当前位置:网站首页>[network security interview question] - how to penetrate the test file directory through
[network security interview question] - how to penetrate the test file directory through
2022-07-06 02:43:00 【LexSaints】
4.6. Directory traversal
4.6.1. brief introduction
Directory traversal ( Also known as directory traversal /directory traversal/path traversal) By using ../ And so on directory control sequence or file absolute path to access any file and directory stored on the file system , Especially the application source code 、 The configuration file 、 Important system files, etc .
4.6.2. Attack load
4.6.2.1. URL Parameters
../..\..;/
4.6.2.2. Nginx Off by Slash
https://vuln.site.com/files../
4.6.2.3. UNC Bypass
\\localhost\c$\windows\win.ini
4.6.3. Filter around
Single replacement
...//
- URL code
16 position Unicode code
\u002e
Super long UTF-8 code
\%e0%40%ae
4.6.4. defense
In the process of file operation API front , User input should be filtered . Whitelist can be used under strong rules , Only alphanumeric characters are allowed .
If the rule allows more characters , It is best to use the current operating system path normalization function to normalize the path , To filter , Finally, make relevant calls .
4.6.5. Reference link
- Directory traversal by portswigger
- Path Traversal by OWASP
- path normalization
- Breaking Parser Logic: Take Your Path Normalization Off and Pop 0days Out defcon
Recommended reading
【 Resource Recommendation 】
Special system for penetration test
- kali-linux-e17-2019.1a-amd64.iso System image
- kali-linux-e17-2019.1a-amd64.iso System image _kalilinux Mirror image -Linux Document resources -CSDN download
- kali-linux-2018.4-amd64 operating system
- kali-linux-2018.4-amd64 operating system _amdkalilinux-Linux Document resources -CSDN download
- manjaro-xfce-17.1.7-stable-x86_64.iso System image
- manjaro-xfce-17.1.7-stable-x86_64.iso System image _manjaro Image download ,manjaro System download -Linux Document resources -CSDN download
- WiFi Special infiltration system nst-32-11992.x86_64.iso Operating system image
- nst-32-11992.x86_64.iso Operating system image .zip_ Explanation and actual combat of common password cracking tools -Linux Document resources -CSDN download
- Parrot-security-4.1_amd64.iso Operating system image
- Parrot-security-4.1_amd64.iso Operating system image _ParrotSecurity-Linux Document resources -CSDN download
- manjaro-xfce-17.1.7-stable-x86_64 operating system
- manjaro-xfce-17.1.7-stable-x86_64 operating system _manjaroxfce Installation tutorial -Linux Document resources -CSDN download
- cyborg-hawk-linux-v-1.1 operating system
- cyborg-hawk-linux-v-1.1 operating system _cyborghawk Virtual machine installation tutorial -Linux Document resources -CSDN download
Penetration test related tools
- Practical column of penetration test
- 【kali Commonly used tools 】 Online behavior monitoring tool
- Internet behavior tools _ Explanation and actual combat of common password cracking tools - Network security document resources -CSDN download
- 【kali Commonly used tools 】 Caught tools Charles Windows64 position Free version
- Caught tools CharlesWindows64 Bit free version _ Explanation and actual combat of common password cracking tools - Network monitoring document resources -CSDN download
- 【kali Commonly used tools 】 Graphic printing tool stamp.zip
- Graphic printing tool stamp.zip_intext:LexSaints- Manufacturing document resources -CSDN download
- 【kali Commonly used tools 】brutecrack Tools [WIFIPR Chinese version ] And wpa/wpa2 Dictionaries
- brutecrack Tools [WIFIPR Chinese version ] And wpa/wpa2 Dictionaries _wifipr course - Other document resources -CSDN download
- 【kali Commonly used tools 】EWSA 5.1.282- Bag breaking tools
- 【kali Commonly used tools 】EWSA5.1.282- Bag breaking tools _kali Bag running tool - Manage software document resources -CSDN download
- 【kali Commonly used tools 】Realtek 8812AU KALI Network card driver and installation tutorial
- 【kali Commonly used tools 】Realtek8812AUKALI Network card driver and installation tutorial _kalirtl8812au,kali install 8812au drive - Network device document resources -CSDN download
- 【kali Commonly used tools 】 Wireless signal search tool _kali to update
- 【kali Commonly used tools 】 Wireless signal search tool _kali to update _kali to update - Internet document resources -CSDN download
- 【kali Commonly used tools 】inssider Signal test software _kali Commonly used tools
- 【kali Commonly used tools 】inssider Signal test software _kali Commonly used tools - Network management software document resources -CSDN download
- 【kali Commonly used tools 】MAC Address modification tool Protect the terminal from exposure
- 【kali Commonly used tools 】MAC The address modification tool protects the terminal from exposure _mac Modifier -Linux Document resources -CSDN download
- 【kali Commonly used tools 】 Script management tools php and jsp page Receive command parameters Execute... On the server side
- Script management tools php and jsp The page receives command parameters and executes them on the server side _intext:LexSaints- Network security document resources -CSDN download
- Java Realize photos GPS location 【 Full script 】
- ReadPicExif.zip-Java Document resources -CSDN download
- Python Realize photos GPS location 【 Full script 】
- python Locate the exact location of the photo, complete code script _ How to locate the location through photos -Python Document resources -CSDN download
- The goddess forgot the photo album password python20 Line code open 【 Full script 】
- The goddess forgot the photo album password python20 Line code open .py_keepalive_timeout-Python Document resources -CSDN download
- python Modify the background color of the certificate 、 size 、 background 、 Cutout 【 Complete source code 】
- python Modify the background color of the certificate 、 size 、 background 、 Cutout 【 Complete source code 】_python Change the color of the certificate -Python Document resources -CSDN download
python actual combat
- 【python actual combat 】 Ex girlfriend wedding ,python Crack the wedding scene WIFI, Changed the name to
- 【python actual combat 】 Encrypted from my ex girlfriend “520 happy .pdf“, I use python After cracking , But found
- 【python actual combat 】 Last night, , I use python Help the little sister next door P ID Photo Selfie , And found that ...
- 【python actual combat 】 My girlfriend worked overtime in the middle of the night and took a selfie python Boyfriend uses 30 Line of code found the amazing secret
- 【python actual combat 】python you TM Too skinny —— Just so 30 One line of code can record every move of the keyboard
- 【python actual combat 】 I forgot the password of the goddess album , I only use Python Yes 20 Line code ~~~
【pygame Development practice development 30 example Complete source code 】
【pygame Game development column , Get the full source code + course 】
- Come and learn together pygame Well Game development 30 example ( Two )—— Tower defense game
- Come and learn together pygame Well Game development 30 example ( Four )—— Tetris games
- Practical column of penetration test
- Windows AD/Exchange Management column
- Linux High performance server architecture
- PowerShell Automation column
CSDN Official learning recommendation ↓ ↓ ↓
- CSDN Out of Python Full stack knowledge map , too strong , I recommend it to you !

边栏推荐
- 2.11 simulation summary
- Network Security Learning - Web vulnerabilities (Part 1)
- I changed the driver to 5.1.35, but it is still the same error. I can succeed even now, but I will report this every time I do an SQL operation
- Structural theme model (I) STM package workflow
- [Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 14
- MySQL winter vacation self-study 2022 11 (8)
- MySQL winter vacation self-study 2022 11 (5)
- Universal crud interface
- [Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 19
- 2345文件粉碎,文件强力删除工具无捆绑纯净提取版
猜你喜欢
Building the prototype of library functions -- refer to the manual of wildfire
![[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 14](/img/c5/dde92f887e8e73d7db869fcddc107f.jpg)
[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 14
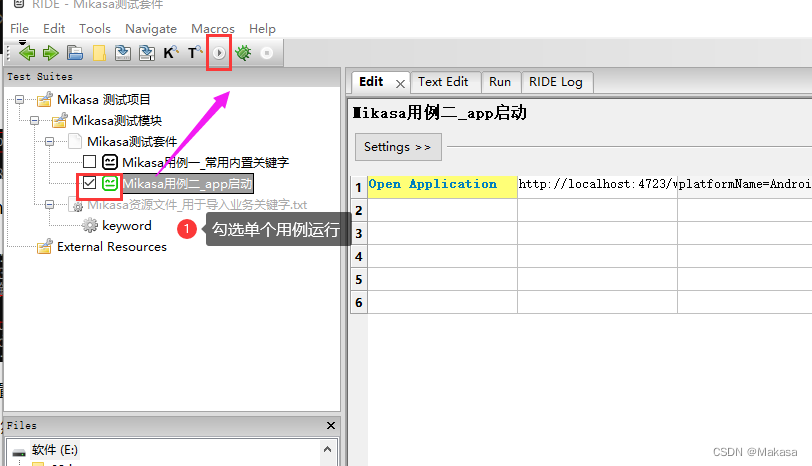
Introduction to robotframework (II) app startup of appui automation
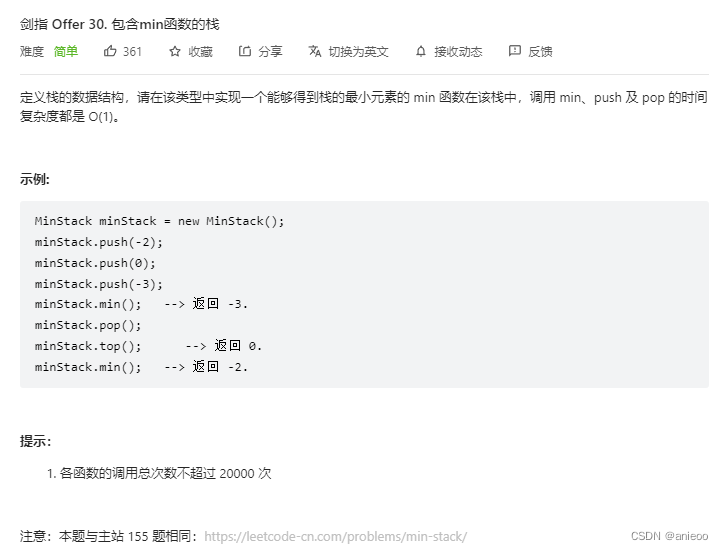
Sword finger offer 30 Stack containing min function
![[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 7](/img/44/1861f9016e959ed7c568721dd892db.jpg)
[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 7
![[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 6](/img/38/51797fcdb57159b48d0e0a72eeb580.jpg)
[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 6
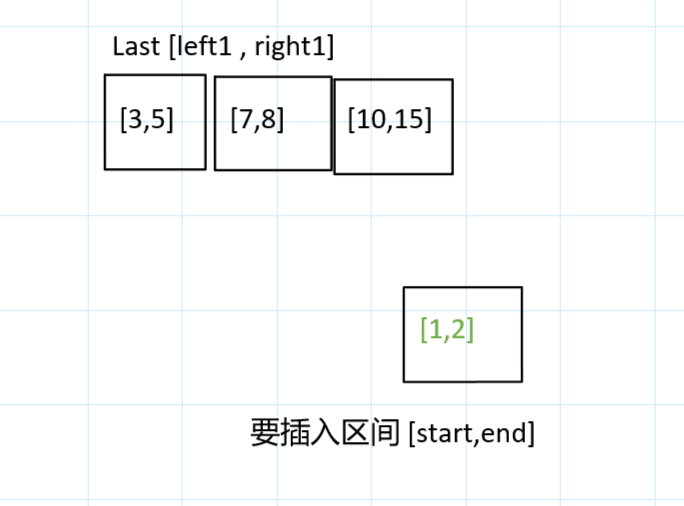
力扣今日题-729. 我的日程安排表 I
The third level of C language punch in
![[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 8](/img/16/33f5623625ba817e6e022b5cb7ff5d.jpg)
[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 8
![[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 18](/img/1a/94ef8be5c06c2d1c52fc8ce7f03ea7.jpg)
[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 18
随机推荐
[Digital IC manual tearing code] Verilog asynchronous reset synchronous release | topic | principle | design | simulation
Which ecology is better, such as Mi family, graffiti, hilink, zhiting, etc? Analysis of five mainstream smart brands
RobotFramework入门(一)简要介绍及使用
[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 14
Advanced technology management - what is the physical, mental and mental strength of managers
"Hands on learning in depth" Chapter 2 - preparatory knowledge_ 2.3 linear algebra_ Learning thinking and exercise answers
[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 12
Redis cluster deployment based on redis5
2345 file shredding, powerful file deletion tool, unbound pure extract version
球面透镜与柱面透镜
高数_向量代数_单位向量_向量与坐标轴的夹角
2345文件粉碎,文件强力删除工具无捆绑纯净提取版
[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 24
Master data management theory and Practice
How to accurately identify master data?
Bigder:34/100 面试感觉挺好的,没有收到录取
数据准备工作
[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 20
Ue4- how to make a simple TPS role (II) - realize the basic movement of the role
2.12 simulation