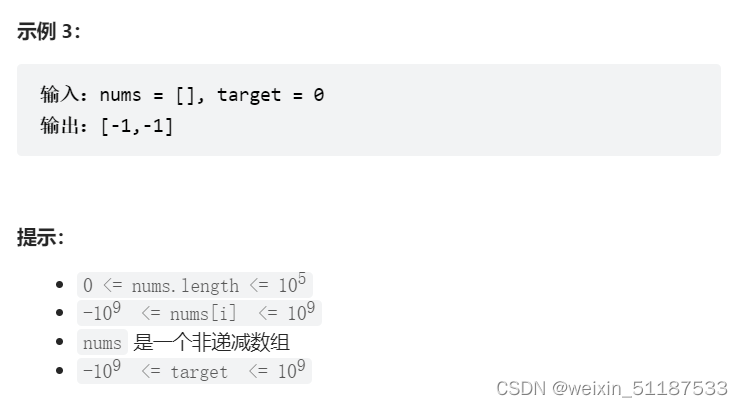
2022-7-7 Leetcode 34. Find the first and last positions of elements in a sorted array
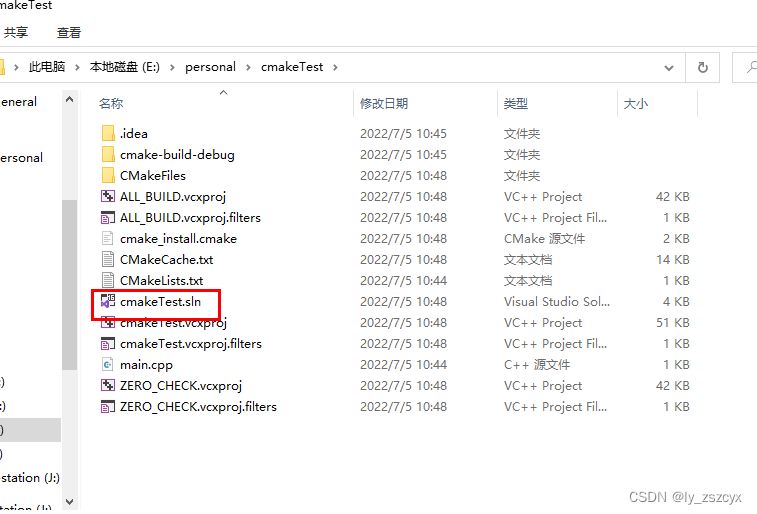
cmake 学习使用笔记(一)
随机推荐
MySQL error 28 and solution
[learning notes] agc010
MongoDB内部的存储原理
Co create a collaborative ecosystem of software and hardware: the "Joint submission" of graphcore IPU and Baidu PaddlePaddle appeared in mlperf
高等数学---第八章多元函数微分学1
高端了8年,雅迪如今怎么样?
2022-7-6 Leetcode27.移除元素——太久没有做题了,为双指针如此狼狈的一天
User management summary of mongodb
1. Deep copy 2. Call apply bind 3. For of in differences
[QNX Hypervisor 2.2用户手册]6.3.4 虚拟寄存器(guest_shm.h)
Server to server (S2S) event (adjust)
1、深拷贝 2、call apply bind 3、for of for in 区别
Fast development board pinctrl and GPIO subsystem experiment for itop-imx6ull - modify the device tree file
What parameters need to be reconfigured to replace the new radar of ROS robot
Show the mathematical formula in El table
Build a secure and trusted computing platform based on Kunpeng's native security
Detr introduction
Esp32 construction engineering add components
Xshell connection server changes key login to password login
OSI 七层模型