当前位置:网站首页>Adb authorization process analysis
Adb authorization process analysis
2022-08-05 07:59:00 【Xiaoyuanzi 2016】
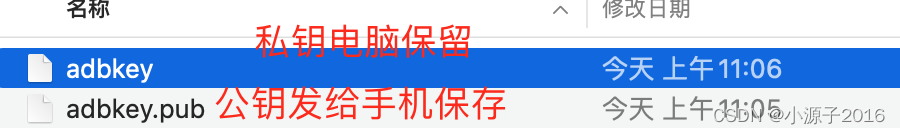
adbkey and adbkey.pub
adbkey and adbkey.pub_caibaihui's blog - CSDN blog _what is adbkey file
Experiments have shown that the public key on the mobile phone and the private key on the computer can be successfully paired, even if I modify the public key on the computer later, it will not affect the previous authorization
For example, the mobile phone has a built-in public key, and the paired private key is generated on my computer to complete the authorization
adb pull /data/misc/adb/adb_keys . The public key is stored in it
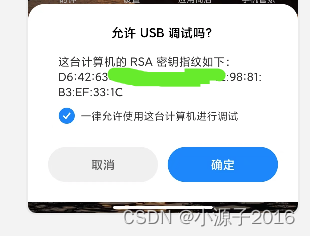
The authorization pop-up window shows that the RSA key fingerprint should be based on the public key. I don't know how to calculate it.
adb keygen cc can be used to generate RSA public and private keys
This information box will typically display the fingerprint (MD5) of the host's public key, not the host's
public key itself
ADB public key and private key authentication mechanism Use the following command to generate the host public key fingerprint: $ awk "{print $1}" < adbkey.pub | openssl base64 -A -d -a | openssl md5 -c | awk "{print $2}" | tr "[:lower:]" "[:upper:]" Actually, I used this command to find that the generated pop-up window is different from the one I saw, I am ready to give up and find new articles In general, it is necessary to process base64 and md5 separately For this, I need to know that the actual key in the file is the base64 encoded part, i.e. long cryptic string of characters.In my case the key field was always followed by the user-host field, i.e. something like In the latter case, I need to filter on the second field.In Windows, apparently, this is done using a Extract the key in the second field of 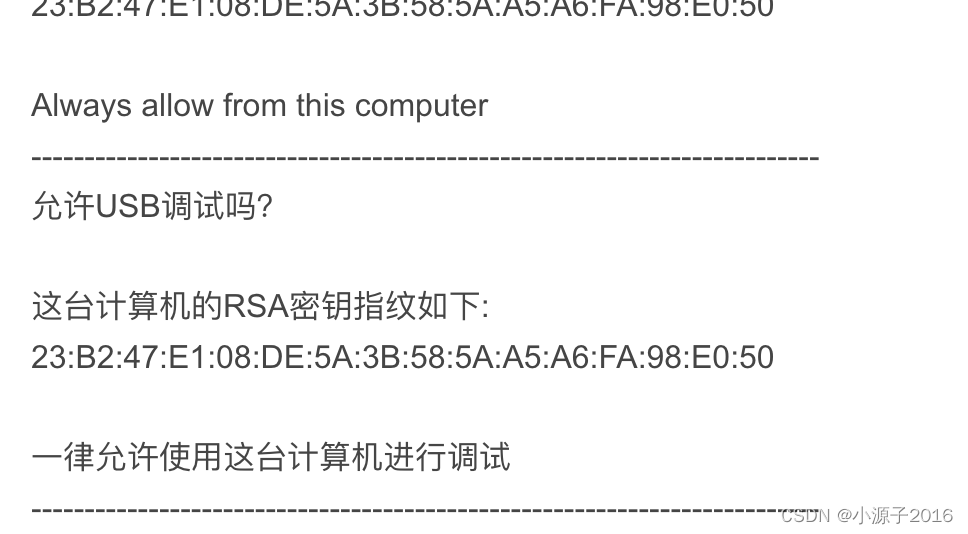
23:B2:47:E1:08:DE:5A:3B:58:5A:A5:A6:FA:98:E0:50[email protected] (also [email protected]), in some strings the case is preceded by a field containing ssh-rsa.for loop.I also send the output to a file for certUtil to do subsequent digestion, the output of which goes into the file again - containing the key which is no longer base64 encoded but in bytes - and finally hashed with MD5.id_rsa.pub into a file named tmp.key_base64:
边栏推荐
猜你喜欢
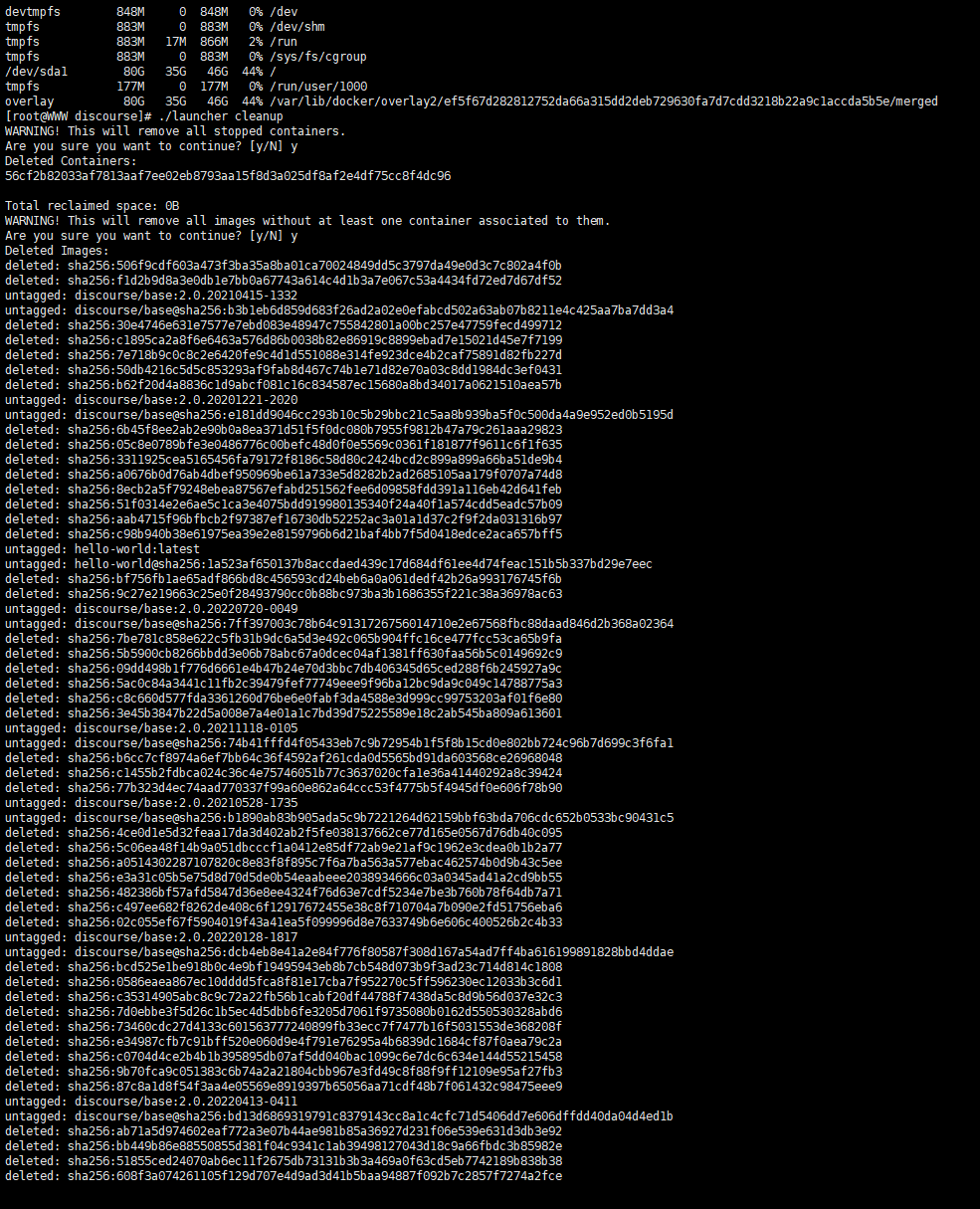
Discourse 清理存储空间的方法
![[Structural Internal Power Cultivation] The Mystery of Enumeration and Union (3)](/img/39/d20f45ccc86ebc4e5aebc8e4d0115f.png)
[Structural Internal Power Cultivation] The Mystery of Enumeration and Union (3)
风控特征的优化分箱,看看这样教科书的操作
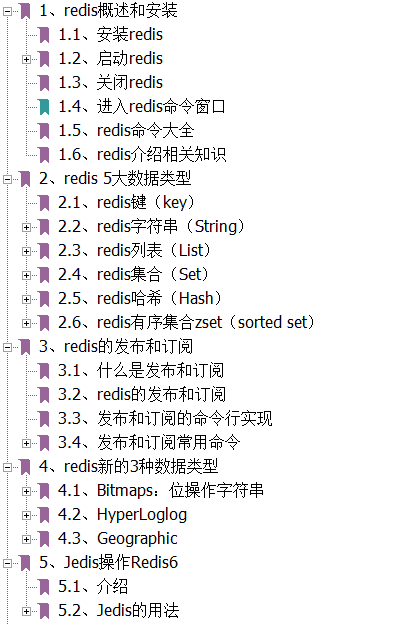
Redis 全套学习笔记.pdf,太全了
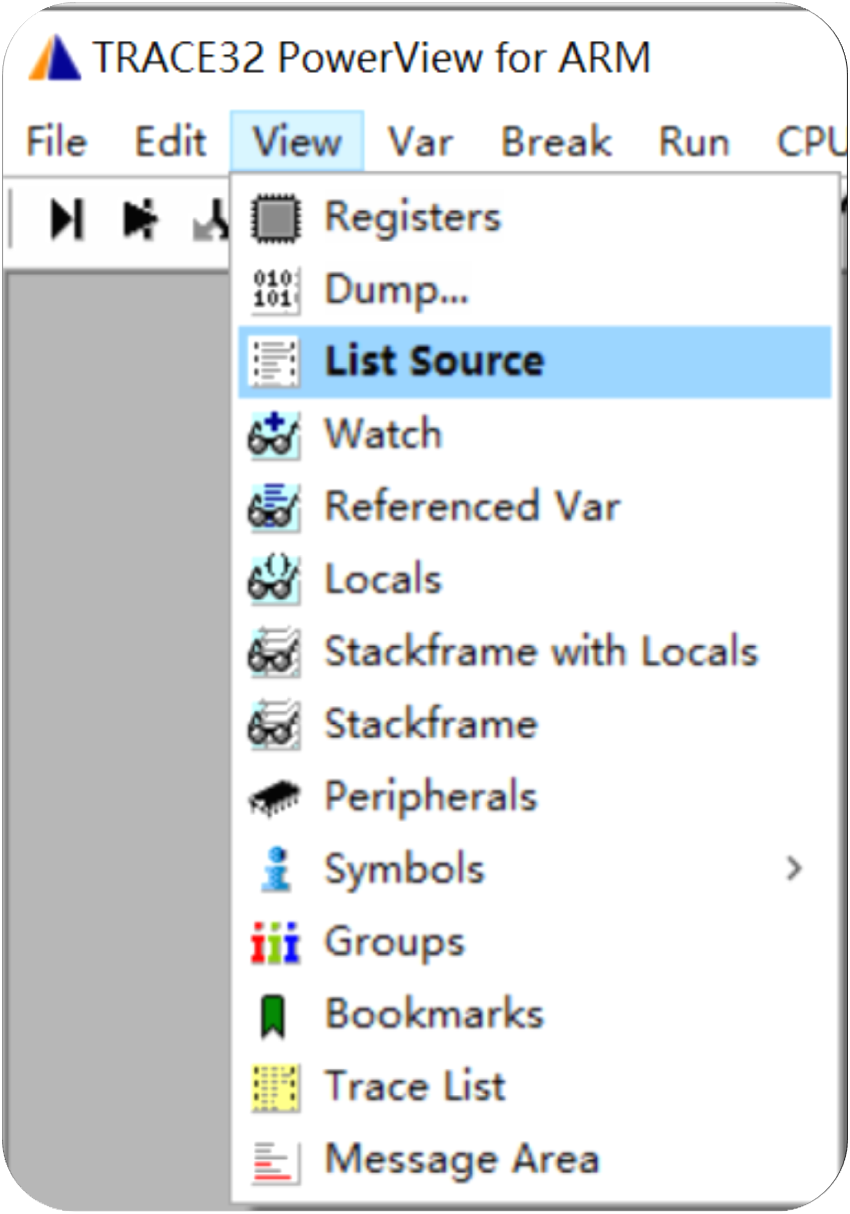
TRACE32——List源代码查看
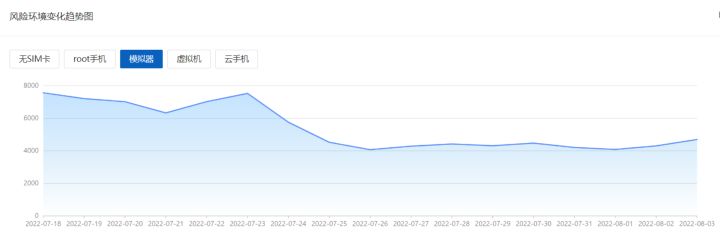
游戏模拟器成了外挂帮凶,灰产对抗再升级
Algorithm Supplements Fifteen Complementary Linked List Related Interview Questions
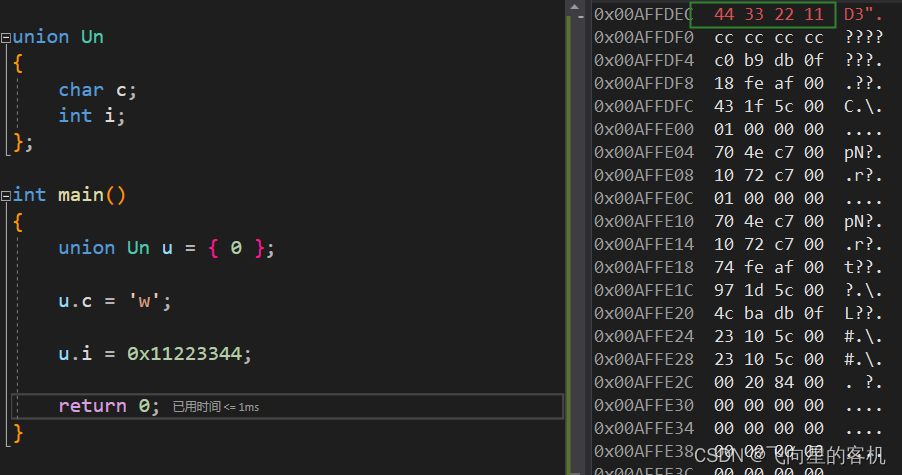
【结构体内功修炼】枚举和联合的奥秘(三)
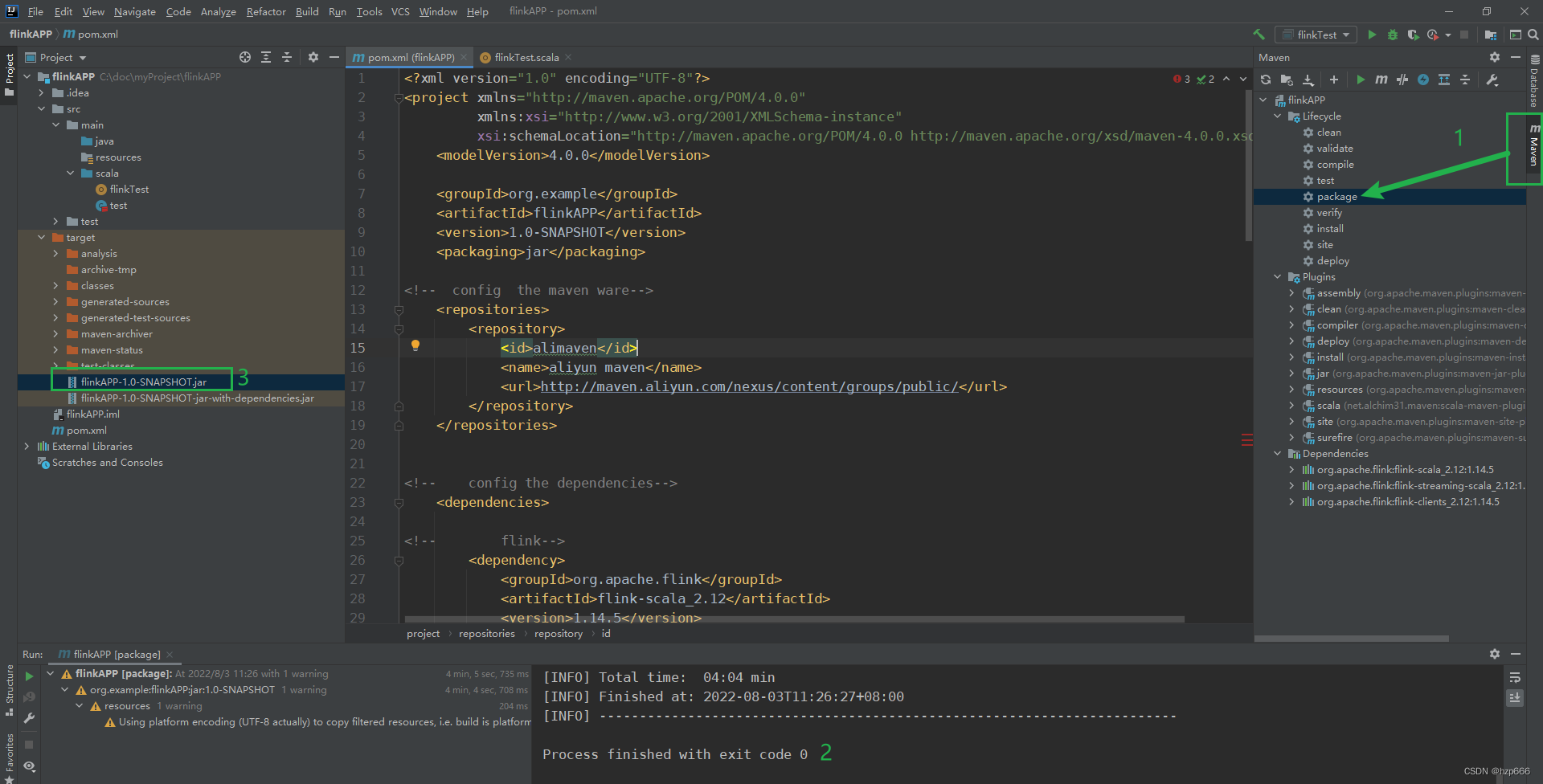
Flink Learning 10: Use idea to write WordCount and package and run
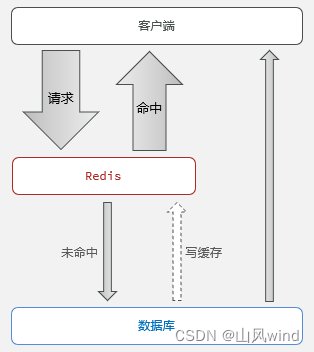
Redis缓存以及存在的问题--缓存穿透、缓存雪崩、缓存击穿及解决方法
随机推荐
【 LeetCode 】 235. A binary search tree in recent common ancestor
Unity—物理引擎+“武器模块”
v-if/v-else根据计算判断是否显示
MySQL: order by sorting query, group by grouping query
Redis 全套学习笔记.pdf,太全了
爬虫之验证码
[Structural Internal Power Cultivation] The Mystery of Enumeration and Union (3)
Hash these knowledge you should also know
软件系统测试和验收测试有什么联系与区别?专业软件测试方案推荐
YOLOv3 SPP理论详解(包括CIoU及Focal loss)
openSource 知:社区贡献
Does Libpq support read-write separation configuration?
Redis常用命令
[NOIP2010 提高组] 机器翻译
学习机赛道加速:请“卷”产品,不要“卷”营销
uniapp时间组件封装年-月-日-时-分-秒
Mysql 死锁和死锁的解决方案
请问my sql如何把两个表的内容集合在一起啊?
数据源对象管理Druid和c3p0
青苹果论坛重新开放