当前位置:网站首页>Alpha Beta Pruning in Adversarial Search
Alpha Beta Pruning in Adversarial Search
2022-07-02 07:23:00 【Drizzle】
Alpha Beta Pruning in Adversarial Search
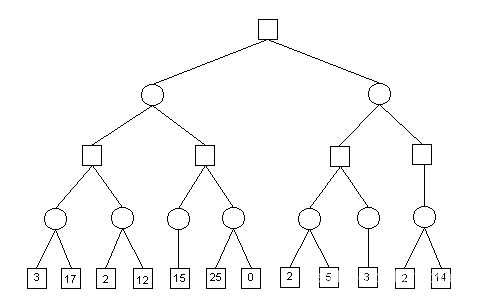
Minimax Implementation
def max-value(state):
initialize v = -∞
for each successor of state:
v = max(v, min-value(successor))
return v
def min-value(state):
initialize v = +∞
for each successor of state:
v = min(v, max-value(successor))
return v
V ( s ) = m a x ( V ( s ′ ) ) s ′ ∈ s u c c e s s o r ( s ) V(s) = max(V(s')) s' \in successor(s) V(s)=max(V(s′))s′∈successor(s)
V ( s ′ ) = m i n ( V ( s ) ) s ∈ s u c c e s s o r ( s ′ ) V(s') = min(V(s)) s \in successor(s') V(s′)=min(V(s))s∈successor(s′)
Alpha Beta Pruning
General configuration (MIN version)
We’re computing the MIN-VALUE at some node n
We’re looping over n’s children
n’s estimate of the childrens’ min is dropping
Who cares about n’s value? MAX
Let α \alpha α be the best value that MAX can get at any choice point along the current path from the root
If n becomes worse than α \alpha α, MAX will avoid it, so we can stop considering n’s other children (it’s already bad enough that it won’t be played)
MAX version is symmetric
Examples
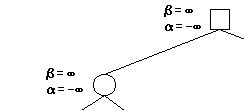
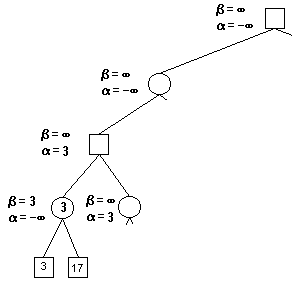
To start with, we know nothing about the bounds, so we set α = − ∞ , β = ∞ \alpha = - \infty, \beta = \infty α=−∞,β=∞.

Then we passing along the bounds to the child, child’s child…
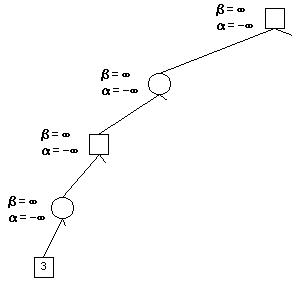
Now we reach at the level: depth of 4. We run our evaluation functions here.
An evaluation function is like:
Ideal function: returns the actual minimax value of the position
In practice: typically weighted linear sum of features: E v a l ( s ) = w 1 f 1 ( s ) + ⋅ ⋅ ⋅ + w n f n ( s ) Eval(s) = w_1f_1(s) + \cdot\cdot\cdot + w_nf_n(s) Eval(s)=w1f1(s)+⋅⋅⋅+wnfn(s).
We get value 3, since this is a min node, we now know the minmax value must be less than or equal to 3, thus, we set β = 3 \beta = 3 β=3.
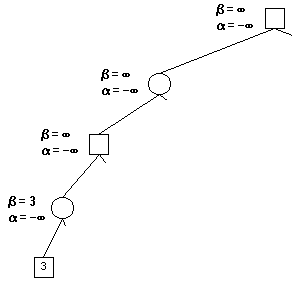
Next child in depth 4 is value 17, while 17 > 3, we ignore this child.
All children handled, we return to depth 3. we have β = 3 \beta = 3 β=3 here, so we can set α = 3 \alpha = 3 α=3 at the depth 2 node.

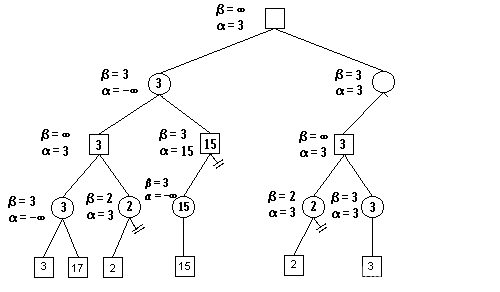
We pass along the bounds of depth2 to next child of depth3.

At this moment, we get α = 3 a n d β = 2 , α > β \alpha = 3 \space and \space \beta = 2, \alpha > \beta α=3 and β=2,α>β.
If these values are to change, children values would be greater than 3 and less than 2, which is impossible. We can prune any children and return.
We do these steps recursively, we will reach this:
Some pictures and ideas comes from h t t p s : / / w w w . c s . u c l a . e d u / https://www.cs.ucla.edu/ https://www.cs.ucla.edu/.
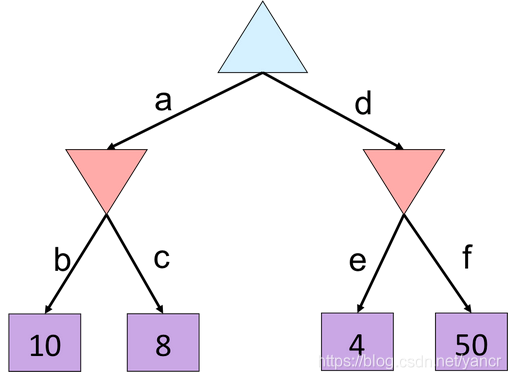
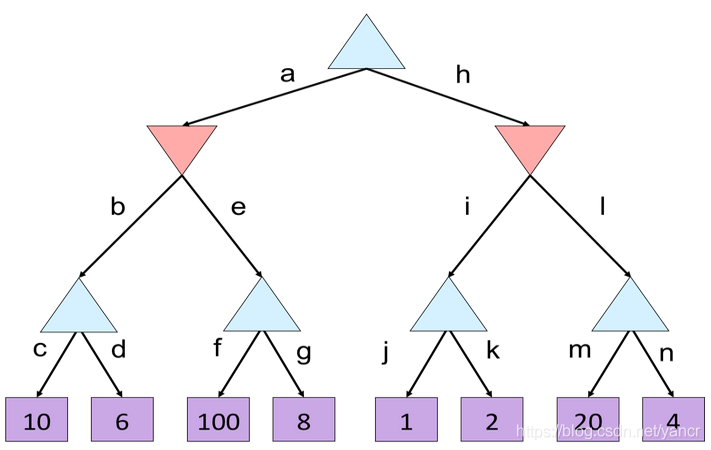
Two Quiz
notice: I do not have answers.
边栏推荐
- Module not found: Error: Can't resolve './$$_gendir/app/app.module.ngfactory'
- 外币记账及重估总账余额表变化(下)
- 【信息检索导论】第七章搜索系统中的评分计算
- ssm垃圾分类管理系统
- CSRF attack
- CONDA creates, replicates, and shares virtual environments
- One field in thinkphp5 corresponds to multiple fuzzy queries
- ORACLE 11G利用 ORDS+pljson来实现json_table 效果
- MapReduce concepts and cases (Shang Silicon Valley Learning Notes)
- RMAN增量恢复示例(1)-不带未备份的归档日志
猜你喜欢

Sparksql data skew
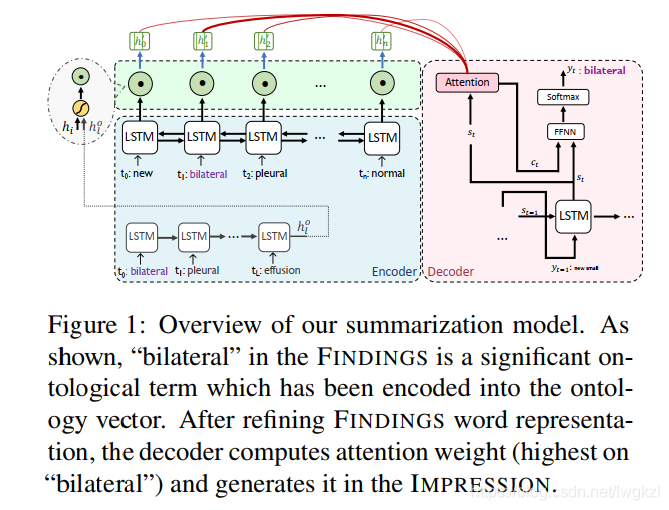
【MEDICAL】Attend to Medical Ontologies: Content Selection for Clinical Abstractive Summarization
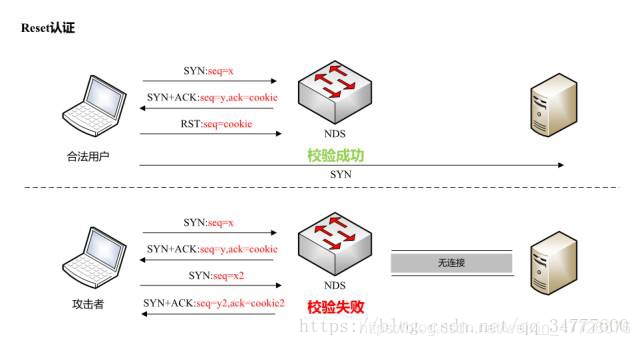
TCP攻击

Error in running test pyspark in idea2020

【信息检索导论】第七章搜索系统中的评分计算
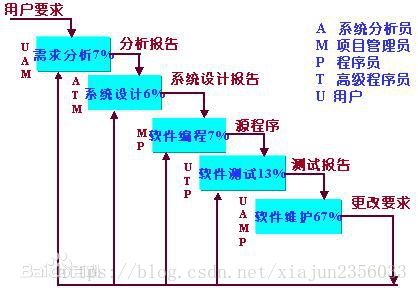
Agile development of software development pattern (scrum)
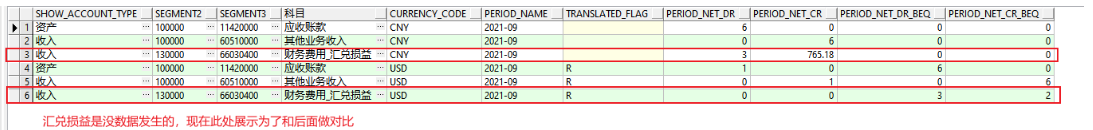
外币记账及重估总账余额表变化(下)

Explain in detail the process of realizing Chinese text classification by CNN
![[medical] participants to medical ontologies: Content Selection for Clinical Abstract Summarization](/img/24/09ae6baee12edaea806962fc5b9a1e.png)
[medical] participants to medical ontologies: Content Selection for Clinical Abstract Summarization

Oracle EBS database monitoring -zabbix+zabbix-agent2+orabbix
随机推荐
[Bert, gpt+kg research] collection of papers on the integration of Pretrain model with knowledge
【调参Tricks】WhiteningBERT: An Easy Unsupervised Sentence Embedding Approach
【Ranking】Pre-trained Language Model based Ranking in Baidu Search
[medical] participants to medical ontologies: Content Selection for Clinical Abstract Summarization
spark sql任务性能优化(基础)
DNS攻击详解
Oracle RMAN semi automatic recovery script restore phase
Conda 创建,复制,分享虚拟环境
2021-07-17c /cad secondary development creation circle (5)
Network security -- intrusion detection of emergency response
RMAN增量恢复示例(1)-不带未备份的归档日志
Ding Dong, here comes the redis om object mapping framework
ORACLE 11G利用 ORDS+pljson来实现json_table 效果
ORACLE EBS DATAGUARD 搭建
oracle-外币记账时总账余额表gl_balance变化(上)
Oracle apex Ajax process + dy verification
Data warehouse model fact table model design
[introduction to information retrieval] Chapter II vocabulary dictionary and inverted record table
Sqli labs customs clearance summary-page1
MySQL has no collation factor of order by