当前位置:网站首页>Understand the session, cookie and token at one time, and the interview questions are all finalized
Understand the session, cookie and token at one time, and the interview questions are all finalized
2022-07-07 22:55:00 【Xiaowu knock code】
01、 What are they respectively ?
session:
session In the middle ⽂ The translation is “ conversation ”, When ⽤ User opens a web Should be ⽤ when , And web Server production ⽣⼀ Time session. The server makes ⽤session hold ⽤ The information of the user is temporarily saved on the server ,⽤ Leave ⽹ Post station session Will be destroyed . such ⽤ User information storage ⽅ The formula is relative to cookie It's safer , But session Yes ⼀ A flaw : If web The server Load balancing is done , So ⼀ An operation request arrived at another ⼀ When it comes to servers session Will lose .
cookie:
cookie It is the data stored in the local terminal .cookie By the server ⽣ become , Send it to the browser , Browser handle cookie With kv Save the form to a ⽬ Recorded ⽂ Ben ⽂ In piece , Next ⼀ This request is the same as ⼀⽹ When you stand, you will cookie Send to the server . because cookie It's on the client side , So the browser adds ⼊ 了 ⼀ Some restrictions ensure that cookie Will not be maliciously used to ⽤, Same as Will not take up too much disk space , So for each domain cookie The quantity is limited .
cookie The composition of is : name (key)、 value (value)、 Effective domain (domain)、 route ( Path to domain ,⼀ Set as global :“”)、 Failure time 、 Safety signs ( After designation ,cookie Only in making ⽤SSL Send to server when connected (https)).
token:
token It means “ token ”, yes ⽤ Household ⾝ Validation of copies ⽅ type , The simplest token form :uid(⽤ Huwei ⼀ Of ⾝ Copy identification )、time( Timestamp of current time )、sign( Signature , from token Before ⼏ position + Salt is hashed into ⼀ Fixed length ⼗ Hex string , It can prevent ⽌ Malicious third ⽅ Splicing token Request server ). You can also put constant parameters into the token, Avoid checking the library many times .
02、 What's the relationship between them ?
cookie,session It can be token A way to store .
cookie For data stored locally , When requested, the data will be submitted to the server for verification .
session For memory data stored on the server , As long as the session is not interrupted , Then the data remains valid .
toke Generally speaking, it belongs to token ,cookie,session It is a way of data storage and use , Tokens can be stored in cookie,session, But actually through url Parameters or form parameters can achieve the same effect . But the cost is high for development and maintenance , Once the backend requests to modify parameters , Such use is a headache for modification .
03、 Their essential differences ?
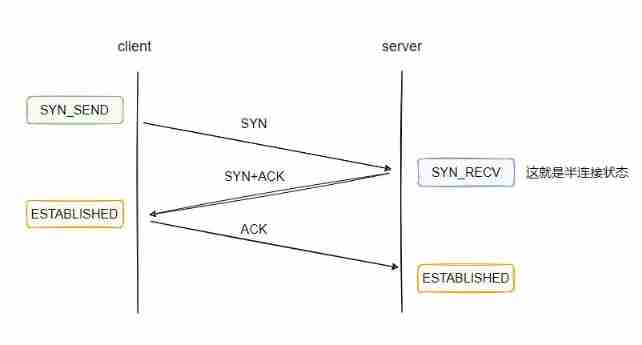
session The way to use is the client cookie Li Cun id, Server side session Save user data , When the client accesses the server , according to id Find user data .
and token The use of is stored in the client id( That is to say token)、 User information 、 Ciphertext , There is nothing on the server , The server has only one piece of encryption code , It is used to judge whether the current encrypted ciphertext is consistent with the ciphertext passed by the client , If it's not consistent , That is, the user data of the client has been tampered , If the same , It means that the user data of the client is normal and correct .
technological process :
session, Register login -> The server will user Deposit in session-> take sessioni In the browser cookie-> Visit again according to cookie Inside sessionid find session Inside user.
token, Register login -> The server generates a based on user information and key token-> take token+user Back to the browser -> When you visit again token+user+ Ciphertext data , The background will be used again user And key generation token, And passed on token Compare , Consistent is correct .
session、cookie、token These concepts often appear in interviews , Because through this concept, you can basically know whether you have any understanding and practical application of network request or permission management .
Finally, thank everyone who reads my article carefully , The following online link is also a very comprehensive one that I spent a few days sorting out , I hope it can also help you in need !
These materials , For those who want to change careers 【 software test 】 For our friends, it should be the most comprehensive and complete war preparation warehouse , This warehouse also accompanied me through the most difficult journey , I hope it can help you ! Everything should be done as soon as possible , Especially in the technology industry , We must improve our technical skills . I hope that's helpful ……
If you don't want to grow up alone , Unable to find the information of the system , The problem is not helped , If you insist on giving up after a few days , You can click the small card below to join our group , We can discuss and exchange , There will be various software testing materials and technical exchanges .
| Click the small card at the end of the document to receive it |
Typing is not easy , If this article is helpful to you , Click a like, collect a hide and pay attention , Give the author an encouragement . It's also convenient for you to find it quickly next time .
Self study recommendation B Stop video :
Zero basis transition software testing : Self taught software testing , Got the byte test post offer, Is the B The best video station !
Advanced automation testing : Huawei has landed , Salary increase 20K,2022 Most suitable for self-study python Automated test tutorial , Spend it yourself 16800 Bought , Free sharing
边栏推荐
- Revit secondary development - Hide occlusion elements
- 【测试面试题】页面很卡的原因分析及解决方案
- 筑起云端 “免疫”屏障,让你的数据有备无患
- Qt Graphicsview图形视图使用总结附流程图开发案例雏形
- Micro service remote debug, nocalhost + rainbow micro service development second bullet
- Debezium series: source code reading snapshot reader
- Revit secondary development - cut view
- 7-18 simple simulation of banking business queue
- What is ADC sampling rate (Hz) and how to calculate it
- Revit secondary development - operation family documents
猜你喜欢
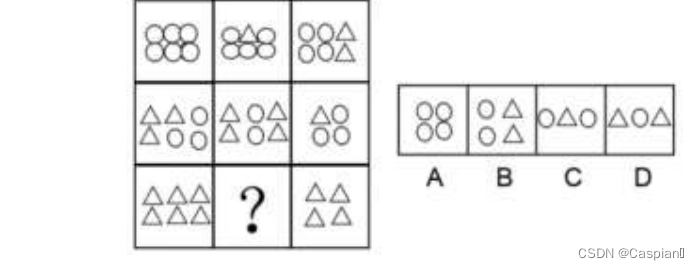
行测-图形推理-8-图群类
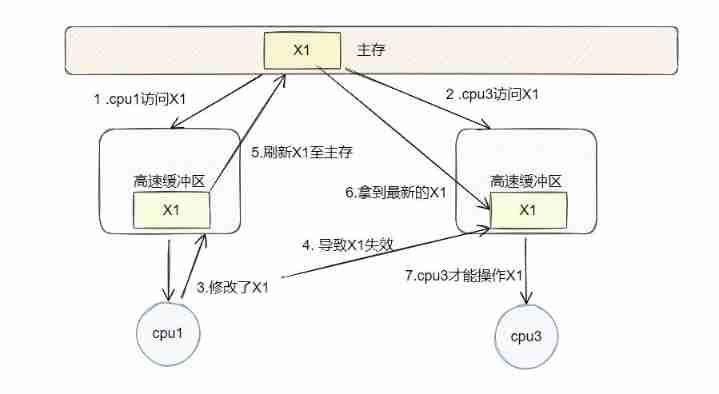
What is fake sharing after filling the previous hole?
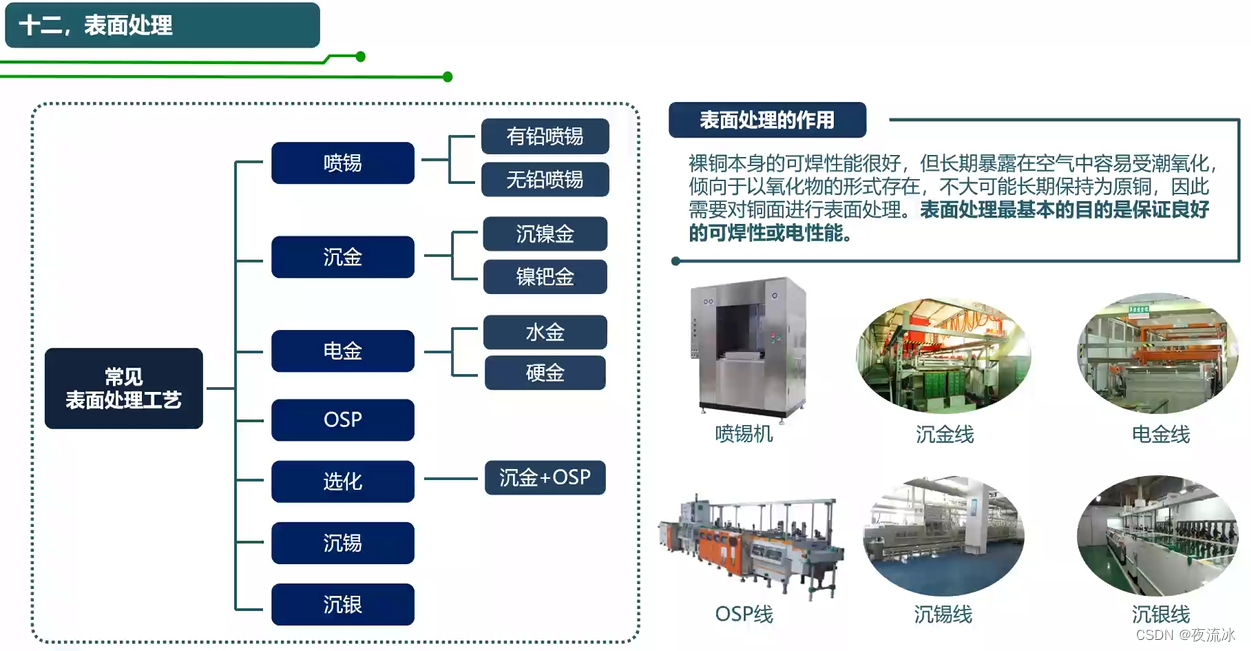
知识点滴 - PCB制造工艺流程
PHP method of obtaining image information

新版代挂网站PHP源码+去除授权/支持燃鹅代抽
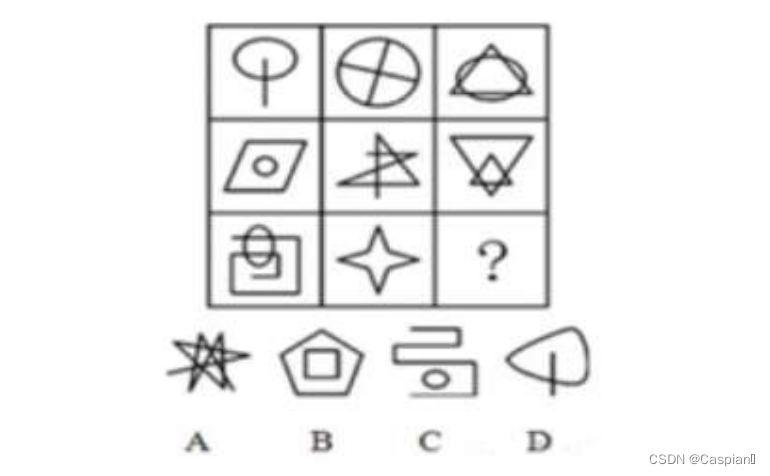
行测-图形推理-9-线条问题类

Microbial Health Network, How to restore Microbial Communities
How to choose the appropriate automated testing tools?
Why is network i/o blocked?
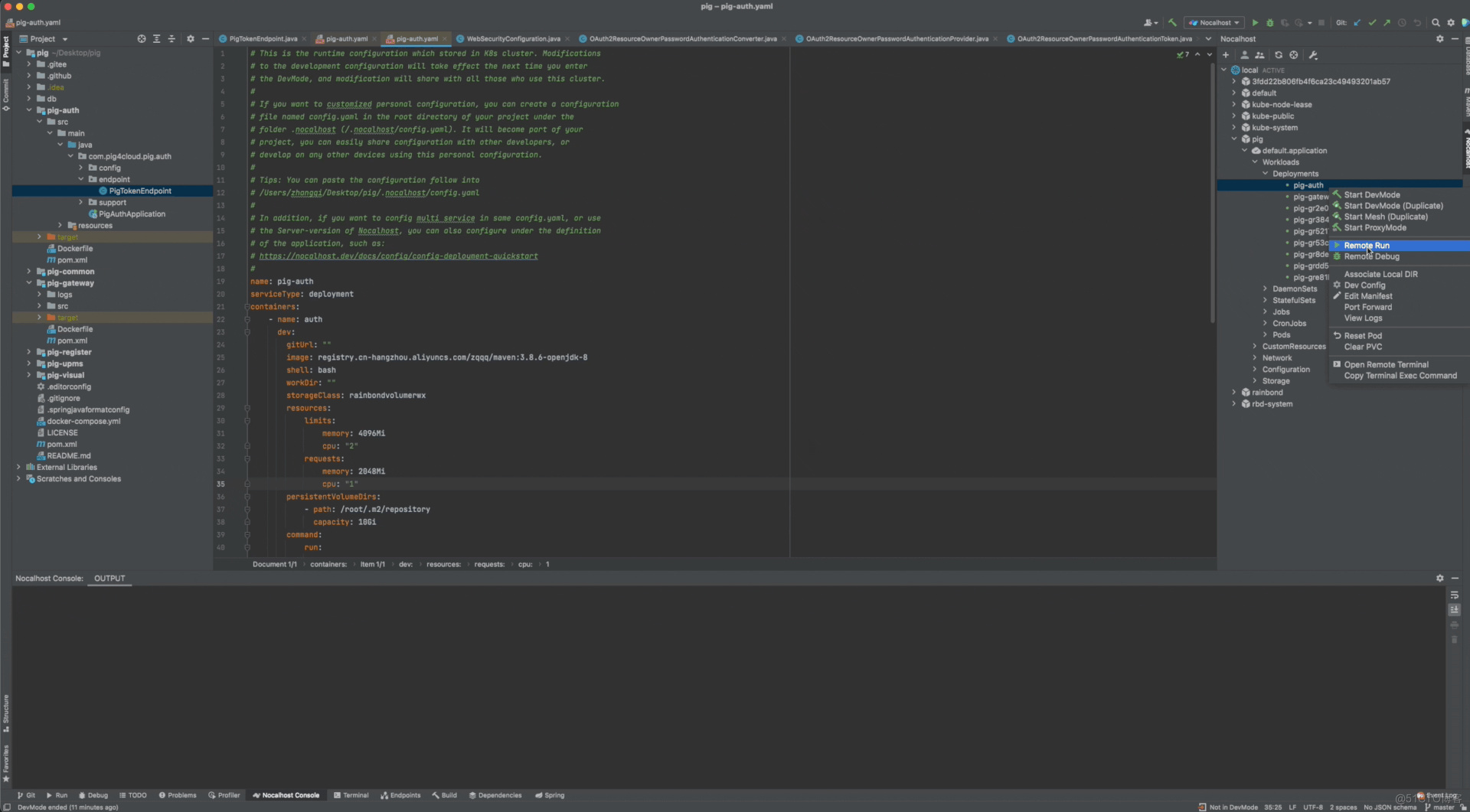
微服务远程Debug,Nocalhost + Rainbond微服务开发第二弹
随机推荐
软件测评中心▏自动化测试有哪些基本流程和注意事项?
Nx10.0 installation tutorial
Redis official ORM framework is more elegant than redistemplate
行测-图形推理-5-一笔画类
行测-图形推理-9-线条问题类
C # Development -- pit encountered in JS intermodulation
Microbial health network, how to restore microbial communities
Sword finger offer 55 - I. depth of binary tree
7-51 combination of two ordered linked list sequences
Typeorm automatically generates entity classes
数字化转型:五个步骤推动企业进步
This experimental syntax requires enabling the parser plugin: ‘optionalChaining‘
XMIND mind mapping software sharing
Debezium系列之:支持 mysql8 的 set role 語句
Knowledge drop - PCB manufacturing process flow
Revit secondary development - get the project file path
Unity local coordinates and world coordinates
一次搞明白 Session、Cookie、Token,面试问题全稿定
Sword finger offer 63 Maximum profit of stock
Select sort (illustration +c code)