当前位置:网站首页>leetcode961. Find the elements repeated N times in the array with length 2n
leetcode961. Find the elements repeated N times in the array with length 2n
2022-07-03 01:57:00 【2021dragon】
Give you an array of integers nums, The array has the following properties :
nums.length == 2*n.numscontain n+1 A different element .numsThere happens to be an element repetition in n Time .
Find and return duplicates n The next element .
Example :
Input :nums = [1, 2, 3, 3]
Output :3
Ideas :
Finding the target element requires two iterations of the array :
- First traversal , Count the number of occurrences of each element .
- Second traversal , Return to appear n Secondary elements , That is, the target element .
The code is as follows :
class Solution {
public:
int repeatedNTimes(vector<int>& nums) {
unordered_map<int, int> countMap;
//1、 First traversal , Count the number of times
for (auto e : nums)
{
countMap[e]++;
}
//2、 Second traversal , Return to appear n Secondary elements
for (auto e : countMap)
{
if (e.second == nums.size() / 2)
return e.first;
}
return -1; // Make sure that the compilation passes ( All paths have return values )
}
};
Explain : According to the question , When executing the code, you must find an occurrence n The second element is returned , This is called execution logic , But when the code is compiled , According to the compilation logic , We must make every logic have a return value , So you need to return an arbitrary value at the end of the code , Its purpose is to make the code compile smoothly , Although we know that the code will not run here to return .
边栏推荐
- Virtual list
- Network security - talking about security threats
- [data mining] task 1: distance calculation
- Network security - firewall
- Rockchip3399 start auto load driver
- Smart management of Green Cities: Digital twin underground integrated pipe gallery platform
- Performance test | script template sorting, tool sorting and result analysis
- 疫情當頭,作為Leader如何進行團隊的管理?| 社區征文
- Answers to ten questions about automated testing software testers must see
- Internal connection query and external connection
猜你喜欢

机器学习笔记(持续更新中。。。)

The technology boss is ready, and the topic of position C is up to you
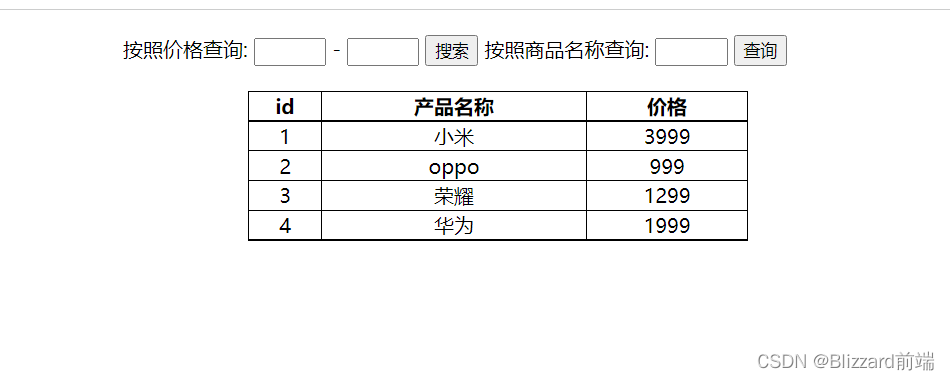
Query product cases - page rendering data
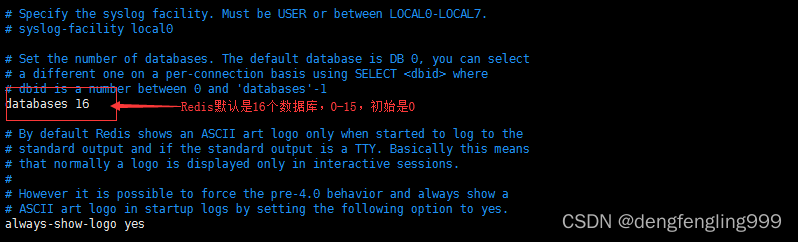
Redis:Redis的简单使用

STM32 - vibration sensor control relay on
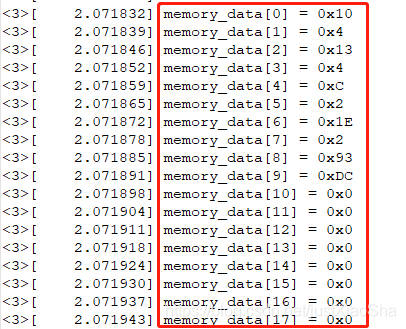
【Camera专题】OTP数据如何保存在自定义节点中
![[North Asia data recovery] data recovery case of raid crash caused by hard disk disconnection during data synchronization of hot spare disk of RAID5 disk array](/img/2a/98400b0d0b5eda1e52abae30746f2b.jpg)
[North Asia data recovery] data recovery case of raid crash caused by hard disk disconnection during data synchronization of hot spare disk of RAID5 disk array

A simple tool for analyzing fgui dependencies

PS去除水印详解
![[camera topic] complete analysis of camera dtsi](/img/cb/d42589fcf0610600c9dc8c7992d4d7.png)
[camera topic] complete analysis of camera dtsi
随机推荐
[AUTOSAR cantp] -2.11-uds diagnostic response frame data segment data padding data filling and data optimization data optimization (Theory + configuration)
Technology sharing | Frida's powerful ability to realize hook functions
Virtual list
可视化yolov5格式数据集(labelme json文件)
小程序开发的部分功能
A 30-year-old software tester, who has been unemployed for 4 months, is confused and doesn't know what to do?
网络安全-中间人攻击
Asian Games countdown! AI target detection helps host the Asian Games!
Learn BeanShell before you dare to say you know JMeter
Modify table structure
Analyzing several common string library functions in C language
[camera topic] turn a drive to light up the camera
[error record] navigator operation requested with a context that does not include a naviga
Network security - scanning and password explosion 2
网络安全-防火墙
微信小程序开发工具 POST net::ERR_PROXY_CONNECTION_FAILED 代理问题
深度学习笔记(持续更新中。。。)
[error record] an error is reported in the fluent interface (no mediaquery widget ancestor found. | scaffold widgets require a mediaquery)
Groovy, "try with resources" construction alternative
Niuniu's ball guessing game (dynamic planning + prefix influence)