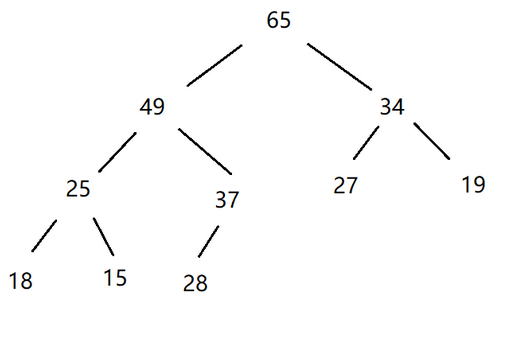
当前位置:网站首页>2.7 binary tree, post order traversal - [FBI tree]
2.7 binary tree, post order traversal - [FBI tree]
2022-07-02 12:33:00 【I boiled the night white_】
List of articles
Title Description

Input description
The first line is an integer N(0<=N<=10)
The second line is a length of 2N Of “01” strand .
Output description
Output a string , namely FBI The subsequent traversal sequence of the tree .
I/o sample
Input :
3
10001011
Output :
IBFBBBFIBFIIIFF
The final code
1. c/c++
#include <bits/stdc++.h>
using namespace std;
char s[2000],tree[280000]; //tree[] Full binary tree
// First, the leaf node has a value , Then determine the value of the parent node according to the value of the leaf node
void build_FBI(int k,int left,int right)
{
// Reach the leaf node
if(left==right)
{
if(s[right]=='1') tree[k]='I';
else tree[k]='B';
return;
}
int mid=(left+right)/2; // Split in two
build_FBI(2*k,left,mid); // Recursive left half
build_FBI(2*k+1,mid+1,right); // Recursive right half
if(tree[2*k]=='B' && tree[2*k+1]=='B') // Both left and right sons B
tree[k]='B';
else if(tree[2*k]=='I'&&tree[2*k+1]=='I') // Both left and right sons I
tree[k]='I';
else tree[k]='F';
}
void postorder (int v){
// After the sequence traversal
if(tree[2*v])
postorder (2*v);
if(tree[2*v+1])
postorder (2*v+1);
printf("%c",tree[v]);
}
int main(){
int n;
scanf("%d",&n);
scanf("%s",s+1);
build_FBI(1,1,strlen(s+1));
// Post order traversal output
postorder(1);
}
2. java
3. python
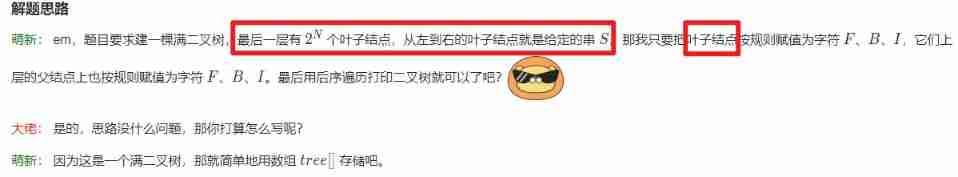
Process understanding

边栏推荐
- 字符串回文hash 模板题 O(1)判字符串是否回文
- Record the range of data that MySQL update will lock
- Day12 control flow if switch while do While guessing numbers game
- Anxiety of a 211 programmer: working for 3 years with a monthly salary of less than 30000, worried about being replaced by fresh students
- Post request body content cannot be retrieved repeatedly
- Initial JDBC programming
- 【工控老马】西门子PLC Siemens PLC TCP协议详解
- Anti shake throttle
- CDA数据分析——Excel数据处理的常见知识点归纳
- Differences between nodes and sharding in ES cluster
猜你喜欢
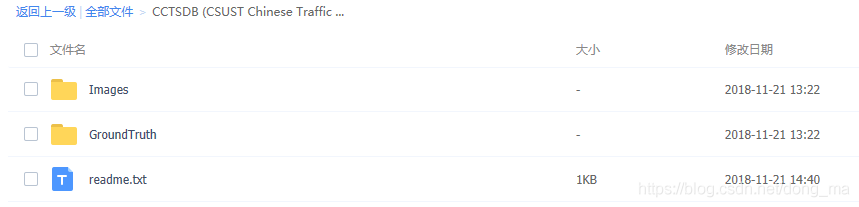
China traffic sign detection data set
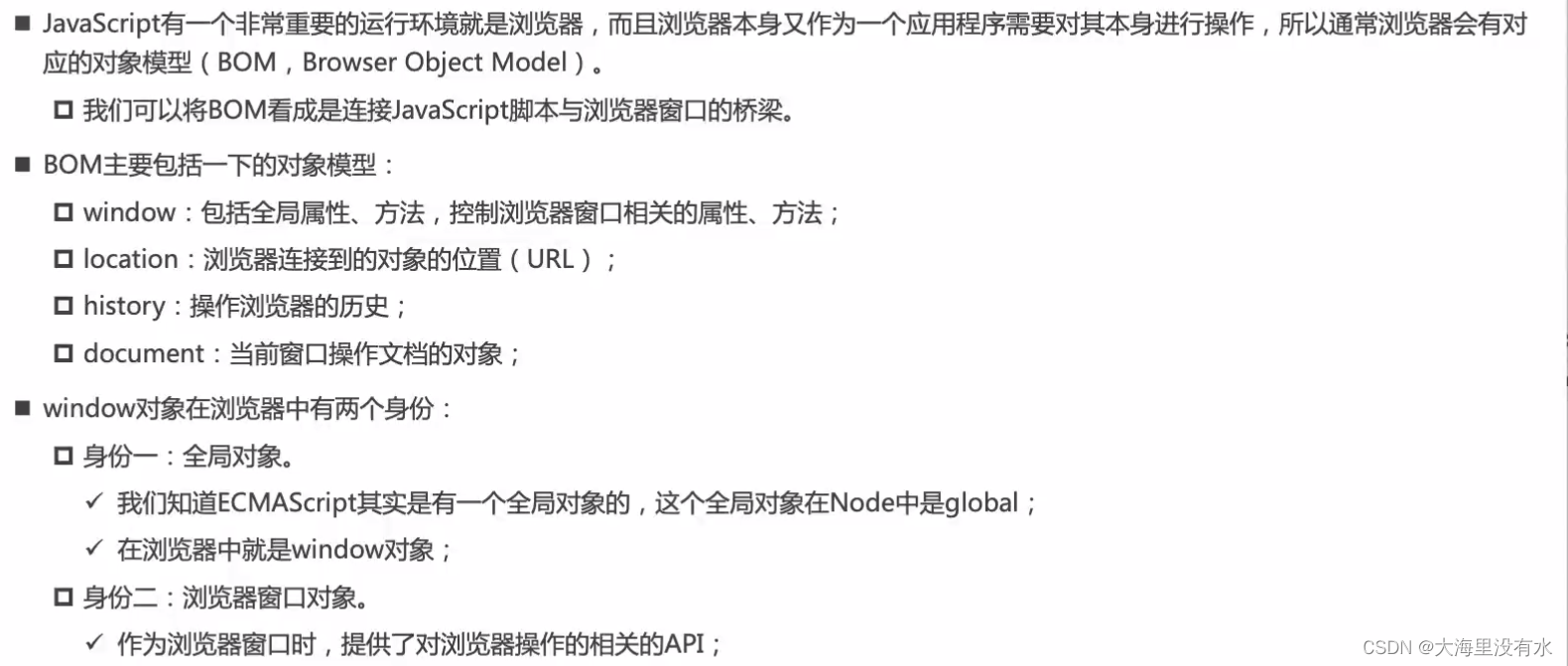
BOM DOM
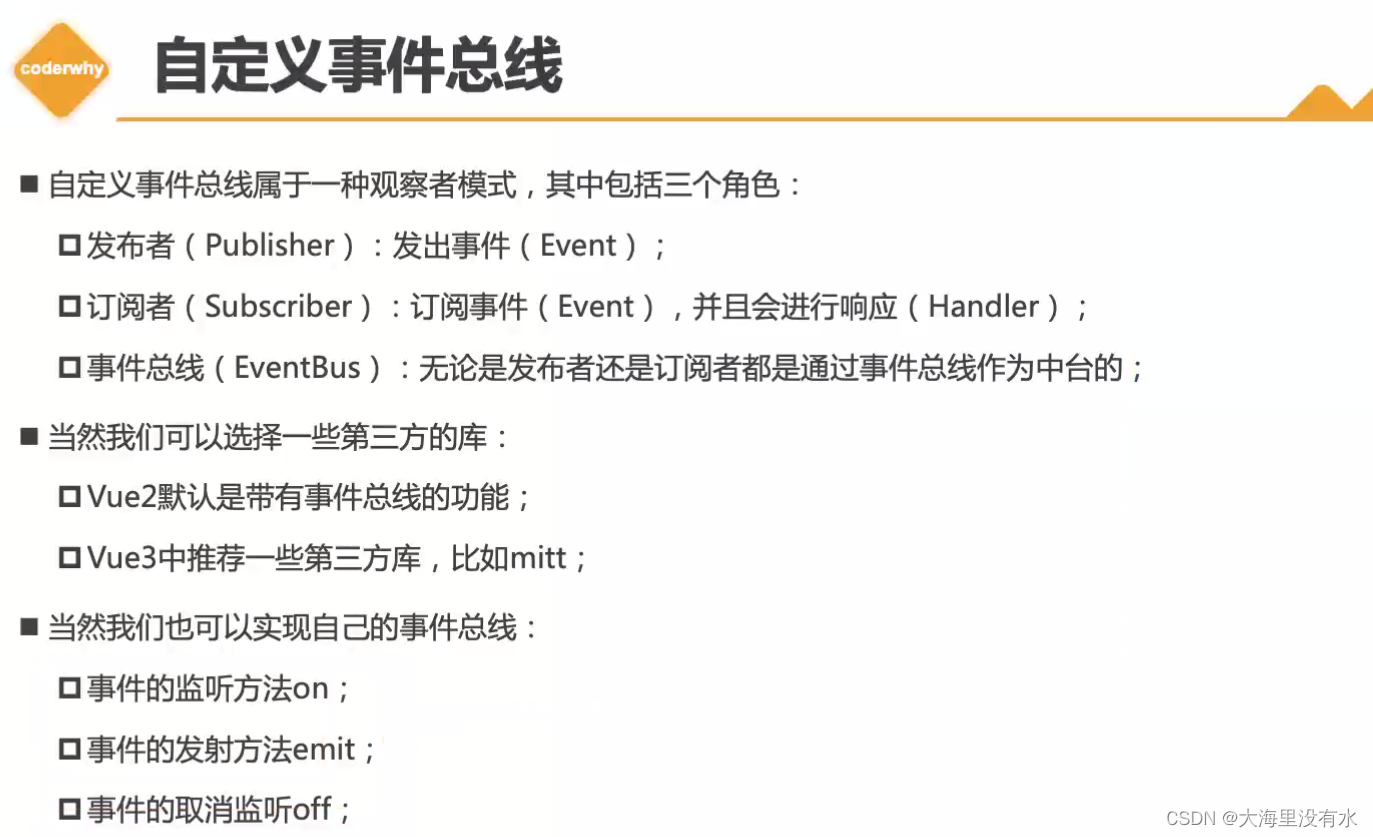
Deep Copy Event bus
Jenkins user rights management
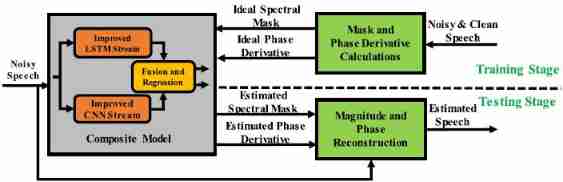
Thesis translation: 2022_ PACDNN: A phase-aware composite deep neural network for speech enhancement
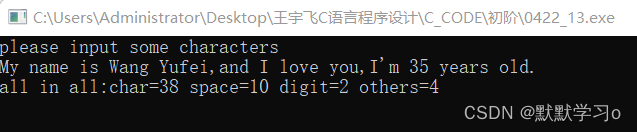
(C language) input a line of characters and count the number of English letters, spaces, numbers and other characters.

Programmers can't find jobs after the age of 35? After reading this article, you may be able to find the answer

AAAI 2022 | Peking University & Ali Dharma Institute: pruning and compression of pre training language model based on comparative learning
堆(优先级队列)

Take you ten days to easily finish the finale of go micro services (distributed transactions)
随机推荐
Lekao.com: experience sharing of junior economists and previous candidates in customs clearance
Natural language processing series (I) -- RNN Foundation
Use sqoop to export ads layer data to MySQL
mysql索引和事务
kubeadm join时出现错误:[ERROR Port-10250]: Port 10250 is in use [ERROR FileAvailable--etc-kubernetes-pki
High performance erasure code coding
JZ63 股票的最大利润
Anxiety of a 211 programmer: working for 3 years with a monthly salary of less than 30000, worried about being replaced by fresh students
LeetCode—剑指 Offer 59 - I、59 - II
BOM DOM
Tas (file d'attente prioritaire)
Programmers can't find jobs after the age of 35? After reading this article, you may be able to find the answer
Leetcode14 longest public prefix
防抖 节流
Openssh remote enumeration username vulnerability (cve-2018-15473)
China traffic sign detection data set
中国交通标志检测数据集
LeetCode—剑指 Offer 37、38
深拷贝 事件总线
This "little routine" is set on the dough cake of instant noodles. No wonder programmers are always hungry