当前位置:网站首页>11. Users, groups, and permissions (1)
11. Users, groups, and permissions (1)
2022-07-01 18:55:00 【51CTO】
1、Linux Security model
3A(authentication、authorization、accouting aduition): authentication 、 to grant authorization 、 Audit
user
Linux Each user in is through User ID(UID) To represent only
Administrators root: uid by 0
Ordinary users :1-60000 Automatically assigned
System users :1-499(centos6) 1-999(centos7) It is used for the daemon to obtain resources and allocate permissions
The logged in user :500+(centos6) 1000+(centos7) Interactive login for ordinary users
User group
Linux You can add one or more users to a user group , User groups also have GID (group id)
Administrators group root:0
The normal group :
System group :1-499(centos6) 1-999(centos7) It is used for the daemon to obtain resources and allocate permissions
The normal group :500+(centos6) 1000+(centos7) For users
The relationship between users and groups
The primary group of users : Users must belong to one and only one main group , By default, when creating a user, a group with the same name as the user name will be automatically created , As the primary group of users , Because there is only one user in this group , Also a private group ;
Additional group : A user can belong to more than one additional group ;

Security context
Linux Security context context: Running program , Process , Run as the process initiator , The permission of a process to read resources depends on the identity of the process operator ;
2、 User and group profiles
User profile
/etc/passwd ( User information , primary unix System user passwords are stored here ) /etc/shadow( Store user password related information )
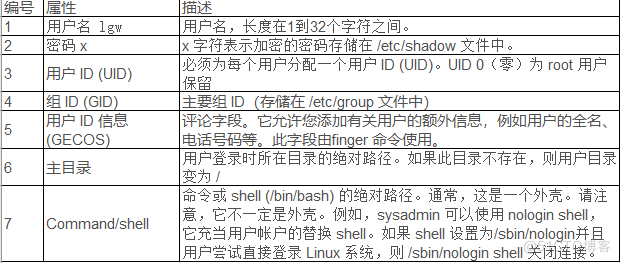
/etc/passwd File format

/etc/shadow File format

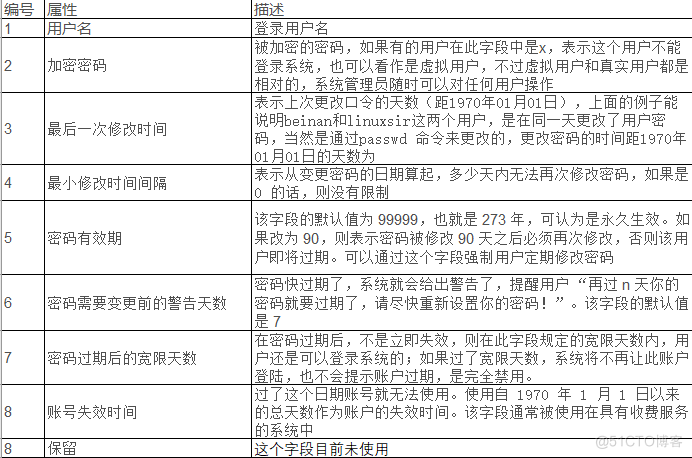
encryption algorithm : It is generally used sha512, Algorithm of changing password :authconfig --passalgo=sha256 --update
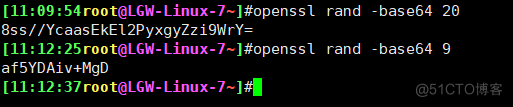
Random password generation :

group File format
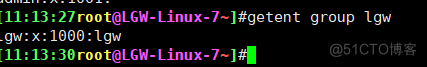
The name of the group Group password group id The current group has been added to the list of users
gshadow File format
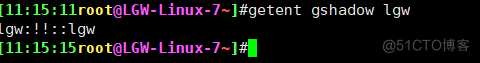
The name of the group Group password Group administrator list List of users with the current group as an additional group : Multiple users are separated by commas ;
File operations (pwck grpck)
Detect whether there are errors in user and group configuration files
边栏推荐
- 解决方案:可以ping别人,但是别人不能ping我
- R language uses the DOTPLOT function of epidisplay package to visualize the frequency of data points in different intervals in the form of point graph, and uses PCH parameters to customize the shape o
- 研究了11种实时聊天软件,我发现都具备这些功能…
- Technology implementation and Architecture Practice
- Why do independent website sellers start to do social media marketing? The original customer conversion rate can be improved so much!
- Write it down once Net travel management background CPU Explosion Analysis
- Create your own NFT collections and publish a Web3 application to show them (Introduction)
- 12 data dimensioning processing methods
- Three.js学习-相机Camera的基本操作(了解向)
- 斯坦福、Salesforce|MaskViT:蒙面视觉预训练用于视频预测
猜你喜欢

Relational database management system of easyclick
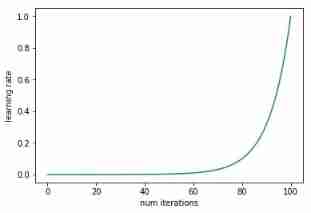
How to find the optimal learning rate

ACM mm 2022 video understanding challenge video classification track champion autox team technology sharing

How to use the low code platform of the Internet of things for personal settings?

Leetcode203 remove linked list elements

搭建一个通用监控告警平台,架构上需要有哪些设计
华为云专家详解GaussDB(for MySQL)新特性

Mysql database of easyclick

关于企业中台规划和 IT 架构微服务转型

Lumiprobe Lumizol RNA 提取试剂解决方案
随机推荐
Leetcode-21 combines two ordered linked lists
AI 训练速度突破摩尔定律;宋舒然团队获得RSS 2022最佳论文奖
斯坦福、Salesforce|MaskViT:蒙面视觉预训练用于视频预测
Technology implementation and Architecture Practice
540. Single element in ordered array / 1684 Count the number of consistent strings
OpenAI|视频预训练 (VPT):基于观看未标记的在线视频的行动学习
Image acquisition and playback of coaxpress high speed camera based on pxie interface
每周推薦短視頻:警惕“現象”與“問題”相互混淆
Introduction to easyclick database
Implementation of converting PCM file to WAV
实现一个Prometheus exporter
AI training speed breaks Moore's law; Song shuran's team won the RSS 2022 Best Paper Award
How to realize the bottom layer of read-write lock in go question bank 16
lefse分析
6款红黄黑榜摄像头评测:谁最安全?谁画质好?从此让你不再踩雷
About enterprise middle office planning and it architecture microservice transformation
bean的生命周期核心步骤总结
如何在自有APP内实现小程序实现连麦直播
Weekly recommended short videos: be alert to the confusion between "phenomena" and "problems"
Clean up system cache and free memory under Linux