当前位置:网站首页>Traffic management and control of firewall Foundation
Traffic management and control of firewall Foundation
2022-06-28 16:10:00 【51CTO】
Firewall traffic management and control
Principle overview :
A firewall ( English :Firewall) Technology is through the organic combination of all kinds of software and hardware equipment for safety management and screening , Help the computer network in it 、 Build a relatively isolated protective barrier between the external networks , A technology to protect user data and information security .
The function of firewall technology is to discover and deal with the possible security risks when the computer network is running 、 Data transmission and so on , The treatment measures include isolation and protection , At the same time, it can record and test all operations in computer network security , To ensure the security of computer network operation , Guarantee the integrity of user data and information , Better for users 、 More secure computer network experience .
So-called “ A firewall ” It refers to an intranet and public access network ( Such as Internet) The way of separation , It is actually an applied security technology based on modern communication network technology and information security technology , Isolation technology . It is more and more used in the interconnection environment of private network and public network , Especially with access Internet The Internet is the most important .
Firewall is a protective barrier between the internal and external network environment with the help of hardware and software , So as to block the unsafe network factors of the computer . Only with the consent of the firewall , Users can enter the computer , If you don't agree, you'll be blocked out , The alarm function of firewall technology is very powerful , When an external user wants to enter the computer , The firewall will quickly send out the corresponding alarm , And remind users of their behavior , And make self judgment to decide whether to allow external users to enter the interior , As long as the user is in the network environment , This kind of firewall can carry out effective query , At the same time, the information found will be displayed to the user , Then users need to implement corresponding settings for the firewall according to their own needs , Block the disallowed user behavior . Through the firewall, you can also effectively view the traffic of information data , And it can also master the speed of uploading and downloading data information , It is convenient for users to have good control judgment on the use of computers , The internal situation of the computer can also be viewed through this firewall , It also has the function of starting and closing the program , And the internal log function of the computer system , In fact, it is also a summary of the real-time situation of the firewall and the internal security of the computer system .
Firewall is a kind of access control scale which is executed when two networks communicate , It can prevent hackers from accessing your network to the maximum extent . It's set up on different networks ( Such as trusted intranet and untrusted public network ) Or a combination of components between network security domains . It is the only access to information between different networks or network security domains , Be able to control according to the safety policy of the enterprise ( allow 、 Refuse 、 monitoring ) Information flow in and out of the network , And it has strong anti attack ability . It's about providing information security services , Infrastructure for network and information security . Logically , The firewall is a separator , A limiter , It's also an analyzer , Effectively monitored the intranet and Internet Any activity between , Ensure the security of the internal network .
The firewall scans its network traffic , This will filter out some attacks , In case it is executed on the target computer . Firewalls can also shut down unused ports . And it can also disable outgoing traffic on specific ports , Block the Trojan horse . Last , It can disable access from special sites , To prevent all communications from unknown intruders .
The barrier of network security
A firewall ( As a blocking point 、 The control points ) It can greatly improve the security of an internal network , And reduce risk by filtering unsafe Services . Because only carefully selected application protocols can pass through the firewall , So the network environment becomes more secure . For example, firewalls can prohibit such as well-known unsafe NFS Protocol access to protected network , In this way, it is impossible for external attackers to use these fragile protocols to attack the internal network . Firewalls can also protect the network from routing based attacks , Such as IP Source routing attacks and ICMP Redirection path in redirection . The firewall should be able to reject all messages of the above types of attacks and notify the firewall administrator .
Strengthen network security strategy
Configure through a firewall centric security scheme , All security software ( Like a password 、 encryption 、 Identity Authentication 、 Audit, etc ) Configure on the firewall . Compared with dispersing network security issues to various hosts , Centralized security management of firewall is more economical . For example, during network access , The one-time password system and other identity authentication systems do not have to be scattered on each host , And focus on the firewall .
Monitoring audit
If all access passes through the firewall , that , The firewall can record these accesses and log them , At the same time, it can also provide statistical data of network usage . When something suspicious happens , The firewall can give appropriate alarm , And provide detailed information on whether the network is monitored and attacked . in addition , It is also very important to collect the usage and misuse of a network . The first reason is to know whether the firewall can resist the detection and attack of attackers , And know whether the control of firewall is sufficient . Network usage statistics are also very important for network demand analysis and threat analysis .
Prevent the leakage of internal information
By using firewall to divide the internal network , It can realize the isolation of key network segments of intranet , Thus, the impact of local key or sensitive network security issues on the global network is limited . also , Privacy is an issue of great concern to the intranet , An unnoticed detail in an internal network may contain clues about security and attract the interest of external attackers , Some security vulnerabilities of the internal network have even been exposed . Using a firewall, you can hide those internal details, such as Finger,DNS Etc .Finger Displays the registered names of all users of the host 、 real name , Last login time and use shell Type, etc . however Finger The information displayed is very easy for attackers to learn . An attacker can know how often a system is used , Whether there are users connecting to the Internet in this system , Whether the system is noticed when being attacked, etc . Firewalls can also block information about internal networks DNS Information , The domain name of such a host and IP The address will not be known to the outside world . In addition to safety , The firewall also supports Internet Service enterprise internal network technology system VPN( Virtual private network ).
Logging and event notification
All data entering and leaving the network must pass through the firewall , The firewall records it through logs , It can provide detailed statistical information of network use . When a suspicious event occurs , The firewall can alarm and notify according to the mechanism , Provide information on whether the network is threatened .
The experimental requirements :
Bandwidth management requirements : An enterprise pulled a line 50M Internet connection
1: The overall uplink and downlink bandwidth of the marketing department is limited to 40M, Guaranteed bandwidth is 20M
2: The overall uplink and downlink bandwidth of the engineering department is limited to 30M, Guaranteed bandwidth is 15M
3: The overall uplink and downlink bandwidth of the administration department is limited to 20M, Guaranteed bandwidth is 10M
4: The maximum uplink and downlink bandwidth per user in all departments 4M, Guaranteed bandwidth 400K
5: If there is congestion , The traffic priority is the marketing department > engineering department > The administration department
Firewall bandwidth management configuration ideas :
1: Configuration area 、 Interface 、IP
2: Configure the routing
3: To configure NAT
4: Configure security policy
5: Configure bandwidth management
The topology :

Basic configuration :
web Configuration page :
Configure interface :

Configure security zones :

Configure the default route :

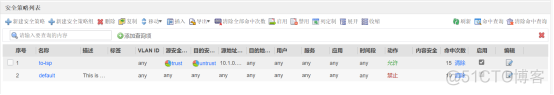
Configure security policy :
To configure NAT Source address translation :

Configure bandwidth channel :

Configure bandwidth policy :

Command line configuration :
ISP:
FW1:
Configure interface :
#
interface GigabitEthernet0/0/0
undo shutdown
ip binding vpn-instance default
ip address 10.1.1.1 255.255.255.0
alias GE0/METH
service-manage http permit
service-manage https permit
service-manage ping permit
service-manage ssh permit
service-manage snmp permit
service-manage telnet permit
#
interface GigabitEthernet1/0/0
undo shutdown
service-manage http permit
service-manage https permit
service-manage ping permit
service-manage ssh permit
service-manage snmp permit
service-manage telnet permit
#
interface GigabitEthernet1/0/0.10
vlan-type dot1q 10
ip address 10.1.1.1 255.255.255.0
service-manage http permit
service-manage https permit
service-manage ping permit
service-manage ssh permit
service-manage snmp permit
service-manage telnet permit
#
interface GigabitEthernet1/0/0.20
vlan-type dot1q 20
ip address 10.1.2.1 255.255.255.0
service-manage http permit
service-manage https permit
service-manage ping permit
service-manage ssh permit
service-manage snmp permit
service-manage telnet permit
#
interface GigabitEthernet1/0/0.30
vlan-type dot1q 30
ip address 10.1.3.1 255.255.255.0
service-manage http permit
service-manage https permit
service-manage ping permit
service-manage ssh permit
service-manage snmp permit
service-manage telnet permit
#
interface GigabitEthernet1/0/1
undo shutdown
ip address 11.1.1.1 255.255.255.0
service-manage http permit
service-manage https permit
service-manage ping permit
service-manage ssh permit
service-manage snmp permit
service-manage telnet permit
- 1.
- 2.
- 3.
- 4.
- 5.
- 6.
- 7.
- 8.
- 9.
- 10.
- 11.
- 12.
- 13.
- 14.
- 15.
- 16.
- 17.
- 18.
- 19.
- 20.
- 21.
- 22.
- 23.
- 24.
- 25.
- 26.
- 27.
- 28.
- 29.
- 30.
- 31.
- 32.
- 33.
- 34.
- 35.
- 36.
- 37.
- 38.
- 39.
- 40.
- 41.
- 42.
- 43.
- 44.
- 45.
- 46.
- 47.
- 48.
- 49.
- 50.
- 51.
- 52.
- 53.
- 54.
- 55.
- 56.
- 57.
- 58.
- 59.
- 60.
- 61.
Configure security zones :
Configure the default route :
Configure security policy :
Configure source address translation :
Configure traffic management :
#
traffic-policy
profile 1
bandwidth maximum-bandwidth whole upstream 40000
bandwidth guaranteed-bandwidth whole upstream 20000
bandwidth maximum-bandwidth whole downstream 40000
bandwidth guaranteed-bandwidth whole downstream 20000
bandwidth maximum-bandwidth per-ip upstream 4000
bandwidth guaranteed-bandwidth per-ip upstream 400
bandwidth maximum-bandwidth per-ip downstream 4000
bandwidth guaranteed-bandwidth per-ip downstream 400
profile 2
bandwidth maximum-bandwidth whole upstream 30000
bandwidth guaranteed-bandwidth whole upstream 15000
bandwidth maximum-bandwidth whole downstream 30000
bandwidth guaranteed-bandwidth whole downstream 15000
bandwidth maximum-bandwidth per-ip upstream 4000
bandwidth guaranteed-bandwidth per-ip upstream 400
bandwidth maximum-bandwidth per-ip downstream 4000
bandwidth guaranteed-bandwidth per-ip downstream 400
profile 3
bandwidth maximum-bandwidth whole upstream 20000
bandwidth guaranteed-bandwidth whole upstream 10000
bandwidth maximum-bandwidth whole downstream 20000
bandwidth guaranteed-bandwidth whole downstream 10000
bandwidth maximum-bandwidth per-ip upstream 4000
bandwidth guaranteed-bandwidth per-ip upstream 400
bandwidth maximum-bandwidth per-ip downstream 4000
bandwidth guaranteed-bandwidth per-ip downstream 400
rule name 1
source-zone trust
destination-zone untrust
source-address 10.1.1.0 mask 255.255.255.0
action qos profile 1
rule name 2
source-zone trust
destination-zone untrust
source-address 10.1.2.0 mask 255.255.255.0
action qos profile 2
rule name 3
source-zone trust
destination-zone untrust
source-address 10.1.3.0 mask 255.255.255.0
action qos profile 3
- 1.
- 2.
- 3.
- 4.
- 5.
- 6.
- 7.
- 8.
- 9.
- 10.
- 11.
- 12.
- 13.
- 14.
- 15.
- 16.
- 17.
- 18.
- 19.
- 20.
- 21.
- 22.
- 23.
- 24.
- 25.
- 26.
- 27.
- 28.
- 29.
- 30.
- 31.
- 32.
- 33.
- 34.
- 35.
- 36.
- 37.
- 38.
- 39.
- 40.
- 41.
- 42.
- 43.
- 44.
Configuration complete ;
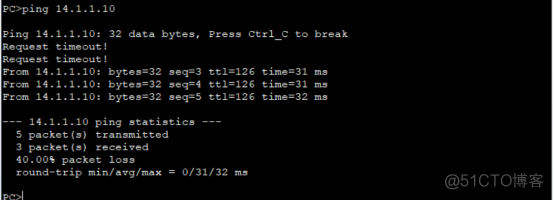
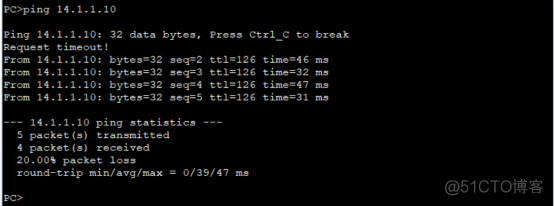
Validation experiment ;
The Marketing Department
engineering department

The administration department
View the number of traffic control hits :

End of experiment ;
remarks : If there is a mistake , Please understand !
This article is my study notes , For reference only ! If there is a repetition !!! Please contact me
边栏推荐
- Analysis of PostgreSQL storage structure
- Azure Kinect微软摄像头Unity开发小结
- Qt5.5.1 configuring msvc2010 compiler and WinDbg debugger
- NFT pledge LP liquidity mining system development details
- 首次失败后,爱美客第二次冲刺港交所上市,财务负责人变动频繁
- 成功迁移到云端需要采取的步骤
- 【高并发基础】MySQL索引优化
- 简单介绍一下tensorflow与pytorch的相互转换(主要是tensorflow转pytorch)
- 【LeetCode】13、罗马数字转整数
- Android, eclipse and MySQL upload pictures and get
猜你喜欢

【Spock】处理 Non-ASCII characters in an identifier

全球陆续拥抱Web3.0,多国已明确开始抢占先机

CODING DevOps 助力中化信息打造新一代研效平台,驱动“线上中化”新未来
10年测试经验,在35岁的生理年龄面前,一文不值

一台服务器最大并发 tcp 连接数多少?65535?

No win32/com in vs2013 help document

Slim GAIN(SGAIN)介绍及代码实现——基于生成对抗网络的缺失数据填补
![The k-th element in the array [heap row + actual time complexity of heap building]](/img/69/bcafdcb09ffbf87246a03bcb9367aa.png)
The k-th element in the array [heap row + actual time complexity of heap building]
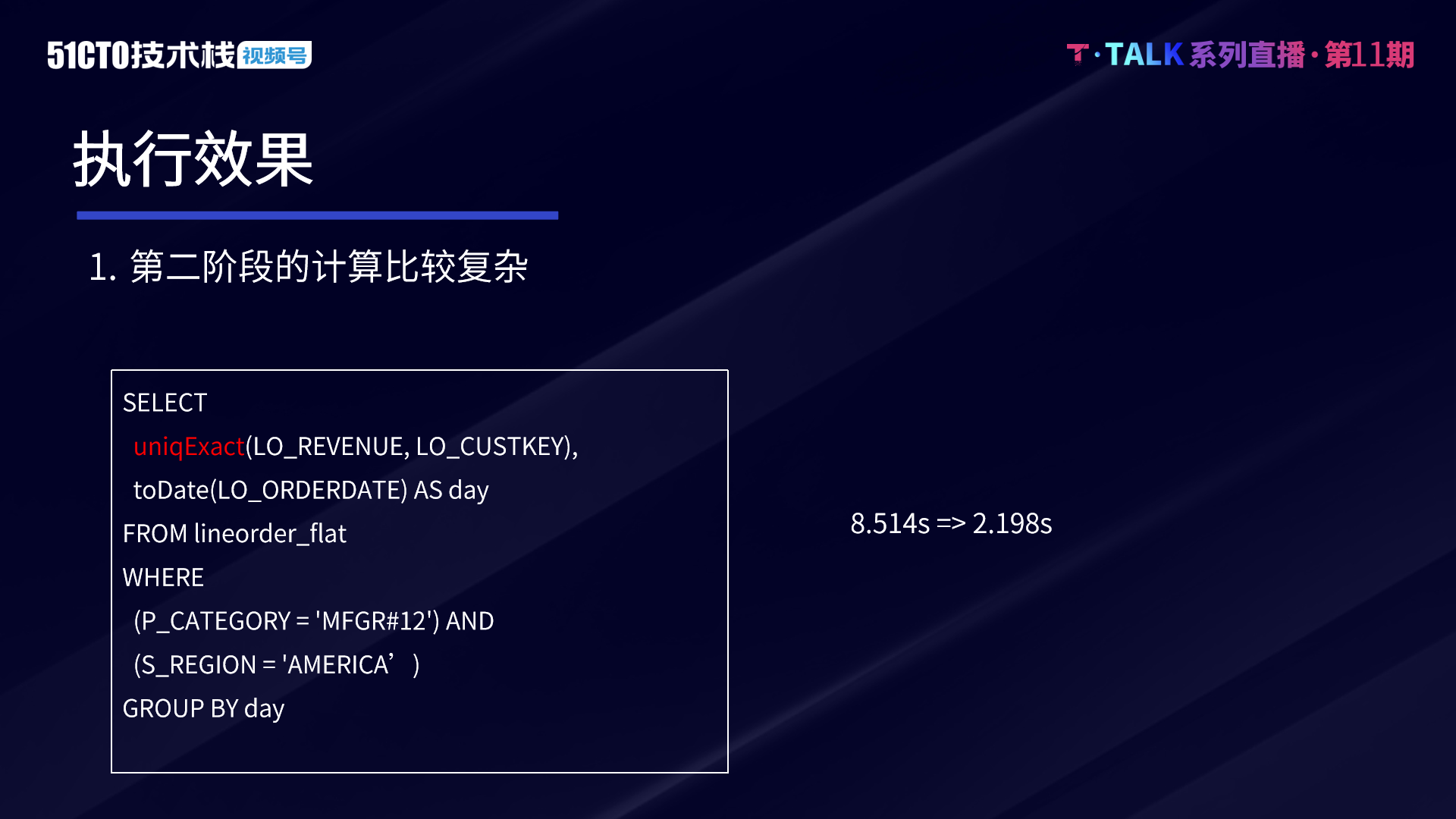
Technical secrets of ByteDance data platform: implementation and optimization of complex query based on Clickhouse

薅羊毛的机会了,点个“赚”即有机会赚取高额佣金
随机推荐
使用openpyxl操作Excel
Application of mongodb in Tencent retail premium code
PostgreSQL enables grouping statistics by year, month, day, week, hour, minute and second
成功迁移到云端需要采取的步骤
Today's sleep quality record is 80 points
Visual Studio 2019软件安装包和安装教程
薅羊毛的机会了,点个“赚”即有机会赚取高额佣金
Knowing these commands allows you to master shell's own tools
Opengauss kernel: analysis of SQL parsing process
Navicat 15 for MySQL
What are the most powerful small and medium-sized companies in Beijing?
5分钟的时间制作一个反弹球游戏
10年测试经验,在35岁的生理年龄面前,一文不值
Android, eclipse and MySQL upload pictures and get
Azure Kinect微软摄像头Unity开发小结
[Spock] process non ASCII characters in an identifier
Among US private server setup
openGauss内核:SQL解析过程分析
Openharmony - detailed source code of Kernel Object Events
QT create 5.0.3 configuring qt4.8.7