当前位置:网站首页>Reptile learning 4 winter vacation series (3)
Reptile learning 4 winter vacation series (3)
2022-07-04 11:20:00 【Kosisi】
Online cloud suppression hot reviews crawl
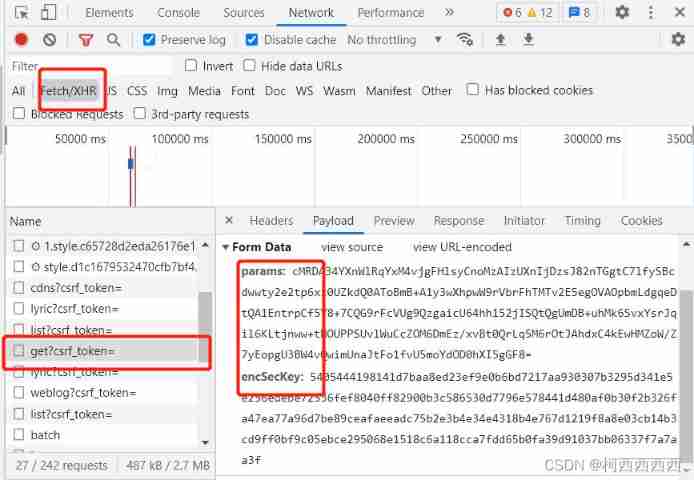
These two parameters are encrypted , Our task is to simulate the encryption process of Netease cloud , Encryption parameters are passed to the browser .
1) New tools ,call stack Called stack , That is, when I send a request to the file on the left , What are they? js Script execution process , Arranged from bottom to top
2) To set breakpoints , View parameter and variable values
3) Learn to simulate website rendering process through stack
4) Learn to simplify the process of website encryption
Judge whether the parameters can be fixed , If it can be fixed , You can get relevant parameters from the web page , Minimize random parameters .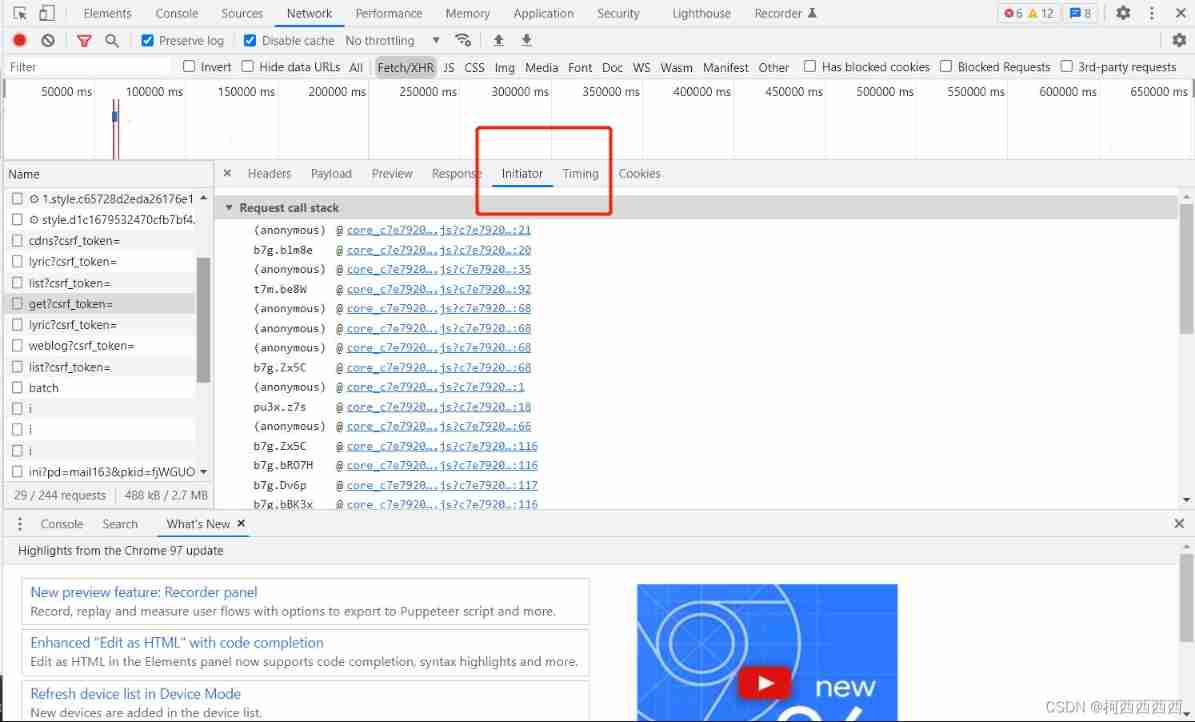
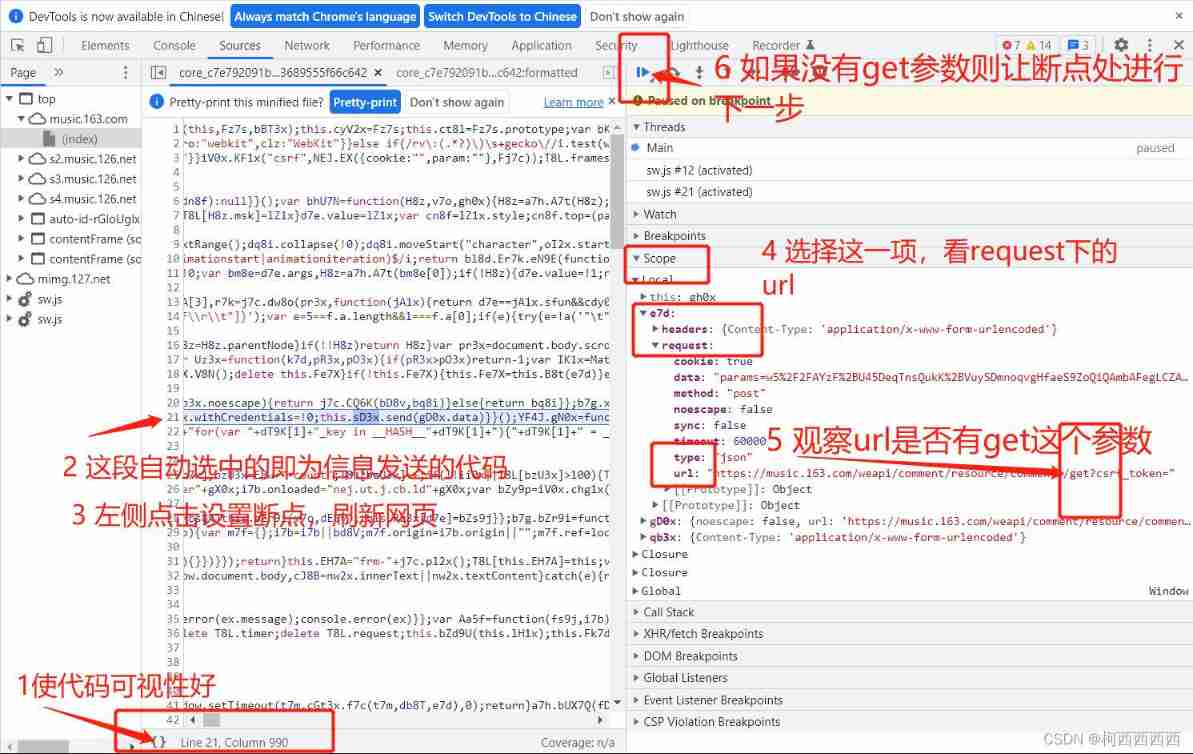
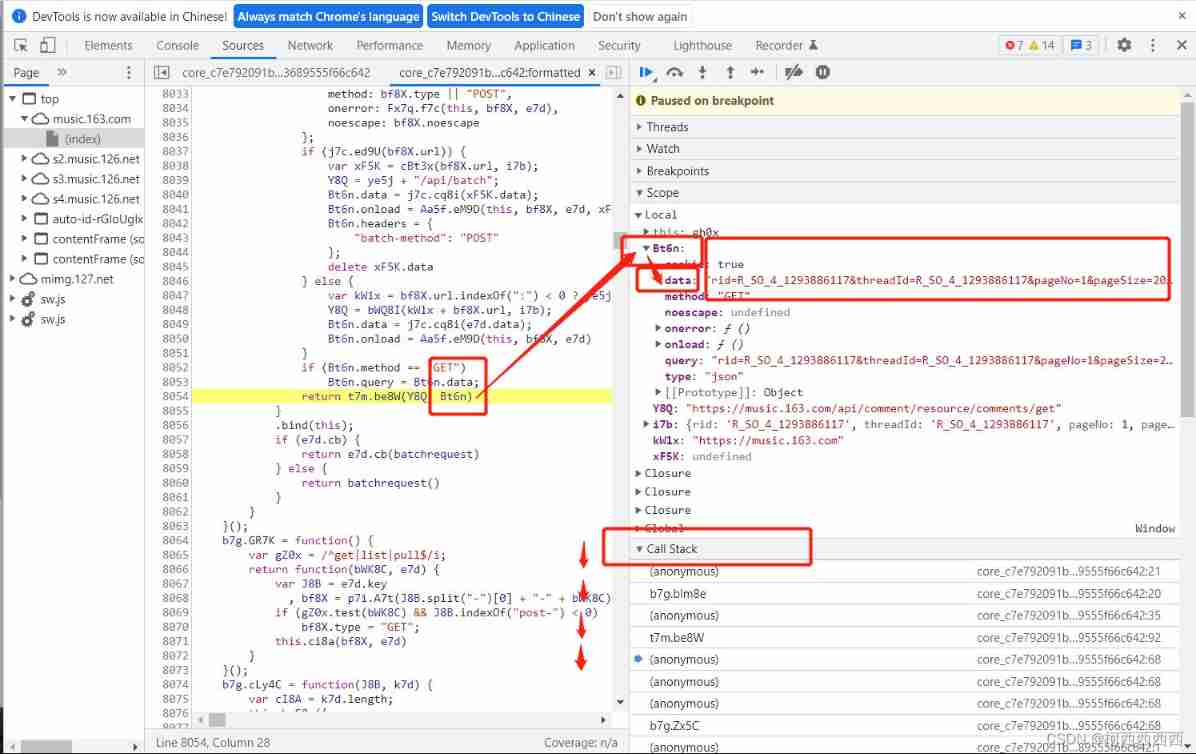
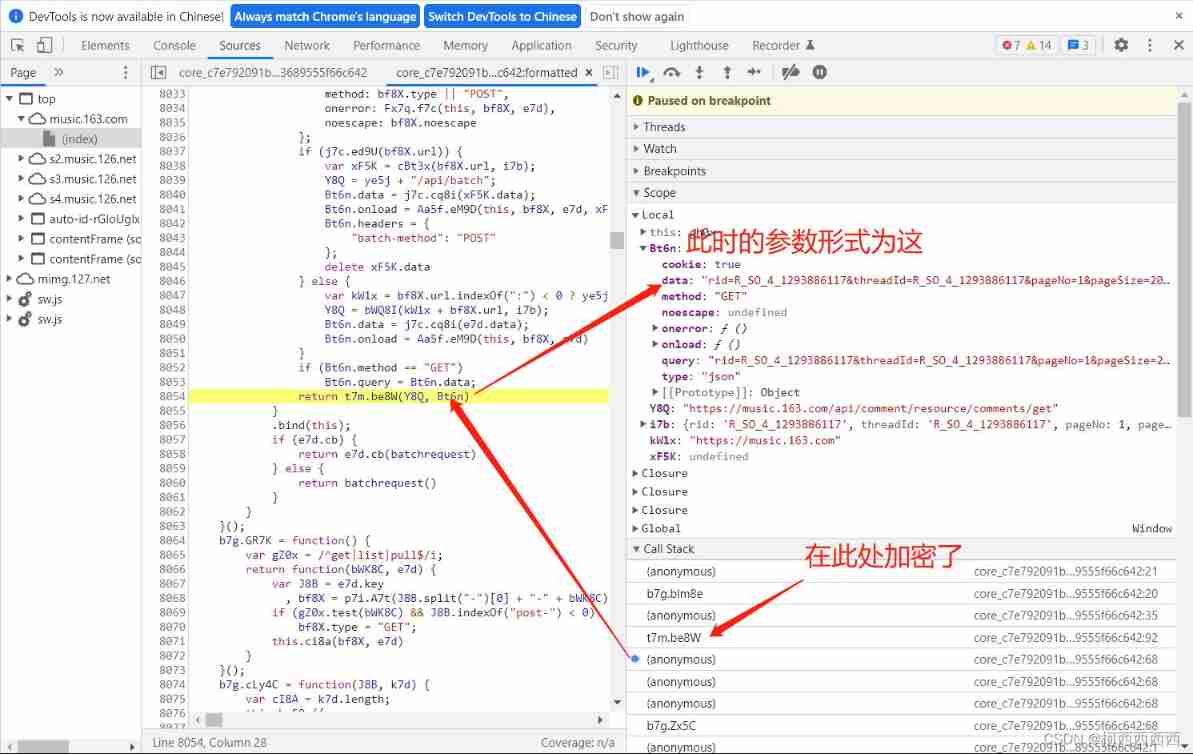
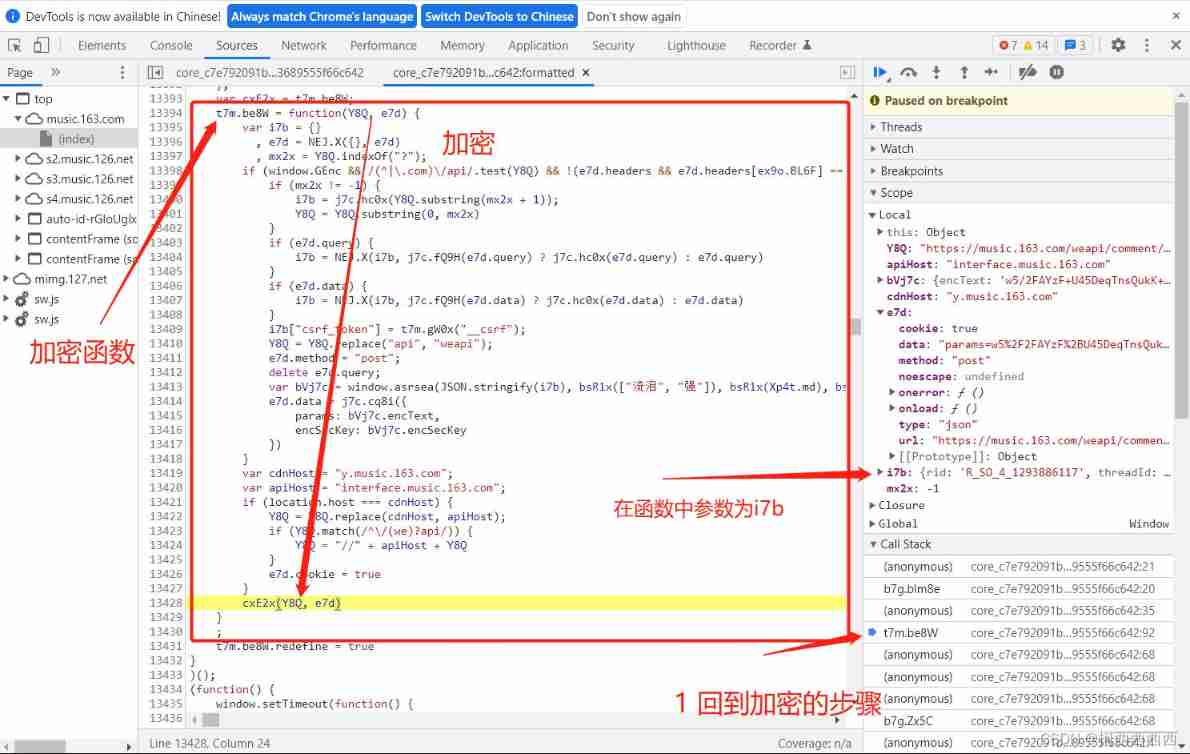
What we need to do now is to figure out how the program is encrypted .
Out of line
It's too complicated
Don't look at the lack of code , But it's complicated , What is involved . Code is the essence , By fixing parameters , Encrypt the final required parameters ; But finding and implementing this encryption process is very strong . I was confused about this project , Take a break .
It's impossible to estimate the probability just by looking at the code and notes , A face of meng , Of course, we should exclude the great gods #pycrypto Module is to provide encryption algorithm #base64 Modules are used to convert to bytes , Give Way utf-8 It can be recognized #json The module is transformed into json String in
The following is the encryption rules obtained from the website following the process , Our task is to understand the principle of encryption , Then we restore the encryption process , The simplification of the tutorial is too strong .
# The encryption process ( The encryption algorithm on the intercepted website )
function a(a=16) {
# Back to c Is random 16 A string
var d, e, b = "abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789", c = "";
for (d = 0; a > d; d += 1)# loop 16 Time
e = Math.random() * b.length,# random number
e = Math.floor(e),# integer
c += b.charAt(e);# Take the string xxx Location
return c
}
function b(a, b) {
# a Is the content to be encrypted ,
var c = CryptoJS.enc.Utf8.parse(b) # c yes b, therefore b It's the key
, d = CryptoJS.enc.Utf8.parse("0102030405060708")
, e = CryptoJS.enc.Utf8.parse(a) # e Is the data
, f = CryptoJS.AES.encrypt(e, c, {
# One key is missing ,c It's an encrypted key
iv: d, # Offset
mode: CryptoJS.mode.CBC # Encryption mode CBC
});
return f.toString()
}
function c(a, b, c) {
var d, e;
return setMaxDigits(131),
d = new RSAKeyPair(b,"",c),
e = encryptedString(d, a)
}
function d(d, e, f, g) {
d: data data, e:010001, f: Very long fixed value , g:0CoJUm6Qyw8W8jud
var h = {
} # An empty object
, i = a(16); # i yes 16 Random values of bits
return h.encText = b(d, g), # g It's the key
h.encText = b(h.encText, i), # Back to you params,i It's also a key
h.encSecKey = c(i, e, f), # What you get is encSecKey, So both parameters are obtained
# hold i Hold on , Then the generated parameter is also a fixed value , because i e f Only i Random number , And c() No random numbers
h
# These four sentences are return h, Need to see b() and c()
}
I've seen that the subsequent operation is to clean the crawled information , Then sort out the key hot words , Form hot word posters .
边栏推荐
- QQ set group information
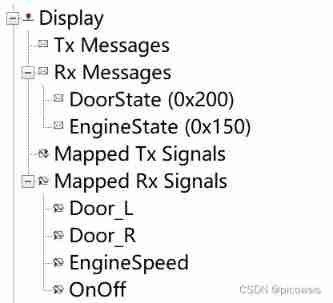
- Canoe test: two ways to create CAPL test module
- Exceptions and exception handling
- For and while loops
- How to deal with the relationship between colleagues
- The most ideal automated testing model, how to achieve layering of automated testing
- Heartbeat启动后无反应
- Canoe - the third simulation project - bus simulation - 2 function introduction, network topology
- Solaris 10 network services
- regular expression
猜你喜欢
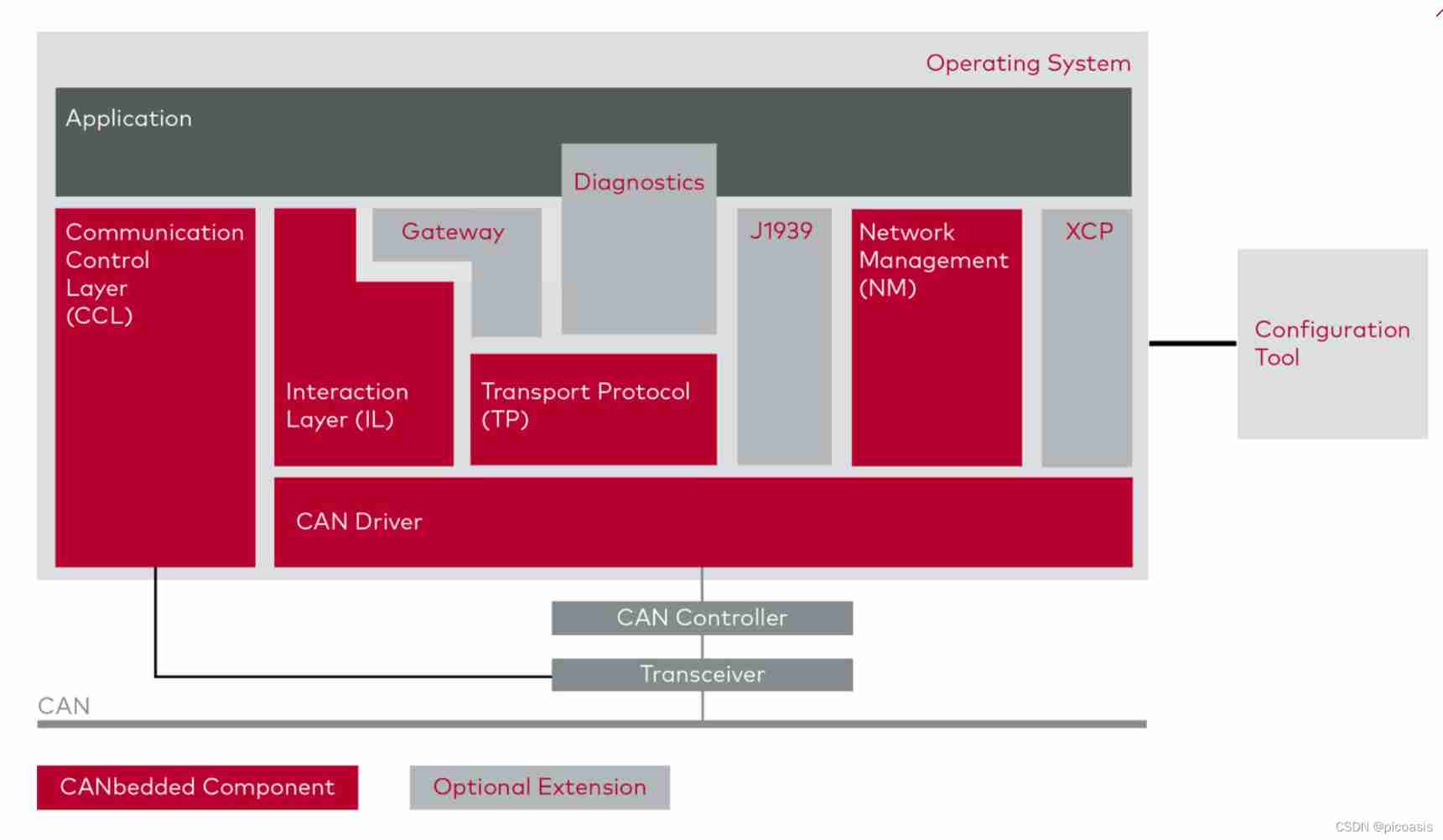
Function introduction of canbedded component
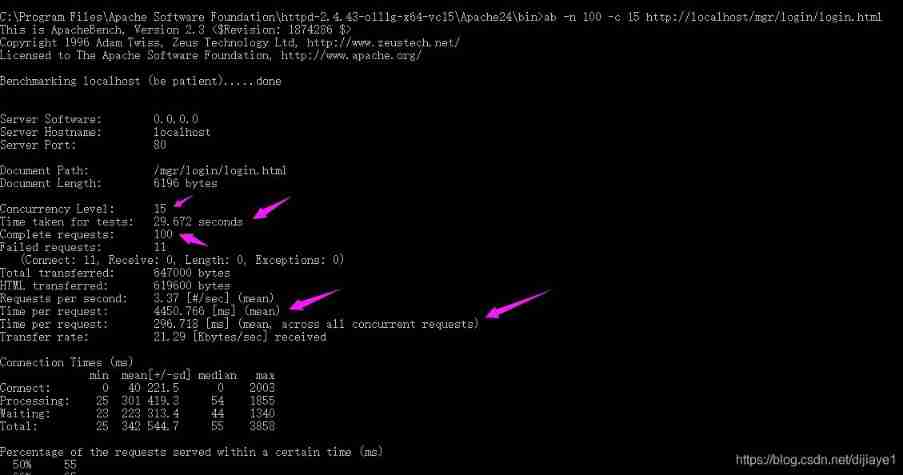
Ten key performance indicators of software applications
Personal thoughts on the development of game automation protocol testing tool
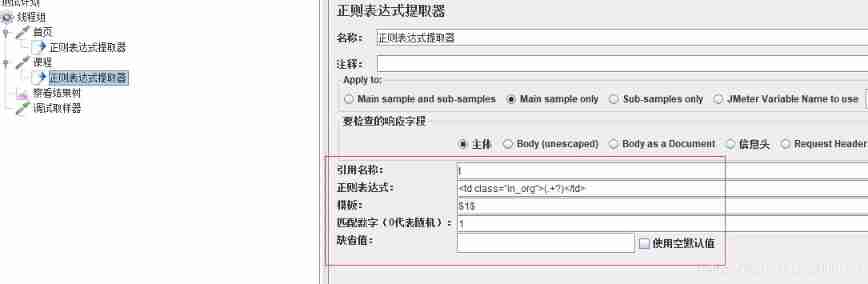
JMeter correlation technology
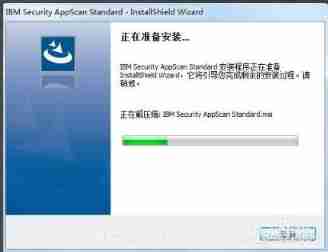
Appscan installation steps
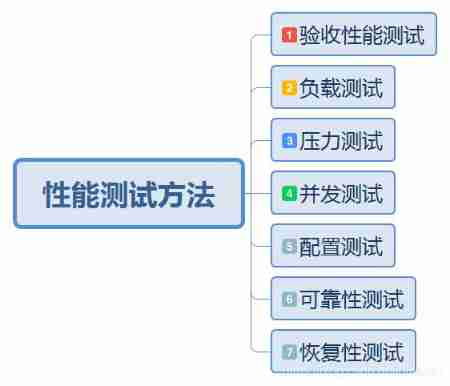
Performance test method
Canoe - the second simulation engineering - xvehicle - 2panel design (principle, idea)
Day01 preliminary packet capture
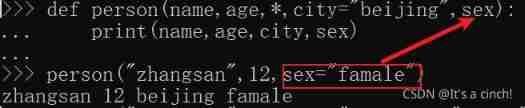
Function parameters (positional parameters, default value parameters, variable parameters, named keyword parameters, keyword parameters)
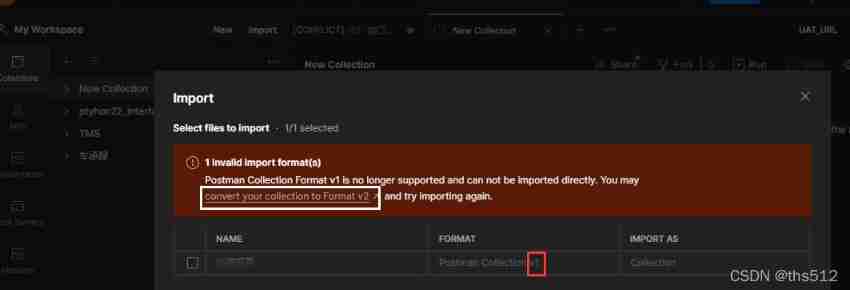
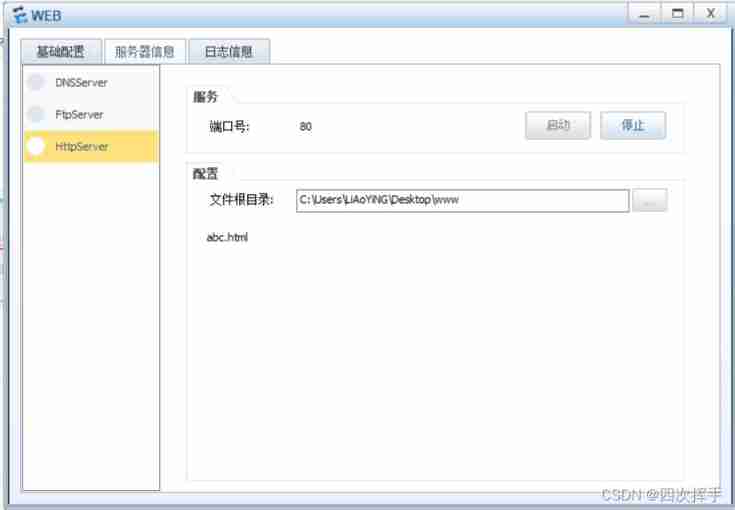
Post man JSON script version conversion
随机推荐
Appscan installation steps
2021 annual summary - it seems that I have done everything except studying hard
Iptables cause heartbeat brain fissure
2、 Operators and branches
Postman interface test
Canoe - the second simulation engineering - xvehicle - 2panel design (principle, idea)
Canoe-the second simulation project-xvehicle-1 bus database design (idea)
Interview and lecture summary 1
Iterator generators and modules
QQ get group member operation time
Process communication and thread explanation
I What is security testing
Understanding of object
Cacti主机模板之定制版
Some tips on learning database
Four sorts: bubble, select, insert, count
Getting started with window functions
Failed to configure a DataSource: ‘url‘ attribute is not specified... Bug solution
Canoe: the fourth simulation project -- bug debugging experience
SSH原理和公钥认证