当前位置:网站首页>Distributed consensus mechanism
Distributed consensus mechanism
2020-11-08 04:49:00 【The name of algorithm】
- C/S Pattern
- Let's start with the simplest two computers , One is the server , One is the client , namely C/S Pattern . The client wants to manipulate the data on the server node .
- Since the client wants to manipulate the data on the server , Network communication is necessary , dispatch orders . But we can't guarantee that every message sent by the client will be received by the server .
- So when the server receives the message , A confirmation message will be sent to the client , If the client does not receive the confirmation message sent by the server , The client will resend the same message command .
- But the time when the client sends a message command to the server may be different . The time when the server sends the confirmation message to the client is also different .
- This will result in different order of message commands received between multiple servers and multiple clients . Between different servers , Their states are different .
- For a group of servers , If all servers execute a sequence of commands in the same order ( This set of commands may be sent by multiple clients ), This group of servers implements state replication . Because it's easier for a single server to do this , We usually only send message commands to a single server , A single server must also execute a sequence of commands in a sequence .
- When a single server receives a command , It can forward this command to other servers . When it receives confirmation from other servers , It will inform the client that the command has been successfully executed .
- A single server is prone to downtime , If we don't use a single server to forward commands , It's a two-phase commit , A client tries to get all the server locks first , If you get all the server locks , Start sending commands . In this way, all servers will not be able to receive commands from other clients , Ensure the order consistency of all servers , After the client sends the command, it releases all the server locks . If this client can't get all the server's locks , Release the lock of the server you get , Wait for a while , Try to get all the server locks again . Of course, to save time , We believe that the client can start to execute the command after getting half of the server's lock , Because one client gets half of the server's locks , Then other clients can't get most of the server's locks , In this way, clients who only get a small number of locks have to release the locks .
- Paxos
When we adopt a two-stage proposal , Instead of a single server forwarding , When multiple clients attempt to acquire the lock of most servers at the same time , What's going to happen ? Whether clients have to release all the locks they acquire , To avoid deadlock . Or the client gets part of the lock and hangs up ?
How about if we let this lock expire ? We call these expired locks tickets . In this way, the server that has not been released will not be locked all the time . First, the client requests a ticket from all servers , Tickets are sent from the server to the client , When the client receives half of the tickets sent from the server , The ticket will be sent to all servers along with the command . If the server finds that the ticket received is the latest one sent out by itself , And it's not overdue , It will give the client a positive feedback . The client received positive feedback from more than half of the server , Will notify All the servers Start executing orders . But the server hasn't been informed by the client to execute the command , It will also continue to accept ticket requests from other clients , And will send an up-to-date ticket to other clients . When other clients get half the votes , New tickets and your own commands will be sent to all servers . At this time, if some servers receive this command and ticket , The previous client that received more than half of the server's positive feedback informed all servers to start executing the command , At this time, the commands of all servers are inconsistent .
版权声明
本文为[The name of algorithm]所创,转载请带上原文链接,感谢
边栏推荐
- CPP (4) boost installation and basic use for Mac
- swiper 窗口宽度变化,页面宽度高度变化 导致自动滑动 解决方案
- Littlest jupyterhub| 02 using nbgitpuller to distribute shared files
- 来自不同行业领域的50多个对象检测数据集
- Supervisor process management installation and use
- 你的主机中的软件中止了一个已建立的连接。解决方法
- Template linked list learning
- Unparseable date: 'Mon Aug 15 11:24:39 CST 2016',时间格式转换异常
- Face recognition: attack types and anti spoofing techniques
- Face recognition: attack types and anti spoofing techniques
猜你喜欢

Sum up some useful functions

FORTRAN77从文件中读入若干数据并用heron迭代公式开方

Qt混合Python开发技术:Python介绍、混合过程和Demo

微信昵称emoji表情,特殊表情导致列表不显示,导出EXCEL报错等问题解决!
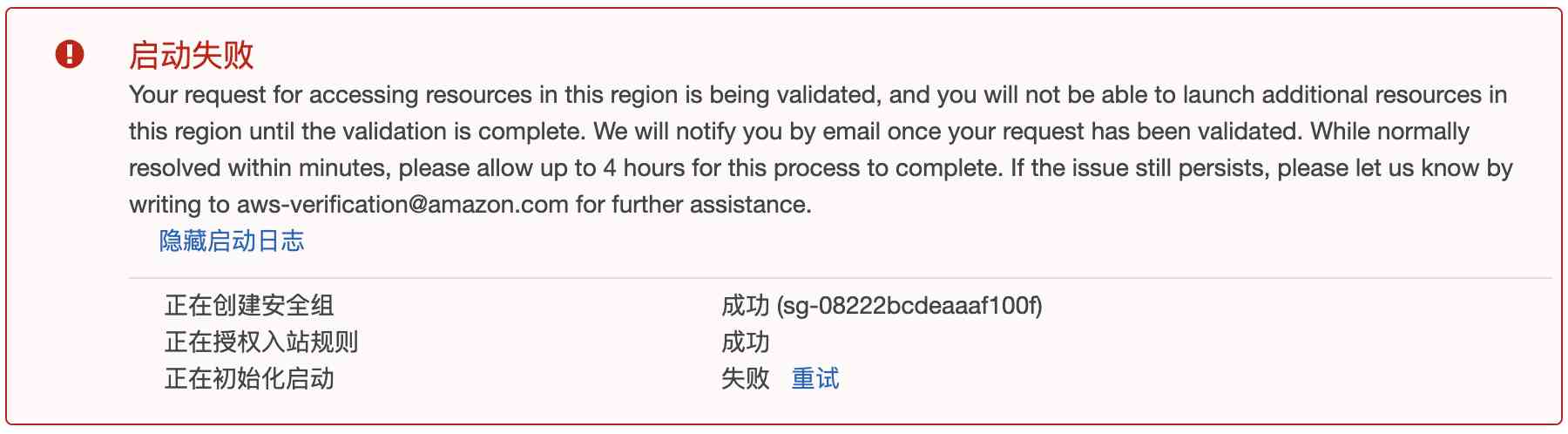
云计算之路-出海记:整一台 aws 免费云服务器

Littlest JupyterHub| 02 使用nbgitpuller分发共享文件

VC6兼容性及打开文件崩溃问题解决
About the promotion of the whole stack of engineers, from the introduction to give up the secret arts, do not click in to have a look?
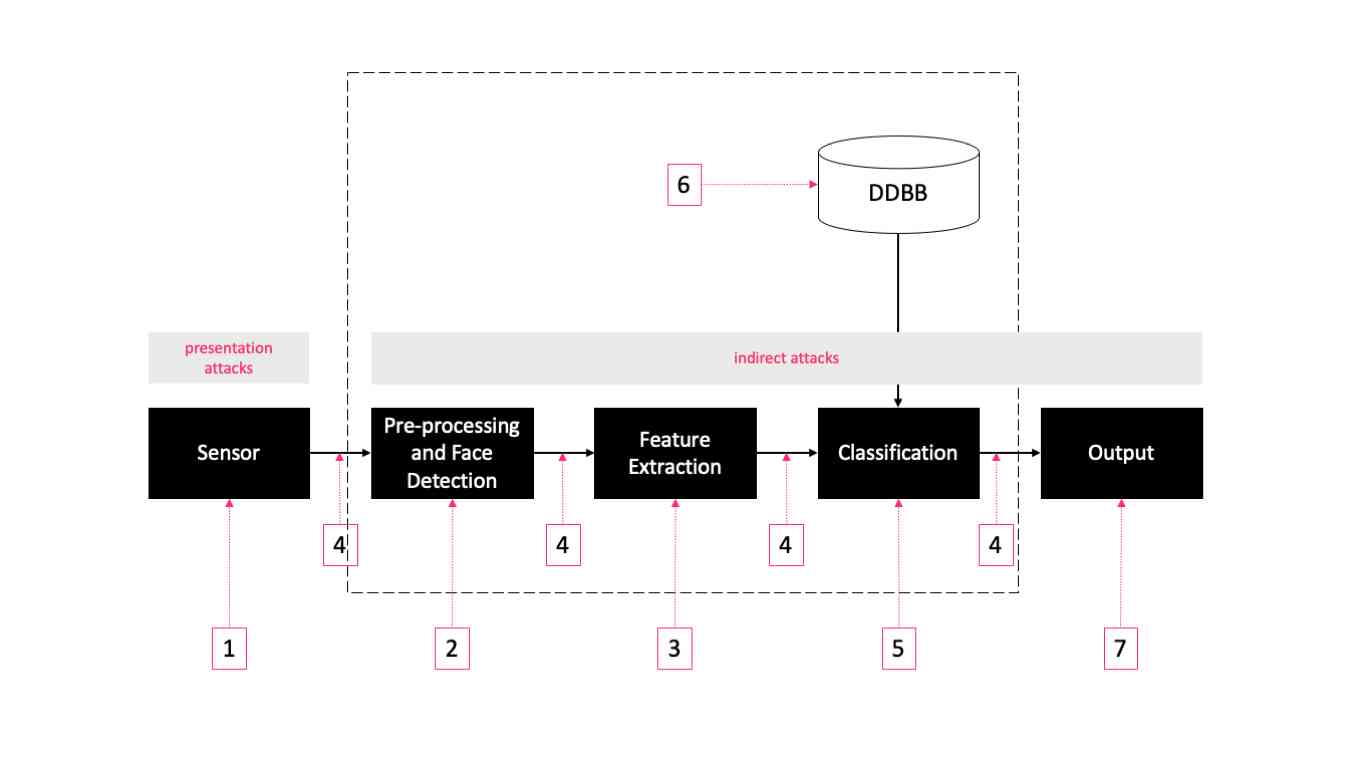
面部识别:攻击类型和反欺骗技术

IOS upload app store error: this action cannot be completed - 22421 solution
随机推荐
nvm
GET,POST,PUT,DELETE,OPTIONS用法与说明
16.文件传输协议、vsftpd服务
Cpp(一) 安装CMake
Everything is 2020, LINQ query you are still using expression tree
Jingtao project day09
0.计算机简史
On the stock trading of leetcode
Download, installation and configuration of Sogou input method in Ubuntu
November 07, 2020: given an array of positive integers, the sum of two numbers equals N and must exist. How to find the two numbers with the smallest multiplication?
What? Your computer is too bad? You can handle these moves! (win10 optimization tutorial)
The software in your host has terminated an established connection. resolvent
See once to understand, graphic single chain table inversion
What kind of technical ability should a programmer who has worked for 1-3 years? How to improve?
C expression tree (1)
Python image recognition OCR
Data transmission of asynchronous serial communication controlled by group bus communication
获取树形菜单列表
GoLand writes a program with template
Using subprocess residue in supervisor and python multiprocessing