当前位置:网站首页>Leetcode 剑指 Offer 59 - II. 队列的最大值
Leetcode 剑指 Offer 59 - II. 队列的最大值
2022-07-06 01:10:00 【May Hacker】
题目
请定义一个队列并实现函数 max_value 得到队列里的最大值,要求函数max_value、push_back 和 pop_front 的均摊时间复杂度都是O(1)。
若队列为空,pop_front 和 max_value 需要返回 -1
示例 1:
输入:
["MaxQueue","push_back","push_back","max_value","pop_front","max_value"]
[[],[1],[2],[],[],[]]
输出: [null,null,null,2,1,2]
示例 2:
输入:
["MaxQueue","pop_front","max_value"]
[[],[],[]]
输出: [null,-1,-1]
限制:
1 <= push_back,pop_front,max_value的总操作数 <= 10000
1 <= value <= 10^5
来源:力扣(LeetCode)
链接:https://leetcode.cn/problems/dui-lie-de-zui-da-zhi-lcof
著作权归领扣网络所有。商业转载请联系官方授权,非商业转载请注明出处。
思路
- 特别注意如果用Java做本题要熟悉Deque和Queue的API,对于Deque来说,能当队列也能当栈,本题会当队列来用,所以查看尾部元素应该用PeekLast(),而不是Peek(),因为Peek()相当于PeekFirst()
- 额外维护一个保存最大值的双向队列,从队头到队尾,应该是逆序的,即当队尾元素小于当前要进队的元素时,要while弹出去这些小元素,从而保证是逆序的
- 出栈的时候,只需要判断一下两个队列的队头是否相等,相等则把这个逆序双向队列也弹出。
Java AC
class MaxQueue {
private Queue<Integer> q = new LinkedList<>();
private Deque<Integer> dq = new LinkedList<>();
public MaxQueue() {
}
public int max_value() {
if(q.isEmpty()){
return -1;
}
return dq.peekFirst();
}
public void push_back(int value) {
q.add(value);
while(!dq.isEmpty()&& dq.peekLast()<value){
dq.removeLast();
}
dq.add(value);
}
public int pop_front() {
if(q.isEmpty()){
return -1;
}
int res = q.poll();
if(dq.peekFirst()==res){
dq.removeFirst();
}
return res;
}
}
/** * Your MaxQueue object will be instantiated and called as such: * MaxQueue obj = new MaxQueue(); * int param_1 = obj.max_value(); * obj.push_back(value); * int param_3 = obj.pop_front(); */
边栏推荐
- Getting started with devkit
- The growth path of test / development programmers, the problem of thinking about the overall situation
- How to extract MP3 audio from MP4 video files?
- MIT doctoral thesis | robust and reliable intelligent system using neural symbol learning
- Three methods of script about login and cookies
- The value of applet containers
- Interview must brush algorithm top101 backtracking article top34
- [groovy] compile time meta programming (AST syntax tree conversion with annotations | define annotations and use groovyasttransformationclass to indicate ast conversion interface | ast conversion inte
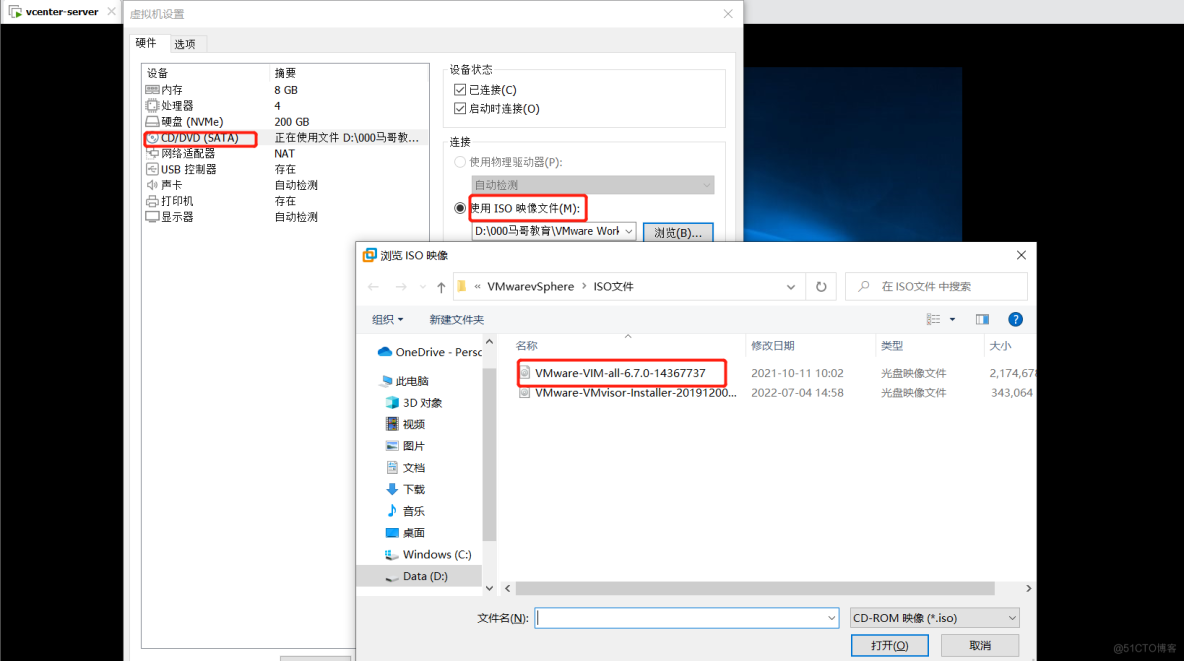
- VMware Tools installation error: unable to automatically install vsock driver
- Study diary: February 13, 2022
猜你喜欢
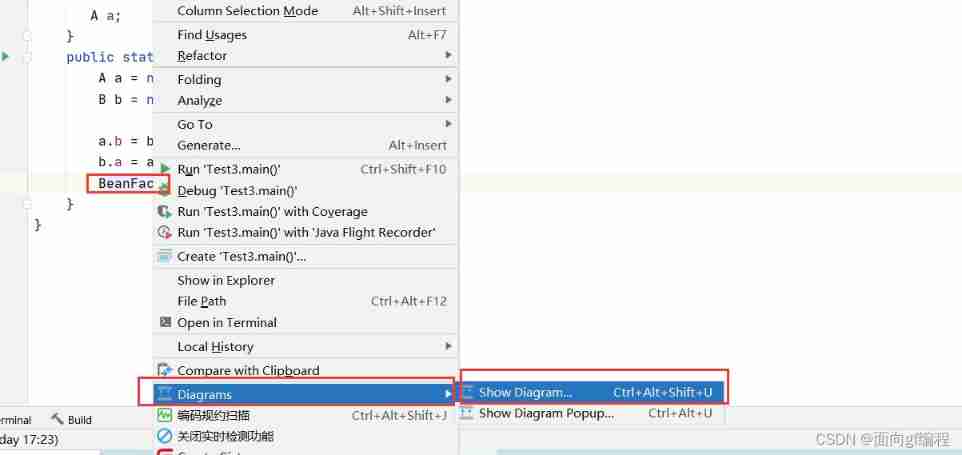
View class diagram in idea
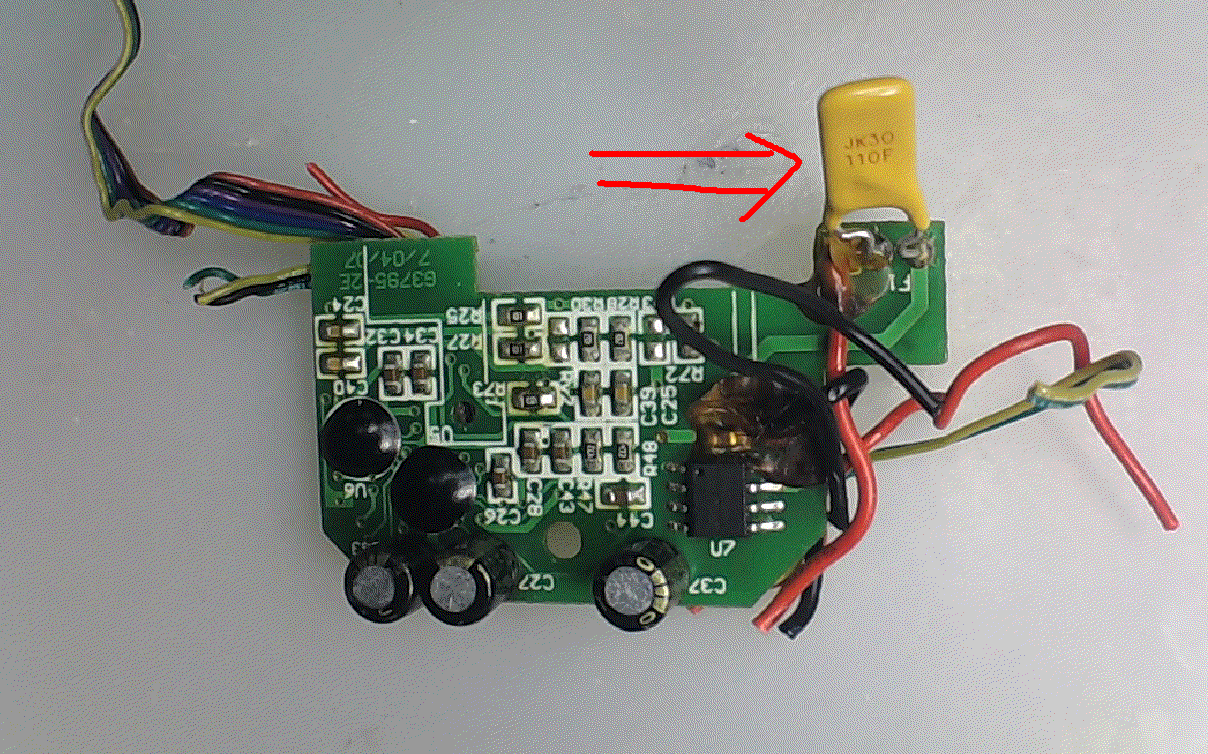
可恢复保险丝特性测试
Intensive learning weekly, issue 52: depth cuprl, distspectrl & double deep q-network
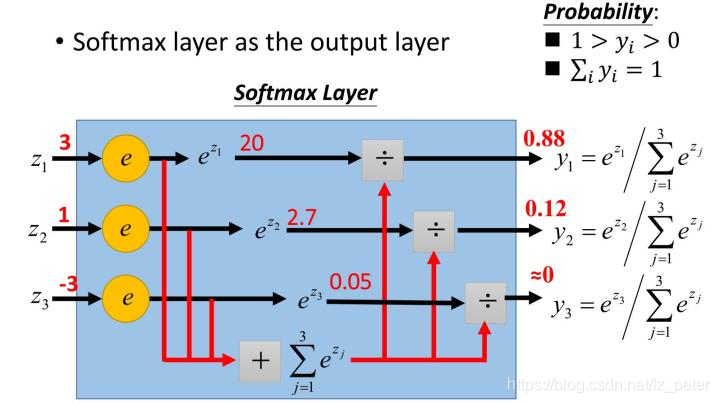
关于softmax函数的见解
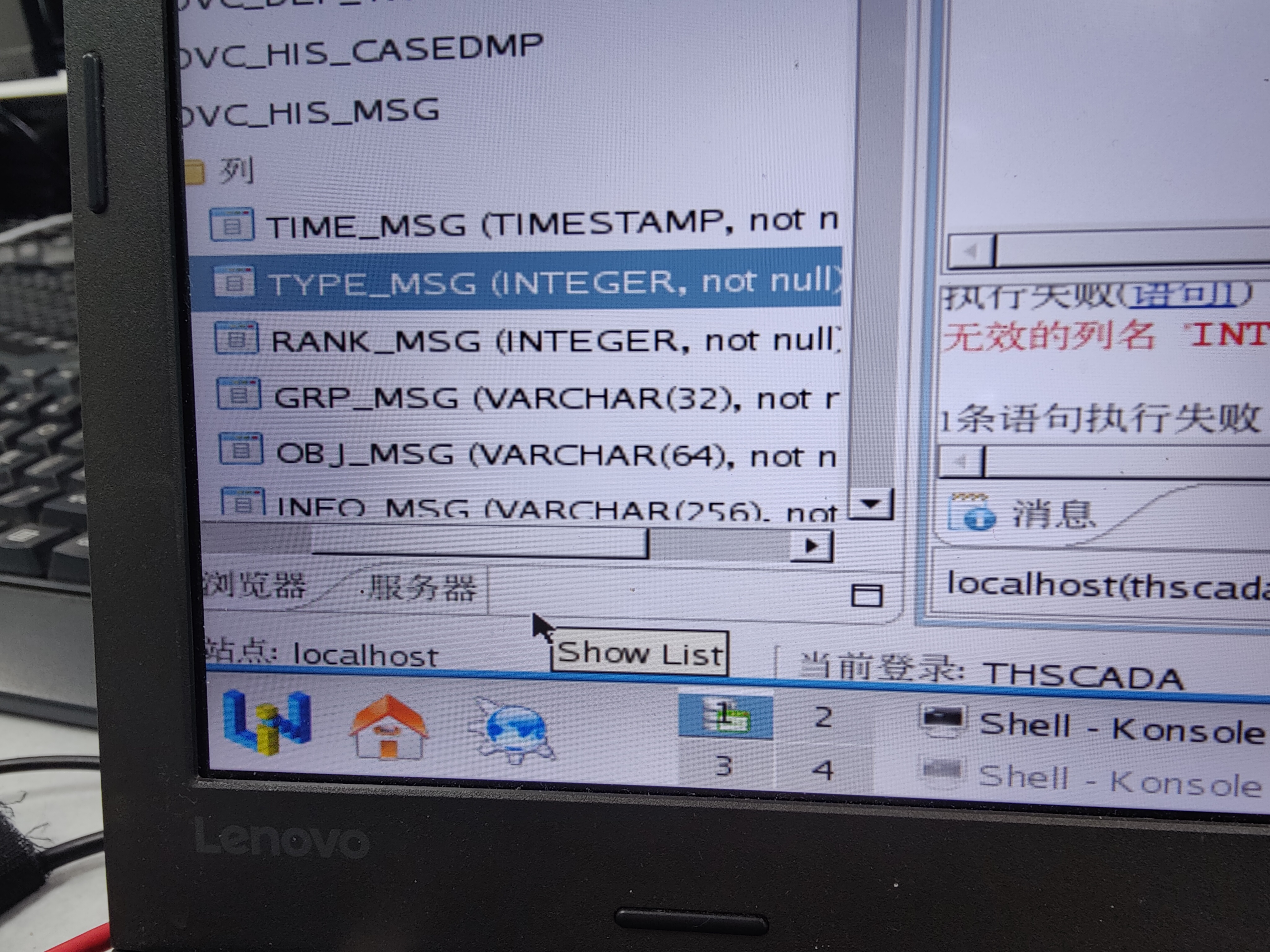
Who knows how to modify the data type accuracy of the columns in the database table of Damon
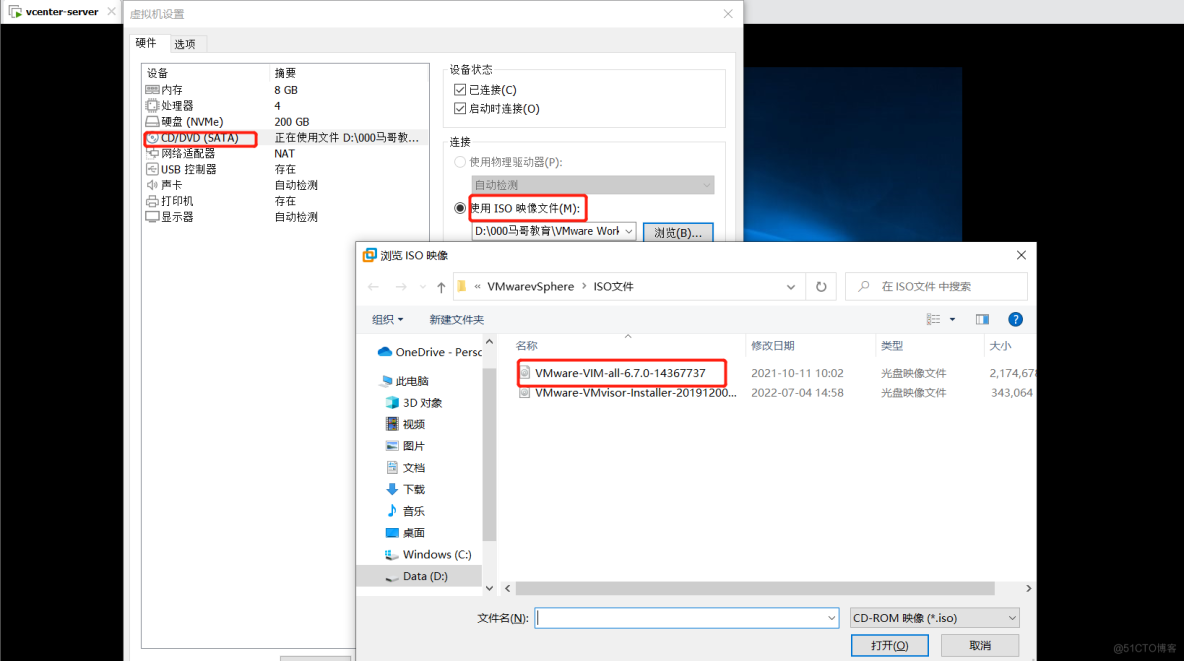
vSphere实现虚拟机迁移

Four commonly used techniques for anti aliasing
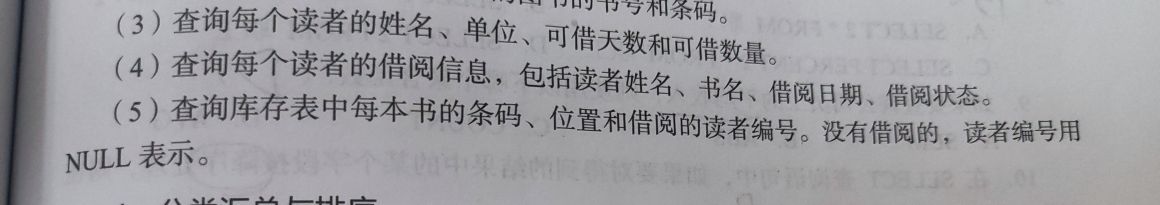
Questions about database: (5) query the barcode, location and reader number of each book in the inventory table
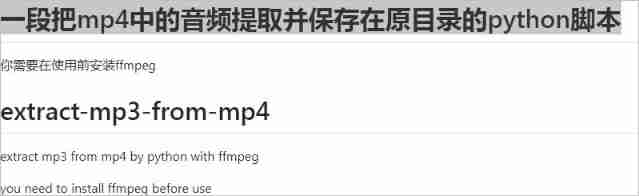
How to extract MP3 audio from MP4 video files?
VSphere implements virtual machine migration
随机推荐
图解网络:TCP三次握手背后的原理,为啥两次握手不可以?
新手入门深度学习 | 3-6:优化器optimizers
Introduction to robotics I. spatial transformation (1) posture, transformation
Construction plan of Zhuhai food physical and chemical testing laboratory
synchronized 和 ReentrantLock
KDD 2022 | EEG AI helps diagnose epilepsy
[groovy] compile time metaprogramming (compile time method injection | method injection using buildfromspec, buildfromstring, buildfromcode)
Finding the nearest common ancestor of binary search tree by recursion
Zhuhai's waste gas treatment scheme was exposed
基於DVWA的文件上傳漏洞測試
MYSQL---查询成绩为前5名的学生
程序员搞开源,读什么书最合适?
Intensive learning weekly, issue 52: depth cuprl, distspectrl & double deep q-network
cf:C. The Third Problem【关于排列这件事】
Recommended areas - ways to explore users' future interests
Arduino hexapod robot
What is the most suitable book for programmers to engage in open source?
[groovy] XML serialization (use markupbuilder to generate XML data | set XML tag content | set XML tag attributes)
WordPress collection plug-in automatically collects fake original free plug-ins
可恢复保险丝特性测试