当前位置:网站首页>Xin'an Second Edition: Chapter 24 industrial control safety demand analysis and safety protection engineering learning notes
Xin'an Second Edition: Chapter 24 industrial control safety demand analysis and safety protection engineering learning notes
2022-07-06 17:34:00 【Moon Dream Studio】
One 、 The outline of this chapter requires
7. Industrial control safety demand analysis and safety protection engineering
7.1 Security threat and demand analysis of industrial control system
◆ Concept and composition of industrial control system (SCADA System 、 Distributed control system 、 Process control system 、 PLC 、 Remote terminal 、 CNC machine tools and CNC systems )
◆ Security threat analysis of industrial control system ( Natural disasters and environment 、 Internal security threats 、 Equipment functional safety failure 、 Malicious code 、 Cyber attacks, etc )
◆ Types of potential safety hazards in industrial control systems ( Industrial control protocol security 、 Security loopholes in industrial control system technology products 、 Security loopholes in basic software of industrial control system 、 Algorithm security vulnerability of industrial control system 、 Firmware vulnerability of industrial control system equipment 、 Hardware vulnerability of industrial control system equipment 、 Open access vulnerability of industrial control system 、 Industrial control system, supply chain security, etc )
◆ Analysis of safety requirements of industrial control system ( Tradition IT The safety of the 、 Control equipment and operation safety 、 Safety management compliance, etc )
7.2 Safety protection mechanism and technology of industrial control system
7.2.1 Physical and environmental safety protection
◆ Video surveillance ◆ Industrial host reinforcement
7.2.2 Security zoning and boundary protection
◆ Security partition ◆ Industrial control firewall ◆ Industrial control safety isolation and information exchange system
7.2.3 Identity authentication and access control
◆ Multifactor certification ◆ Minimum privilege ◆ Avoid using default passwords or weak passwords
7.2.4 Remote access security
◆ Disable high-risk Services ◆ Safety reinforcement ◆ Virtual private network (VPN) ◆ Security audit
7.2.5 Safety reinforcement of industrial control system
◆ Security configuration policy ◆ Identity authentication enhancement ◆ Enforce access control ◆ Program white list control
7.2.6 Industrial control safety audit
◆ Security audit equipment deployment ◆ Audit data backup ◆ Analysis and utilization of audit data
7.2.7 Malicious code prevention
◆ Anti virus software testing, deployment and operation
◆ Anti virus and malware intrusion management mechanism
◆ Major industrial control security vulnerability information acquisition and patch upgrade measures
7.2.8 Industrial control data security
◆ Industrial data management methods
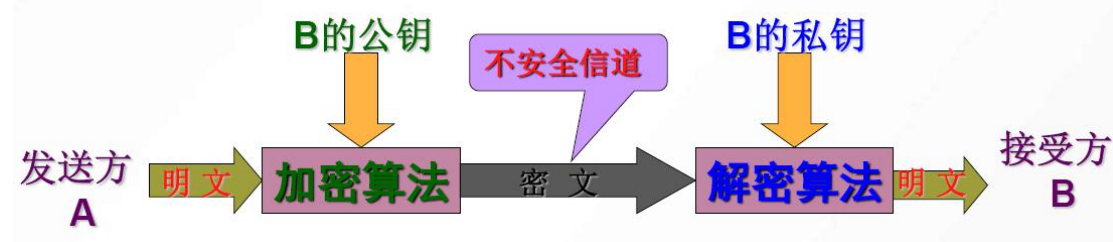
◆ Industrial data security protection measures ( Safe isolation 、 Access control 、 encryption
边栏推荐
- Automatic operation and maintenance sharp weapon ansible Playbook
- Take you hand-in-hand to do intensive learning experiments -- knock the level in detail
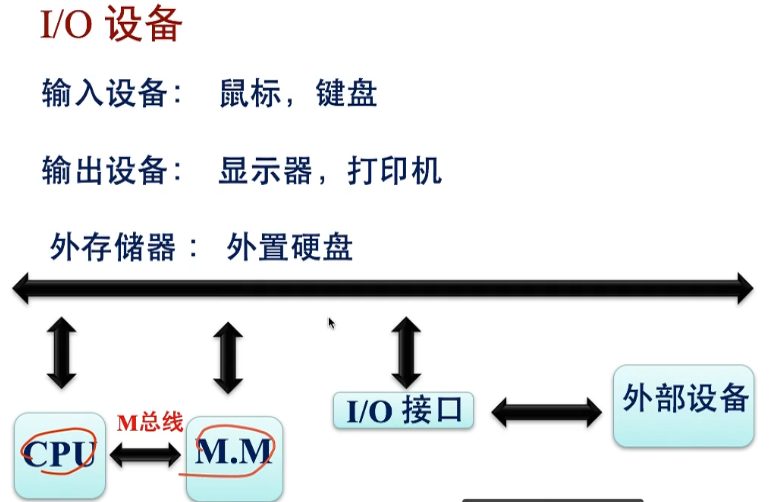
- 网络分层概念及基本知识
- mysql的列的数据类型详解
- The NTFS format converter (convert.exe) is missing from the current system
- Based on infragistics Document. Excel export table class
- Garbage first of JVM garbage collector
- C# WinForm系列-Button简单使用
- Detailed explanation of data types of MySQL columns
- CentOS7上Redis安装
猜你喜欢
信息与网络安全期末复习(基于老师给的重点)
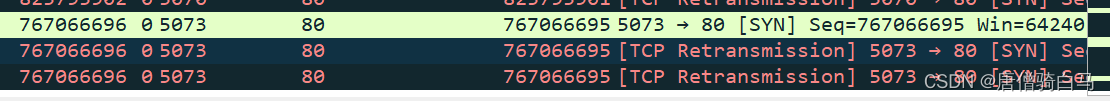
TCP connection is more than communicating with TCP protocol
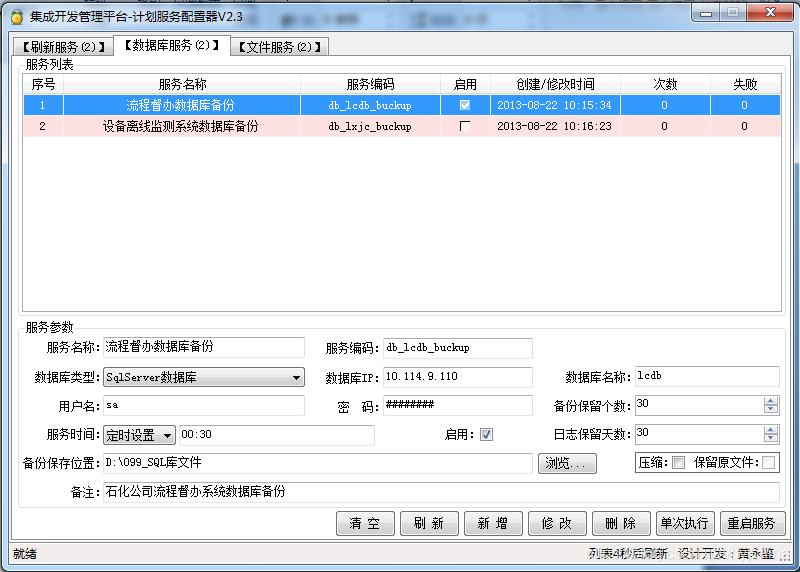
轻量级计划服务工具研发与实践
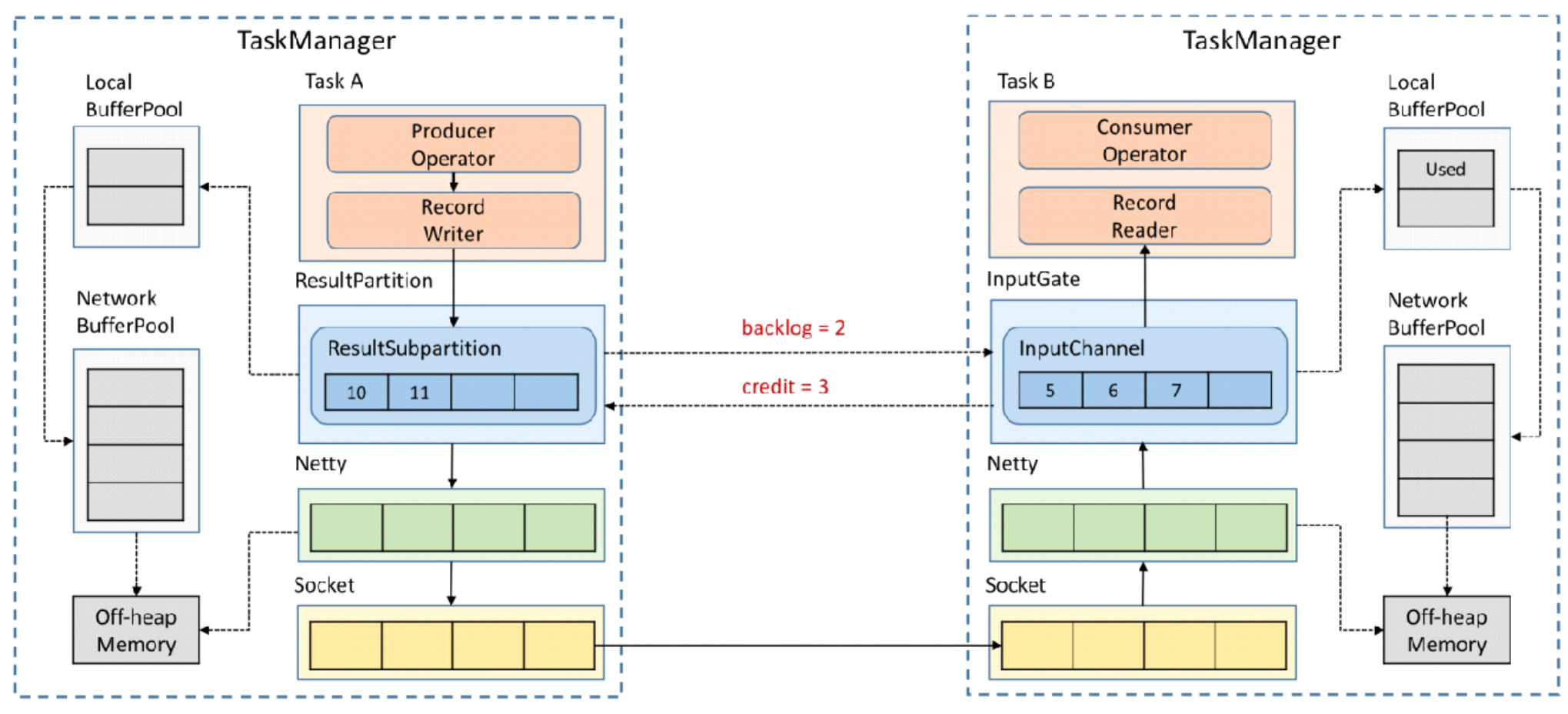
Flink analysis (II): analysis of backpressure mechanism
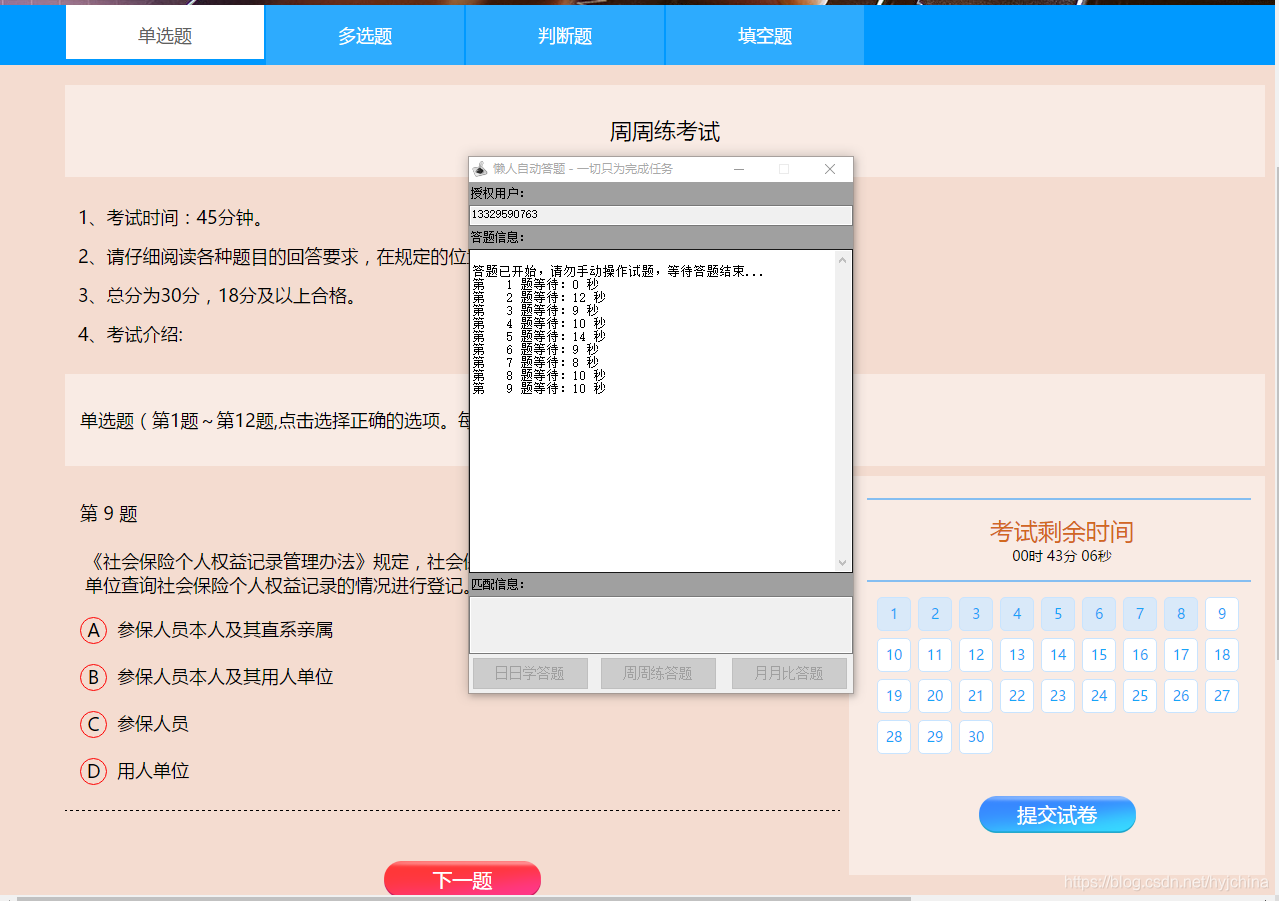
自动答题 之 Selenium测试直接运行在浏览器中,就像真正的用户在操作一样。
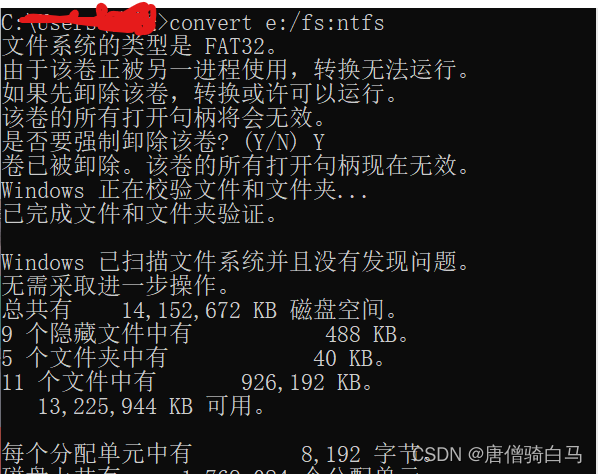
The NTFS format converter (convert.exe) is missing from the current system
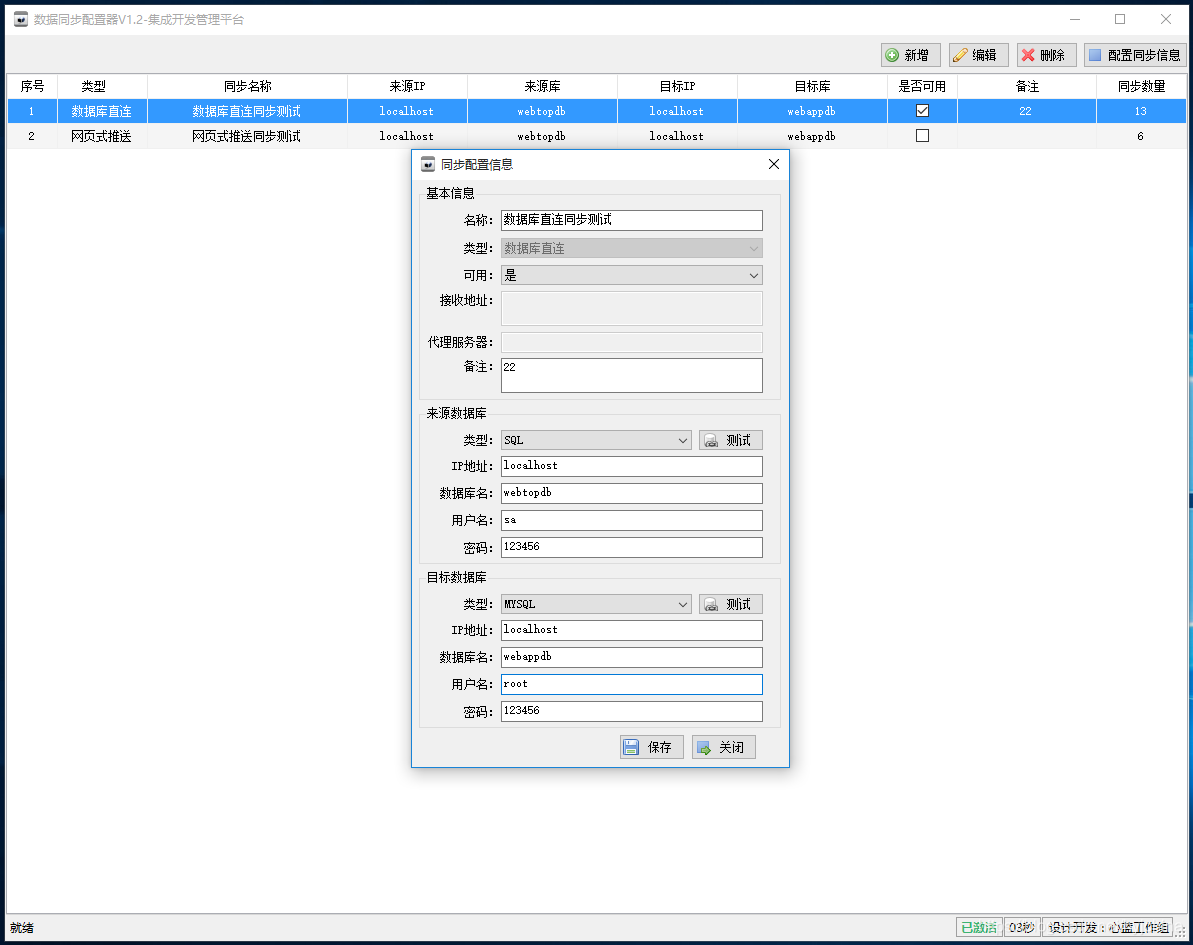
05个人研发的产品及推广-数据同步工具

【Elastic】Elastic缺少xpack无法创建模板 unknown setting index.lifecycle.name index.lifecycle.rollover_alias
华为认证云计算HICA
![[reverse primary] Unique](/img/80/9fcef27863facc9066e48f221c6686.png)
[reverse primary] Unique
随机推荐
CTF逆向入门题——掷骰子
February database ranking: how long can Oracle remain the first?
1. Introduction to JVM
Development and practice of lightweight planning service tools
Program counter of JVM runtime data area
Akamai anti confusion
连接局域网MySql
vscode
数据仓库建模使用的模型以及分层介绍
Vscode matches and replaces the brackets
【逆向】脱壳后修复IAT并关闭ASLR
学习投资大师的智慧
Flink 解析(一):基础概念解析
Flink 解析(七):时间窗口
04个人研发的产品及推广-数据推送工具
mysql的合计/统计函数
yarn : 无法加载文件 D:\ProgramFiles\nodejs\yarn.ps1,因为在此系统上禁止运行脚本
Take you hand-in-hand to do intensive learning experiments -- knock the level in detail
Deploy flask project based on LNMP
Flink源码解读(一):StreamGraph源码解读