当前位置:网站首页>Introduction of network security research direction of Shanghai Jiaotong University
Introduction of network security research direction of Shanghai Jiaotong University
2022-07-04 11:14:00 【loveCC_ orange】
I haven't updated my blog for a long time , Because we also need to operate official account , Other words , Even now school begins , Have been writing before NP Things to learn , Now? NP There is little time to watch , So blog is basically stopped . however , I feel I should pick it up , Continue to update , On the one hand, it is to communicate with partners in related majors , On the other hand, I force myself to study . Now it's almost a month since school starts . Next, if there is no accident , It should be updated frequently . however , Today's article , It's not about technology , It's when I was sorting out my mobile photo album today , I found that I took a lot of introductions of some research directions at the tutor selection meeting at the beginning of school , Take it out and tidy it up today , It can help the young friends who want to take the Internet Security exam of Jiaotong University next , Learn about the Network Security College of Jiaotong University in advance . Of course , I may not say everything , You can refer to the official website of the school of network security of Jiaotong University .
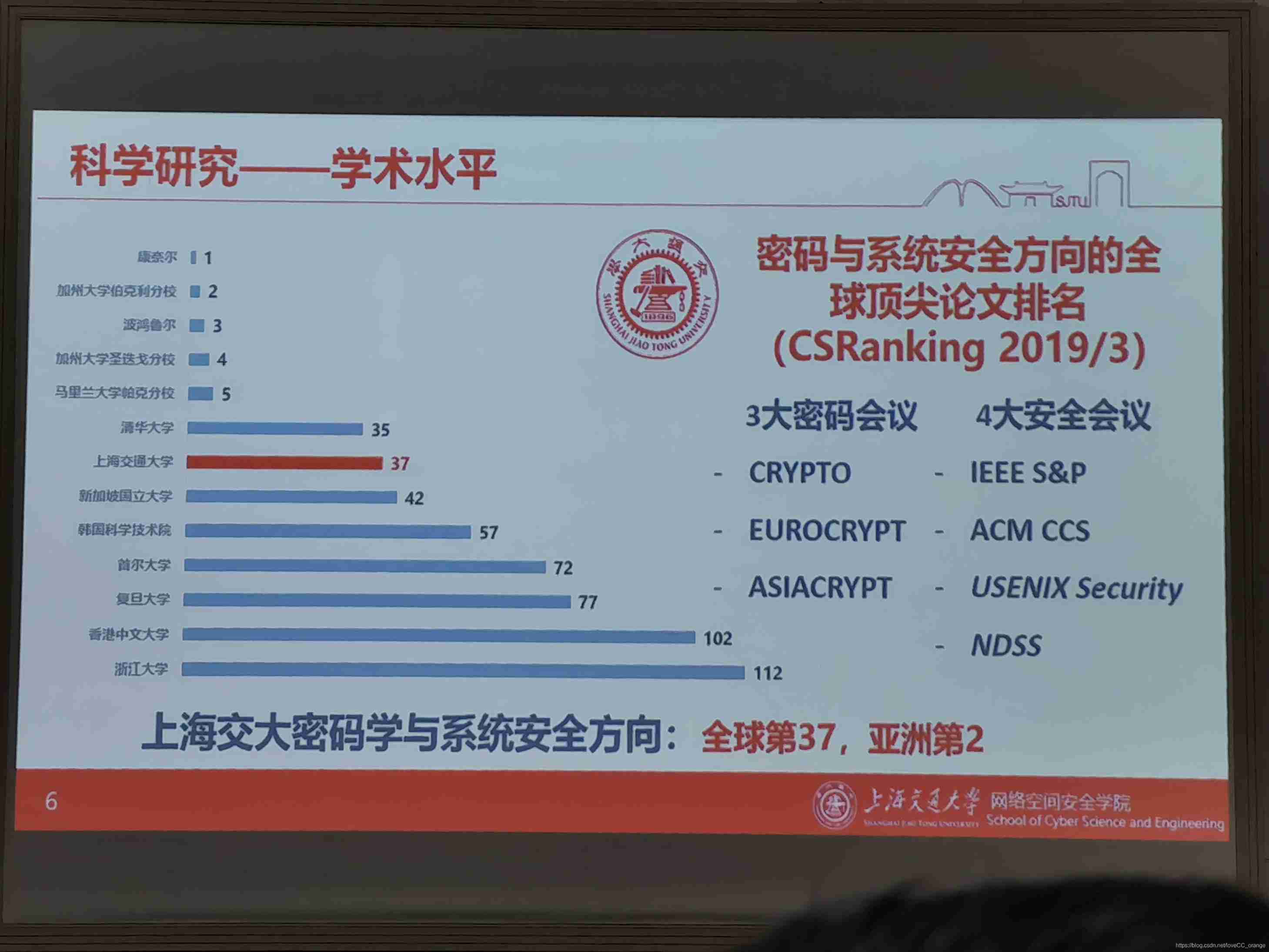
Overview of Network Security College of Jiaotong University
- 2000 Founded in , It is the first college established network security talent training base in China
- 2016 In, it was renamed the College of Cyberspace Security
- 2019 Countries approved in “ First class network security college ”
- The first level discipline of Cyberspace Security in China ( Soft science ranking ,2019 year 10 month )
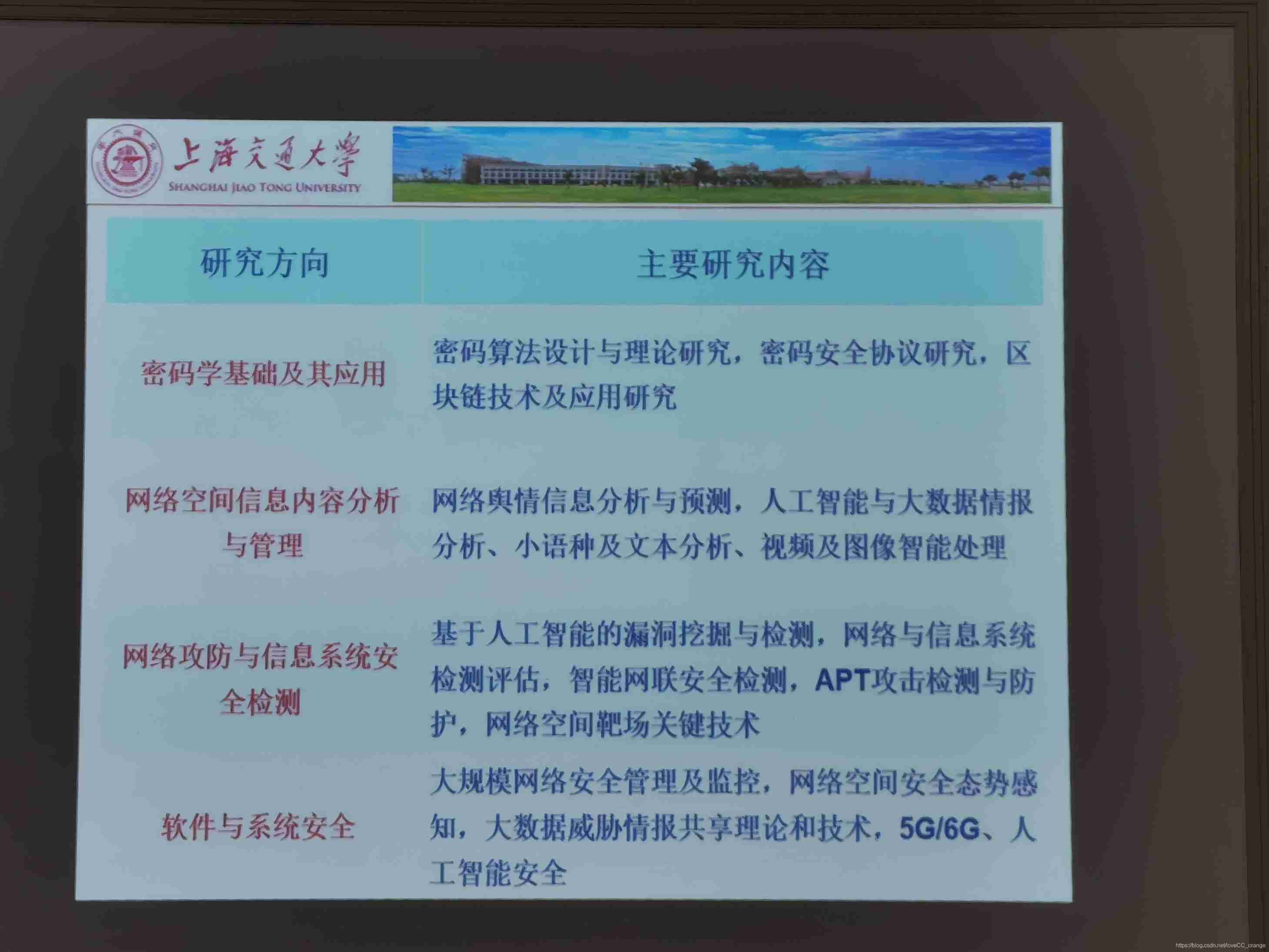
Research direction
- Blockchain and financial security
- Big data security
- Software and system security
- AI security
- Network security defense
- Cryptography science and Engineering
Laboratory Introduction
- Password and Computer Security Laboratory ( Professor gudawu is responsible for )
Research directions include :- cryptography
- software security
- Hardware security
- Network security
- Cryptanalysis and big data security laboratory ( Professor qiuweidong is responsible for )
Research directions include :- cryptanalysis / Cryptographic Engineering
- Intelligent analysis of image and video multimedia / Natural scene text processing technology
- AI Security and privacy protection
- Financial big data analysis
- Internet Measurement Technology
- Network and system security laboratory ( Professor Xue Zhi is responsible for )
Research directions include :- Network Penetration Testing Technology
- Vulnerability mining and analysis
- System security defense technology
- Safety assessment and risk assessment
- Internet Content Security Technology
- Mobile and Internet of things Security Laboratory ( Researcher Wu Yue is responsible for )
Research directions include :- after 5G Mobile communication security
- Internet of vehicles security
- Internet of things security
- Industrial control network security
- Satellite network security
- Information security and Cognition Laboratory ( Professor jiangxinghao is responsible for )
Research directions include :- Intelligent analysis and recognition technology of digital content
- Digital content Forensics Technology
- Intelligent detection technology for image countermeasure data
- Video steganography and steganalysis
- Internet of vehicles information security detection technology
- Artificial Intelligence Security Research Laboratory ( Professor liugongshen is responsible for )
Research directions include :- The application of artificial intelligence in security field : Malicious code detection, etc
- The security of AI itself : Including deep learning framework security 、 Data model security 、 Learning algorithm security, etc
- Network and system security laboratory ( Professor Li Xiaoyong is responsible for )
Research directions include :- Massive data storage system
- Big data analysis of security events
- Cloud computing and container technology
- Threat Intelligence Analysis Technology


Academy of Cyberspace Security Science and Technology
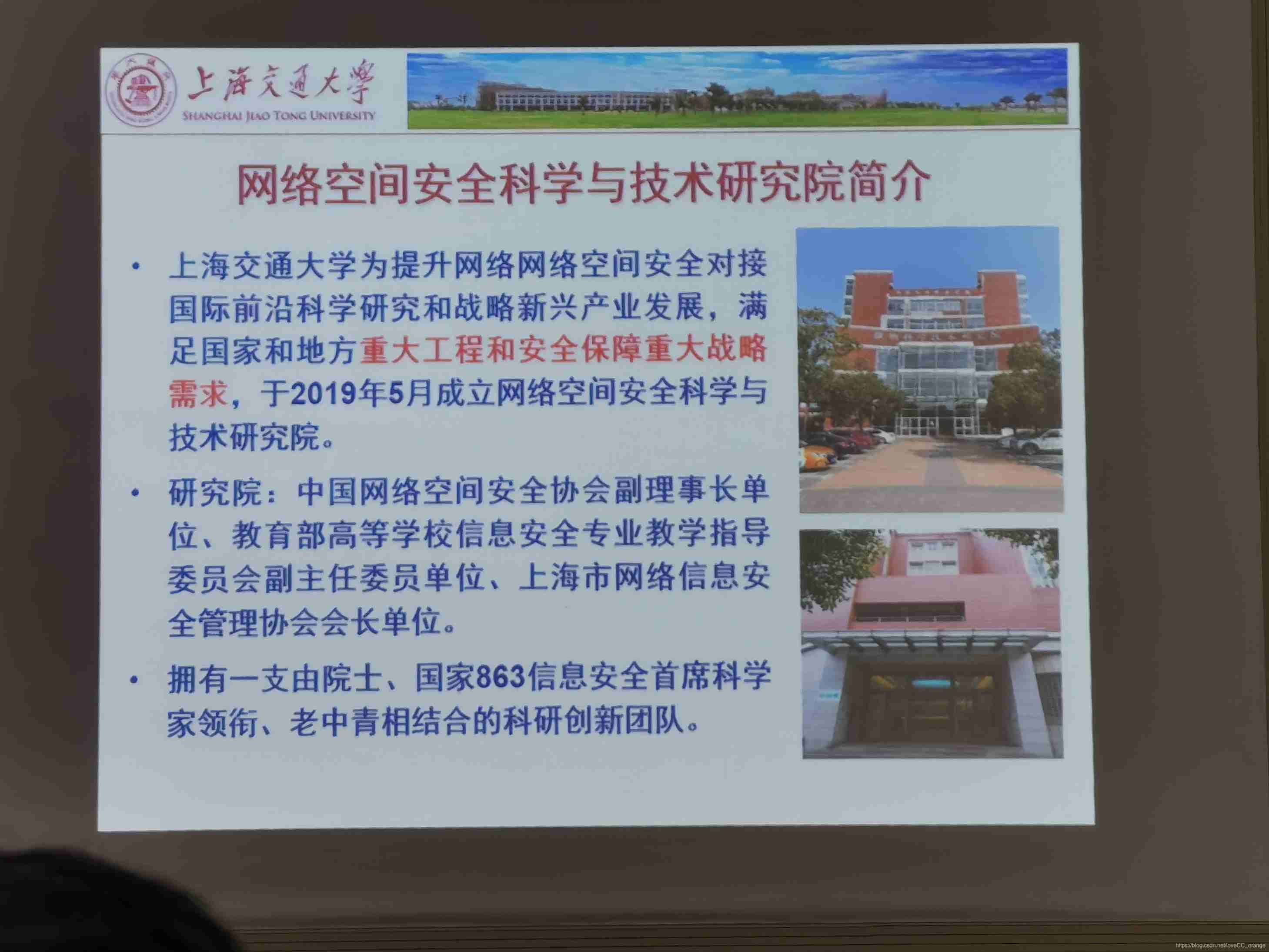
This research institute is 19 year 5 In June, a research institute was separated from the original network security college , He just said , However, when recruiting students for the exam, they are recruited according to the network security college , I didn't know there was such a research institute when I applied for the exam , This has no effect on the registration , It doesn't affect your choice of tutor , It's just a research institute in name ...
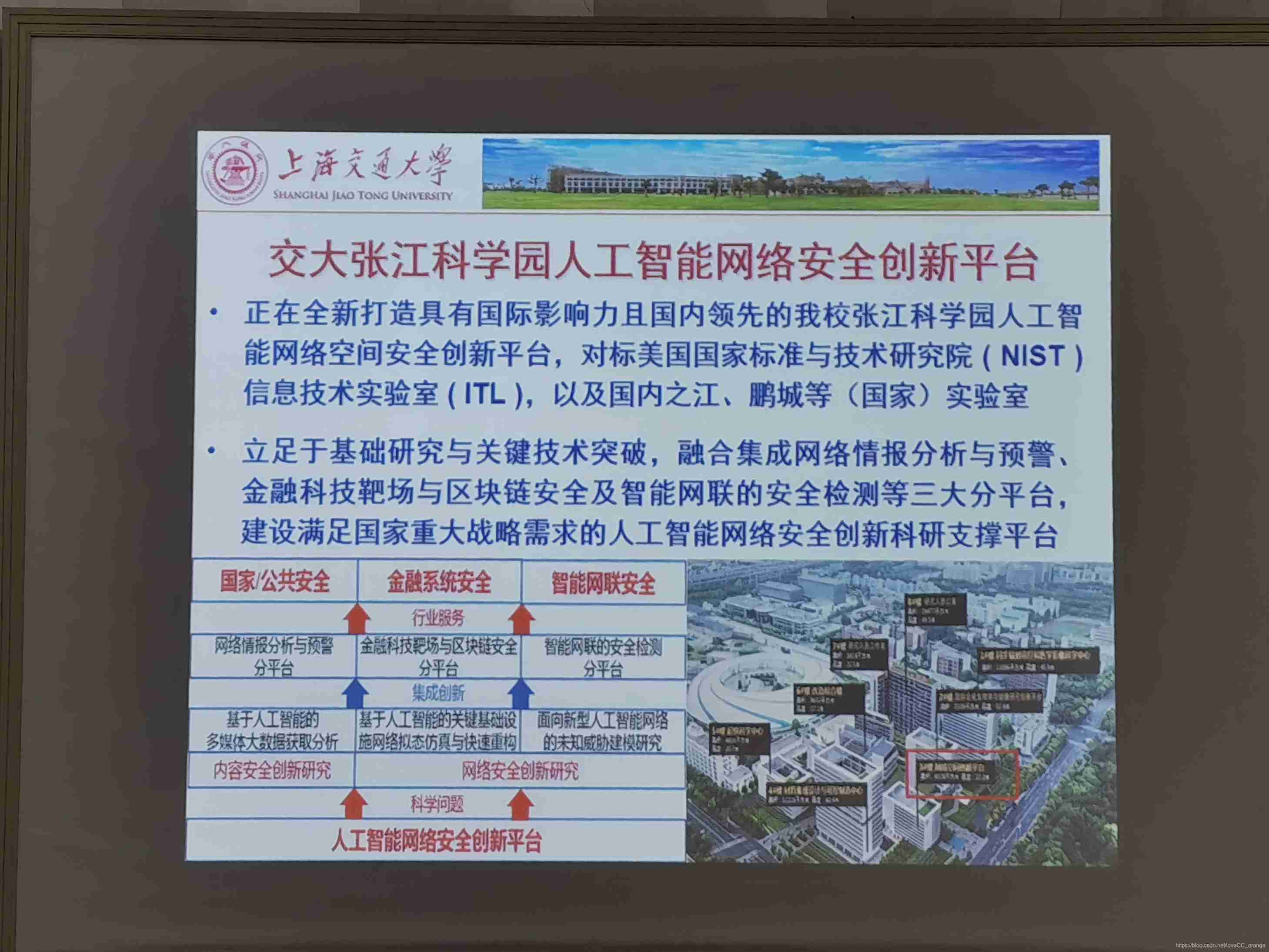
This is a base of Jiaotong University Network in Zhangjiang , It is said that it will be put into use by the end of this year , It is possible that the younger students of network security who will enter school next year may go to Zhangjiang to do scientific research , Maybe , It's just possible ... I don't know the specific situation . We are still on the main campus this year , That is, Minhang . I personally feel that Minhang is better , Infrastructure is more complete , Zhang Jiang's words , It may be more like the Institute of the Chinese Academy of Sciences , Not the environment I like too much . But the accommodation conditions , It must be better , After all, the new building , The place is also more spacious , The dormitory here is really small ..
边栏推荐
- Locust installation
- Canoe test: two ways to create CAPL test module
- Number and math classes
- Appscan installation error: unable to install from Net runtime security policy logout appscan solution
- Canoe: distinguish VT, VN and vteststudio from their development history
- Get the data of the top 100 headlines today with Tianxing data
- Day06 list job
- QQ group collection
- Canoe - the third simulation project - bus simulation - 3-1 project implementation
- 试题库管理系统–数据库设计[通俗易懂]
猜你喜欢
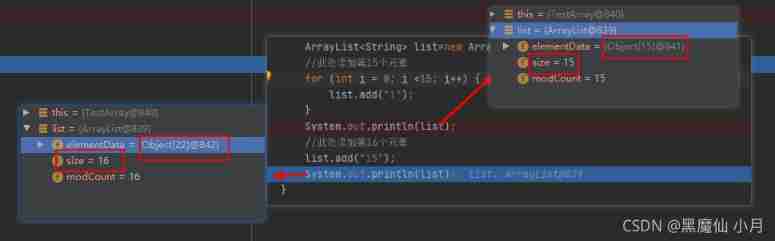
Detailed array expansion analysis --- take you step by step analysis
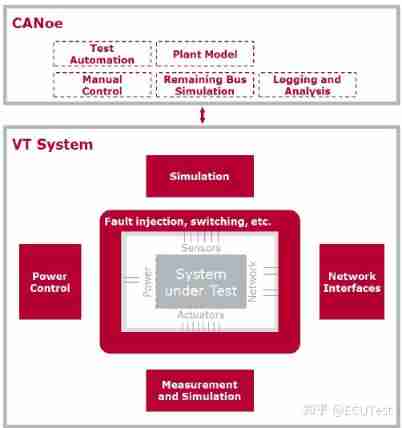
Canoe: what is vtsystem

Deepmind proposed a Zuan AI, which specially outputs network attack language
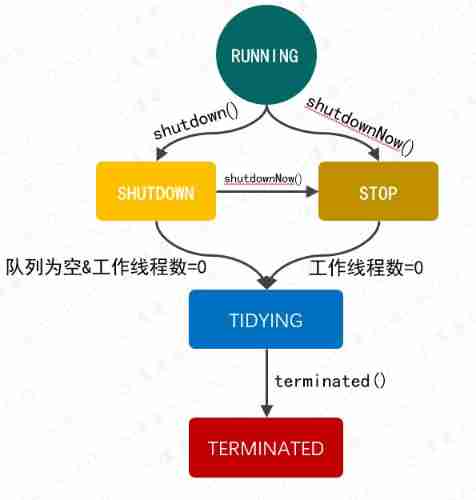
Write a thread pool by hand, and take you to learn the implementation principle of ThreadPoolExecutor thread pool
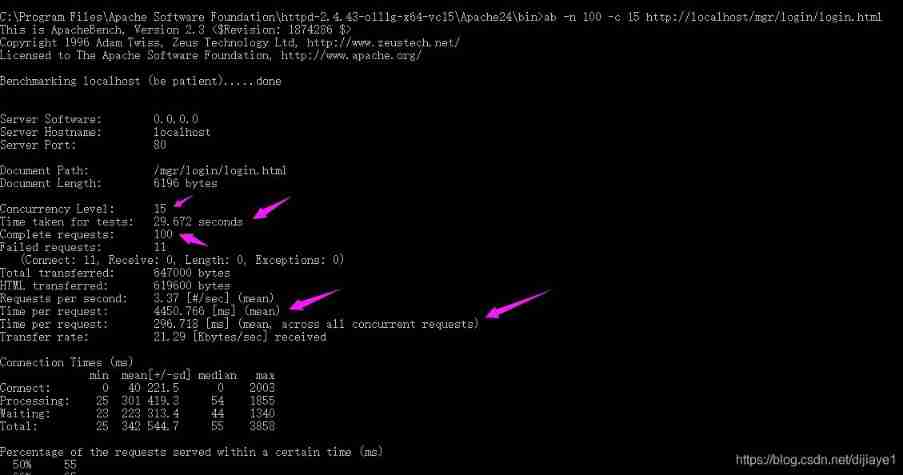
Ten key performance indicators of software applications
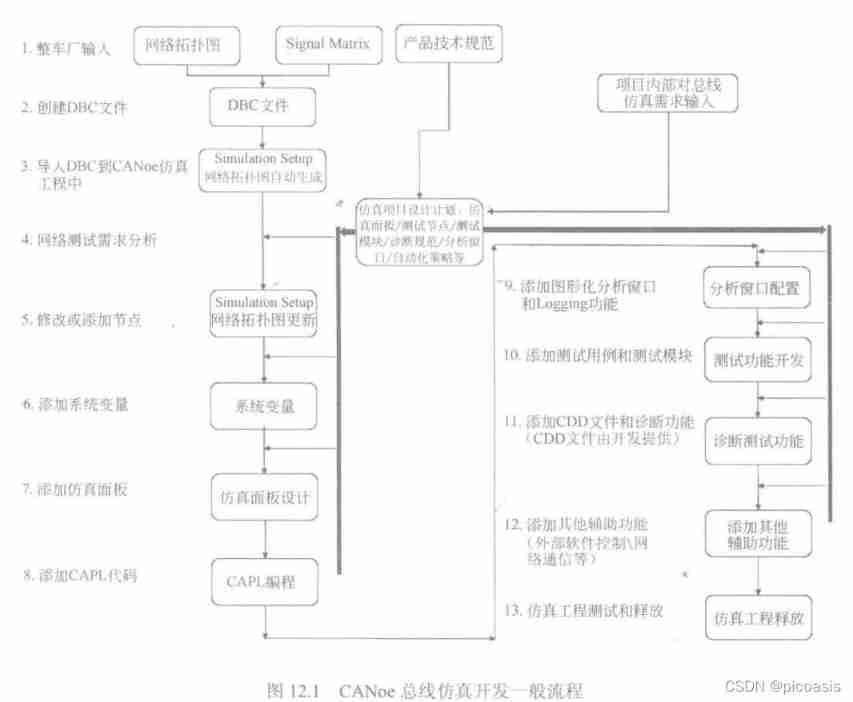
Canoe - the third simulation project - bus simulation-1 overview
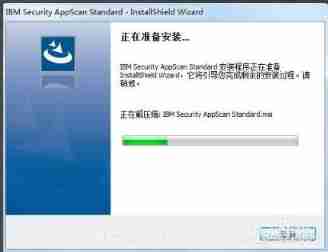
Appscan installation steps
Personal thoughts on the development of game automation protocol testing tool
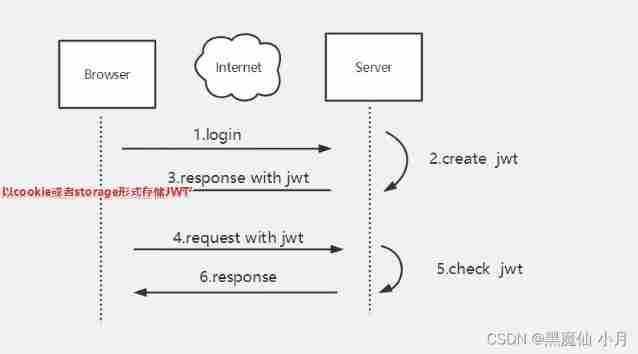
Simple understanding of seesion, cookies, tokens
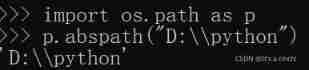
os. Path built-in module
随机推荐
I What is security testing
Canoe test: two ways to create CAPL test module
Common system modules and file operations
Ten key performance indicators of software applications
Exceptions and exception handling
Advanced order of function
Properties and methods of OS Library
Elevator dispatching (pairing project) ②
QQ set group information
unit testing
Canoe - the second simulation engineering - xvehicle - 2panel design (principle, idea)
Interview and lecture summary 1
array_ The contains() function uses
OSI model notes
SSH principle and public key authentication
CAPL: on sysVar_ Update difference on sysvar
Performance test method
Day06 list job
Supercomputing simulation research has determined a safe and effective carbon capture and storage route
Performance features focus & JMeter & LoadRunner advantages and disadvantages