当前位置:网站首页>Cvpr2022 | backdoor attack based on frequency injection in medical image analysis
Cvpr2022 | backdoor attack based on frequency injection in medical image analysis
2022-07-07 14:27:00 【Zhiyuan community】
This work was jointly completed by JD Exploration Research Institute and Northwestern Polytechnic University , Has been CVPR2022 receive . In this paper, we propose a backdoor attack method based on frequency domain information injection (Frequency-Injection based Backdoor Attack,FIBA). say concretely , We design a frequency domain trigger , By linearly combining the amplitude spectra of the two images , Inject the low-frequency information of the trigger image into the toxic image . because FIBA The semantics of contaminated image pixels are preserved , Therefore, we can attack the classification model , It can also attack the dense prediction model . We have carried out experiments on three benchmarks in the field of medical images ( For classification of skin lesions ISIC-2019 Data sets , For segmentation of renal tumors KiTS-19 Data sets , And for endoscopic artifact detection EAD-2019 Data sets ), To verify FIBA The effectiveness of attack medical image analysis model and its advantages in bypassing backdoor defense .
Thesis link :https://arxiv.org/abs/2112.01148
Code link : https://github.com/HazardFY/FIBA
边栏推荐
- 3D detection: fast visualization of 3D box and point cloud
- Source code analysis of ArrayList
- Mmkv use and principle
- 用例图
- GVIM [III] [u vimrc configuration]
- The longest ascending subsequence model acwing 1012 Sister cities
- How can the PC page call QQ for online chat?
- Seven propagation behaviors of transactions
- Multi merchant mall system function disassembly lecture 01 - Product Architecture
- Excuse me, as shown in the figure, the python cloud function prompt uses the pymysql module. What's the matter?
猜你喜欢
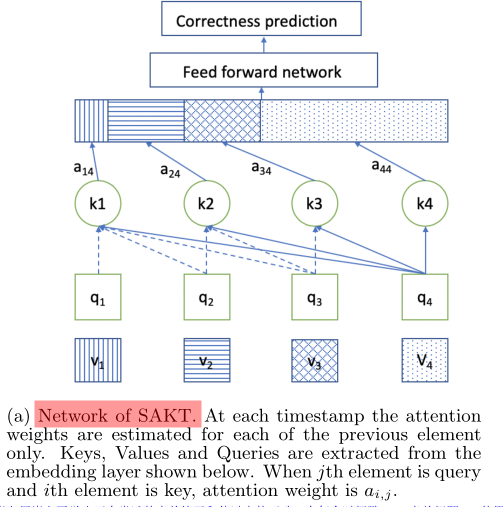
Introduction to sakt method
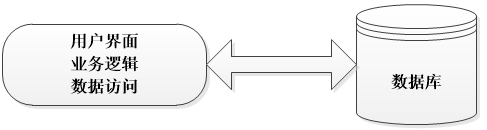
Take you to master the three-tier architecture (recommended Collection)
UML state diagram
LeetCode 648. Word replacement
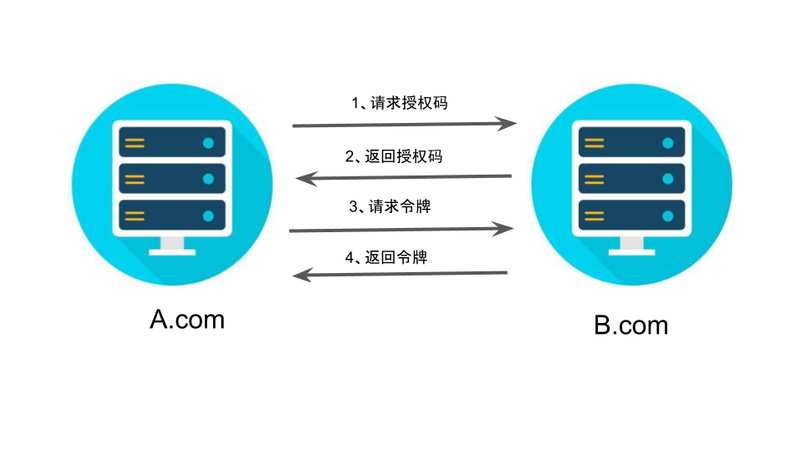
OAuth 2.0 + JWT 保护API安全
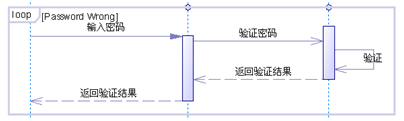
UML 顺序图(时序图)

设备故障预测机床故障提前预警机械设备振动监测机床故障预警CNC震动无线监控设备异常提前预警
![[Reading stereo matching papers] [III] ints](/img/d3/4238432492ac3dc4ec14a971b8848d.png)
[Reading stereo matching papers] [III] ints
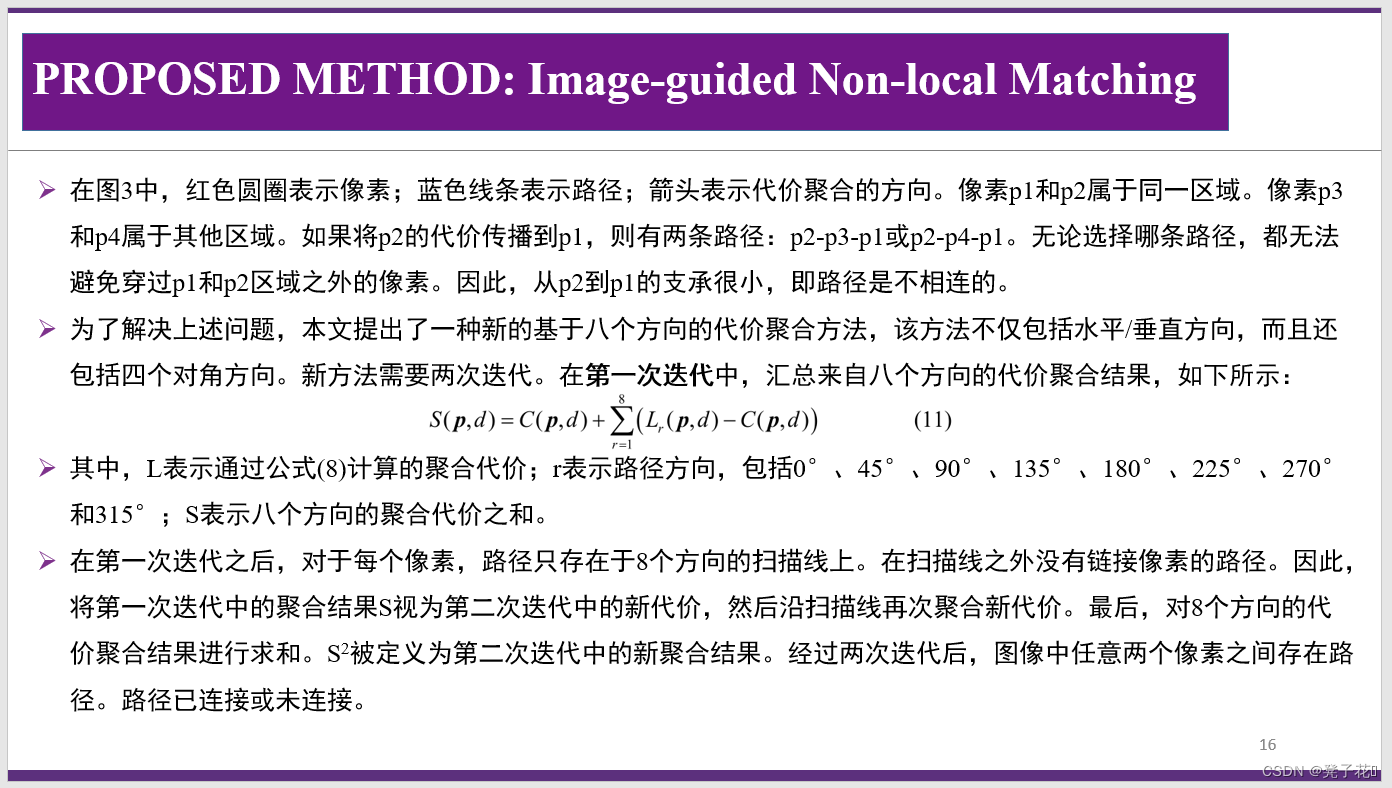
【立体匹配论文阅读】【三】INTS
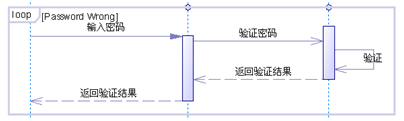
UML sequence diagram (sequence diagram)
随机推荐
【服务器数据恢复】某品牌StorageWorks服务器raid数据恢复案例
手把手教会:XML建模
请问,我kafka 3个分区,flinksql 任务中 写了 join操作,,我怎么单独给join
When FC connects to the database, do you have to use a custom domain name to access it outside?
MySQL "invalid use of null value" solution
VSCode 配置使用 PyLint 语法检查器
解析PHP跳出循环的方法以及continue、break、exit的区别介绍
Leetcode——344. 反转字符串/541. 反转字符串 II/151. 颠倒字符串中的单词/剑指 Offer 58 - II. 左旋转字符串
FCOS3D label assignment
Search engine interface
UML 状态图
Interface automation test - solution of data dependency between interfaces
一个简单LEGv8处理器的Verilog实现【四】【单周期实现基础知识及模块设计讲解】
Data flow diagram, data dictionary
课设之百万数据文档存取
Substance Painter笔记:多显示器且多分辨率显示器时的设置
CSMA/CD 载波监听多点接入/碰撞检测协议
Selenium Library
最长上升子序列模型 AcWing 1012. 友好城市
Hangdian oj2092 integer solution