当前位置:网站首页>On December 8th, 2020, the memory of marketing MRC application suddenly increased, resulting in system oom
On December 8th, 2020, the memory of marketing MRC application suddenly increased, resulting in system oom
2022-07-07 08:57:00 【bboyzqh】
List of articles
background
12.08 At noon on the th mrc Applications suddenly appear, memory continues to rise , From 67% Rise to 85% about ( Monitoring is as follows ), Fortunately, the rising process is relatively slow , A decisive restart solved the problem . The process of solving and analyzing problems is as follows .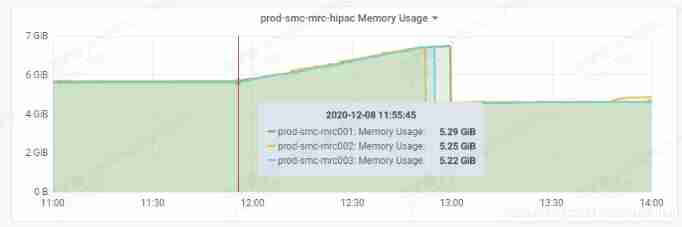
Problem solving process
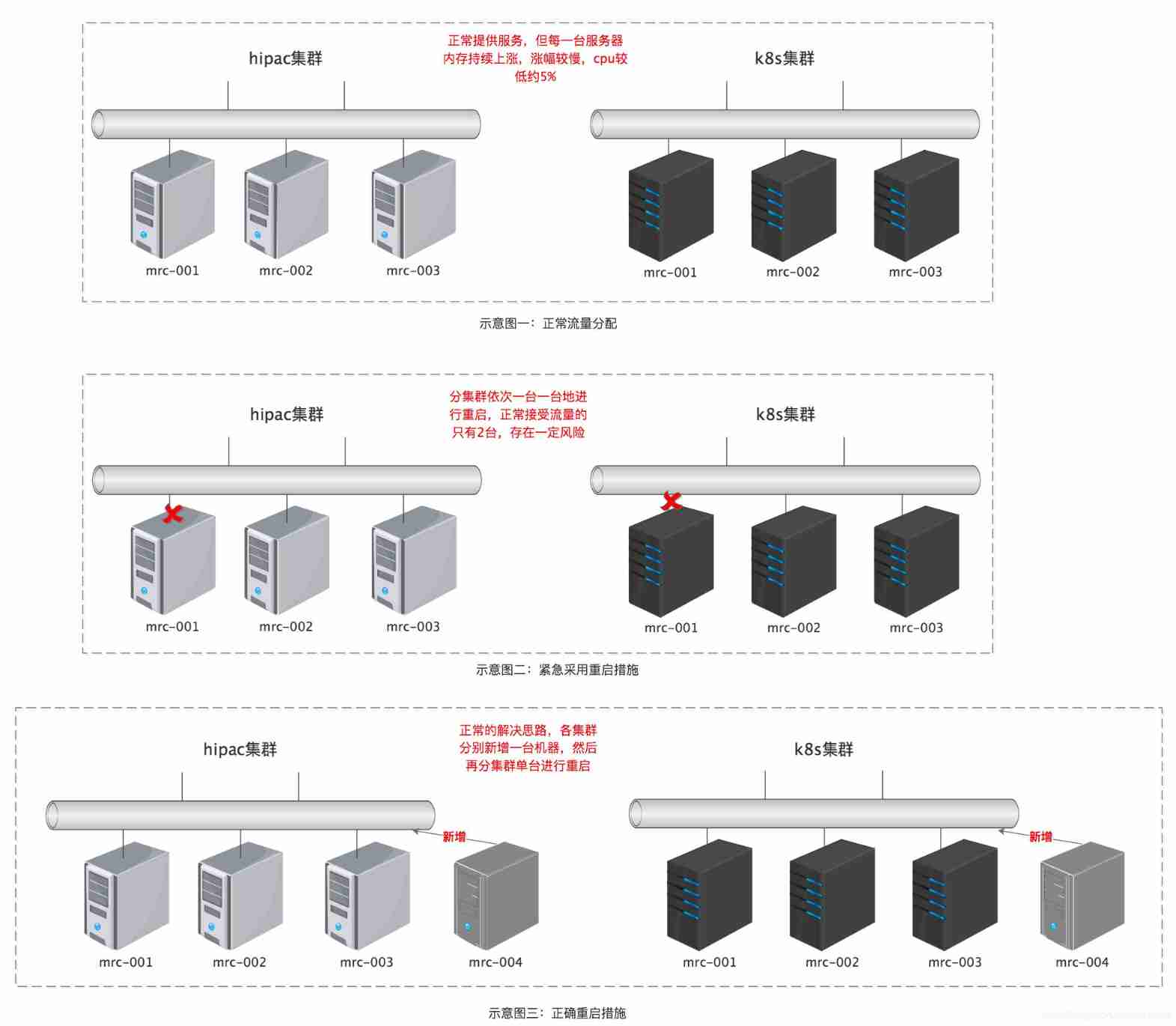
mrc It's the bottom application of marketing , Main partial rule calculation , common 6 Taiwan machine (2 Next cluster , And cluster traffic is isolated from each other , Such as the upper layer hipc Cluster traffic will not be requested to k8s Cluster machines ),6 At the same time, the memory keeps rising , Refer to sketch 1 .
Because it was a big promotion at noon that day , Considering that there are only 3 Taiwan machine , I'm afraid that in the process of restarting one , The other two can't stand the flow of big promotion , At first, I didn't dare to consider a single restart , After a short period of time, the decision was made taking into account the cpu Only 5% about , The worst worry is that memory can't take care of it all of a sudden , If frequent gc May affect the normal traffic access , So prepare for the worst : Restart decisively ( Remove traffic before restart , meanwhile dump Memory for subsequent analysis ), As a result, there was no problem , Refer to sketch 2 . The whole process is as follows :
- The target restarts the machine for traffic removal , Adjust to restart the machine dubbo The weight of 0 that will do , because dump Memory processes are memory consuming operations , Server may appear feign death phenomenon, affect normal call , So we need to remove the traffic .
- Force the target machine to restart once full gc, The purpose is to reclaim the normal memory object occupation , To prevent the normal memory occupation and the influence of real memory leak objects , The impact analysis , You can use the following command :
- dump Next target machine memory , The order is as follows :
jmap -histo:live 13 ( Trigger full gc)
or
jmap -dump:live,file=dump_001.bin 13 ( Trigger full gc, When triggered, put dump_001.bin File deletion )
or
jcmd 13 GC.run ( Trigger young gc)
- Use IBMAnalyzer( perhaps jdk Self contained jvisualvm Tools or mat Tools ) Yes dump File analysis is enough
jmap -dump:format=b,file=dumpFile 13
After the event, the best plan is to add a new one to Tongyun maintenance mrc machine , And then restart each one , Refer to sketch 3 .
Post analysis
After the event dump Document analysis , As it involves specific business, I will not elaborate on it , Just describe the conclusion : Because that day mrc Configuring the shadow library results in . The root cause is druid Threads that monitor shadow library configuration will not exit with the end of the pressure test , stay mrc After pressure testing, the thread creation is triggered without restart , Lead to mrc Application memory keeps rising .
Welcome to WeChat official account. : Fang Chen's blog 
边栏推荐
- Vagrant failed to mount directory mount: unknown filesystem type 'vboxsf'
- Greenplum 6.x common statements
- Un salaire annuel de 50 W Ali P8 vous montrera comment passer du test
- How to realize sliding operation component in fast application
- Original collection of hardware bear (updated on June 2022)
- Platformization, a fulcrum of strong chain complementing chain
- Tronapi wave field interface - source code without encryption - can be opened twice - interface document attached - package based on thinkphp5 - detailed guidance of the author - July 6, 2022 - Novice
- RuntimeError: Calculated padded input size per channel: (1 x 1). Kernel size: (5 x 5). Kernel size c
- Simulation volume leetcode [general] 1609 Parity tree
- MySQL主从延迟的解决方案
猜你喜欢
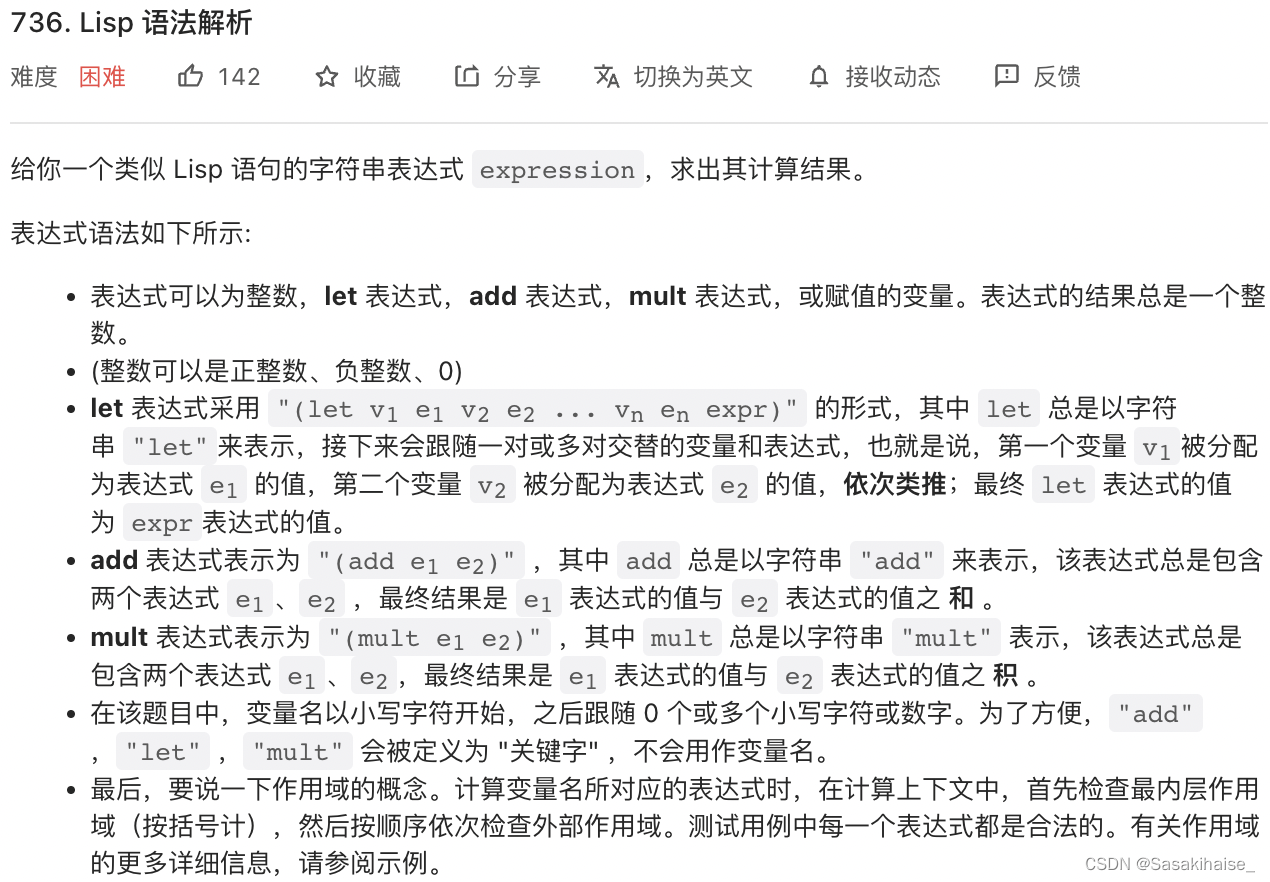
LeetCode 736. LISP syntax parsing

Nanjing commercial housing sales enabled electronic contracts, and Junzi sign assisted in the online signing and filing of housing transactions
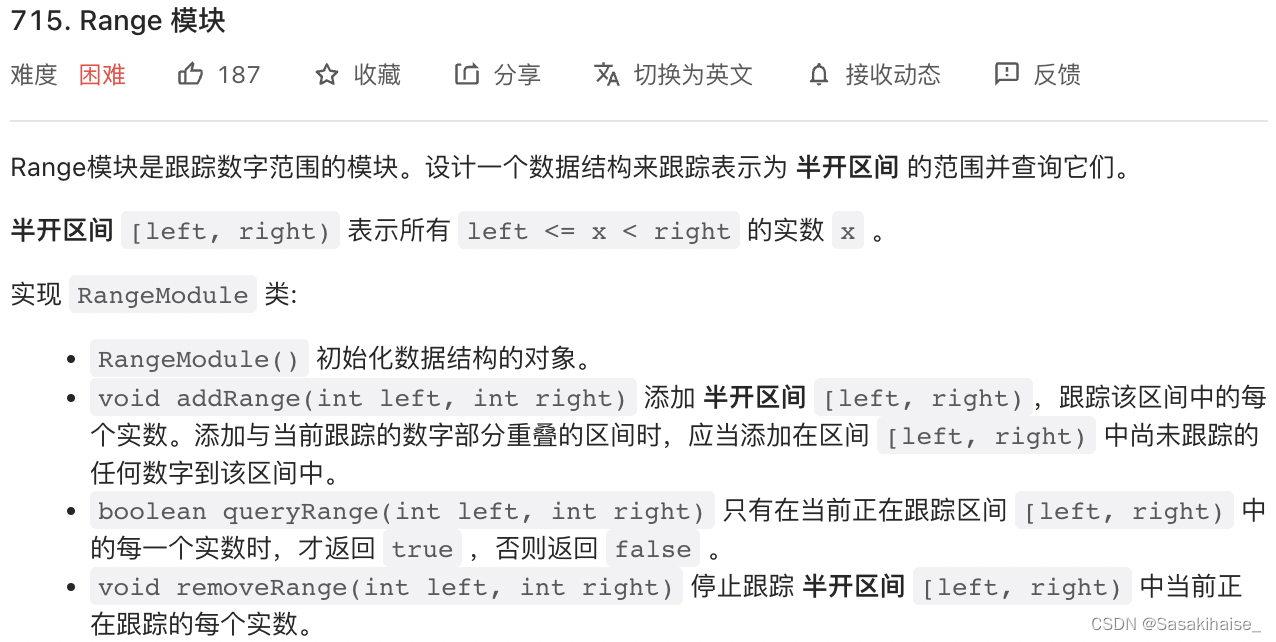
LeetCode 715. Range 模块

Image segmentation in opencv
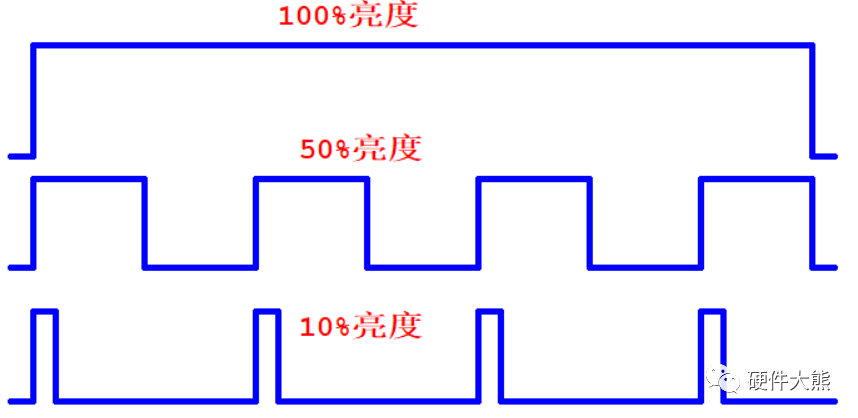
LED模拟与数字调光

Markdown编辑器Editor.md插件的使用
Count sort (diagram)
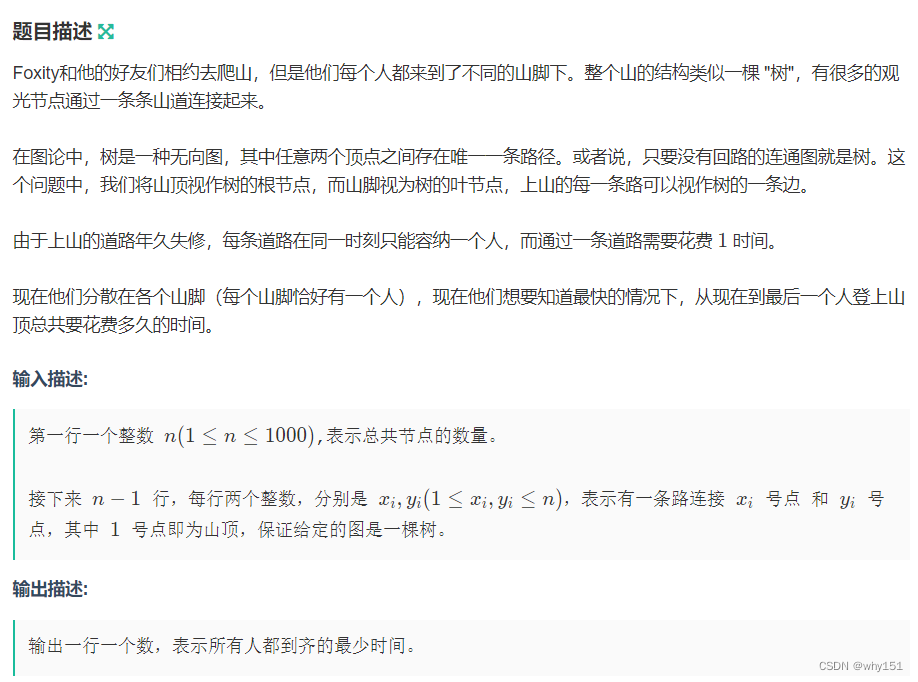
Mountaineering team (DFS)

Three series of BOM elements
![[MySQL] detailed explanation of trigger content of database advanced](/img/6c/8aad649e4ba1160db3aea857ecf4a1.png)
[MySQL] detailed explanation of trigger content of database advanced
随机推荐
2022-07-06 unity core 9 - 3D animation
Newly found yii2 excel processing plug-in
C language for calculating the product of two matrices
MySQL partition explanation and operation statement
NCS Chengdu Xindian interview experience
Database storage - table partition
cmake命令行使用
【istio简介、架构、组件】
Image segmentation in opencv
对API接口或H5接口做签名认证
Uniapp wechat applet monitoring network
Speaking of a software entrepreneurship project, is there anyone willing to invest?
Simulation volume leetcode [general] 1705 The maximum number of apples to eat
2022-06-30 unity core 8 - model import
LeetCode 736. Lisp 语法解析
阿里p8手把手教你,自动化测试应该如何实现多线程?赶紧码住
ncs成都新电面试经验
ESP32-ULP协处理器低功耗模式RTC GPIO中断唤醒
How to count the number of project code lines
Greenplum6.x重新初始化